Javascript code "encryption"
-
I'm trying to integrate with a proprietary js library. The "meat" of the code is stuffed inside this "encrypted" string, which is unrolled during the initial page load.
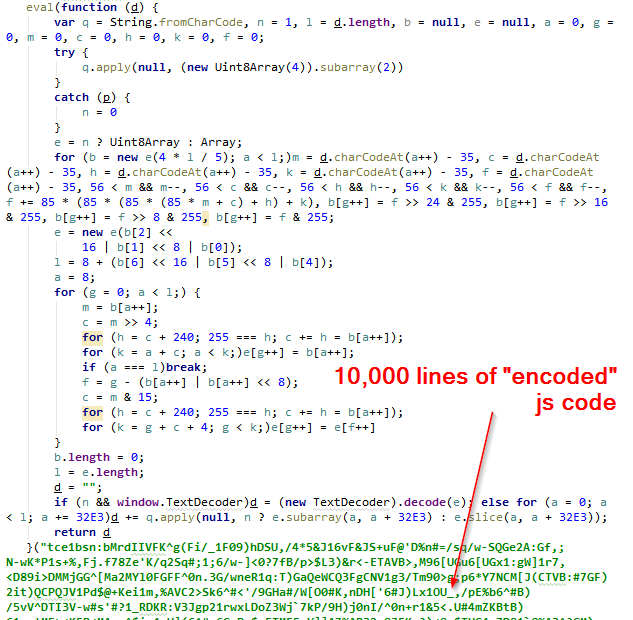
Drat! These library authors are so clever! I have finally met my match. How will I ever steal their precious codez now!?
Oh wait.
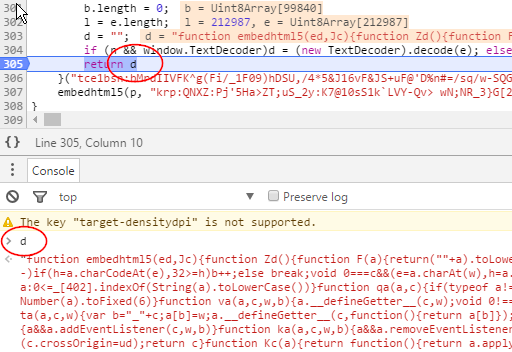
Right. This is javascript.
-
obviously they should have double encrypted it
-
That's why when I'm going to encrypt sensitive javascript code, I'll be transforming it into a interpreted assembly-like virtual machine.
Would be more fun to steal, and way more time-consuming.
-
@CreatedToDislikeThis
I suppose you need to have a debugger for the interpreter.
-
I seen stuff like this done before, it stops any numpty nicking the script. It is only one better than minimising but if you are selling JavaScript code it probably the best you can do to protect it.
-
My guess is they're relying on the legal principle that if you put a lock on your shed, even if it's a shitty lock, it's clearly illegal to open it, while an unlocked shed can be taken as an invitation. Stuff like this: http://cyb3rcrim3.blogspot.com/2006/09/can-you-hack-unsecured-computer.html
That said, different courts have ruled differently on that sort of thing, it's all very weird. I'm not sure this "encryption" would help.
-
@lucas1 said in Javascript code "encryption":
I seen stuff like this done before, it stops any numpty nicking the script. It is only one better than minimising but if you are selling JavaScript code it probably the best you can do to protect it.
It's only the user who pays the price of all that decrypting,
evaling and memory consumption.
-
@Yamikuronue even if I post a note next to the lock with instructions on how to open it?
@cartman82's browser might have broken the law by following instructions. TIL
-
@Yamikuronue said in Javascript code "encryption":
I'm not sure this "encryption" would help.
It's particularly problematic with code, since in order to execute it, it must become readable by the computer in a semantically-meaningful way, and that's all you need to recreate the definition (or something sufficiently similar).
-
@Yamikuronue I don't think that is right.
I don't know about the USA (but I suspect it is very similar) but the moment you write a piece of code you (or your employer) then hold the copyright to that code.
-
@cartman82 They could just use a regular minimizer instead of one that probably takes ages to run and does like a million string operations.
-
@Yamikuronue What's so harmful about your users (who allegedly paid for the right to use your library) being able to see and modify the code though?
I've heard the argument that there are "trade secrets" in the code, but I really doubt this example in particular has any of those. If it's a 10000 line javascript library, your users are most likely paying for the work you did putting all that code together, not for any function in particular.
