Symantec email exploit bites Symantec
-
Not sure if this has been posted or not yet. It isn't not brand new, but it's not even 2 months old yet and I haven't seen anything about it on here, so here we go:
Researchers at Google found an arbitrary code execution exploit against Symantec's antivirus scanner, including the module that automatically scans emails for malware. The best part: when they sent the POC to Symantec, it tried to scan the attachment containing the exploit POC, which then crashed their email server!
I know that at this point, making fun of Symantec suckiness is like shooting fish in the barrel of circular swimming, but this is a real WTF even by Symantec standards...
-
@masonwheeler funny how installing an antivirus can increase the attack surface of your computer...
-
I've always found that most major antivirus products behave more like viruses themselves.
Edit: Tried to upload the EICAR test file to Nod
 just for shits and giggles... but Symantec keeps deleting it on my end.
just for shits and giggles... but Symantec keeps deleting it on my end.
-
-
-
Am I correct in thinking it's the same vulnerability as this?
-
@anotherusername said in Symantec email exploit bites Symantec:
Am I correct in thinking it's the same vulnerability as this?
*sigh* Looks like I got
 'd.
'd.
-
@masonwheeler maybe so, but yours is funny because it mentions the fact that the guy who tried to email the POC to Symantec triggered the bug and crashed their server.
-
@anotherusername said in Symantec email exploit bites Symantec:
Fun fact: Chrome will load it up just fine, but actually saving it is a no-no.
-
@Tsaukpaetra fun fact: it's a valid DOS executable.
-
@anotherusername said in Symantec email exploit bites Symantec:
valid DOS executable.
Doh! Apparently WOW doesn't work for (assumedly) 16-bit programs anymore...
Unless adjusting the text of the program is enough to actually break it.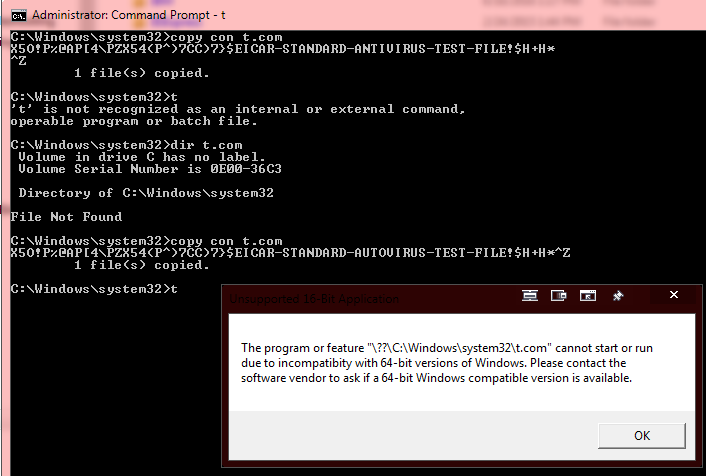
-
-
@Tsaukpaetra said in Symantec email exploit bites Symantec:
Doh! Apparently WOW doesn't work for (assumedly) 16-bit programs anymore...
Correct, 64-bit Windows can't run 16-bit programs.
-
@kt_ said in Symantec email exploit bites Symantec:
@masonwheeler hey you, what antivirus do you use?
Windows Defender. Why?
-
@masonwheeler said in Symantec email exploit bites Symantec:
@kt_ said in Symantec email exploit bites Symantec:
@masonwheeler hey you, what antivirus do you use?
Windows Defender. Why?
@masonwheeler said in Symantec email exploit bites Symantec:
@kt_ said in Symantec email exploit bites Symantec:
@masonwheeler hey you, what antivirus do you use?
Windows Defender. Why?
Cause I hear Microsoft is really bad at security.
Seriously though, I'm curious. Everybody's bashing every security company out there -- who's good at security and can be trusted if no one is good at security?
-
@kt_ My antivirus strategy generally consists of common sense. I have yet to see software that would infect my PC without me taking any stupid action, and I have yet to see an antivirus that would convince me not to run this piece of software I just willingly downloaded. Either I won't download it in the first place, or I'll figure it's one of a billion false positives.
