Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...)
-
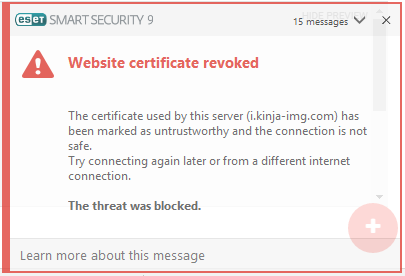
Huh, why does my security suite keep blocking all these sites?
...wonderful.
-
...I wonder if that's why my helpdesk got a couple calls from users getting cert expiration messages on the client's SSO page...
Edit: Signs pointing to yes! I just loaded up our SSO page and the cert is indeed given by GlobalSign. Wheeee!
-
The 🔒https:// key is a definite improvement over the Caps Lock key.
-
@LB_ said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
The 🔒https:// key is a definite improvement over the Caps Lock key.
I hate these stock images so much. There's like three dozen of them in our stock image library and I'm so glad we've never used them.
-
@Fox I want a keyboard that's just the bullshit keys that stock images have.
-
@ben_lubar said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@Fox I want a keyboard that's just the bullshit keys that stock images have.
Too bad they're usually rectangular, otherwise you could just make a regular keyboard have those labels instead.
-
I've never heard of GlobalSign. Why are top websites using them?
-
I think they should just create new e-cert with unaffected CA cert, with the same expiration date (or some duration later as apology) according to their transaction records, then email to the contact point of their customer to let them update the cert of their servers instead of waiting the browsers to update the revocation list to resolve the issue.
-
I think the customers should just spend an hour and $30 getting their cert elsewhere.
-
@dangeRuss said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
$30
Let's Encrypt doesn't cost anything, and if you need an EV certificate, it's not going to be that cheap.
-
@ben_lubar said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@dangeRuss said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
$30
Let's Encrypt doesn't cost anything, and if you need an EV certificate, it's not going to be that cheap.
OK so $100 instead of $30, but at least you won't have your site down for a week.
Now about lets encrypt, how trusted are they by browsers?
-
Has anyone found a good technical description of what happened? The GlobalSign statement suggests it might be buggy OCSP code in "some browsers".
-
@dangeRuss said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
Now about lets encrypt, how trusted are they by browsers?
They're cross-signed by IdenTrust, so pretty much trusted.
-
@Greybeard My understanding is this:
One of the intermediate certificates GlobalSign uses in their Extended Validation signing certificate authority got marked as expired.
Browsers are thus marking all certificates expired with this EV chain as expired as well.
Now, GlobalSign is trying to say that the browser makers are at fault because they shouldn't treat certificates as expired just because their signatory's certificates are expired.
Of course, if I am grasping this correctly, GlobalSign is wrong as the main reason to cancel a certificate signing authority's certificates is because they were either:
- Stolen
- Fraudulent
which makes any certificates signed with them suspect.
-
@powerlord That makes no sense. Certificates don't get marked as expired, they expire after the validity date in the certificate. OCSP has nothing to do with expiration.
-
@Greybeard Bad wording on my part, they revoked said certificate.
-
@powerlord Their statement said they revoked a cross-cert. Do you have any evidence that what they revoked should have caused clients to distrust the server certs?
-
@Greybeard said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@powerlord Their statement said they revoked a cross-cert. Do you have any evidence that what they revoked should have caused clients to distrust the server certs?
Because the trust chain was broken. Apparently the thinking was, if you broke the trust at the level above you (i.e. closer toward the authority), you're likewise no longer trusted, but only because verifying the trust chain failed.
-
@Tsaukpaetra Globalsign's statement says "some browsers incorrectly inferred that the cross-signed root had revoked intermediates, which was not the case." This suggests buggy browsers, not a broken trust chain.
Look, I asked if anyone had found a good technical description of what happened. I didn't ask for inaccurate, vague, uninformed claptrap, but as that's what I've gotten so far, is it any wonder I'm cranky?