-
@anonymous234 oh, I agree it's stupid. I just suspect that's why they bothered: some half-formed defense against a hypothetical lawsuit.
-
@dkf said in Javascript code "encryption":
in order to execute it, it must become readable by the computer in a semantically-meaningful way
Expressing that meaning in an esolang can make the semantics difficult enough to discern that borrowing for re-use becomes not worth the trouble.
-
@anonymous234 said in Javascript code "encryption":
What's so harmful about your users (who allegedly paid for the right to use your library) being able to see and modify the code though?
Keep away from my precious bodily fluids, you commie bastard
-
I once had a student friend phone me up to inquire on how to encrypt a
bashscript. My answer was "no", then I explained that the bash interpreter would need to see the source to run it. I told him aboutset -xand other funny stuff. Then I told him to rewrite it in C. Which he declined. Then we explored the possibilities of compiling a special bash version that would be able to read encrypted scripts without leaking them, which I enjoyed for sheer absurdity.The kicker? I later learned the bash script in question was 50 lines tops. I'd written it for a shop that wanted to install it on client computers, and they wanted to protect it. Because I'd told the shop that encrypting it was pointless and refused to even make an offer, they turned to my friend who'd been involved in the project. This "friend" then promptly called me to inquire on how to do this, without telling me who his client was. I didn't connect the dots until I talked to the shop owner a year later, when they wanted to extend the script. Hilarious in retrospect.
-
@anonymous234 said in Javascript code "encryption":
What's so harmful about your users (who allegedly paid for the right to use your library) being able to see and modify the code though?
Because 9 times out of 10 they would break it and then call ask you to help fix it.
-
@lucas1 said in Javascript code "encryption":
Because 9 times out of 10 they would break it and then call ask you to help fix it.
And this is when the billing-timer starts. What's wrong with that ?
-
@Yamikuronue said in Javascript code "encryption":
I'm not sure this "encryption" would help.
A better lock would be a license file stating that the code is not freely available for reuse without payment. Or whatever it is they're trying to prevent.
-
@TimeBandit Because it usually turns into a PITA. Maybe I am just not greedy enough.
-
@cartman82 It is amazing to me how many copy&paste "coders" out there don't understand, at all, the tools they are using

-
@Jaloopa said in Javascript code "encryption":
obviously they should have double encrypted it
...using ROT13

-
@Vaire I made some mention of this
https://what.thedailywtf.com/topic/19914/the-basics/29
I showed one of the juniors the JS console, he almost shat himself.
-
@lucas1 I'm always amazed at people who go through 3-4 years of schooling (and presumably produce thousands lines of code) without ever learning there is such thing as debugger.
-
@cartman82 At my University most of the lecturers were in the IT industry in the 70s, so everything was concepts about files, tests, requirements and most of the programming could be done with nothing more complicated that notepad++.
-
@gleemonk said in Javascript code "encryption":
Then we explored the possibilities of compiling a special bash version that would be able to read encrypted scripts without leaking them, which I enjoyed for sheer absurdity.
I know of systems that do just that. All that it takes is just something to turn off the introspection capabilities in the language in question. It's not perfect — anyone who knows what they're doing can reverse engineer it — but it stops the average idiot from poking their fingers in and breaking stuff.
Mind you, stopping the average idiot can be done by just stuffing the code in a ZIP file and changing the extension, so there's that too…
-
@Yamikuronue You're probably on the right track with their line of thinking. Copyright violation is only one layer of protection (I was about to say a civil matter, but I think in the US there are criminal aspects if caught). By "encrypting" the code they can now show that the the offender broke the DRM too and they might also be charged under the DMCA?
-
@quijibo said in Javascript code "encryption":
By "encrypting" the code they can now show that the the offender broke the DRM too and they might also be charged under the DMCA?
That was my thought. IIRC (IANAL), all that the DMCA requires is that the lock be "effective", and effective is rather loosely defined.
This post brought to you by Calibre and Apprentice Alf. This post not brought to you by Amazon Kindle and 1984.
-
@lucas1 said in Javascript code "encryption":
@Vaire I made some mention of this
https://what.thedailywtf.com/topic/19914/the-basics/29
I showed one of the juniors the JS console, he almost shat himself.
