WTF Bites
-
-
@Zerosquare said in WTF Bites:
Hey! No space-traveling-shaming!
I only shame in the temporal dimension.
-
There should be ICANN-like organization for naming projects.
While I agree, programmers being the way they are there would soon be n+1 such organisations with a fair amount of naming overlap. And some projects would inevitably get different names in different organizations.
-
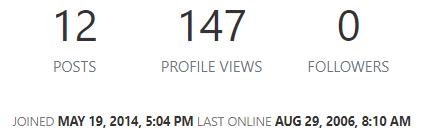
Last online 8 years before they joined.
Seriously, the "last online" timestamp is (presumably) accurate. The "joined" timestamp is when their profile was migrated from CS to Discurse. For whatever reason, the "last online" timestamps were preserved in the migration, but the "joined" timestamps weren't. So anybody who stopped visiting TDWTF before


 will have a "last online" timestamp older than their "joined" (really "profile migration") timestamp.
will have a "last online" timestamp older than their "joined" (really "profile migration") timestamp.
-
@BernieTheBernie said in WTF Bites:
@loopback0 said in WTF Bites:
@BernieTheBernie Considering how many security vulnerabilities get announced for Chrome
 here is blocking it from
here is blocking it from updating.... installing more fresh vulnerabilities plus some resurrected older vulnerabilities.
If you rotate the vulnerabilities on regular basis, the overall chance of getting hacked is lower.
-
@BernieTheBernie said in WTF Bites:
@loopback0 said in WTF Bites:
@BernieTheBernie Considering how many security vulnerabilities get announced for Chrome
 here is blocking it from
here is blocking it from updating.... installing more fresh vulnerabilities plus some resurrected older vulnerabilities.
If you rotate the vulnerabilities on regular basis, the overall chance of getting hacked is lower.
-
@izzion lower, not low.
-
If you rotate the vulnerabilities on regular basis, the overall chance of getting hacked is lower.
"Are we vulnerable to XSS attacks?"
"Let me check... No, that's on Fridays. Today it's buffer overflows."
-
@izzion lower, not low.
pats @Gąska on the forehead
It's cute that you think hackers / viruses don't just run from a toolkit that contains a massive library of known vulnerabilities.
-
It's cute that you think hackers / viruses don't just run from a toolkit that contains a massive library of known vulnerabilities.
Of course they do. But they're humans just like us, and their
 is as strong as ours, and I don't think those toolkits have auto-updaters (at least the ones I used didn't). So no hacker has all the exploits, but usually, if they have exploits for newer stuff, they also have exploits for older stuff. I haven't run the math, but intuitively, updating regularly to new shiny
is as strong as ours, and I don't think those toolkits have auto-updaters (at least the ones I used didn't). So no hacker has all the exploits, but usually, if they have exploits for newer stuff, they also have exploits for older stuff. I haven't run the math, but intuitively, updating regularly to new shiny backdoorshonest accidental bugs should shave a tiny margin off the total probability of getting hacked over a given period of time.
-
-
@HardwareGeek I am your mod.
-
inb4 we are all @boomzilla
-
I tried following links through Twitter to an article (no, that's not the
 , although...), starting from a post here (warning! this is a garage post!) and ending up on ITV's website.
, although...), starting from a post here (warning! this is a garage post!) and ending up on ITV's website.(actually I was just trying to have fun by checking if the article's title was botched or if it just was butchered by its inclusion in a tweet... the latter, apparently, but anyway it wasn't a funny-enough butchering to warrant posting -- also please no comment here on the content of that article, see the garage thread linked above for that)
Of course, I immediately got a big overlay about "eat our cookies." Well, that's still not the
 , this is (unfortunately) the norm nowadays.
, this is (unfortunately) the norm nowadays.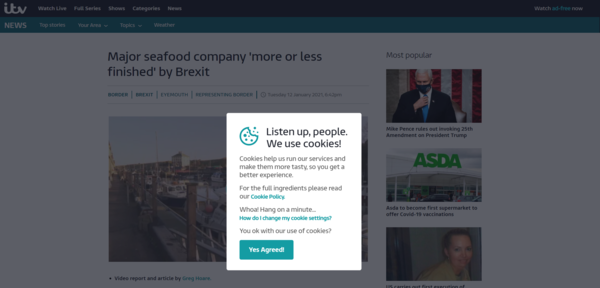
I'm sometimes sad for those poor developers who spent time writing all this code (they're probably JS devs so not really, but still), so I sometimes try to refuse all the cookies I can refuse, just for lulz. Let's see, no obvious button to do so here, so let's click on "how do I change my cookie settings?"
