WTF Bites
-
@pie_flavor said in WTF Bites:
the controls don't move around properly.

Why? It's not a resizable dialog. It would be a total waste of effort.
-
It's not a resizable dialog. It would be a total waste of effort.
So… does it break utterly when the dialog opens on a screen with a different font scaling factor to what you tested for?
-
It's not a resizable dialog. It would be a total waste of effort.
So… does it break utterly when the dialog opens on a screen with a different font scaling factor to what you tested for?
No. Because dialogs just work. (The dialog is specified via the RC file - those are dialog units, not pixels.)
Edit: Scaling is very different from just changing size. If I lay something out at 100x100 units, scaling will preserve all those relationships. But when random other thing says: you are now 300x100 units! you just broke assumptions made during the design of the dialog.
-

Which is it?
-
@hungrier both?
-
Base64encoding seems to take ages under iOS - it took two minutes for a 3MB picture...
That's because each of those 64 characters are hand crafted artisanal bytes made in small batches by local indie developers ´*´
Sure, it may take a little longer, and cost a little bit more, but it's worth it for the brave, innovative quality. ´**´
´*´ note that some percentage between 0-100% of bytes may come from child labour.
´**´ quality not guaranteed. Apple Care does not cover lack of quality due to improper use, proper use, or lack of use. Warranty limitations do not count in states or counties that do not allow warranty limitations. At least not until we buy new laws in those areas.
-
@Lorne-Kates said in WTF Bites:
by local indie developers
I like the ambiguity of "indie" developer.
-
Base64encoding seems to take ages under iOS - it took two minutes for a 3MB picture...
Placing bet now: the library doesn't use a string builder so each new byte gets a new string append....
-
@Lorne-Kates said in WTF Bites:
by local indie developers
I like the ambiguity of "indie" developer.
"Indie."
Let's see...- unemployed
- south Asian
- history teacher

-
Why? It's not a resizable dialog. It would be a total waste of effort.
In GTK, resizable is the default and making it fixed takes extra effort. In Qt, it is a few extra clicks in the designer. I never understood why in the Windows ones it is either so hard (in the older ones) or non-obvious (in the newer ones).
-
@Bulb it's not that it cannot be done. It's that it'll be ugly. Imagine if the "application crashed, looking for solutions" dialog was maximized.
-
@Lorne-Kates said in WTF Bites:
by local indie developers
I like the ambiguity of "indie" developer.
"Indie."
Let's see...- unemployed
- south Asian
- history teacher

You forgot:
- Doing it for “exposure”
-
@Lorne-Kates said in WTF Bites:
by local indie developers
I like the ambiguity of "indie" developer.
"Indie."
Let's see...- unemployed
- south Asian
- history teacher

You forgot:
- Doing it for “exposure”

-
@dkf I would list that as a subcategory of "unemployed."
-
@Tsaukpaetra said in WTF Bites:
Base64encoding seems to take ages under iOS - it took two minutes for a 3MB picture...
Placing bet now: the library doesn't use a string builder so each new byte gets a new string append....
Each byte is a separate in-app purchase
-
@loopback0 said in WTF Bites:
Stupid ass-company
Never heard of SAC?
That's a major city to the east of us. (Ok, fine. It's the state capital. Whatever.)
Never heard of the city of Strategic Air Command, in California or even Nebraska.
-
@boomzilla And while the Southern Athletic Conference is delusional, it's not delusional enough to be a city.
-
@Lorne-Kates said in WTF Bites:
by local indie developers
I like the ambiguity of "indie" developer.
"Indie."
Let's see...- unemployed
- south Asian
- history teacher

