Breaking news: UEFI implementations still suck
-
What happens if you run
sudo rm -rf /sys/on a Linux system?If you guessed "it deletes a bunch of stuff and breaks the system", you guessed right. But on some UEFI based computers, there's a bonus: it deletes necessary UEFI variables, permanently bricking the motherboard.
See
http://www.intelsecurity.com/advanced-threat-research/content/AttackingAndDefendingBIOS-RECon2015.pdf pages 39-46, but feel free to read the rest if you're interested in this stuff
(Of course, this isn't a Linux thing, you can do it from any Windows process running as admin too)
-
I wonder if that's fixable by JTAG.
-
Ouch. If I were to be in a position to design an OS, I would not let a user brick their motherboard without giving them
A HUGE FREAKING WARNING THAT THIS MIGHT BRICK THEIR SHIT
possibly a flag along the lines of --no-preserve-motherboard to go with the --no-preserve-rootflag...
-
He points out that mounting EFI variables as read-only could break some user-space applications
What the fuck are userspace programs doing that would require writing into fucking UEFI? What's next, monkey-patching the running kernel from your browser?
-
If you are doing something that needs you to have write access to UEFI variables, I'm pretty sure you are smart enough to work out how to unmount them and remount them so they are writeable. If you can't work that out, you shouldn't be fucking with them in the first place!
-
What's next, monkey-patching the running kernel from your browser?
Nah, ActiveX driver installers are a thing of the past.
-
For that command to run, you should run it as root or sudo.
Well, basically that's a what you get by mounting it as filesystem but cannot mount it as readonly one.
It sounds like a good idea to use Linux on motherboards with CrashFree BIOS or equivalent, that when it goes wrong, you can plug the flash drive with image of ROM in and reboot.
-
If someone want to ruin your day, they can just remount the filesystem as "rw" for you before doing that.
-
Nothing I've ever read about UEFI has led me to believe that it was particularly well thought out. Same applies to ACPI. Both emit the faint but unmistakable stench of software designed by hardware engineers.
-
I couldn't believe how many people I saw defending mounting the efi fs as RW by default. It makes no sense for
rmto be able to hose your motherboard.
-
I can't believe UEFI is designed to permit this on any O/S. This is a lovely target for hackers.
-
 : Hey, maybe you should only mount this read-only; deleting things from here is dangerous...
: Hey, maybe you should only mount this read-only; deleting things from here is dangerous...
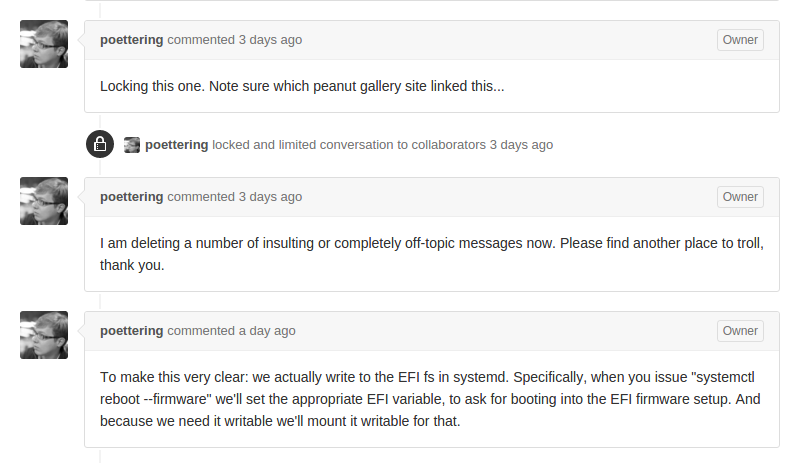
 (Lennart Poettering): Nah, destroying your system is a valid use case, plus that takes effort CLOSED WONTFIX DOINGITWRONG
(Lennart Poettering): Nah, destroying your system is a valid use case, plus that takes effort CLOSED WONTFIX DOINGITWRONGWhere have I heard that before?
I can't believe UEFI is designed to permit this on any O/S. This is a lovely target for hackers.
So's the NVRAM on Macs. So's the BIOS on all the old EZFlash motherboards. So what? Hackers don't brick systems anymore, they're after revenue and bricking doesn't get them any.
-
Well, actually, it's not...
At least, from what they were saying, a UEFI implementation to spec should boot even if the variables go bad.
Actually, wouldn't the same thing happen if the CMOS battery went dead?
-
same thing happen if the CMOS battery went dead?
Not if everything is stored in NVRAM...
-
So's the NVRAM on Macs. So's the BIOS on all the old EZFlash motherboards. So what? Hackers don't brick systems anymore, they're after revenue and bricking doesn't get them any.
ISIS. (For example.) How much revenue are they looking for?
-
Actually, no.
IMO, the UEFI part in sysfs should always be read-only (i.e.: they should remove the writing part from the kernal source). If you need to write to UEFI, you use corresponding libraries.
-
What the fuck are userspace programs doing that would require writing into fucking UEFI?
Word on the street is that you have to write into UEFI variables if you want to use UEFI boot, and that you have to update those variables if you do things like upgrade your kernel and still be able to boot. I expect that the folks on the street are excitable, and that you only have to update that data if you update your bootloader, but it seems that the UEFI committee did decide that it was reasonable to require you to write far more than just "I want to boot from this disk" into a motherboard's NVRAM in order to boot an OS in UEFI mode.
-
ActiveX lives!
-
UEFI ain't done until Linux won't run.
-
they should remove the writing part from the kernal source
I don’t think the [url=https://en.wikipedia.org/wiki/KERNAL]kernal[/url] has UEFI support at all.
-
-
http://www.phoronix.com/scan.php?page=news_item&px=UEFI-rm-root-directory
As a public service announcement, recursively removing all of your files from / is no longer recommended.
Ò_o
E_WONTFIX:toys_pram.tar.gz:
-
At least, from what they were saying, a UEFI implementation to spec should boot even if the variables go bad.
