target=_blank exploit
-
Gone Phishing
When a website uses target='_blank' on their links in order to open a new tab or window, that website gives the new page access to the existing window through the window.opener API, allowing it a few permissions. Some of these permissions are automatically negated by cross-domain restrictions, but window.location is fair game.
Apparently, if you open a site with
target="_blank", they can reach back and mess with your originalwindow, including transfer you to a phishing website. This was just effectively demonstrated to me when I followed a link to this blog from my RSS reader. And it can be demonstrated for you too when you click the link above.I had no idea this was possible. Why the fuck is this even a thing? What were the browser vendors thinking?
-
@cartman82 said in target=_blank exploit:
when you
left click the link aboveMy default muscle-memory middle-clicks - doesn't happen then.
Not that that's any excuse mind you...
-
Quoth the page:
If you landed on this page, I encourage you to contact the developers of the referring website and alert them of this issue.
Shouldn't this be in (or refer
red to in)Bugs?
-
@all_users said in target=_blank exploit:
Shouldn't this be in (or referred to in) Bugs?
Bugs are for the WTDWTF forum software of the day. This is a wider issue.
-
@cartman82 said in target=_blank exploit:
Bugs are for the WTDWTF forum software of the day. This is a wider issue.
Technically, it's both (hence the parenthetical comment...)
-
@cartman82 said in target=_blank exploit:
What were the browser vendors thinking?
well, back when that API was created it was a more innocent time, developers hadn't realized exactly how much of an issue cybercrime would become. They sought only to create the ability to make more functional websites with interconnected tabs, because the idea of SPA had not become a thing (thank the goddess). These good intentions have now been warped and perverted to uses the developers never considered and would,. probably, be appalled to consider.
-
Interesting, it seems my Firefox settings or the NoRequestPolicyContinued plugin somehow intercepts this. It does raise a warning in a new tab though, asking me for permission as if to follow a redirect...
-
So adding
rel="noopener noreferrer"to all links withtarget="_blank"is supposed to prevent this interaction?
-
@cartman82 said in target=_blank exploit:
And it can be demonstrated for you too when you click the link above.
It just opens the new page in the same tab. I don't see anything unusual.
-
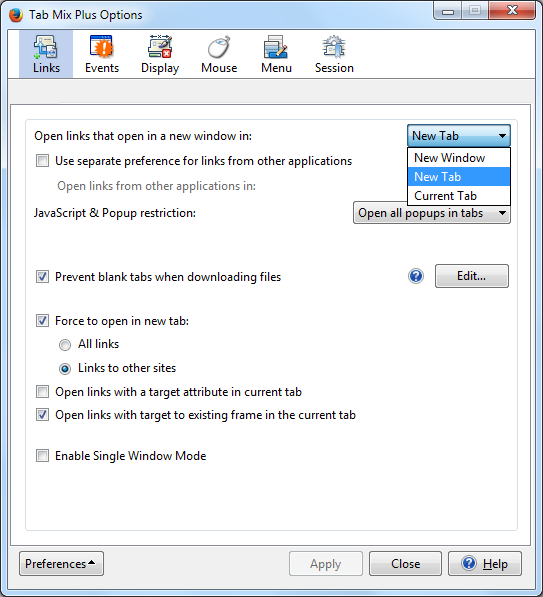
@anotherusername or just don't use
target="_blank". It's 2016, mouses have middle buttons, the last browser that didn't support tabs is long dead, there's pretty much no point in using it anymore. If I want something opened in a new tab, I'll just open it in a new tab, thank you very much.
-
@all_users said in target=_blank exploit:
@cartman82 said in target=_blank exploit:
when you
left click the link aboveMy default muscle-memory middle-clicks - doesn't happen then.
Not that that's any excuse mind you...
A lot of sites disable middle-click now. I really want to beat them with a spiky clue-bat. Especially my main online news site, middle-click no longer works and you have to left-click to open an almost full-page dialog that covers the original page with the article contents and closes if you accidentally click anywhere...
-
@anonymous234 said in target=_blank exploit:
It just opens the new page in the same tab.
Yeah, because it doesn't work.
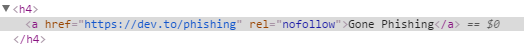
<a href="https://dev.to/phishing" target="_blank">Does this?</a>
Does this?
-
@Maciejasjmj no. Point blank no. The opposite in fact. I virtually always want links to open in new tabs, unless they're navigating within the same website I'm already on. If I want an external link to open in the current tab I'll drag it up to the location bar myself.
-
Okay, it looks like it's stripping out
target="_blank"(which the original raw post also had, by the way), but for people who have settings that force links to open in new tabs, the behavior still takes place.
