WTF is happening with Windows 11? And nothing else
-
@Benjamin-Hall said in WTF is happening with Windows 11? And nothing else:
@topspin said in WTF is happening with Windows 11? And nothing else:
TPMs are an anti-feature that you’d want to disable in the bios
<serious> Why? What's wrong with them? I don't think I know enough to make an informed decision, but from the vague bits I know, it seems like a reasonable increase in security vs boot-based persistent threats.</serious>
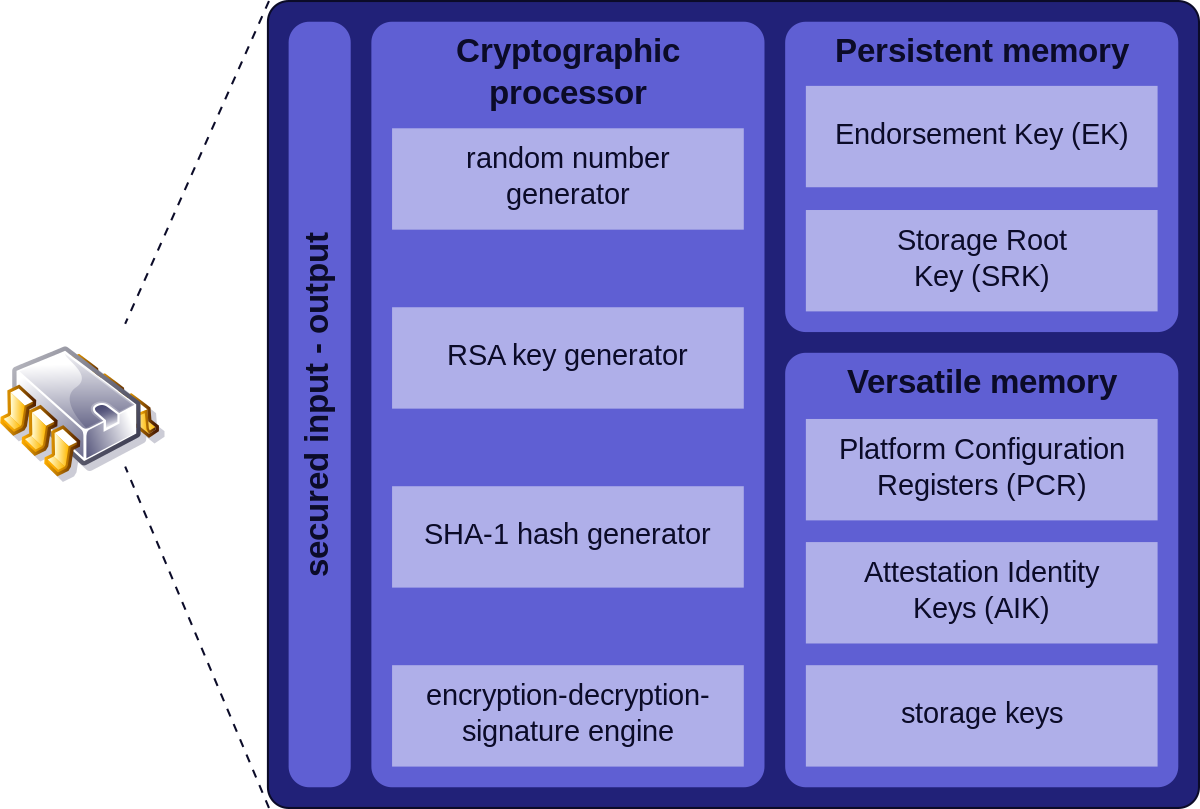
A hardware module for storing keys and calculating hashes. On a... looks through Wikipedia page ...an SPI bus, so the speed is on par with USB 1.0 at best. So you're not going to push the Windows kernel through it at boot time.
At the same time, it has a globally unique, standardized identifier. In hardware. That "can't be forged". So that even if you try to run that government-mandated tool in a virtual machine, your physical machine can still be identified and reported.

-
@acrow said in WTF is happening with Windows 11? And nothing else:
So that even if you try to run that government-mandated tool in a virtual machine, your physical machine can still be identified and reported.
I don't think this is true, since TPM can be emulated in software:
Virtual TPM- Google Compute Engine offers virtualized TPMs (vTPMs) as part of Google Cloud's Shielded VMs product.