People terrify me. The barrier to entry to this profession is not high enough, at all! :/
My lawn, get off it! = _=/*
-
@Dreikin said in Javascript code "encryption":
That was my thought. IIRC (IANAL), all that the DMCA requires is that the lock be "effective", and effective is rather loosely defined.
But this encryption is so bad it's entirely possible to not notice it, that and it automatically decrypts on every page Load. As @blakeyrat said, a usual minifier would probably be way more cryptic, and space /time efficient.
-
@Vaire said in Javascript code "encryption":
@lucas1 said in Javascript code "encryption":
@Vaire I made some mention of this
https://what.thedailywtf.com/topic/19914/the-basics/29
I showed one of the juniors the JS console, he almost shat himself.
People terrify me. The barrier to entry to this profession is not high enough, at all! :/
My lawn, get off it! = _=/*I went to college and got a computer science degree. Very little time was spent on tools, it was all concepts and algorithms and things. I had to take a VB class to learn any Windows programming. I learned the core parts of building software my first year working.
-
@fwd Your experience and mine are very similar.
Except I didn't take any classes on real programming, I just kinda hammered on it until it was sorted. ;)
-
@swayde said in Javascript code "encryption":
@Dreikin said in Javascript code "encryption":
That was my thought. IIRC (IANAL), all that the DMCA requires is that the lock be "effective", and effective is rather loosely defined.
But this encryption is so bad it's entirely possible to not notice it, that and it automatically decrypts on every page Load. As @blakeyrat said, a usual minifier would probably be way more cryptic, and space /time efficient.
Doesn't really matter, as I understand it - the trigger is the circumvention, regardless of the effectiveness of the protection measure being circumvented.
From http://www.stoel.com/the-anti-circumvention-rules-of-the-digital-millennium :
The DMCA's basic rule prohibits the act of circumventing technological measures that "effectively control access" to a copyrighted work without the consent of the copyright owner. (An "effective access control" is a measure that in the ordinary course of its operation requires the application of information, or a process or treatment, with the authority of the copyright owner, to gain access to the work.) Prohibited acts therefore include descrambling a scrambled work, decrypting an encrypted work, or otherwise avoiding, bypassing, removing, deactivating or impairing a technological measure without the authority of the copyright owner. For example, assume you have a copy of an encrypted e-book that cannot be read without purchasing the right to access it from the publisher. The DMCA says you may not, without authorization from the copyright owner, hack the encryption to read the book. The House Report on the DMCA likened violations of the basic anti-circumvention rule to breaking into a locked room to obtain a copy of a book - the invasion inside another's property is itself the offense. This rule does not apply to access controls on materials in the public domain, e.g. Shakespeare, since they are not protected by the copyright law.
Aside: Does anyone know of a way (other than disabling javascript) to prevent sites from adding extra text on copy? E.g., blogs and such that add "Read more at XYZ" to the end of copied text.
-
@Dreikin yeah, but you could actually not notice it - if the break point was one level out you'd just get the pure js.
-
@swayde said in Javascript code "encryption":
@Dreikin yeah, but you could actually not notice it - if the break point was one level out you'd just get the pure js.
Hm. True. I wonder if you could get out of it by that (if for some
 reason you were to end up in court over this in the first place) using the idea that it's not effective if you can accidentally stumble upon it, and then point to "parallel construction" to shore up your argument.
reason you were to end up in court over this in the first place) using the idea that it's not effective if you can accidentally stumble upon it, and then point to "parallel construction" to shore up your argument.
-
@Dreikin said in Javascript code "encryption":
Does anyone know of a way (other than disabling javascript) to prevent sites from adding extra text on copy?
Assuming it's being done via events, I'd say check for mouse and selection events and get rid of them.
-
If only there were some way of submitting data to a secure server not controlled by the end user, doing all proprietary computations there, and only returning the results to the user. Perhaps marked up in a text language that supports hyperlinks...
-
@Lorne-Kates said in Javascript code "encryption":
If only there were some way of submitting data to a secure server not controlled by the end user, doing all proprietary computations there, and only returning the results to the user. Perhaps marked up in a text language that supports hyperlinks...
I swear to god, are you me? Are you what I am when I am sleeping or something?o_O
-
@Vaire
I had my exit interview yesterday. I mentioned the:- The lack of what I would call basic skills in some team members.
People terrify me. The barrier to entry to this profession is not high enough, at all! :/
It like anything else, the good people go to the top, the rest just end up making WTFs for intranet systems.