- Kremlin-sponsored hackers
-
@boomzilla said in WTF Bites:
@loopback0 said in WTF Bites:
Stupid ass-company
Never heard of SAC?
That's a major city to the east of us. (Ok, fine. It's the state capital. Whatever.)
Never heard of the city of Strategic Air Command, in California or even Nebraska.
Sack SAC!
-
I checked the app store to see what amazing things I should be enjoying.
1 - The current version of the Facebook iOS app is 213.0. TWO HUNDRED AND THIRTEEN.
2 - The app store description on the update is the same as the last 10 versions.We update the app regularly so we can make it better for you. Get the latest version for all of the available Facebook features. This version includes several bug fixes and performance improvements. Thanks for using Facebook!
3 - The App Store page shows the app as 450MB. That's larger than the macOS version of Eclipse with all the J2EE stuff installed.
4 - According to my iPhone it's 264MB.
-
@loopback0 said in WTF Bites:
1 - The current version of the Facebook iOS app is 213.0. TWO HUNDRED AND THIRTEEN.
They outchromed Chrome.
-
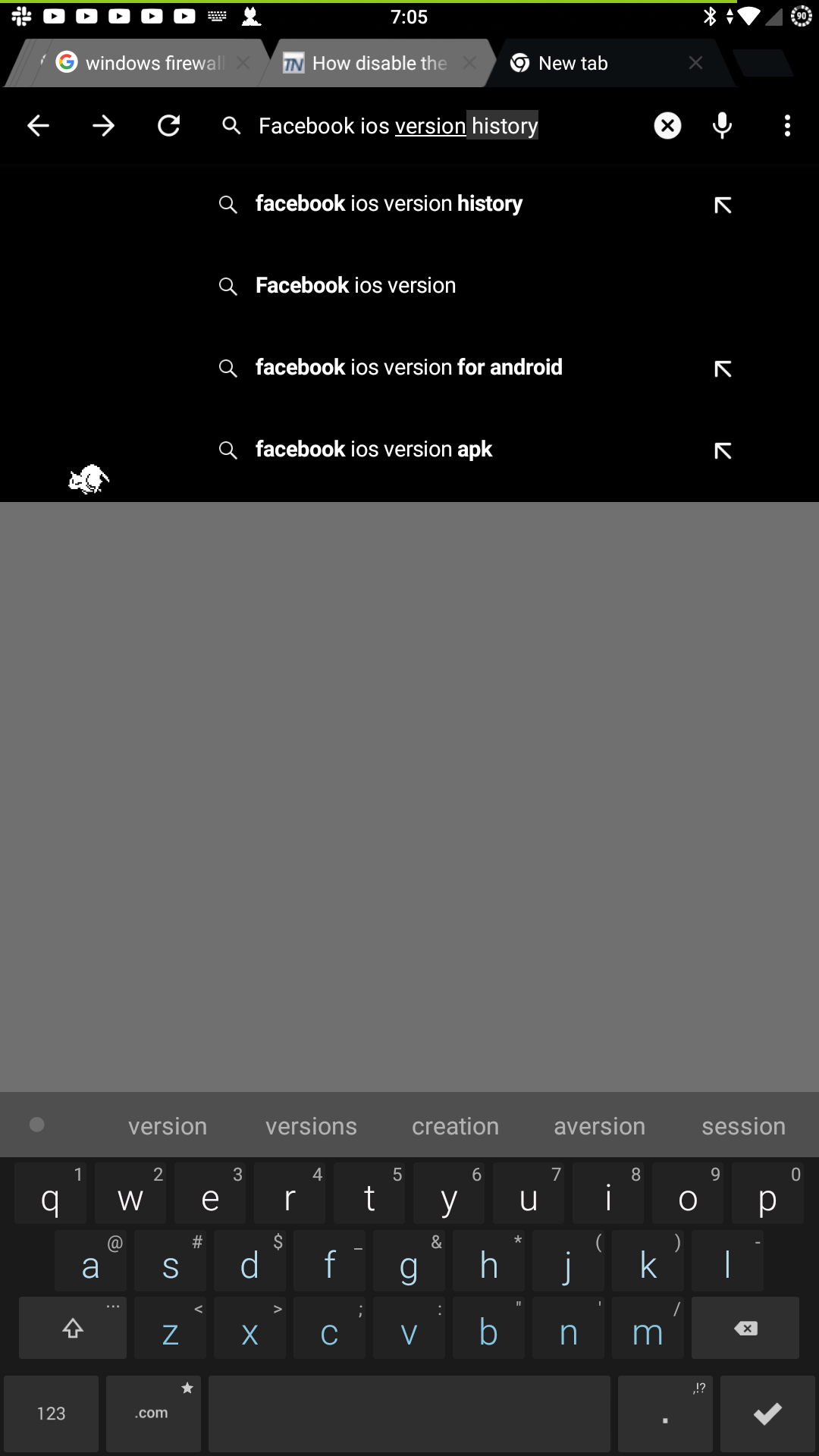
Bonus WTF is when I headed to Google to see if I could get a version history of the iOS Facebook app further back than the 6 months available in the App Store.
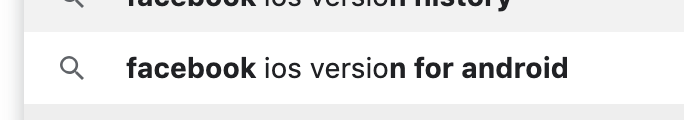
How many people are searching for an Android iOS Facebook app?!
-
@loopback0 no repro. You must've googled a lot for random applications for Android.
-
Am I dumb, or isn't the plus sign supposed to stop Google from including results without that term?
To add to the other responses, I'd guess that went away when Google+ started since +Name is how you refer to someone on G+. Well, how you used to refer to them.
-
@dkf I would list that as a subcategory of "unemployed."
-
@Applied-Mediocrity said in WTF Bites:
@Lorne-Kates said in WTF Bites:
by local indie developers
I like the ambiguity of "indie" developer.
"Indie."
Let's see...- unemployed
- south Asian
- history teacher