- The libtpms library provides software emulation of a Trusted Platform Module (TPM 1.2 and TPM 2.0). It targets the integration of TPM functionality into hypervisors, primarily into Qemu.
-
@Zerosquare said in WTF is happening with Windows 11? And nothing else:
@acrow said in WTF is happening with Windows 11? And nothing else:
So that even if you try to run that government-mandated tool in a virtual machine, your physical machine can still be identified and reported.
I don't think this is true, since TPM can be emulated in software:
Virtual TPM- Google Compute Engine offers virtualized TPMs (vTPMs) as part of Google Cloud's Shielded VMs product.
- The libtpms library provides software emulation of a Trusted Platform Module (TPM 1.2 and TPM 2.0). It targets the integration of TPM functionality into hypervisors, primarily into Qemu.
In which case the ID identifies it as one of such. They all get, at the bottom of it, a burned-in or maybe maybe startup generated ID.
-
@acrow said in WTF is happening with Windows 11? And nothing else:
a virtual machine
(inb4 404)Chapter 5 Virtual MachineMicrosoft recognizes that the user experience when running the Windows 11 in virtualized environments may vary from the experience when running non-virtualized. So, while Microsoft recommends that all virtualized instances of the Windows 11 follow the same minimum hardware requirements as described in Section 1.2, the Windows 11 does not apply the hardware-compliance check for virtualized instances either during setup or upgrade. Note that... fuh-fuh-fuhI would assume that includes trusted TPM module.
-
@Applied-Mediocrity said in WTF is happening with Windows 11? And nothing else:
I would assume that includes trusted TPM module.
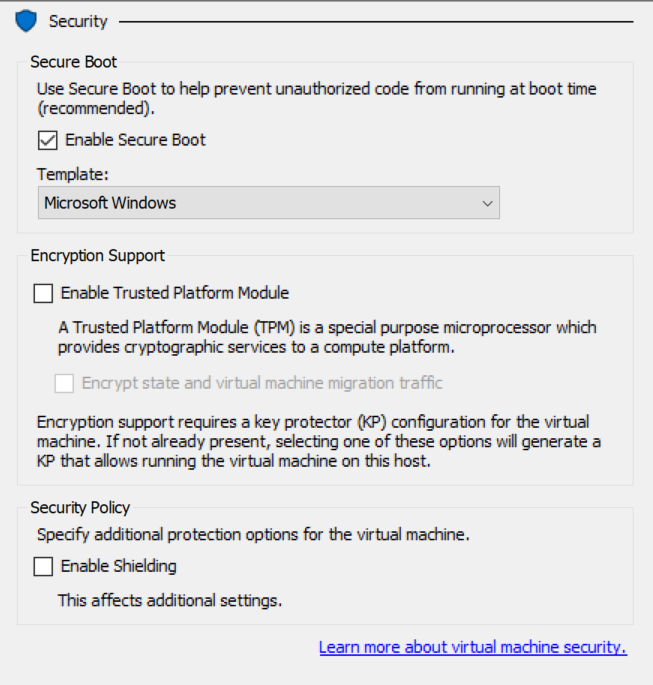
I wouldn't... (VM settings in Hyper-V)
-
@dcon It seems you might be right.
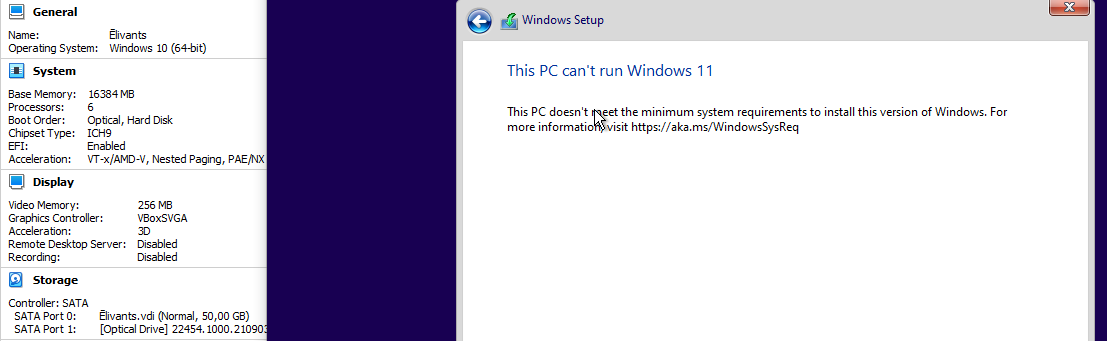
I picked the wrong ISO when doing Science. Build 22454 cannot be installed on VirtualBox VM anymore.