-
@anonymous234 NoScript stops it from happening.
-
@anotherusername said in target=_blank exploit:
The opposite in fact. I virtually always want links to open in new tabs, unless they're navigating within the same website I'm already on.
Then click them with your middle mouse button. PROBLEM SOLVED!
It should be up to the user, really. You want all links in new tabs, I want all links in the same tab unless I explicitly state I want a new tab. Instead, with target=_blank, I have no option to open the link in the same tab other than dragging it to the address bar, and that's just a retarded way to work around it.
-
@Maciejasjmj The justifiable use case is probably opening a smaller informative window, without losing the data in the current page (for example when filling a form).
Yes, you can simulate it with javascript too, but that applies to everything.
-
@mott555 said in target=_blank exploit:
A lot of sites disable middle-click now. I really want to beat them with a spiky clue-bat.
Someone needs to create and maintain a "things that are not acceptable to do in a website ever" list.
- Break middle click
- Make the page jump up and down (no, not even while loading, if the page is visible it should be usable, otherwise just hide it and show a spinner)
-
@anonymous234 3. Hijack scrolling
-
@anonymous234 said in target=_blank exploit:
The justifiable use case is probably opening a smaller informative window, without losing the data in the current page (for example when filling a form).
Except that no longer works as it's supposed to. target=_blank doesn't open a popup since, uh, IE6?
-
@mott555 said in target=_blank exploit:
an almost full-page dialog that covers the original page with the article contents
OH, like USA Today and a bunch of local sites? That's really obnoxious.
-
@Maciejasjmj said in target=_blank exploit:
Except that no longer works as it's supposed to. target=_blank doesn't open a popup since, uh, IE6?
Is still opens the link in a new context that doesn't move you off your current page
-
@Jaloopa said in target=_blank exploit:
@Maciejasjmj said in target=_blank exploit:
Except that no longer works as it's supposed to. target=_blank doesn't open a popup since, uh, IE6?
Is still opens the link in a new context that doesn't move you off your current page
Is there even a use case for that anymore? I honestly can't think of any.
-
@Maciejasjmj said in target=_blank exploit:
Then click them with your middle mouse button. PROBLEM SOLVED!
Not every mouse has one of those. And why should I have to use an alternate button for what should be the default behavior?
It should be up to the user, really.
That's what addons are for.
@anonymous234 said in target=_blank exploit:
The justifiable use case is probably opening a smaller informative window, without losing the data in the current page (for example when filling a form).
My settings force those to open in new tabs also. If I want to detach it to a separate window so I can see them both at the same time, I'll do that manually.
-
@bb36e said in target=_blank exploit:
@anonymous234 3. Hijack scrolling
Does "making the page longer when you scroll down" count? Because if yes, I'm 100% with you.
-
@mott555 said in target=_blank exploit:
A lot of sites disable middle-click now.
 How can a site disabled browser behaviour?
How can a site disabled browser behaviour? 
@mott555 said in target=_blank exploit:
left-click to open an almost full-page dialog
 How can a site override a browser's behaviour?
How can a site override a browser's behaviour? 
-
@Lorne-Kates it's called Javascript. It makes it possible to have web pages that do things other than text and images. On a modern browser, without core features turned off, some pages actually look different to this one:
-
@cartman82 said in target=_blank exploit:
Why the fuck is this even a thing? What were the browser vendors thinking?
Mainly for this reason:
- Click a "Open here to do shit" link
- It uses _blank to open a new window, where another application runs.
- You interact with that application. Putting in data of some sort.
- You click save in the popup. It calls back into the original opener and passes data base
- The window closes, and the parent application has data from the child popup
It's not smart at all. But that's how pop-up data entry worked before AJAX.
-
@Lorne-Kates said in target=_blank exploit:
@mott555 said in target=_blank exploit:
A lot of sites disable middle-click now.
 How can a site disabled browser behaviour?
How can a site disabled browser behaviour? 
@mott555 said in target=_blank exploit:
left-click to open an almost full-page dialog
 How can a site override a browser's behaviour?
How can a site override a browser's behaviour? 
<a href="#" onclick="openPopUp('/page.htm')">Yes,
 . But you asked how.
. But you asked how.
-
target=_blank is helpful for javascript games (inb4 derision of the concept) where leaving the page means you lose game progress, at least for links that you are likely to misclick while playing the game.
-
@coderpatsy saving state in a cookie or in
localStorageso the game can resume where it was interrupted is even more helpful for those games.
Seriously though, that's not a bad idea; in fact it's what I did in the HTML/JS games I wrote (Sudoku) or adapted (4096) to play in DropBox, because my iPhone is really quick to force quit an app I was just using because I opened a different app and it only has like 3 bytes of RAM.
