Ashley Madison: Crypto Edition
-
So AM smartly hashed their passwords using bcrypt (although it doesn't seem like they salted them). Except…
They then created an alternate login token that was (in most cases1):
@Ars Technica said:md5(lc($username)."::"lc($pass))
So someone finally does (mostly) the right thing with passwords, and what happens? They undermine it by also creating and storing an md5 version using the all-lowercase version of the password

Bonus: graphical summary of the wtf (FTA):
1: The other version was almost as bad, except it used more information: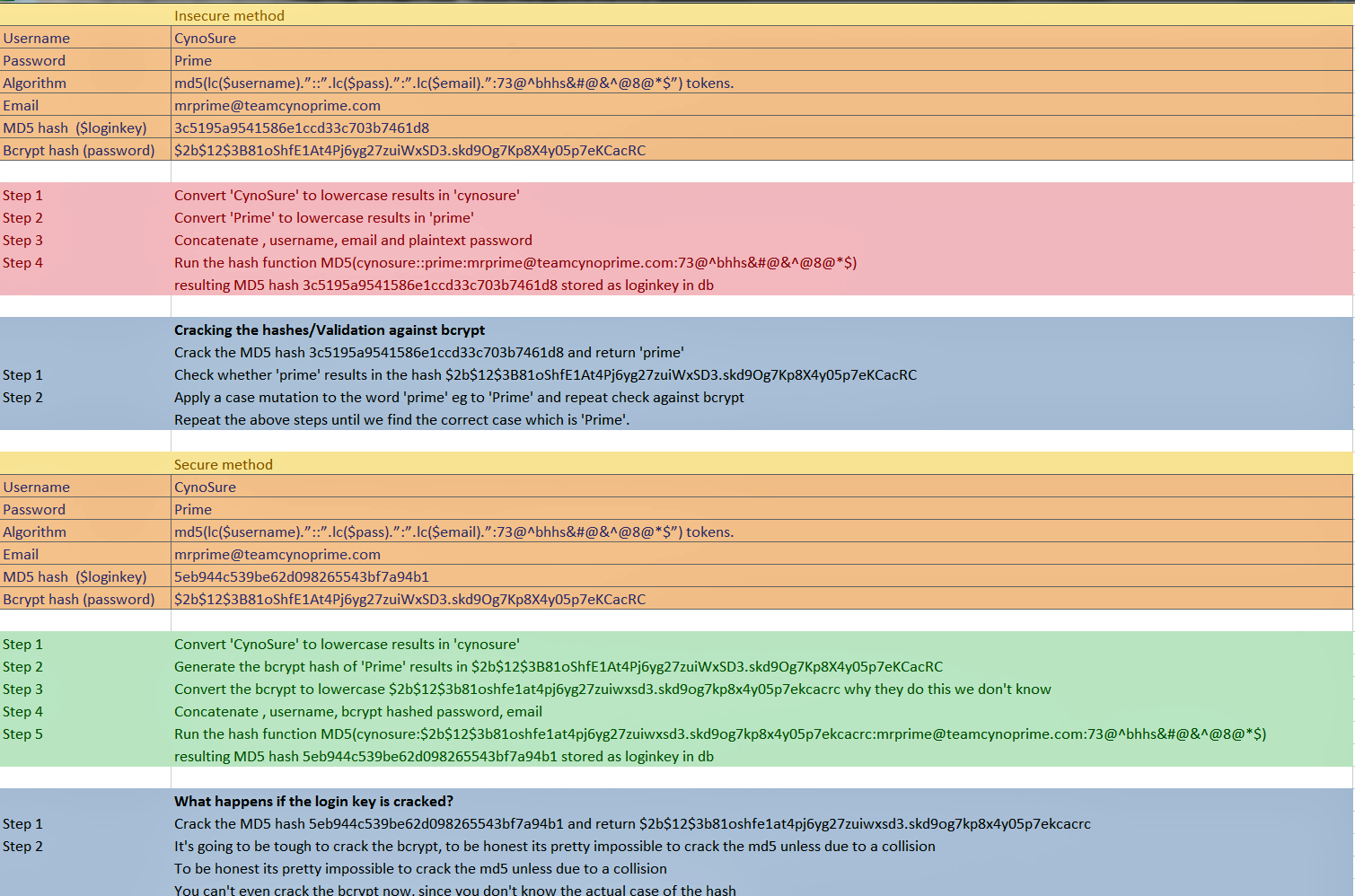
-
Only way this makes sense to me is if the MD5 stuff is leftovers from before a bcrypt cutover. I can't think of a good reason to derive login keys from user credentials instead of just using a chunk of CSPRNG output.