- Kremlin-sponsored hackers
Those peoples get paid in weekly installments of "your family gets to live a while longer".
Or bitcoin. Whichever is more evil
-
@loopback0 no repro. You must've googled a lot for random applications for Android.

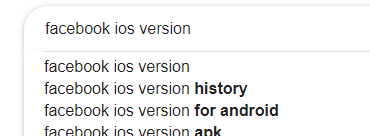
Different computer, Incognito mode, same results:
-
@loopback0 but did you change IP? Google is very thorough in their spying.
-
@Gąska I get the same result on my phone

-
@TimeBandit the phone that has the same Google account logged in that you check mail for on your computer?
Alternatively, might be regional thing.
-
Never searched it ever, this is my result....
-
@Tsaukpaetra must be regional then. On my phone, I don't get "for android", but I get "apk".
-
@TimeBandit the phone that has the same Google account logged in that you check mail for on your computer?
Yes
Alternatively, might be regional thing.
@loopback0 isn't in Canada
-
-
It's been over 90 days since I reported it and @TPLINK never responded, so: arbitrary command execution on the TP-Link SR20 smart hub and router (and possibly other TP-Link device).
TP-Link routers frequently run a process called "tddp" (TP-Link Device Debug Protocol) as root. It's had multiple vulnerabilities in the past and the protocol is fairly well documented. Version 1 has no auth, version 2 requires the admin password.
The SR20 still exposes some version 1 commands, one of which (command 0x1f, request 0x01) appears to be for some sort of configuration validation. You send it a filename, a semicolon and then an argument.
The router then connects back to the requesting machine over TFTP, requests the filename via TFTP, imports it into a LUA interpreter and passes the argument to the config_test() function in the file it just imported. The interpreter is running as root.
The os.execute() method allows you to execute whatever you want, and you're running as root, so victory. tddp is listening on all interfaces but the default firewall rules block WAN access, so this is local network only.
Anyway, stop shipping debug daemons on production firmware and if you're going to have a webform to submit security issues then have someone actually respond to it.
Source: Matthew Garrett @mjg59
-
This post is deleted!
-
-
@Bulb
wget -U "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1)"
-
@TimeBandit … I think you don't even have to do that since wget isn't curl…
-
wget isn't curl

Where's my coffee

curl --user-agent "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1)"
-
could allow an authenticated, remote attacker with administrative privileges on an affected device to execute arbitrary commands.
I realize that this isn't all the way past the airtight vault door, but it still sounds funny.
-
@Bulb The HN discussion for that clusterfuck went on a tangent about User Agents, and I learned what the upcoming Edge-but-based-on-Chromium will call itself:
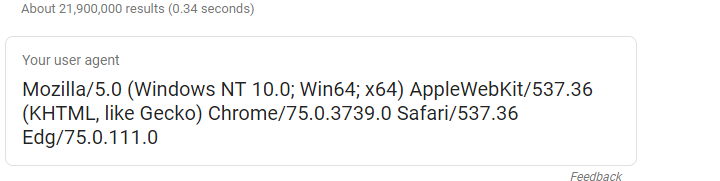
Source: HN
-
WTF of my day: I was riding my bike from and to work today and on my way inside a "30 km/h limit" zone (residental area, several schools and kindergarten), a woman disregarded my right of way rather massively - didn't slow down, just mow over the crossing at what I'd estimate to be 50. Good thing I'm accustomed to this idiocy and was still aproaching the crossing more slowly - still had to brake, though. Too bad for her that this didn't yield any measurable advantage as she then had to wait behind other cars and there was also this red traffic light.
Which allowed me to catch up. So I stopped beside her, knocked on her window and asked her if she even saw me?
She got mad instantly, began to yell (because "no one touches my car!") and then pushed open her door. While I was still on my bike beside her. Which of course caused a dent in her door. Then she got really mad. Parked her car in a shitty way (on top of a bike lane, of course!), tried to call the cops (who probably told her to
bugger offtake her complaint to a station) and generally tried to shove me around. Took a photo of me (I'm a handsome guy, what can I say?)And then took off.
You'll note that nowhere did she try to get my name. Or tried to get any witnesses.
I, on the other hand, did just that. Plus, I also reported her to our parking violation department for parking on a bike lane (bikes don't have a license plate. Cars do...). So in the unlikely case that she manages to find out who I am I'll have witnesses to her shoving and jerking me around (I could have easily decked her but decided that this would be a needless escalation), yelling and cursing at me and being a general asshat. In the rather more likely event that the police decides not to follow up (I mean, how willing would you as a cop be to follow up on searching for a guy with no criminal background on a bike in a city with 1+ million citizens? For a rather mundane thing?) she'll be shit out of luck anyway.