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
I have yet to see software that would infect my PC without me taking any stupid action
Basically:
- Don't disable UAC
- If UAC pops up, PAY ATTENTION TO WHICH PROGRAM IT SAYS
- Keep software up to date
- End result: no viruses
-
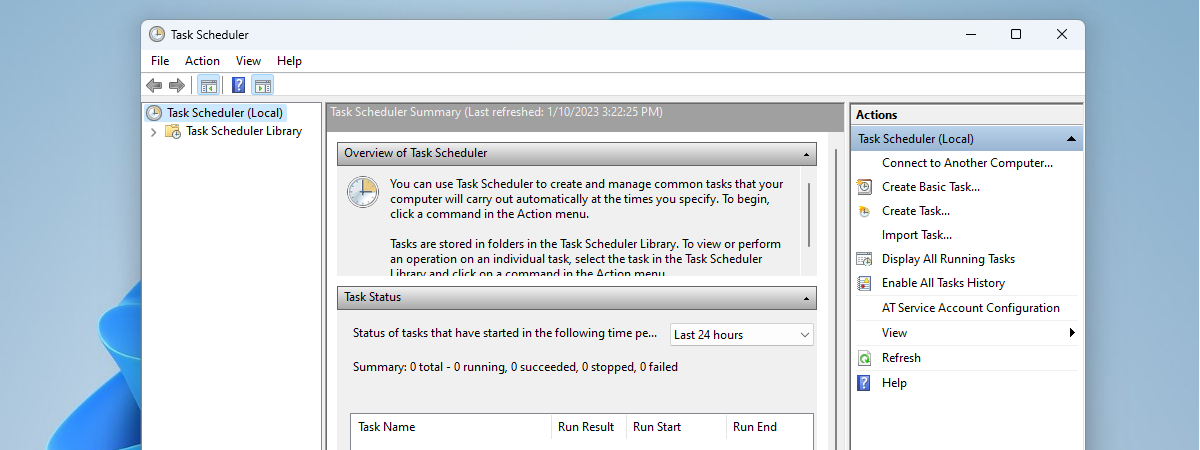
@ben_lubar UAC is generally bypassable via Task Scheduler shenanigans, but it still won't be a problem if you don't run the damn program. Which you either won't, or will agree to whatever it asks you for anyway.
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
@ben_lubar UAC is generally bypassable via Task Scheduler shenanigans, but it still won't be a problem if you don't run the damn program. Which you either won't, or will agree to whatever it asks you for anyway.
Yeah, a good strategy is to only tell your computer to do things you want your computer to do.
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
@kt_ My antivirus strategy generally consists of common sense. I have yet to see software that would infect my PC without me taking any stupid action, and I have yet to see an antivirus that would convince me not to run this piece of software I just willingly downloaded. Either I won't download it in the first place, or I'll figure it's one of a billion false positives.
That strategy works until a link you click redirects to a malformed PDF.
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
I have yet to see software that would infect my PC without me taking any stupid action
I've seen fresh installs get pwned and rooted in the time it took me to log in for the first time and install Windows Updates.
I've seen websites that automatically and silently installed shit using zero-day exploits with no user interaction whatsoever.
"Don't run shady executables" is not an effective strategy for avoiding malware.
Edit: fuck, for that matter, I've seen an installer for a program I've trusted and used for years, silently get a trojan horse added to it on the official website.
Editedit: Oh! And removable media like CDs and USB sticks can carry viruses around that auto-install! See: Sony rootkit
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
UAC is generally bypassable via Task Scheduler shenanigans
Really? That would be a major Windows vulnerability.
-
@error said in Symantec email exploit bites Symantec:
I've seen fresh installs get pwned and rooted in the time it took me to log in for the first time and install Windows Updates.
I've seen websites that automatically and silently installed shit using zero-day exploits with no user interaction whatsoever.
"Don't run shady executables" is not an effective strategy for avoiding malware.
Edit: fuck, for that matter, I've seen an installer for a program I've trusted and used for years, silently get a trojan horse added to it on the official website.