-
@Greybeard said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
Look, I asked if anyone had found a good technical description of what happened. I didn't ask for inaccurate, vague, uninformed claptrap, but as that's what I've gotten so far, is it any wonder I'm cranky?
That's hilarious, it's almost like you just found this forum or something...
Edit: I would think you would seek out the source of the problem, then, if you wanted a good technical description (i.e. the browser's faulty code, apparently).
-
I'm sensing some happy times at places I used to worked:
 We're going to need jQuery, so I'll just download the minified library and reference it on our server
We're going to need jQuery, so I'll just download the minified library and reference it on our server
 NO! That's so much extra bandwidth! Don't other people host it for you?
NO! That's so much extra bandwidth! Don't other people host it for you?
 Uh, yeah, I guess we could do the dumb thing and hotlink to it. But why rely on a third party for a tiny file on a low bandwidth site?
Uh, yeah, I guess we could do the dumb thing and hotlink to it. But why rely on a third party for a tiny file on a low bandwidth site?
 Um, actually, I think jQuery is trustworthy. They aren't going anywhere, and they'll always be available. Ship it!
Um, actually, I think jQuery is trustworthy. They aren't going anywhere, and they'll always be available. Ship it!
 Whatever.
Whatever. <script src='https://code.jquery.com/jquery.min.js' />Ah-- sweet sweet "i fucking told you so"
-
@Tsaukpaetra said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
Edit: I would think you would seek out the source of the problem, then, if you wanted a good technical description (i.e. the browser's faulty code, apparently).
Hard to do without the input conditions. Just what was the OCSP response? To what query?
GlobalSign could be blowing smoke, but it's entirely plausible that what they revoked shouldn't have broken the browser's trust. One could perhaps fault them for failure of imagination in their QA department or, more likely, their incident handling and communication process, but the primary incident just might not be their fault.
-
@Greybeard said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@Tsaukpaetra said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
Edit: I would think you would seek out the source of the problem, then, if you wanted a good technical description (i.e. the browser's faulty code, apparently).
Hard to do without the input conditions. Just what was the OCSP response? To what query?
GlobalSign could be blowing smoke, but it's entirely plausible that what they revoked shouldn't have broken the browser's trust. One could perhaps fault them for failure of imagination in their QA department or, more likely, their incident handling and communication process, but the primary incident just might not be their fault.
Yes and if you want to spend time researching that on a reputable source of reliable information and intelligent thought, feel free to report your results back here at your discretion.
Otherwise, enjoy the WTF for what it is and stop trying to tear down the scales of obscurity from everyone's eyes without cause.
-
@Lorne-Kates I think the scary part in your dialog is they plan to always use the latest version of jquery.
There are breaking changes between versions (Say you'll not be able to remove attribute on some DOM attributes such as "disabled" with .removeProp() because some browser will behave funny if you use it that way. You should do something like .prop("disabled", ""))
3rd party components using .removeProp() that way will break.
-
@cheong said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@Lorne-Kates I think the scary part in your dialog is they plan to always use the latest version of jquery.
There are breaking changes between versions (Say you'll not be able to remove attribute on some DOM attributes such as "disabled" with .removeProp() because some browser will behave funny if you use it that way. You should do something like .prop("disabled", ""))
3rd party components using .removeProp() that way will break.
Oh yeah, I experienced this first-hand. Migrated from something like 1.6 to 1.11 (I think) a year ago. Optimizations and corrections meant that my predecessor's idea of destroying a DOM element and then hiding it on the next line no longer jived. Amongst a suite of "WTF were you thinking" pieces of awe-something-ness...
-
@Tsaukpaetra said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
Because the trust chain was broken.
The trust chain itself wasn't. That's why this is recoverable in a few days as caches get flushed.