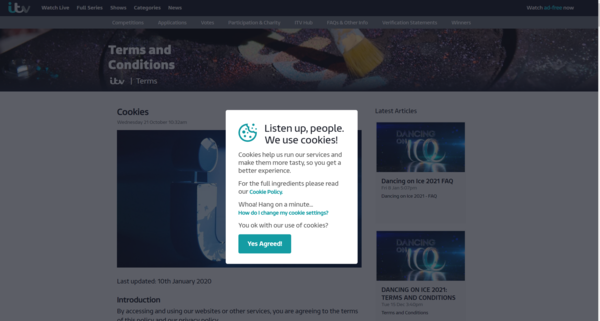
Of course. What else did I expect?

Note that I can still scroll through the underlying page (I could edit the DOM anyway or click on the button to get rid of the popup, but whatever) and see the actual instructions:
"you can block cookies from your browser, this will break our site, lol your fucked"
-
@remi most websites nowadays are unusable without clicking on reader mode. That immediately gets rid of overlays, videos, flashy sidebars and other JS garbage they spent all their time developing.
Oh, and then there's the fact that even after you've gone to "youronlinechoices.com" (or a handful of similar places "managing" your settings for a buttload of websites), if you actually denied whatever you can deny and enforce that by using browser's tracking protection, you still get these popups everywhere. Which do everything they can to hide the buttons for "deny" (on the phone it's sometimes really hard to click stuff that is literally off-screen and doesn't want to be scrolled), make it unclear which setting actually is "deny" or "allow", have 600 categories, or a "legitimate interest" category (from which I conclude all others are illegitimate) that can't be deactivated.
-
@topspin I always open YouTube in private mode*. Every day, it's something like 20 clicks before I can watch the first video.
No, I'm not going to install any stupid browser extensions.
*not counting video embeds elsewhere
-
@topspin I always open YouTube in private mode*. Every day, it's something like 20 clicks before I can watch the first video.
No, I'm not going to install any stupid browser extensions.
*not counting video embeds elsewhere
Yeah, it starts the video, 5 seconds later it displays a retarded pop-up, then rewinds the video back to the beginning. And then it shows another popup asking if I'm looking for the autoplay button.

-
inb4 we are all @boomzilla
But only one of us gets a notification whenever someone posts about it.
-
@boomzilla Is it @mikeTheLiar?
-
Oh, and then there's the fact that even after you've gone to "youronlinechoices.com" (or a handful of similar places "managing" your settings for a buttload of websites), if you actually denied whatever you can deny and enforce that by using browser's tracking protection, you still get these popups everywhere. Which do everything they can to hide the buttons for "deny" (on the phone it's sometimes really hard to click stuff that is literally off-screen and doesn't want to be scrolled), make it unclear which setting actually is "deny" or "allow", have 600 categories, or a "legitimate interest" category (from which I conclude all others are illegitimate) that can't be deactivated.
They use all sorts of tricks such as using random IDs for everything and a huge number of different websites. But if you can hit the first stage of the loader, the bit initially pulled in to set up the rest (at a fixed location because the real website code authors are lazy, and which cuts itself out of the page to make finding it hard), then the rest becomes defanged. The workaround for that from the main website side is to pull in the complex ad loader code from their own site rather than from a third party, but that's quite a bit more work to set up (as the code in question isn't static).
And if a site insists on not working after you do that, fuck 'em. Go elsewhere.
-
@loopback0 said in WTF Bites:
@boomzilla Is it mikeTheLiar?
Oh, stop it.
You should target @by-joining-this-group-you-agree-to-be-mentioned-randomly-for-no-reason-is-that-okay-yes-no instead.
Or maybe that's only supposed to go in its official thread...
-
@JBert I have been summoned, and so I appear.
-
@JBert I have being summoned and thus I have appeared.
-
-
-
@remi
@dangeRuss linked to Washington Post over :
:
Eat shit and die!
Worked for me in Incognito mode. You must be using a Microsoft Browser.
-
@HardwareGeek said in WTF Bites:
I would reply with the appropriate comment, but this is not garage.
-
@remi
@dangeRuss linked to Washington Post over :
:
Eat shit and die!
