Symantec email exploit bites Symantec
-
@cheong ads? what're those?
-
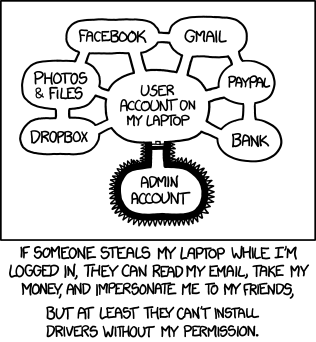
I'm not sure what all the excitement is about running as an administrator.
Viruses don't need to do that to cause lots of damage.
- Your computer can be used as a spam bot or the like with your everyday account, and
- If any of your files are accessible (which they probably are if you do anything useful with your computer) then malware can delete, upload copies, or encrypt all of your files.
No admin privileges needed to do a lot of damage.
So a good AV scanner is needed, but not the crap that auto-executes the viruses for you...
-
@quijibo running as administrator can allow it to dig its hooks in much deeper though, making it harder to detect, and harder if not impossible to remove without wiping the drive and reinstalling the OS.
-
@quijibo said in Symantec email exploit bites Symantec:
a good AV scanner is needed
Now if someone could just invent one of those...
-
@anotherusername You see there is Advertisement that hosted in Yahoo sites? Some malicious people registered the Ad hosting service and placed some Flash with content that can trigger Flash player related vulnerabilities. If you visit that site without Flash disabled, no matter you visit via Chrome or IE, even if you do not click on the Ads, the ransomeware will be executed on your system, encrypting your files and demands you money to get back the key for decryption.
This first happens on Yahoo Japan and a few months later also in Yahoo Taiwan.
-
@cheong Which is of course why browsing the Web without a comprehensive ad blocker installed, in 2016, is an act of suicidal optimism.
-
@error said in Symantec email exploit bites Symantec:
Or fucking CNET.
I was amused to discover, having installed uBlock Origin for the first time, that it put up a huge scary warning page when I then tried to download Panda Free Antivirus. For reasons I cannot begin to imagine, the Panda folks thought that download.cnet.com would make a fine and dandy distribution platform for their product.
-
@ben_lubar said in Symantec email exploit bites Symantec:
@Maciejasjmj said in Symantec email exploit bites Symantec:
I have yet to see software that would infect my PC without me taking any stupid action
Basically:
- Don't disable UAC
- If UAC pops up, PAY ATTENTION TO WHICH PROGRAM IT SAYS
Impossible, absolutely. Do you? If you do you are into dwarfs and such
- Keep software up to date
Yes
Do not click on just anything you see in email
Block ads
Do not run random software you find in da Internetz from helpful Russian websites to boost the performance of your PC- End result: no viruses
Yes. I have not had problem with viri for 20 years. No anti-virus ever, and no thanks to UAC either.
-
@cheong said in Symantec email exploit bites Symantec:
Don't visit Yahoo
Good advice.

@cheong said in Symantec email exploit bites Symantec:
Their Ads can contain ransomware that infect your computer via Flash related vulnerability.
- Adblock.
- Flashblock.
- My new laptop at home doesn't even have Flash installed. It's 2016, why would I want that?
-
@another_sam said in Symantec email exploit bites Symantec:
It's 2016, why would I want that?
There's a few sites where it's necessary. :( Fortunately they don't carry ads (for others) and I use a whitelist. :)
-
@lucas1 said in Symantec email exploit bites Symantec:
@Tsaukpaetra I still mourning the loss of
> edit myfile.txtStill one of my favourite text editors.
It is a source of dismay that Windows 10 for x64 does not have a built-in copy of EDLIN.
-
@Steve_The_Cynic I've had to rely on something filthy i.e. vim being installed as a quick command line editor. Or having to pipe something to notepad.
-
@Steve_The_Cynic said in Symantec email exploit bites Symantec:
It is a source of dismay that Windows 10 for x64 does not have a built-in copy of EDLIN.
Wikipedia tells me that I should be glad that I included the qualifier "for x64". 32-bit builds of Windows NT-derived systems, up to and including Windows 10, do, apparently, include a version of EDLIN.
-
@Steve_The_Cynic Yes. It would have been nice if they had rebuilt those apps with a 64bit compiler (it may of not been possible).
-
@lucas1 The word is that in the 32-bit builds, it's actually still an MS-DOS executable, not a Win32 executable. (Approximately MS-DOS 5.0.)
-
@Steve_The_Cynic Oh that makes a lot more sense. My brain has been sullied by doing a Linux from Scratch and Gentoo build when at university (I didn't have a girlfriend at the time to distract me from such fruitless pursuits).
-
@cheong
 I was adding the obligatory "I use adblock, what are these 'ads'?" reply.
I was adding the obligatory "I use adblock, what are these 'ads'?" reply.
-
@lucas1 said in Symantec email exploit bites Symantec:
doing a Linux from Scratch and Gentoo build when at university (I didn't have a girlfriend at the time to distract me from such fruitless pursuits).
Methinks the latter the former makes.
-
@dkf said in Symantec email exploit bites Symantec:
There's a few sites where it's necessary.