-
@Applied-Mediocrity said in WTF is happening with Windows 11? And nothing else:
@dcon It seems you might be right.
I picked the wrong ISO when doing Science. Build 22454 cannot be installed on VirtualBox VM anymore.
Science harder!
-
@Gribnit Go fetch me ze brain, Igor
-
@Applied-Mediocrity said in WTF is happening with Windows 11? And nothing else:
@Gribnit Go fetch me ze brain, Igor
...
Right away!
(Leaves. Pause. Sound of shattering glass. Returns with brain. Jar is very clean.)
-
This PC can't run Windows 11
This PC is immune from Windows 11

-
@Zerosquare said in WTF is happening with Windows 11? And nothing else:
This PC can't run Windows 11
This PC is immune from Windows 11

 This PC can't run Windows 11.
This PC can't run Windows 11.
 Everyone in my family runs Windows 10.
Everyone in my family runs Windows 10.
 No one runs in your family, you obese piece of shit.
No one runs in your family, you obese piece of shit.
-
@dcon OK, I've ignored the whole Secure Boot / TPM thing. Any tl;dr on wtf those are supposed to do?
To elaborate a bit. From what I understand, Secure Boot checks that the bootloader is officially blessed, and is supposed to ensure that everything from then on is running the "right" code. TPM stores stuff like crypto keys in HW and apparently has some sort of unique ID, ostensibly making it more difficult to extract said keys (and apparently faking that unique ID).
Now, because of Windows 11 & secure boot, I briefly read up on the Linux side of things. Based on that, there are apparently two ways of dealing with it. First, there's an officially blessed "shim" that would then load the (AFAIK unsigned) kernel. Secondly, you can -at least on some motherboards- add your own keys to the secure boot thing, so that you can sign your kernel etc. (The latter seems potentially useful, as you use it to further harden your own machine. Not sure how far that goes, though.)
But, OK, what's the reason MS wants it to exist so badly? E.g., this video (warning LTT) discusses that Riot wants to use it to prevent cheating. But is that really in the scope of that tech?
Specifically, you can apparently emulate both Secure Boot and TPM (as shown in the screenshot). Now, the client OS can detect that it's running in a virtualized environment in this case.I did read about there being hypervisors/virtualization solutions that are designed to be undetectable by the clients (I don't remember exactly where, but at the time, I didn't really see much reason to doubt that claim). In that case, the latter kinda falls flat on its face again?
(Aside from that ... there are piles of devices that can muck with the RAM directly e.g. across PCIe. Is there anything preventing one of those being used to subvert the system after it's been started?)
-
@cvi said in WTF is happening with Windows 11? And nothing else:
OK, I've ignored the whole Secure Boot / TPM thing. Any tl;dr on wtf those are supposed to do?
It's another step in the game of walls and ladders between people wanting to run code on your machine and people wanting to prevent your machine from running said code, but those are two different technologies. Most of what I know about them I had learned from Matthew James Garret's blog, e.g. here.
From what I understand, Secure Boot checks that the bootloader is officially blessed, and is supposed to ensure that everything from then on is running the "right" code.
Yes, Secure Boot is just good old offline signature verification. Ostensibly, you as the owner of the device would enrol your public key into it and sign the bootloader with the private key. The bootloader (and everything above it) is smart and also verifies signatures of everything (including, say, kernel modules) before running it. (Also, hibernate on Linux is disabled because nobody bothered to perform any signing or verification on the hibernation image.)
This way we supposedly thwart the Evil Maid attack where someone patches or replaces a small part of the boot chain while we're away from the device. The device just plain refuses to boot and the Maid is foiled!
Except they can replace the whole device if they're really after you. Or replace part of it that stores allowed certificates. You'll just type in your full disk encryption key and it's game over. Here's where TPM comes in.
TPM stores stuff like crypto keys in HW and apparently has some sort of unique ID, ostensibly making it more difficult to extract said keys (and apparently faking that unique ID).
TPM stores encryption keys and makes it really hard to extract them unless you can present something to it. For example, boot the system to a known good state and present the hash of that state to the TPM. Years ago I read that Microsoft wants to push BitLocker by default on newer Windows laptops, and TPM is perfect for storing the encryption key: either we're booting a good, untampered system (in which case we can let it decrypt the volume and rely on it to verify the user's password) or something is amiss and we fail to boot.