What happens is GlobalSign have a bunch of CA certificates derived from their root, and it seems that they cross-sign between these other certificates in their OCSP statement (i.e., not in information that needs to be used to make the primary SSL trust decision). The OCSP statement is used by clients to decide when to revoke a certificate; its purpose is similar to that of CRL in a simpler CA, though it uses a more sophisticated description. However, this must've been causing them some operational problems of some kind (details unknown) since they'd decided to try and reduce the amount of cross-signing. And browsers took this to mean that the cross-signed certificates were invalid (and hence everything they signed was also bad), though whether this is because the OCSP statement was botched or browsers were interpreting it outside what the standard actually says is unclear.
So that's it; everyone gets to see a bit more of the details of how things really work when some of it breaks…
-
@ben_lubar said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@Fox I want a keyboard that's just the bullshit keys that stock images have.
-
@ben_lubar said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@dangeRuss said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
$30
Let's Encrypt doesn't cost anything, and if you need an EV certificate, it's not going to be that cheap.
Let's Encrypt cost my company several days of a developer's time to implement because we have Windows servers and Windows is the one special snowflake case that CertBot doesn't cover. Then it cost another developer day to fix shit broken by the first developer because of confusion around Let's Encrypt.
-
@Arantor said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@ben_lubar said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@dangeRuss said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
$30
Let's Encrypt doesn't cost anything, and if you need an EV certificate, it's not going to be that cheap.
Let's Encrypt cost my company several days of a developer's time to implement because we have Windows servers and Windows is the one special snowflake case that CertBot doesn't cover. Then it cost another developer day to fix shit broken by the first developer because of confusion around Let's Encrypt.
/me wishes we could use it for our domains at work because other than our ecommerce domains we don't need the EV certs we're paying for and we have a LOT of non ecommerce domains.
on the other hand the web team can't find their arse with an atlas..... so if we did i'd be the one maintaining that and after the last time their servers fell over and appdev was blamed for it because i had a login to the server i went and issued
sudo userdel accaliaon all their servers i still had access to and said "fuck it. you're on your own. have fun with that."
-
@accalia said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
sudo userdel accala
so because of @accalia's you still have accounts on all of them?
-
@Jaloopa said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@accalia said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
sudo userdel accala
so because of @accalia's you still have accounts on all of them?
no, that was just at ypo in the post not in the sudo
-
@accalia said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
at ypo
you're doing this on porpoise now aren't you?
-
@Jaloopa said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@accalia said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
at ypo
you're doing this on porpoise now aren't you?
i hvae no ieda waht you cuold possbily maen.
-
@cheong said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@Lorne-Kates I think the scary part in your dialog is they plan to always use the latest version of jquery.
Toby Fair, it might have been
/versomething/jquery...instead oflatest.
-
@accalia said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@Jaloopa said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
@accalia said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
at ypo
you're doing this on porpoise now aren't you?
i hvae no ieda waht you cuold possbily maen.
I don't even see the typos anymore. I just see "yip", "kyon", and "bark"
-
Found out today that the client's SSO page cert errors were because of this.
I laughed.
-
@Greybeard said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
GlobalSign could be blowing smoke
Apparently they were. Their OCSP service was buggy.
-
What I don't get - why is just updating the OCSP enough? As I understand it, a revocation gets its authority from being signed by the original signer's private key, not by any web mechanism for distributing the revocations. Couldn't an attacker potentially re-distribute the erroneous revocations at some future date? Shouldn't all those certificates be re-issued?
-
@PleegWat The CRL has a timestamp so reusing that old copy with the revocations in it can be detected as being an outdated CRL. Newer versions can include a line in the "ledger" that a certificate is reinstated.
As for OCSP responses, they too have a timestamp and they're not meant to be cached for too long either.
-
@Greybeard said in Website Certificate Revoked (jquery.com, theguardian.com, kinja-img.com, ...):
Look, I asked if anyone had found a good technical description of what happened. I didn't ask for inaccurate, vague, uninformed claptrap, but as that's what I've gotten so far, is it any wonder I'm cranky?
If you actually think anyone (here or anywhere else) has that kind of answer, then that is the real
 . I seriously doubt that even the principals in the situation knew what really happened, at least not at the time you posted this.
. I seriously doubt that even the principals in the situation knew what really happened, at least not at the time you posted this.