Yeah, those are (unfortunately) somewhat common. But my
 wasn't so much the "eat shit or die" dialog on ITV, rather the fact that if you click on the link that's supposed to explain why/how they use cookies, you have to accept the cookies before you can read it (the fact that you can't really disable cookies is just the cherry on the cake). It's basically the return of the shrink-wrap license, and it's still stupid and despicable.
wasn't so much the "eat shit or die" dialog on ITV, rather the fact that if you click on the link that's supposed to explain why/how they use cookies, you have to accept the cookies before you can read it (the fact that you can't really disable cookies is just the cherry on the cake). It's basically the return of the shrink-wrap license, and it's still stupid and despicable.
-
-
@remi
@dangeRuss linked to Washington Post over :
:
Eat shit and die!
 is they being able to detect private mode.
is they being able to detect private mode.
-
you have to accept the cookies before you can read it (the fact that you can't really disable cookies is just the cherry on the cake).
But in their case that's just a notification about "hey, we've stored cookies already. You can click ok now, it's a done deed anyway."
-
-
@Atazhaia note to self: don't buy Intel.
-
@topspin I didn't think Youtube allowed that kind of content
-
@Atazhaia note to self: don't buy Intel.
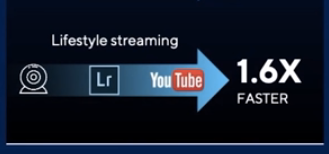
Even skipping the Lifestyle part,
 is up with that workflow? Webcam to Lightroom to YouTube? So I'm supposed to take still images with a webcam and make a slideshow of them?
is up with that workflow? Webcam to Lightroom to YouTube? So I'm supposed to take still images with a webcam and make a slideshow of them?
-
So I'm supposed to take still images with a webcam and make a slideshow of them?
FYI- Teams, being limited to roughly 15 FPS in some modes, does that for you for free.
-
Whoever wrote this really wanted an int.
-
Eat shit and die!
Only identified users can continue without identifying themselves.
-
Whoever wrote this really wanted an int.
I'm trying and failing to find the esoteric language where every instruction has a 50/50 chance of becoming a noop.
-
I'm trying and failing to find the esoteric language where every instruction has a 50/50 chance of becoming a noop.
There are probably others; that's just the first one my searching came up with. Somebody has "invented" an esolang for pretty much any restriction you could imagine on anything that comes close to being called a computer language.
-
@pcooper Let's see...
Hello, world!
This has a 0.000043% chance of running, which effectively means it will never run.Awesome! Although I wonder what the chance of the program running correctly is on top of that...
-
It's not the language I was thinking of (I'm sure it's older than that one), but close enough.
IIRC you could actually write a useful program in it if you used enough redundancy to make the chance of failure negligible, but to accomplish it you'd have to make sure all your functions were completely idempotent and call them excessively (which is why the snippet reminded me of it).
-
I'm trying and failing to find the esoteric language where every instruction has a 50/50 chance of becoming a noop.
One microcontroller actually had that exact hardware bug -- the probability was much lower than 50%, but it did randomly skip instructions. For extra fun, the effect was temperature-dependent: the colder it was, the higher the probability was.
I can only imagine how fun isolating that bug was.
-
@Zerosquare said in WTF Bites:
I'm trying and failing to find the esoteric language where every instruction has a 50/50 chance of becoming a noop.
One microcontroller actually had that exact hardware bug -- the probability was much lower than 50%, but it did randomly skip instructions. For extra fun, the effect was temperature-dependent: the colder it was, the higher the probability was.
I can only imagine how fun isolating that bug was.
Hipster microcontroller: executing instructions before it was cool

-
"Universal Windows Apps" (UWP) is really "universal":
Universality is reached by forcing the whole universe into the hole of downgrading to Windows 10.
Yeah, UNIVERSAL!
Even more universal than the "Universal Serial Bus" (USB).
-
-
@BernieTheBernie "Universal" in that they can run on Windows 10 desktop,
Windows RT, Windows Core for Things, Xbox One, Xbox Series,HoloLens, andWindows 10 Mobile.
-
@TwelveBaud IOW, it's like when .NET came out, Microsoft claimed it was cross-platform, as long as the platform was Windows
-
Here's a fun one. I have an https site which loads an image from the Google static map api. Every browser I have properly complains if I reference that api via http.
Chrome, safari, edge, and firefox for Mac: loads the image over either http or https.
IE and firefox for windows: will only load the image over http. Shows a broken image icon if https is used.
Since this is important and ie is required support (as we have clients who can't even run edge), I'm having to eat a browser warnings and insecurities. Fun times in single letter commits.
-
Add a bit of Javascript that reloads the image using http if the https version fails to load (or just hardcode it to detect IE specifically)?