-
Fucking idiots. Everyone knows you should use uc(string). Uppercases are higher in the ASCII chart, and so take longer for bots to get to, and so are MORE SECURE.
Filed under: Will they set up a special hotline for people to report their cracked passwords?
-
Only way this makes sense to me is if the MD5 stuff is leftovers from before a bcrypt cutover. I can't think of a good reason to derive login keys from user credentials instead of just using a chunk of CSPRNG output.
I can't think of a good reason to re-implement datetime functions either, but it's an amazingly popular sport going by the frontpage.
From the CynoSure blogpost:
[quote="CynoSure Prime"]
The $loginkey variable seemed to be used for automatic login, but we didn’t spend much time investigating further. It was generated upon user account creation and was re-generated when the user modified their account details including username, password and email address.
[/quote]Reading further, the first algorithm appears to have been used on account creation, and the second algorithm for account information updates (so let that be yet another
 : two different paths for the same purpose).
: two different paths for the same purpose).
-
-
Not true in the Southern Hemisphere.
No on in the Southern Hemisphere has money, so they aren't AM's target audience.
Filed under: Plus, if they get horny, they can just fuck a sheep or a kangaroo
-
I mean, there are only 2 Australians on the Internet, and we all know the other countries can't afford internet service. So yeah, what @Lorne_Kates said
Filed Under: Can I get a few more groups offended in there? Taking suggestions!
-
I mean, there are only 2 Australians on the Internet, and we all know the other countries can't afford internet service. So yeah, what @Lorne_Kates said
Filed Under: Can I get a few more groups offended in there? Taking suggestions!
Some of them can afford an Internet, but they have to wait for the donkey cart with the wifi-router to wander by to get coverage. And then they're more likely to eat the donkey, because they're starving to death.
Also, blackface.
Also Also, close your fucking tags.
Also also also: Why is there a "Quote entire post" button on the reply-- once you've already decided what you're replying to-- but no Reply With Quote button on each message? WHAT THE FUCK DIPSPOON?
Filed under: Should I meta.d that request?
-
@Lorne_Kates said:
Also also also: Why is there a "Quote entire post" button on the reply-- once you've already decided what you're replying to-- but no Reply With Quote button on each message? WHAT THE FUCK DIPSPOON?
Not supported, doing it wrong, etc
Filed Under: The only reason it's a meme is because it's a meme, holyfrack_500.html_is_a_valid_page
-
Filed Under: The only reason it's a meme is because it's a meme, holyfrack_500.html_is_a_valid_page
And it tells you to post a new topic if the problem keeps happening. Because of course if you 500 on trying to post a new topic, trying to post another one on the same forum is going to help
 .
.Filed Under: Jeez, I'm getting really critical of Discourse today, I wonder why that could be?"
-
Filed Under: Jeez, I'm getting really critical of Discourse today, I wonder why that could be?"
It must be a day starting with "A".
-
@Lorne_Kates said:
Also also also: Why is there a "Quote entire post" button on the reply-- once you've already decided what you're replying to-- but no Reply With Quote button on each message? WHAT THE FUCK DIPSPOON?
Also, the "Quote
entirewhole post" button is special. Because it's the only way of quoting that quotes the raw instead of the baked post, so it's the only way to preserve formatting in the quote. So if you want to quote only part of a post, but want to preserve the formatting, quote the whole thing, then edit out the parts you don't want (including the, full:truein the quote tag, for raisins).There used to be a Q keyboard shortcut to reply with quote, but I think it also used the baked (so no formatting). Also, it doesn't work any more. It's now functionally identical to R: It replies, but it doesn't quote.
-
hey!
we also fuck llamas!
-
@Lorne_Kates said:
Some of them can afford an Internet
This guy stole my internet:
But last night this guy stole his Prime Ministership:
http://resources3.news.com.au/images/2011/08/05/1226108/824063-malcolm-turnbull.jpg
Apparently he was 4 days short of the length of service required for a lifetime PM pension.
-
md5(lc($username)."::"lc($pass))
I'm puzzled: why the fuck would anyone want to convert to lowercase before md5-hashing?
I mean, other mistakes I can understand but this one doesn't make sense, even for idiots.