Editedit: Oh! And removable media like CDs and USB sticks can carry viruses around that auto-install! See: Sony rootkit
I've seen reputable websites that talk extensively about security issue redirect me to pages that auto-download bogus "browser updates" because someone shady got into their ad network.
-
@masonwheeler said in Symantec email exploit bites Symantec:
@error said in Symantec email exploit bites Symantec:
I've seen fresh installs get pwned and rooted in the time it took me to log in for the first time and install Windows Updates.
I've seen websites that automatically and silently installed shit using zero-day exploits with no user interaction whatsoever.
"Don't run shady executables" is not an effective strategy for avoiding malware.
Edit: fuck, for that matter, I've seen an installer for a program I've trusted and used for years, silently get a trojan horse added to it on the official website.
Editedit: Oh! And removable media like CDs and USB sticks can carry viruses around that auto-install! See: Sony rootkit
I've seen reputable websites that talk extensively about security issue redirect me to pages that auto-download bogus "browser updates" because someone shady got into their ad network.
Oh, don't get me started about the big DOWNLOAD buttons on "safe" download sites that are actually ads to download malware. Or malware downloaders.
Or fucking CNET.
-
@kt_ said in Symantec email exploit bites Symantec:
who's good at security and can be trusted if no one is good at security?
When everyone's crap, no-one is.. ..
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
@kt_ My antivirus strategy generally consists of common sense. I have yet to see software that would infect my PC without me taking any stupid action, and I have yet to see an antivirus that would convince me not to run this piece of software I just willingly downloaded. Either I won't download it in the first place, or I'll figure it's one of a billion false positives.
There were situations were viruses that attack IPs at random would find flaws in your system, if you connected directly to the internet, it happened to WinXP. There was bugs in outlook express too, that would run code just from previewing an e-mail.
-
@ben_lubar said in Symantec email exploit bites Symantec:
Yeah, a good strategy is to only tell your computer to do things you want your computer to do.
Until you're prevented from telling it not to do something, like reboot without warning (here's looking at you, BSODs!)
-
@kt_ said in Symantec email exploit bites Symantec:
@masonwheeler said in Symantec email exploit bites Symantec:
@kt_ said in Symantec email exploit bites Symantec:
@masonwheeler hey you, what antivirus do you use?
Windows Defender. Why?
@masonwheeler said in Symantec email exploit bites Symantec:
@kt_ said in Symantec email exploit bites Symantec:
@masonwheeler hey you, what antivirus do you use?
Windows Defender. Why?
Cause I hear Microsoft is really bad at security.
Seriously though, I'm curious. Everybody's bashing every security company out there -- who's good at security and can be trusted if no one is good at security?
EMET supposedly helps. If Defender is the only thing someone has, definitely consider installing it as well.
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
UAC is generally bypassable via Task Scheduler shenanigans
REALLY.
Will somebody PLEASE tell Adobe and Oracle, so they can fix their fucking goddamn updaters?
And no, this wasn't news to me...
-
-
@anonymous234 said in Symantec email exploit bites Symantec:
@Maciejasjmj said in Symantec email exploit bites Symantec:
UAC is generally bypassable via Task Scheduler shenanigans
Really? That would be a major Windows vulnerability.
-
@anotherusername I followed the link at the top of TFA and saw this:
Where to find the Task Scheduler in Windows 8 & 8.1
In Windows 8, search is the fastest way to start just about anything. The problem is that you must perform the search using the word "schedule". If you type "task" or some other word, you won't get the appropriate search results. Then, filter the results by Settings and click or tap on "Schedule tasks".Yeah, that sounds about right from my experience trying to search for things in Windows.
Is there no UAC prompt to get into task scheduler in the first place?
-
@boomzilla IIRC you have to give it an admin user's username and password to run the task under.
-
@anotherusername So...it's like some blakey definition of "bypass" then.
-
@boomzilla it makes it so that your program will run as administrator without requiring UAC elevation every single time it runs.
-
@lucas1 said in Symantec email exploit bites Symantec:
@Tsaukpaetra I still mourning the loss of
> edit myfile.txtStill one of my favourite text editors.