(Note to self: TPM-based randomware. Hmm.)
TPM can also let the device authenticate itself to you (that's the part where the unique ID is "impossible" to duplicate), kinda preventing the Evil Maid 2.0 attack (the tampered device won't be able to obtain the function of the ID from the TPM and present it to you a-la TOTP to verify on your smartphone) or to some remote party (classified work VPN? DRM? lots of possibilities here).
What if they install a passive keylogger? Well, then you're screwed. Next time you leave, they'll just type your user password.
First, there's an officially blessed "shim" that would then load the (AFAIK unsigned) kernel.
I thought it had to be signed. But then modules have to be signed too, and some insecure stuff doesn't work.
I did read about there being hypervisors/virtualization solutions that are designed to be undetectable by the clients (I don't remember exactly where, but at the time, I didn't really see much reason to doubt that claim). In that case, the latter kinda falls flat on its face again?
As long as it raises the cost of an attack, it's somewhat useful. Will likely be used for BitLocker. We might get some interesting DRM, but Matthew argues it's impractical.
(Aside from that ... there are piles of devices that can muck with the RAM directly e.g. across PCIe. Is there anything preventing one of those being used to subvert the system after it's been started?)
I think we have IOMMUs against that, at least until the next Razer mouse.
-
@aitap Ok, that makes (mostly) sense. Thanks!
I thought it had to be signed. But then modules have to be signed too, and some insecure stuff doesn't work.
Hmm, ok. I admit I mostly just skimmed the part with the shim. But where I read it was specifically for Gentoo, where you are expected to compile your own kernel + modules. Since you won't get that signed with any sort of official key, I assumed that the shim would boot an unsigned kernel. But I might be wrong about that.
I think we have IOMMUs against that,
OK - different approach. Malicious RAM modules that let you poke the RAM contents directly. To be fair, that also raises the cost of the attack just a tiny bit. (Keyloggers are a bit passe - did those decades ago in school.)
-
@aitap said in WTF is happening with Windows 11? And nothing else:
Years ago I read that Microsoft wants to push BitLocker by default on newer Windows laptops, and TPM is perfect for storing the encryption key: either we're booting a good, untampered system (in which case we can let it decrypt the volume and rely on it to verify the user's password) or something is amiss and we
fail to bootask the user to type in the 48 digit recovery key.Which I have to do almost every time I boot my Windows partition (once a month so IT doesn't brick the install). That's what happens when Ubuntu does system updates.
-
@cvi said in WTF is happening with Windows 11? And nothing else:
(Keyloggers are a bit passe - did those decades ago in school.)
 : This is going on your permanent record, young man.
: This is going on your permanent record, young man.
-
@cvi said in WTF is happening with Windows 11? And nothing else:
Since you won't get that signed with any sort of official key, I assumed that the shim would boot an unsigned kernel. But I might be wrong about that.
The shim contains the public key of your distro -- for Gentoo, this is likely the bootstrap environment from before you compile your own world. You can, and for those distros are expected to, create your own key and enroll it in the shim's database, verify it during first boot, and sign the kernel and modules you build. You could also enroll your key directly in your EFI since, because legal reasons, Microsoft can't contractually obligate x86-based PC manufacturers from preventing you, and e.g. the military needs to be able to add their keys so the vendors "have to" make that available. But adding keys to the shim is easier.
-
I must be the only person here dual-booting by selecting the boot medium via BIOS menu at start-up. I got tired of Windows and Ubuntu complaining about each other.
Now if only the motherboard supported manually selecting boot drive on every startup. Now I have to bang a key.
-
@acrow said in WTF is happening with Windows 11? And nothing else:
Now I have to bang a key.
Wanted to avoid having to do that. I've not had too many issues with using two separate drives, i.e., one with the bootloader for Linux and one for Windows. Bootloader for Linux is the bios/efi boot drive and has an option to chainload Windows (grub).
No secure boot, though. CBA for now. Using two separate drives solved the issue of Windows occasionally nuking the bootloader.
-
@cvi said in WTF is happening with Windows 11? And nothing else:
Using two separate drives solved the issue of Windows occasionally nuking the bootloader.