I have a keyboard shortcut to deal with them. It's Ctrl-W.
-
@lucas1 said in Symantec email exploit bites Symantec:
(it may of not been possible).
@lucas1 said in Symantec email exploit bites Symantec:
(it may of not been possible).
@lucas1 said in Symantec email exploit bites Symantec:
(it may of not been possible).
@lucas1 said in Symantec email exploit bites Symantec:
(it may of not been possible).
-
@another_sam said in Symantec email exploit bites Symantec:
I have a keyboard shortcut to deal with them. It's Ctrl-W.
Life's not always that kind. Why our online timesheet system needs Flash I don't know, and I don't care. OTOH, not much else needs it either. (A whitelist isn't very good if it isn't kept short…)
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
Apparently as of Windows 10 it doesn't work, huh. Would have to check the Win8 VM I have somewhere
Given how many people freaked out about what they insisted wasn't a security problem, they probably just disabled it to shut them up.
-
@another_sam If you have Edge or Chrome installed, Flash renderer is built-in. You have to manually disable it yourself.
-
@cheong said in Symantec email exploit bites Symantec:
If you have Edge or Chrome installed, Flash renderer is built-in. You have to manually disable it yourself.
I have for a while been considering trying Chrome, now I've changed my mind.
-
@quijibo said in Symantec email exploit bites Symantec:
I'm not sure what all the excitement is about running as an administrator.
Viruses don't need to do that to cause lots of damage.
- Your computer can be used as a spam bot or the like with your everyday account, and
- If any of your files are accessible (which they probably are if you do anything useful with your computer) then malware can delete, upload copies, or encrypt all of your files.
No admin privileges needed to do a lot of damage.
So a good AV scanner is needed, but not the crap that auto-executes the viruses for you...
-
@error I want an OS where programs can only open files that either they created or that were opened using an OS-provided file chooser dialog.
-
@ben_lubar You mean, like Modern UI Windows apps?

-
@ben_lubar said in Symantec email exploit bites Symantec:
@error I want an OS where programs can only open files that either they created or that were opened using an OS-provided file chooser dialog.
-
@ben_lubar said in Symantec email exploit bites Symantec:
@error I want an OS where programs can only open files that either they created or that were opened using an OS-provided file chooser dialog.
You mean Android as of version 5.0?
-
@Tsaukpaetra said in Symantec email exploit bites Symantec:
@ben_lubar said in Symantec email exploit bites Symantec:
@error I want an OS where programs can only open files that either they created or that were opened using an OS-provided file chooser dialog.
You mean Android as of version 5.0?
You mean Linux was doing what I wanted all this time?
-
@ben_lubar said in Symantec email exploit bites Symantec:
@Tsaukpaetra said in Symantec email exploit bites Symantec:
@ben_lubar said in Symantec email exploit bites Symantec:
@error I want an OS where programs can only open files that either they created or that were opened using an OS-provided file chooser dialog.
You mean Android as of version 5.0?
You mean Linux was doing what I wanted all this time?
No. Because it's not a Linux behaviour .It's an Android behaviour .
-
@ben_lubar said in Symantec email exploit bites Symantec:
@error I want an OS where programs can only open files that either they created or that were opened using an OS-provided file chooser dialog.
You can if you use Linux with SELinux enabled, provided your programs saves file to different directory and you take time to tune the privilege settings for those directories.
-
@FrostCat A bit different, if it can trick you to run it, it can also access folders like Photo or Music (Although access to these locations have to be declared, who read these boilerplate text?
 ).
).
-
@cheong said in Symantec email exploit bites Symantec:
You can if you use Linux with SELinux enabled, provided your programs saves file to different directory and you take time to tune the privilege settings for those directories.
And you only use filesystems that support the SELinux attributes.
-
@cheong said in Symantec email exploit bites Symantec:
You can if you use Linux with SELinux enabled
Why on Earth would I want to do that?
-
@anotherusername said in Symantec email exploit bites Symantec:
@anonymous234 said in Symantec email exploit bites Symantec:
@Maciejasjmj said in Symantec email exploit bites Symantec:
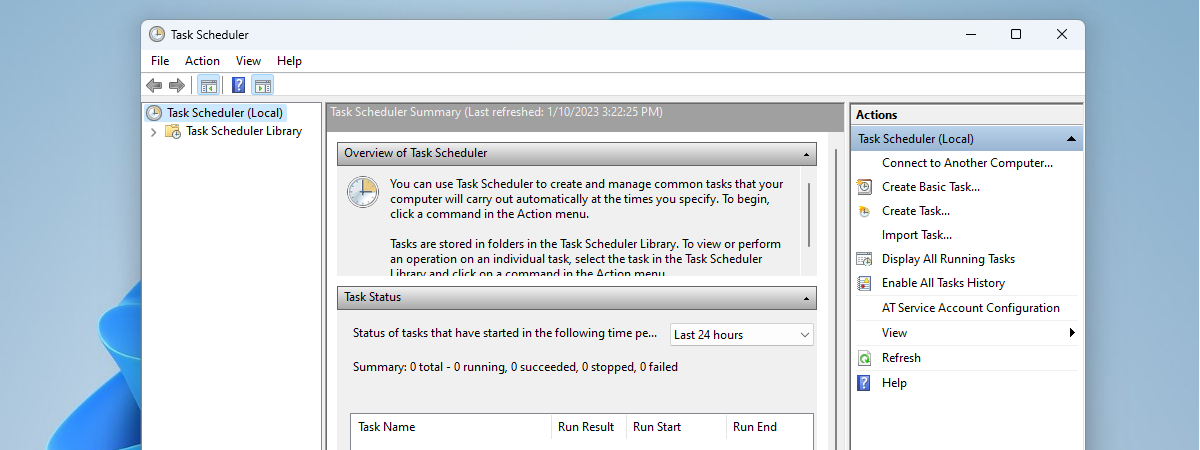
UAC is generally bypassable via Task Scheduler shenanigans
Really? That would be a major Windows vulnerability.