-
This guy stole my internet:
So that is where the purple cactus dildo went!
Just look:
@another_sam said:http://www.smh.com.au/content/dam/images/1/3/s/p/t/n/image.related.articleLeadwide.620x349.13z3j0.png/1425925092169.jpg
-
Apparently he was 4 days short of the length of service required for a lifetime PM pension.
See, you now have responsible politicians who keep the taxpayer’s concerns in mind!
-
@Lorne_Kates said:
Some of them can afford an Internet
This guy stole my internet:
Australia was governed by Agent Smith?
That does explain your internet policy. And your immigration policy. And why your capital city is called "Whoa".
-
My guess is it's a holdover from a previous login system where both the username and password were case-insensitive. You can't convert it to the new hash unless you know their plaintext password, i.e. the next time they try to log in and provide that password. The old hash can leak password information, though, so you don't want to keep it around any longer than necessary.
TRWTF is if they continued generating the insecure hash even after they switched over, or left it intact any longer than necessary to validate a login and replace it with the new hash.
A more secure approach would be:
Add the new column to your table and redesign your login page to check that first. If the new column is null for the user's ID, attempt the old login method. If it succeeds, generate the hash for the new column, and replace the value in the old column with null. (Optionally, depending on how much disruption you want to cause the user, inform them that passwords are now case-sensitive and require them to change their password at this point.)
Finally, it would probably be a good idea to flag accounts that have shown no activity in the past ~x months as inactive, null out the old password column, and require those users to reset their password if they ever wish to reclaim the accounts.
This way, most of your inactive accounts and all of the active accounts (the first time they log in) will have null in the insecure hash column, meaning that very few accounts will be vulnerable to having the old hashes brute-forced if someone ever gets direct access to your data.
-
Add the new column to your table and redesign your login page to check that first. If the new column is null for the user's ID, attempt the old login method. If it succeeds, generate the hash for the new column, and replace the value in the old column with null. (Optionally, depending on how much disruption you want to cause the user, inform them that passwords are now case-sensitive and require them to change their password at this point.)
I had to do that once. Migrated a site from Derpal to WordPress. Derpal used some shitty, non-salted, easy to break encryption. WordPress used a proper salt. But I couldn't just reset thousands of users' passwords, or expect thousands of people to follow a Password Reset link. (Not when one of the migration's stated goals was Make The Site More Usable and Don't Disrupt Shit... okay, maybe implied rather than stated).
So when someone logs in, it first checks to see if they can login via WordPress method. if that fails, it tries logging in via Derpal. If that succeeds, it takes the plaintext password, WordPresses it, and blanks out the old password.
The site's been live for a while, so I suppose any regulars will have converted by now. Everyone else either is unlikely to come back, or can live with doing a password reset-- or is a spammer with a password of 1234, so fuck them hard with a plug-in.
-
Right... that's exactly what I described, except what I added: figure out your users' usage patterns and decide that if someone hasn't been active in, say, 6 months, the vast majority of the time they won't ever be coming back. You null out their passwords, and the handful who might come back will have to reset their passwords but there are few enough of them that the amount of disruption overall is still negligible.
Like I said, that's optional, but it doesn't cost much in terms of disruption, and it eliminates more insecure passwords from your database.
-
Also, the "Quote entirewhole post" button is special.
(not fixing disquoting)
The what? I've never seen a "quote whole post" button... There's "Reply" and "quote reply" (for selected text). I know, it must be something that is so obvious to ■■■■ that I'm Doing it Wrong™.
-

-
It makes you wonder if it was like placeholder debugging code accidentally left in the finished product.
-
It makes you wonder if it was like placeholder debugging code accidentally left in the finished product.
Given that 98% of their female users are placeholder "debugging" accounts "accidentally" left in the production userset...
-
Ah. I was looking for a button to start the reply. Not something after-the-fact. Guess my thought process works differently then ■■■■'s. I consider that a good thing.
-
@Lorne_Kates said:
@blakeyrat said:
It makes you wonder if it was like placeholder debugging code accidentally left in the finished product.
Given that 98% of their female users are placeholder "debugging" accounts "accidentally" left in the production userset...
Are you sure about that?
-
-
if someone hasn't been active in, say, 6 months, the vast majority of the time they won't ever be coming back. You null out their passwords
Even better, brute force their passwords and convert them to the new hash format. It's a great message to management what the risks are.