RIP
Notepad2 is a pretty good editor for when you just need to edit a fucking file and don't need the fluff of even a multi-document interface. It even has an option for a registry hack that makes Windows launch it in place of
notepad.exeno matter how it gets launched (without actually touchingnotepad.exe).Edit: Actually, I prefer: http://xhmikosr.io/notepad2-mod/
-
@anotherusername Yes, by having you put in the necessary credentials. It's an alternative to UAC, but not "bypassing" it, I'd say.
-
@boomzilla logging in as an administrator doesn't ordinarily disable UAC or let you launch elevated processes without triggering a UAC elevation prompt, though.
-
There was bugs in outlook express too, that would run code just from previewing an e-mail.
Yeah, but to fall prey to that, you had to already be running malware.
-
@HardwareGeek said in Symantec email exploit bites Symantec:
<abbr title=Outlook Express">malware.
Ya forgot a closing tag somewhere..
-
@Maciejasjmj said in Symantec email exploit bites Symantec:
UAC is generally bypassable via Task Scheduler shenanigans,
How?
-
@blakeyrat said in Symantec email exploit bites Symantec:
@Maciejasjmj said in Symantec email exploit bites Symantec:
UAC is generally bypassable via Task Scheduler shenanigans,
How?
Filed under: Similar in concept, but not identical.
-
@Tsaukpaetra No, the opening quote on the title text, and I didn't forget it; my mobile is being a bit flaky about detecting touches today.
Filed under:


-
@anotherusername Huh. That actually seems to work.
I thought the "trick" was just going to be to use Task Scheduler to run the app using RunAs, which is technically "bypassing UAC" but actually not really.
But this is genuinely weird.
I can find tons of sites telling people how do to this "trick", but zero sites explaining why Microsoft allows it.
-
@anotherusername said in Symantec email exploit bites Symantec:
@boomzilla IIRC you have to give it an admin user's username and password to run the task under.
Yeah, except no.
Relevant ProjectZero discussion, and a proof of concept.. It's a PowerShell script so it'd be disabled by default, but I seem to remember schtasks works just as well.
EDIT: Apparently as of Windows 10 it doesn't work, huh. Would have to check the Win8 VM I have somewhere.
-
@error 100% agree. Sometimes I just do JS in notepad, crazy I know, but JS programming for me isn't like structured or rational ... I just program. Having a really shit text editor like notepad or edit really helps that sort of thinking.
-
@HardwareGeek said in Symantec email exploit bites Symantec:
@Tsaukpaetra No, the opening quote on the title text, and I didn't forget it; my mobile is being a bit flaky about detecting touches today.
Filed under:


I leave out closing tags deliberately as a little gift for anyone who tries to quote me.

-
@Maciejasjmj said in Symantec email exploit bites Symantec:
@kt_ My antivirus strategy generally consists of common sense. I have yet to see software that would infect my PC without me taking any stupid action, and I have yet to see an antivirus that would convince me not to run this piece of software I just willingly downloaded. Either I won't download it in the first place, or I'll figure it's one of a billion false positives.
Don't visit Yahoo Japan or Taiwan (and possibly any site that hosts Ads that can be Flash based) with Flash enabled then. Their Ads can contain ransomware that infect your computer via Flash related vulnerability.
-
@ben_lubar said in Symantec email exploit bites Symantec:
@Maciejasjmj said in Symantec email exploit bites Symantec:
I have yet to see software that would infect my PC without me taking any stupid action
Basically:
- Don't disable UAC
- If UAC pops up, PAY ATTENTION TO WHICH PROGRAM IT SAYS
- Keep software up to date
- End result: no viruses
Also well worth doing:
- Install uBlock Origin in your browser
to get rid of malvertising zero-day drive-bys.
-
@error said in Symantec email exploit bites Symantec:
I've seen fresh installs get pwned and rooted in the time it took me to log in for the first time and install Windows Updates.
I've seen websites that automatically and silently installed shit using zero-day exploits with no user interaction whatsoever.All those moments will be lost in time, like tears... in... rain.