That too. Wondering how long this system lasts until I have to hunt for a motherboard that supports locking out the Linux disk while Windows is running. I wouldn't put it past Windows 11 to "helpfully" nuke any competitors' drives and add the storage to its own pool.
We have detected unused drive space, which could be used for Update Boost. Would you like to use it?
[Yes] / [Yes (but without telling me)]
-
@acrow Need a physical switch to select between drives.

(OK, sata or m.2 might require a bit more than two lanes, so, the switch might need to be a tiny bit larger.)
-
@cvi said in WTF is happening with Windows 11? And nothing else:
(OK, sata or m.2 might require a bit more than two lanes, so, the switch might need to be a tiny bit larger.)
 The data bus, sure. The power bus, now... I think most SATA SSDs only use the 5V pin on the power cable...
The data bus, sure. The power bus, now... I think most SATA SSDs only use the 5V pin on the power cable...
-
@acrow said in WTF is happening with Windows 11? And nothing else:
We have detected unused drive space, which could be used for Update Boost. Would you like to use it?
[Yes] / [Yes (but without telling me)]All your volumes are where you left them.

-
@acrow said in WTF is happening with Windows 11? And nothing else:
I must be the only person here dual-booting by selecting the boot medium via BIOS menu at start-up. I got tired of Windows and Ubuntu complaining about each other.
When I got my current computer the drives were set up in some kind of RAID thing. Even though there was just the m2 and the spinning rust. I had to turn that off in the BIOS to install my SSDs with Linux on it. Now Windows doesn't want to boot because apparently when I turned that off it didn't think it should be turned off.
So I haven't actually booted into Windows since.
-
@boomzilla When you got a presumably second-hand (if it had RAID like that) computer, your first action wasn't to nuke and repave?

-
@acrow the disks weren't in RAID. But some Intel disk controller bullshit was in "RAID mode." I had SSDs from my previous computer that I plugged in from my previous system. I really didn't need the disks that came with the system, but hey, it's there. Could be handy!
-
@aitap said in WTF is happening with Windows 11? And nothing else:
I think we have IOMMUs against that
IOMMU is fun. Although last time I enabled it Windows refused to boot until I turned it off because
 . Even though the secondary benefit of having it on is that it adds another layer of security. You know, the thing that MS loves so much, allegedly.
. Even though the secondary benefit of having it on is that it adds another layer of security. You know, the thing that MS loves so much, allegedly.
-
@acrow said in WTF is happening with Windows 11? And nothing else:
@boomzilla When you got a presumably second-hand (if it had RAID like that) computer, your first action wasn't to nuke and repave?

Pretty sure it was RAID vs AHCI:
For whatever reason, I couldn't boot from my Linux disk in RAID mode and Windows doesn't seem to like AHCI.
-
@aitap said in WTF is happening with Windows 11? And nothing else:
randomware
Finally, a proper name for the things I develop.
-
@Zerosquare said in WTF is happening with Windows 11? And nothing else:
TPM can be emulated in software
However, this doesn't always work well. For a while, I had a work laptop that required the Bitlocker recovery key every single time I woke it from sleep, because it didn't play nice with the emulated TPM.
-
@boomzilla said in WTF is happening with Windows 11? And nothing else:
Windows doesn't seem to like AHCI.
It usually does, but only when that mode is selected and active while Windows' bare-metal installer is running. Trying to rehabilitate an existing install doesn't actually work -- even though it should -- because Intel's drivers are crap.
-
@TwelveBaud ahhh....I guess that would be it then, because I recall switching over to AHCI in Windows, too.
Fortunately, nothing of value has been lost.
-

-
@acrow said in WTF is happening with Windows 11? And nothing else:
We have detected unused drive space, which could be used for Update Boost. Would you like to use it?
[Yes] / [Yes (but without telling me)]One one of my more limited PCs, there literally wasn't enough space to even download the update, much less copy it the three times it does when installing.
Windows asked me to plug in a flash drive to do the update.
I said

-
@boomzilla said in WTF is happening with Windows 11? And nothing else:
When I got my current computer the drives were set up in some kind of RAID thing.
Ah, yes, intel storage soft raid what-the-fuckall.
Which, even if you're not actually doing a RAID will still tell the OS it's RAID and things get... interesting.
-
@TwelveBaud said in WTF is happening with Windows 11? And nothing else:
@boomzilla said in WTF is happening with Windows 11? And nothing else:
Windows doesn't seem to like AHCI.
