NSA backdoor used against the US
-
Continuing the discussion from Juniper Networks backdoor confirmed, password revealed, NSA suspected:
http://boingboing.net/2015/12/21/juniper-networks-backdoor-conf.html
Apparently, the backdoor in Juniper devices was not used by the NSA.
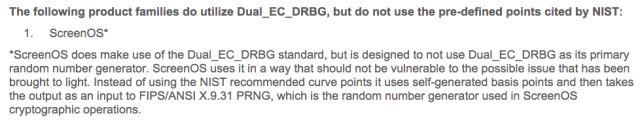
Do you remember Dual_EC_DRBG, the random number generator with the NSA backdoor? Depending on the parameter you pass into the random number generator, the results may be predictable.
Some Juniper devices use that RNG. The bug that was recently "fixed" by Juniper was that someone changed that parameter in the code.
So: Some other country used the NSA backdoor against a US company (and, probably, the US government) and made it its own backdoor. Juniper "fixed" that by resetting the backdoor parameter to its original value.
-
"Reports indicate" (link to tweet.)
No. Sorry. I'm all for Twitter, but stuff posted on Twitter does not count as "reports".
-
The other tweet primarily contained a link:
-
That's the same article I read yesterday. It says absolutely NOTHING about the backdoor "being repurposed by America's adversaries". He's just making shit up. Jesus. That's even worse than citing a tweet as "reports".
-
That's the same article I read yesterday. It says absolutely NOTHING about the backdoor "being repurposed by America's adversaries"
Read the blog post linked in the OP. One vulnerability they found and fixed is the changed parameter passed to Dual_EC_DRBG. That "America's adversaries" (whoever that may be) are responsible for that is speculation, but the NSA backdoor was definitely repurposed by someone else.
-
is speculation
HELLO THAT IS MY POINT.
Question.
Are there any "reports that indicate a backdoor designed by the NSA has been repurposed by America's adversaries?"
Hell for that matter, are there any reports that indicate the backdoor was designed by the NSA in the first fucking place?
Snowden's tweet is a lie based on another lie. He posts it with no "opinion" tag or "speculation" tag, and guess what? That's sleezy.
-
Hell for that matter, are there any reports that indicate the backdoor was designed by the NSA in the first fucking place?
The broken RNG? Yep, that one definitely was designed by the NSA. Did they actually force Juniper to use it or was Juniper just stupid? Or did Juniper even add a backdoor on purpose without NSA intervention? Who knows, but it's a backdoor that the NSA designed.
Also, "America's adversaries" can mean pretty much anything ranging from criminals to foreign nations, so - technically - it's not incorrect.

-
Bullshit.
Look, you might bow before Snowden and kiss his ass every morning for being a national hero or whatever, but he's TALKING ENTIRELY OUT OF HIS ASS in that tweet and you aren't doing anybody any favors by white knighting for him.
-
There are three possibilities:
- Someone from the US government changed the parameter to the one that activates the backdoor
- Someone NOT from the US government changed the parameter to the one that activates the backdoor
- Someone managed to change the parameter to the one possible value that would activate the backdoor accidentally
-
TALKING ENTIRELY OUT OF HIS ASS in that tweet
I get your point, it's speculation, but "entirely out of his ass" is not correct either. There are signs what he states might be true, especially since several authorities seem to be interested in investigating the incident.
Originally, I only wanted to link the blog post. But I thought the tweet was funny (for cynical people like me) and would probably start a nice flamewar, so I included it in my post.
-
I have yet to see any evidence that the US government is involved at all.
-
There are signs what he states might be true,
There's signs that every conspiracy theory is true. That doesn't make any of them true.
especially since several authorities seem to be interested in investigating the incident.
That would have happened if this backdoor was installed by Larry the Juniper Janitor. It's evidence for nothing.
-
He posts it with no "opinion" tag or "speculation" tag, and guess what? That's sleezy.
He posted it on Twitter. That is indication enough that it is opinion and/or speculation.
-
That would have happened if this backdoor was installed by Larry the Juniper Janitor. It's evidence for nothing.
It's evidence that the authorities think someone made that mistake on purpose. And since that person must have had some crypto knowledge, Larry is not one of the suspects, I'm afraid.
conspiracy theory
So, every bit of speculation is a conspiracy theory to you? Nobody said anything about any conspiracy.
-
It's evidence that the authorities think someone made that mistake on purpose.
Right. Larry.
It's not evidence that the fucking NSA is involved. If you have evidence for that, by all means, share it.
And since that person must have had some crypto knowledge, Larry is not one of the suspects, I'm afraid.
Wow you're an asshole towards janitors. How the fuck do you know what Larry knows or does not know?
So, every bit of speculation is a conspiracy theory to you?
