Newegg card info entered between Aug 14 - Sep 18 skimmed
-
Keep an eye on your statements.
I also think it's funny how Engadget says that the attackers 'went to pains to hide their identity' by using a private domain registration, like this is some uber secret trick.
-
Tech company can't find literally anyone to do cyber sleuthing?
Shame.
-
@bb36e said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
'went to pains to hide their identity' by using a private domain registration
It's not so secret. They live the next house over to me: 125 Fake Street, Nowhere, CA 90210
-
How did this code end up on the payment processing page? Were their servers compromised? Was it an inside job?
-
@Lorne-Kates said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
It's not so secret. They live the next house over to me: 125 Fake Street, Nowhere, CA 90210
E_VALIDATION_FAIL: Zip code does not match city
-
@Polygeekery this appears to be the same malware which infected British airways' site
-
@dcon said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@Lorne-Kates said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
It's not so secret. They live the next house over to me: 125 Fake Street, Nowhere, CA 90210
E_VALIDATION_FAIL: Zip code does not match citySome people consider Beverly Hills to be nowhere.
-
@Polygeekery said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
How did this code end up on the payment processing page? Were their servers compromised? Was it an inside job?
Yes, that's the part that I find weird. All the reports about this are extremely light on details and only say something very vague like "Some Javascript was injected into the checkout page."

Considering that NewEgg does $2.5 Billion a year, you would think their payment processing would be pretty decent. I suspect NewEgg is keeping details quiet because there's an embarrassing WTF involved.
-
@El_Heffe said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@Polygeekery said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
How did this code end up on the payment processing page? Were their servers compromised? Was it an inside job?
Yes, that's the part that I find weird. All the reports about this are extremely light on details and only say something very vague like "Some Javascript was injected into the checkout page."

Considering that NewEgg does $2.5 Billion a year, you would think their payment processing would be pretty decent. I suspect NewEgg is keeping details quiet because there's an embarrassing WTF involved.
Yeah, @bb36e said it was the same malware that hit another site, but how is it getting there? How is it getting served or injected or whatever and served to customers?
-
@Polygeekery As far as I can find nobody's said how it got there. It was on their servers (like the TicketMaster UK breach), not the third-party injection that hit British Airways, according to the ArsTechnica article on it.
-
@Polygeekery said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
Yeah, @bb36e said it was the same malware that hit another site, but how is it getting there? How is it getting served or injected or whatever and served to customers?
It's not exactly the same thing. The attack here is "inserting nasty JavaScript into checkout pages on reputable sites", dubbed MageCart because it first started attacking Magento webshops. By now, this attack has expanded to other e-commerce systems (NewEgg's ASPX site is not Magento, Magento is PHP). Vectors that have been reported:
- the original: getting access to the target server and adding links to external JS, original write-up about 7000+ sites affected and NewEgg write-up
- getting access to the target server and replacing existing files, like British Airways
- hacking a third-party library that's loaded by the reputable site, like Feedify hacked to inject shit into 4000+ websites or Inbenta hacked to inject shit into TicketMaster
Getting access to the target server is easier than you'd think, because there are too many idiots out there.
- Magento has no protection against brute-forcing admin passwords, no support for moving the admin panel to a custom URL, or adding an additional layer of HTTP Basic Auth, or anything else to make it harder to mass-attack. All these measures would help and there are third-party recommendations to apply them, but idiots deploying these shops won't read them or do anything above the bare minimum.
- System maintenance is haaaaard. The British Airways site that got popped was serving files with 'Last-Modified: sometime in 2012' headers, implying that updates were not done as often as one would hope.
- Sysadmin is haaaaaard. Welcome to NewEgg's systems:
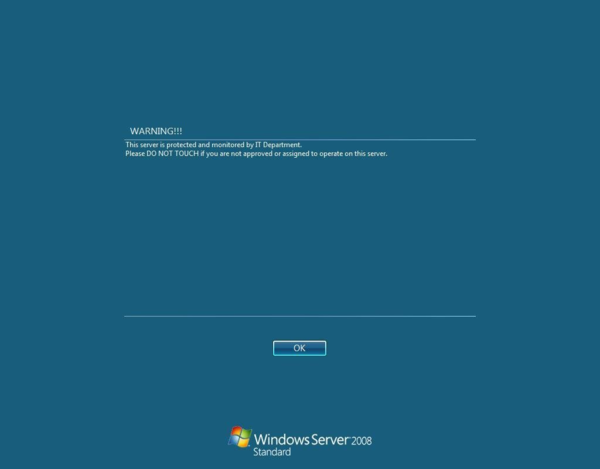
Source: @Viss
It is also worth noting that this skimming is only possible because websites want their visitors to enter payment details in the site itself, instead of going to the payment gateway. Payment gateways have dedicated infrastructure for taking payments, and one of the key requirements for that infrastructure is to keep the merchant from learning your payment details. But no, every fucking site on the list has elected to collect payment details by themselves. (One wonders what PCI-DSS would say about that.)
How this can be avoided?
- DON'T COLLECT PAYMENT DETAILS, use a payment gateway. Yes, that means a completely separate step in the checkout process. Deal with it. Most gateways let you style this step, and sometimes even iframe it in your site for appearances.
- Ensure all the scripts you are loading are actually what you think they are.
- Don't expose unnecessary shit to the internet.
- The usual, keep your systems updated, ensure strong passwords, etc.
-
@DCoder For all we know at this point it could have been a compromised browser plugin too.
-
@blakeyrat I imagine at least one of the many security researchers looking at this would have noticed that by now.
-
@DCoder Right I'm a stupid idiot moron, I get it.
Point is, I'm just saying that it's perfectly possible the credit cards got skimmed without the site itself getting hacked.
-
@DCoder said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
Ensure all the scripts you are loading are actually what you think they are.
I feel like Scott Helme and Troy Hunt are the only two people on earth qualified to make a website.
-
@El_Heffe said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@Polygeekery said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
How did this code end up on the payment processing page? Were their servers compromised? Was it an inside job?
Yes, that's the part that I find weird. All the reports about this are extremely light on details and only say something very vague like "Some Javascript was injected into the checkout page."