-
-
@Tsaukpaetra must be regional then. On my phone, I don't get "for android", but I get "apk".
That's because everyone in your region pirates everything. Google is very well trained.
-
-
The British have been inspecting Huawei's source code, and what they found is both familiar and disturbing:
3.33 The report analysed the use of the commonly used and well maintained open source component OpenSSL. OpenSSL is often security critical and processes untrusted data from the network and so it is important that the component is kept up to date. In the first version of the software, there were 70 full copies of 4 different OpenSSL versions, ranging from 0.9.8 to 1.0.2k (including one from a vendor SDK) with partial copies of 14 versions, ranging from 0.9.7d to 1.0.2k, those partial copies numbering 304. Fragments of 10 versions, ranging from 0.9.6 to 1.0.2k, were also found across the codebase, with these normally being small sets of files that had been copied to import some particular functionality. There were also a large number of files, again spread across the codebase, that had started life in the OpenSSL library and had been modified by Huawei.
3.34 In the later version, there were only 6 copies of 2 different OpenSSL versions, with 5 being 1.0.2k and one fork from a vendor SDK. There remained 17 partial copies of 3 versions, ranging from 0.9.7d to 1.0.2k. The fragments from the 10 different versions of OpenSSL remained across the codebase as do the OpenSSL derived files that have been modified by Huawei. More worryingly, the later version appears to contain code that is vulnerable to 10 publicly disclosed OpenSSL vulnerabilities, some dating back to 2006. This shows the lack of maintainability and security resulting from the poor configuration management, product architecture and component lifecycle management.
3.36 In summary:
• There were over 5000 direct invocations of 17 different safe memcpy()-like functions and over 600 direct invocations of 12 different unsafe memcpy()-like functions. Approximately 11% of the direct invocations of memcpy()-like functions are to unsafe variants.
• There were over 1400 direct invocations of 22 different safe strcpy()-like functions and over 400 direct invocations of 9 different unsafe strcpy()-like functions. Approximately 22% of the direct invocations of strcpy()-like functions are to unsafe variants.
• There were over 2000 direct invocations of 17 different safe sprintf()-like functions and almost 200 direct invocations of 12 different unsafe sprintf()-like functions. Approximately 9% of the direct invocations of sprintf()-like functions are to unsafe variants.3.38 Analysis of relevant source code worryingly identified a number pre-processor directives of the form
#define SAFE_LIBRARY_memcpy(dest, destMax, src, count) memcpy(dest, src, count)
, which redefine a safe function to an unsafe one, effectively removing any benefit of the work done to remove the unsafe functions in the source code. There are also directives which force unsafe use of potentially safe functions, for example of the form
#define ANOTHER_MEMCPY(dest,src,size) memcpy_s((dest),(size),(src),(size))
.Source: Her Majesty's Government / The Register
-
Status: Azure wanted to provide a lot of precision for some sizes for some reason...
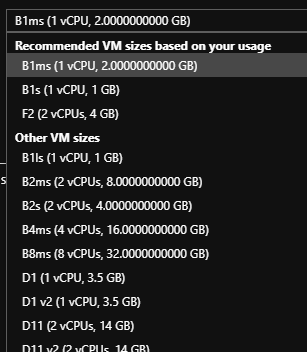
-
@Tsaukpaetra Those ought to be “GiB” if they're using that much precision…
-
@Tsaukpaetra Those ought to be “GiB” if they're using that much precision…
GiBlets for the sub-bit precision parts?

 Dissociative identity disorder - Wikipedia
Dissociative identity disorder - Wikipedia