No; I'm just saying you need to engage your critical thinking skills, or this will turn into a conspiracy theory. Evidence first.
-
It's not evidence that the fucking NSA is involved
The fact that the hole (in the RNG) exists due to the NSA does make them involved, tangentially, but involved none the less.
-
It's not evidence that the fucking NSA is involved.

Nobody claims that there's an epic spy battle going on between the NSA and [Ex-KGB/Mossad/$insert_secret_service_here]. But the NSA designed a RNG with a backdoor a while ago. Someone who wasn't the NSA took advantage of that.
BTW: That's the whole point Snowden has been trying to make for a while: If you put backdoors on software/crypto/…, someone else will use them, so putting backdoors in software is a bad idea. In that context, he posted that tweet.
-
I'm not saying it's a good idea, I'm saying he's pulling shit out of his assssssssssssssss.
-
You did read the part where he used the word indicate, right? And I'm pretty sure you know the difference between "indicate" and "prove".
-
I see no indications.
-
Dual_EC_DRBG is also exceptionally slow compared to other RNGs and many in the academic world thought it was flawed or backdoored long before the Snowden docs. There was no reason to chose it over any other RNG in the first place except for the obvious one of being coerced into doing so.
-
Also, "America's adversaries" can mean pretty much anything ranging from criminals to foreign nations
Or depending on who you ask, the federal government.
-
The discussion about the RNG is a bit of a red herring. The biggest issue was that several versions of the software that contained a hardcoded password that allowed an intruder to sign on as any user. Administrative users as well, natch.
CVE-2015-7755: Juniper ScreenOS Authentication Backdoor
The password was, and I quote:
<<< %s(un='%s') = %uIt was explicitly defined to look like a string format item for a logging print. Darn simple hack, for the effect.
Schneier has a good post on this.
Addendum:
This article called the above hack, "But on the technological awesomeness scale it rates about a two out of ten, maybe a step above 'hit the guy with a wrench'."
-
The discussion about the RNG is a bit of a red herring.
How? There are two vulnerabilities, one of which was a backdoor password and the other is one that allows an attacker to passively decrypt VPN traffic. Both are extremely severe.
-
allowed an intruder to sign on as any user. Administrative users as well, natch.
It allowed authentication as the
systemuser, which seems to be like theSYSTEMWindows account ("hidden," and with complete access to the system).
-
How? There are two vulnerabilities, one of which was a backdoor password and the other is one that allows an attacker to passively decrypt VPN traffic. Both are extremely severe.
There are two vulnerabilities, but several of the articles I've seen have focused on "this incredibly difficult to understand don't worry your head about it highbrow encryption potential problem" and have basically ignored the authentication hack, which anyone can understand.
I should add that I don't minimize the other discussion; just don't let it bury the authentication hack.
It allowed authentication as the system user, which seems to be like the SYSTEM Windows account ("hidden," and with complete access to the system).
From the first article I linked: "Update: Fox-IT reached out and confirmed that any username can be used via Telnet or SSH with the backdoor password, regardless of whether it is valid or not."
-
"this incredibly difficult to understand don't worry your head about it highbrow encryption potential problem" and have basically ignored the authentication hack, which anyone can understand.
Really? It seems to be the reverse for me. We're discussing it here because we can understand the encryption vulnerability.
Also, it isn't a "potential problem," it's an exploit that whoever planted (or anyone who figures out the e value) can use to easily decrypt VPN traffic.
From the first article I linked: "Update: Fox-IT reached out and confirmed that any username can be used via Telnet or SSH with the backdoor password, regardless of whether it is valid or not."
If you look at the log example that's everywhere, you punch in
anyusernameand are logged in assysteminstead ofanyusernamewhich is how you can tell if you've been compromised by that vulnerability. But thanks for highlighting the article for me.Link on the SSH hack: https://community.rapid7.com/community/infosec/blog/2015/12/20/cve-2015-7755-juniper-screenos-authentication-backdoor
-
It's not evidence that the fucking NSA is involved
Here is some damning proof, finally:
-
Dual_EC_DRBG was proven to be vulnerable well before the Snowden docs were released... and since the NSA was the group that designed it...
There was actually a patent filed in the U.S. in 2005 by Certicom and two of its employees on how to break Dual_EC_DRBG. Said employees were members of the ANSI committee reviewing Dual_EC_DRPG... which got approved anyway.
-
They got a patent for doing their job? No wonder they no longer want to do it, they're just sitting on royalties...
-
There was actually a patent filed in the U.S. in 2005 by Certicom and two of its employees on how to break Dual_EC_DRBG. Said employees were members of the ANSI committee reviewing Dual_EC_DRPG... which got approved anyway.
Wow.
Guess someone owes them some money for patent infringement, huh?