It usually does, but only when that mode is selected and active while Windows' bare-metal installer is running. Trying to rehabilitate an existing install doesn't actually work -- even though it should -- because Intel's drivers are crap.
I've had pretty good success moving controllers at least, and what's more
 is changing VM's controllers to/from VirtIO. It's finicky, but works when the stars are correctly off-kilter.
is changing VM's controllers to/from VirtIO. It's finicky, but works when the stars are correctly off-kilter.
-
@Tsaukpaetra said in WTF is happening with Windows 11? And nothing else:
I've had pretty good success moving controllers at least
So it didn't turn the neighbourhood into a smoking crater?
-
@Zerosquare said in WTF is happening with Windows 11? And nothing else:
But TPM support isn't the only requirement for Windows 11. You also need a CPU that's explicitly listed as supported. And a number of "powerful enough, and not that old" CPUs are not included in this list.
Even the official Windows 10 supported CPU list only goes back to 5th gen Intel Core, even though it happily installs and runs on much older.
The compatibility list for Windows 11 just controls which computers Microsoft will offer the upgrade via Windows Update. You can, if you so wish, just create a Windows 11 USB drive and install it yourself.
-
@topspin said in WTF is happening with Windows 11? And nothing else:
@Applied-Mediocrity said in WTF is happening with Windows 11? And nothing else:
@Atazhaia said in WTF is happening with Windows 11? And nothing else:
At least anyone with a Ryzen CPU will have a TPM as it's built into the CPU itself
Ass-us recent (at least June 2021) BIOS updates are now enabling it by default. Probably others do, too.
I guess that’s the end-game here?
TPMs are an anti-feature that you’d want to disable in the bios but Windows requiring it forces you to have it enabled?TPM has also been a requirement for computers which come with Windows pre-installed since 2016. It's only a new requirement for enthusiast-built computers.
-
@loopback0 I guess I should repeat that I was just speculating out of a semi-uninformed position.
(The question marks didn’t make that particularly clear and I didn’t remember that the post that started this train of thought for me where I asked if it’s mostly a DRM only anti-feature was actually in another thread)
-
@topspin I hadn't caught up when I replied, because that's

-
@dkf said in WTF is happening with Windows 11? And nothing else:
@Tsaukpaetra said in WTF is happening with Windows 11? And nothing else:
I've had pretty good success moving controllers at least
So it didn't turn the neighbourhood into a smoking crater?
No, Network Neighborhood was destroyed when lightning struck the token ring.
-
@Tsaukpaetra said in WTF is happening with Windows 11? And nothing else:
@dkf said in WTF is happening with Windows 11? And nothing else:
@Tsaukpaetra said in WTF is happening with Windows 11? And nothing else:
I've had pretty good success moving controllers at least
So it didn't turn the neighbourhood into a smoking crater?
No, Network Neighborhood was destroyed when lightning struck the token ring.
It probably just knocked the token loose. Check behind stuff.
-
@Tsaukpaetra said in WTF is happening with Windows 11? And nothing else:
(https://dilbert.com/strip/1996-05-02)token ring
-
If it's a tolkien ring, you better hope it didn't fall into a volcano.
-
-
@boomzilla said in WTF is happening with Windows 11? And nothing else:
Love the little disclaimer at the bottom "don't use this for real lol" when you KNOW you're writing that article for people who want to defeat the protections for real because their computer has a
 or they're too
or they're too  about M$ and automatically assume all new M$ features are th3 3v1ls.
about M$ and automatically assume all new M$ features are th3 3v1ls.
-
@izzion Eh. I might take a look if I ever get to the point of needing to install Windows 11. Too
 to dick around with secure boot (running a locally built kernel). I'm sure it's doable, but not dealing with it seems easier.
to dick around with secure boot (running a locally built kernel). I'm sure it's doable, but not dealing with it seems easier.Not that concerned about evil maids at home. Not like I can afford one, evil or not.
-
@cvi said in WTF is happening with Windows 11? And nothing else:
OK, I've ignored the whole Secure Boot / TPM thing. Any tl;dr on wtf those are supposed to do?
DRM. Or at least that's the reason Windows 11 requires it
-
@Applied-Mediocrity
 is like
is like  or the popular or irl version of
or the popular or irl version of 
PS: you have to read this as emojis as well as by :their_name: to get the full experience!
 Trusted Platform Module - Wikipedia
Trusted Platform Module - Wikipedia