-
Yeah but the original passwords were case-insensitive and you don't know how they usually typed it. They might not have typed it in all lowercase.
-
You can still upgrade to more brute-force resistant hashing - you'll just have to handle two comparison algorithms. That still solves your problem without inconveniencing any customers.
-
Maybe I was just lazy and didn't bother to take them out.
-
So instead of 1-step migration and 2 different types of password hashes in your database:
weak hash, case insensitive
strong hash, case sensitive...you'll need 2 steps and 3 types of password hashes:
weak hash, case insensitive
strong hash, case insensitive
strong hash, case sensitive
-
Are you sure about that?
Based on data mining someone did and reported on at Ars Technica or somewhere, it seems like a reasonable guess.
-
See, you now have responsible politicians who keep the taxpayer’s concerns in mind
Well, that's the story they like to repetitively bleat anyway. Despite being the (economically) Liberal party, we're in worse shape than we were when the guys who supposedly spend too much money were in. And on every other front we've gone backwards too. Crazy Catholic nutjob fooled just enough people into thinking he was a better option than Labour, and that only worked because Labour couldn't decide who they wanted to lead. We've had five PMs in five years.
-
@Lorne_Kates said:
Given that 98% of their female users are placeholder "debugging" accounts "accidentally" left in the production userset...
Are you just dirty that you didn't get as many dates as you expected?
-
Maybe, but it doesn't change the fact that the overwhelming majority of female profiles on Ashley Madison are fake.
-
Maybe, but it doesn't change the fact that the overwhelming majority of female profiles on Ashley Madison are fake.
Do you think they hired people to pretend to be these women too. It's a brilliant idea when you think about it. We'll hire 100 women to pretend to be a thousand to give the appearance of life and then charge people for the privilege of using a secretive facebook. We'll probably attract real people to eventually keep the site ticking over and then we can fire the call center while keeping the subscription model.We'll be rick!
-
We'll be rick!
https://40.media.tumblr.com/f5ae2efd0ead6217745a54f81ddad9a3/tumblr_ns476ghtTM1uphguko1_500.png
-
@Lorne_Kates said:
@blakeyrat said:
It makes you wonder if it was like placeholder debugging code accidentally left in the finished product.
Given that 98% of their female users are placeholder "debugging" accounts "accidentally" left in the production userset...
Was it not obvious enough?
-
We'll hire 100 women to pretend to be a thousand to give the appearance of life and then charge people for the privilege of using a secretive facebook.
Small correction: We'll make a small handful of our female employees create fake profiles and converse with clients to lure them into spending more money. These employees will do this as part of their normal job duties, and will receive no additional compensation. We may occasional pay for them to go to dinner with a client as "just a first date" to further keep up the illusion.*
- note: the second part may be isolated to just dating sites, rather than sex sites, but I wouldn't be surprised. **
** also: half the employes pretending to be females are probably guys anyways.
-
@Lorne_Kates said:
half the employes pretending to be females are probably guys anyways.
probably doesn't work so good with
@Lorne_Kates said:
pay for them to go to dinner with a client as "just a first date" to further keep up the illusion
-
@Lorne_Kates said:
half the employes pretending to be females are probably guys anyways.
probably doesn't work so good with
@Lorne_Kates said:
pay for them to go to dinner with a client as "just a first date" to further keep up the illusion
There's subsections of the site for whom that would work perfectly.
-
Relevant:
@BBmotherfuckingC-- I mean Channel fucking Four News said:
Two former employees of Global Personals have described to Channel 4 News how the company carried out industrial-scale deception to dupe innocent daters into parting with their cash.
Ryan Pitcher and Tom (not his real name - he does not want to be identified) were recruited to join Global Personals' 30-strong team of "pseudos" - a dedicated team of staff whose job it was to set up and run fake profiles on the company's network of sites.
-
-
That was magnificently evil. What kind of debaurchy do you engage to train your mind like this.
-
I believe Lorne works in IT.
-
-
Maybe, but it doesn't change the fact that the overwhelming majority of female profiles on
Ashley Madisonthe internet arefakemale.<empty
-
@Lorne_Kates said:
The most evil kind of development.
No. There's always smart TVs from the top company of top
BITCHesCOMPLAINers! They seem to have achieved worse.
 Once seen as bulletproof, 11 million+ Ashley Madison passwords already cracked
Once seen as bulletproof, 11 million+ Ashley Madison passwords already cracked