-
Nice. Funny thing is, I opened this topic as a new tab (with a middle click) from the list of topics, then left-clicked the link (and my settings are to open links in new tabs): not only did it change this tab, but it also went back and changed the tab with the list of topics! (in addition to opening a new tab with the new page in it, of course)
Out of curiosity, what kind of information is passed around when opening a new tab that makes this possible?
-
@cartman82 Except you linked the landing page instead of:
Which exposes the bug, even when I middle click in Chrome.
-
@JazzyJosh said in target=_blank exploit:
@cartman82 Except you linked the landing page instead of .
Looks like WTDWTF isn't vulnerable, because we don't get redirected.
Unless I'm misunderstanding.
It's vulnerable if the user's setting is to open links in new tabs by default. Which, granted, isn't the default setting, but it's common enough that it might be good to protect those users. Adding
rel="noopener noreferrer"to external links shouldn't hurt anything, in any case.
-
-
@JazzyJosh said in target=_blank exploit:
@cartman82 Except you linked the landing page instead of:
That doesn't do anything other than load the page in the new tab when I click on it:
The original link did:
-
@anotherusername For me, opening the onebox in the OP does nothing, but opening the onebox in my post does.
EDIT: Ah, the top isn't a onebox and I don't have it configured to open links in new tab, because I use middle click.
-
@ben_lubar is this a thing the sanitizer can protect against?
-
@JazzyJosh okay, after inspecting the links, apparently this:
<a href="something" target="_blank" rel="nofollow">(which is what the onebox plugin is generating) is not triggering the exploit, but this:
<a href="something" rel="nofollow">(the default link that it's generating) is triggering it, when my settings make the link open in a new tab.

You, on the other hand, are seeing the opposite behavior.

-
Okay, the recommended fix:
<a href="something" rel="nofollow noopener noreferrer">still exposes the
window.opener. WHAT THE FUCK.edit: same for:
<a href="something" rel="noopener noreferrer">
-
@Maciejasjmj said in target=_blank exploit:
If I want something opened in a new tab, I'll just open it in a new tab, thank you very much.
QFT. I’ve been slightly annoyed by sites that open links in new windows/tabs ever since that first started appearing — I can decide for myself which window/tab I want to view the linked site in, thank you very much. But at least it’s not a damned lightbox.
-
@remi said in target=_blank exploit:
Nice. Funny thing is, I opened this topic as a new tab (with a middle click) from the list of topics, then left-clicked the link (and my settings are to open links in new tabs): not only did it change this tab, but it also went back and changed the tab with the list of topics! (in addition to opening a new tab with the new page in it, of course)
Out of curiosity, what kind of information is passed around when opening a new tab that makes this possible?
Don't give Nod
 too much credit. Much of the jellypotato behavior can be ascribed to the way it uses socket.io to broadcast messages. There is apparently some cross-talk between socket.io sessions that causes the wrong tabs to receive certain messages, or tabs to miss messages they should have received.
too much credit. Much of the jellypotato behavior can be ascribed to the way it uses socket.io to broadcast messages. There is apparently some cross-talk between socket.io sessions that causes the wrong tabs to receive certain messages, or tabs to miss messages they should have received.I don't know whether to blame socket.io or the way it's being used here.
-
@Maciejasjmj said in target=_blank exploit:
@anotherusername or just don't use
target="_blank". It's 2016, mouses have middle buttons, the last browser that didn't support tabs is long dead, there's pretty much no point in using it anymore. If I want something opened in a new tab, I'll just open it in a new tab, thank you very much.Some people's bosses order them to set specific links to automatically open with
target="_blank"
-
@anotherusername said in target=_blank exploit:
Yes, . But you asked how.
I meant "why the fuck is javascript (context of web page) allowed to override a right-click Context Menu (context of browser/system)"
-
@Lorne-Kates that's a completely different question that doesn't apply to this situation at all. Simple javascript links don't override the right-click context menu. They just make some of the options in the right-click menu not work correctly.
-
-
@Tsaukpaetra hey, I have an avatar!
See:
 -- nope.
-- nope.
 -- there's mine.
-- there's mine.
:@remi: -- nope.Except you, @anotherusername , you're cool. :D
...oh. Nevermind.
-
@Tsaukpaetra Fine.
-
-
@coderpatsy said in target=_blank exploit:
@Tsaukpaetra Fine.
My avatar started as a perversion of the

 default, but now it's no longer recognizable as such.
default, but now it's no longer recognizable as such.
My previous avatar was a perversion of the CS default avatar (I added devil horns to the silhouette), which was the style at the time.
 DEV Community
DEV Community