Considering that NewEgg does $2.5 Billion a year, you would think their payment processing would be pretty decent. I suspect NewEgg is keeping details quiet because there's an embarrassing WTF involved.
Rule 1 of data breaches: it's always worse than you think
Rule 2 of data breaches: it's even worse
-
@DCoder I think SRI should be next on the list of requirements for browsers to flag a page as 'secure' . It doesn't take as much work as HTTPS, either.
-
@blakeyrat said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
I'm a stupid idiot moron
I didn't say that.
@blakeyrat said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
I'm just saying that it's perfectly possible the credit cards got skimmed without the site itself getting hacked.
One of the known vectors I mentioned was
hacking a third-party library that's loaded by the reputable site
. And as you said, popular browser extensions have been taken over by malicious actors in the past for similar means. It's probably just a matter of time before this attack starts using that approach as well, but the write-ups on NewEgg all point towards a hacked server.
-
@Jaloopa said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
Rule 2 of data breaches: it's even worse
Hofstadter's Law applies: It's always worse than you think it is, even after you factor in Hofstadter's Law.
-
New victim: TechRabbit, acknowledging compromise from Feb 2017 through May 2018.
-
@dcon said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@Lorne-Kates said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
It's not so secret. They live the next house over to me: 125 Fake Street, Nowhere, CA 90210
E_VALIDATION_FAIL: Zip code does not match cityCAstands for Canada…
-
Bad news: There's also a skimmer on the Guild Wars 2 website.
Good news: It's this one:
https://guildwars2.staticwars.com/img/pof/mounts/skimmerBg.21697e08.mp4
-
@dkf said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@dcon said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@Lorne-Kates said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
It's not so secret. They live the next house over to me: 125 Fake Street, Nowhere, CA 90210
E_VALIDATION_FAIL: Zip code does not match cityCAstands for Canada…Error report: Localization string for
E_VALIDATION_FAILmessage is wrong.
-
@The_Quiet_One said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@dcon said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@Lorne-Kates said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
It's not so secret. They live the next house over to me: 125 Fake Street, Nowhere, CA 90210
E_VALIDATION_FAIL: Zip code does not match citySome people consider Beverly Hills to be nowhere.
Everyone knows Beverly Hills is 90210
-
@JazzyJosh said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@The_Quiet_One said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@dcon said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
@Lorne-Kates said in Newegg card info entered between Aug 14 - Sep 18 skimmed:
It's not so secret. They live the next house over to me: 125 Fake Street, Nowhere, CA 90210
E_VALIDATION_FAIL: Zip code does not match citySome people consider Beverly Hills to be nowhere.
Everyone knows Beverly Hills is
90210where I want ta be.FTFY.
-
@Tsaukpaetra kokomo…