I'm probably not the first one to say this, but this requires to be running with administrative permissions in the first place...
-
@ben_lubar said in Symantec email exploit bites Symantec:
@error I want an OS where programs can only open files that either they created or that were opened using an OS-provided file chooser dialog.
I don't.
-
@Medinoc said in Symantec email exploit bites Symantec:
@anotherusername said in Symantec email exploit bites Symantec:
@anonymous234 said in Symantec email exploit bites Symantec:
@Maciejasjmj said in Symantec email exploit bites Symantec:
UAC is generally bypassable via Task Scheduler shenanigans
Really? That would be a major Windows vulnerability.
I'm probably not the first one to say this, but this requires to be running with administrative permissions in the first place...
Yes, like installing something does. So you install it with administrator privileges and then it
bugs you every damn time it needs to do its shitdoes its thing silently without any annoying popups to re-authorize it.
-
@Medinoc said in Symantec email exploit bites Symantec:
this requires to be running with administrative permissions in the first place
At work, for the last 2-3 years, I have deliberately NOT run as an administrator, because most of my clients don't. It helps me to find problems they might otherwise run into.
-
@Medinoc said in Symantec email exploit bites Symantec:
I'm probably not the first one to say this, but this requires to be running with administrative permissions in the first place...
Well duh but the point of it is it doesn't require elevation.
-
@Steve_The_Cynic said in Symantec email exploit bites Symantec:
@cheong said in Symantec email exploit bites Symantec:
You can if you use Linux with SELinux enabled
Why on Earth would I want to do that?
For a record, I did that when I was a Linux server administrator.
All you need is to allow it to run in permissive mode for a week or so, then collect the log and make adjustment to the directory permissions. I rarely need to adjust the permission thereafter.
-
@blakeyrat So does starting a service running with LocalSystem account from a regular user account, when you set the ACL of the service to be start-able by normal user. That don't require elevation either.
-
@blakeyrat said in Symantec email exploit bites Symantec:
@Medinoc said in Symantec email exploit bites Symantec:
I'm probably not the first one to say this, but this requires to be running with administrative permissions in the first place...
Well duh but the point of it is it doesn't require elevation.
But setting it up does, so it's not in and of itself a security flaw.
It's just the equivalent of making a programsetuid rooton Unix systems: it's only unsafe is the program is (which it automatically is if it wasn't designed specifically forsetuid rootin the first place).
-
@Medinoc setting it up doesn't require elevation. Just logging in as an administrator.
The whole point of UAC is that logging in as an administrator doesn't willy nilly allow processes to elevate. UAC is designed so that you can use an admin account and processes that you start aren't supposed to be elevated unless you confirm a UAC prompt.
-
@another_sam said in Symantec email exploit bites Symantec:
@cheong said in Symantec email exploit bites Symantec:
If you have Edge or Chrome installed, Flash renderer is built-in. You have to manually disable it yourself.
I have for a while been considering trying Chrome, now I've changed my mind.
It also blocks by default IIRC so... yeah
-
@candlejack1 said in Symantec email exploit bites Symantec:
@Maciejasjmj said in Symantec email exploit bites Symantec:
@kt_ My antivirus strategy generally consists of common sense. I have yet to see software that would infect my PC without me taking any stupid action, and I have yet to see an antivirus that would convince me not to run this piece of software I just willingly downloaded. Either I won't download it in the first place, or I'll figure it's one of a billion false positives.
There were situations were viruses that attack IPs at random would find flaws in your system, if you connected directly to the internet, it happened to WinXP.
This is one of the rare cases in which a home router would actually save you as attacking an IP at random would hit the router and not the devices behind it.
-
@cheong said in Symantec email exploit bites Symantec:
you take time to tune the privilege settings
You're saying we need to check our privilege?
-
@anotherusername said in Symantec email exploit bites Symantec:
setting it up doesn't require elevation. Just logging in as an administrator.
Logging in as administrator is a form of elevation. Maybe not the one you were thinking of, but it's definitely on that scale.
-
@powerlord exactly what does a home router do differently here? The only thing I can think of is the firewall they usually come with that is enabled by default.
-
@error There is a command audit2allow that will check the log files to help you adjust the SELinux policy so SELinux won't get in the way of your daily activities.