Yes. But it's already so fucking hard to get hardware makers to to actually follow relatively simple standards like USB or SATA, making them implement (even if it's just adapting from existing code) a full operating system in the firmware of a computer and expecting things to not have any bugs is crazy.
Even the Windows and Linux kernels have bugs and need regular patching, and they are written on a higher level of abstraction by competent developers.
Part of the job of creating a standard is to know how all relevant parties will react to it, and find ways to make things work. That means creating extensive testing and certification programs, punishing vendors who do things wrong, etc. which the UEFI forum has NOT done properly (IMO).
-
Maybe they could set up an EFI CDN?
-
My bad for typo.
I think kernel has UEFI support, though.
-
-
Relatively simple. As in compared to UEFI.
But I really meant to write "USB mass storage" there. I've found flash drives that didn't work with some devices which I think is ridiculous.
-
I've found flash drives that didn't work with some devices which I think is ridiculous.
Yeah, but that's exactly because USB is an extremely complicated standard that tries to do everything. I'm not even sure it's less fucked up than UEFI.
-
OK, you got me, I don't know anything about how USB works.
I just assumed it was on the same level of complexity as TCP/IP.
-
I just assumed it was on the same level of complexity as TCP/IP.
TCP/IP operate on OSI layers 3 and 4. USB covers all 7 layers for a lot of different use cases. Also, USB devices have to support a lot of different protocol versions by now.
-
Where have I
I thought Discourse's responses to bugs was bad, but systemd has people seriously enraged. Even Linus gets in on the hate:
the systemd people say "sorry, we stole your thing and made it useless, and it's not a bug because you didn't call shot-gun".
-
Zombie apocalypse confirmed. It all started in Korea…
No. They have a cure. They decided that ActiveX is bad so they make users download exe files and install them.
Very clever. Always one step ahead. Things you wouldn't even imagine in your dreams.
-
What the fuck are userspace programs doing that would require writing into fucking UEFI? What's next, monkey-patching the running kernel from your browser?
There's actually a number of things related to Secure Boot that the OS needs access to to get it up and running, and needs access to to ensure that security is maintained. Look up the UEFI Secure Boot Database.
You can also do things like modify the boot order to choose which bootloader you want, while previously you'd have had to make that selection in person or set up the order beforehand permanently. If you've ever wanted to boot a system to the CD drive remotely, you'll know exactly what I mean. Hell, it's even a pain in the ass with a VM since they boot so fast. Instead of saying, "Reboot", you can say, "reboot to the network" or "reboot to the CD drive" or "reboot to the USB diagnostic disk". No more guessing if you have to mash Esc, or F10, or F9, or F1, or F12, or Del, or F8, or Shift, or Space, or Enter, or Shift-P (yes, I've seen all of those... F8 was fun because you got to time it since Windows uses that key, too) or whatever key the BIOS manufacturer made.
What I don't get -- well, it's because of cost, but still -- what I don't get why there isn't a 128 MB flash chip soldered on the motherboard just for UEFI firmware. This whole, "let's store firmware on secondary storage," thing is just ripe for problems. It used to be that the required hardware to boot a system was the CPU, motherboard, RAM, and display adapter. Now we've added a disk drive. Yeah, computers aren't typically very useful without them, but making it a requirement doesn't feel like an advance. I've heard of problems with disk cloning and disk failure, too. There's the Lenovo UEFI hijack, too, but I suppose this doesn't fix that.
-
what I don't get why there isn't a 128 MB flash chip soldered on the motherboard just for UEFI firmware.
I think you will find there is. The problem being that systemd mounts that writable in the file system and allows you to blat it with rm. And see no issue with this because that's how they have always done it...
-
No, there isn't. Granted, I haven't worked with a new system in 2-3 years so it very well may have changed (which would be great) but when EFI and the first UEFI came out it was all stored on the system's hard drive in a 100 MB partition at the start of the disk. This was because flash was still pretty expensive and because redesigning a board to add another chip is also pretty expensive.
-
No more guessing if you have to mash Esc, or F10, or F9, or F1, or F12, or Del, or F8, or Shift, or Space, or Enter, or Shift-P (yes, I've seen all of those... F8 was fun because you got to time it since Windows uses that key, too) or whatever key the BIOS manufacturer made.
Worst I've seen was "Ctrl-Alt-Ins". And it wasn't written anywhere on the screen. I think it was a Packard Bell.
Was trying everything I could think of, without success. Then I called support. They told me about 5 different key combination (that I already tried) before getting to "try Ctrl-Alt-Ins".Using 5 different key combination to access the BIOS :

-
ISIS. (For example.) How much revenue are they looking for?
They do a different type of hacking.
-
Sabotage is a thing, you know.
-
-
ISIS. (For example.) How much revenue are they looking for?
Bombs and shit ain't free.
-
-
Bombs and shit ain't free.
Oh, yeah, I know that. But they're also looking for weaknesses—they are still pursuing guerrilla warfare tactics after all—and this is a massive weakness. And people looking for weaknesses think computers as well as military targets these days.
So a belief that all possible attackers, "...are only looking for a profit..." and "...will only attack that which yields a profit..." is naive at best.
Digital Attack Map gallery has some examples of people who were attacking/not looking for profit.
-
-
Bombs and shit ain't free.
If shit ain't free...
How much does a pound of shit sell for ?I know some people who may be worth a lot

-
@PleegWat said:








 :A:Start
:A:StartWhy are you being so antisocial?








 :A:SelectStart
:A:SelectStart








 CtrlAltDel
CtrlAltDelF13
Happy now peeps?

-
a pound of shit sell for ?
Manure calculator ?
Depends on quality I guess. Base rates starting at $0.25/lb?
-
?
-
Red

-
How much does a pound of shit sell for ?
US$35: Night soil does 14¢ each and there's 250 to the pound.
 Linux Hardware Reviews & Performance Benchmarks, Open-Source News
Linux Hardware Reviews & Performance Benchmarks, Open-Source News