SHOCKING NEWS: Big Banks Not Ready For Mobile
-
A result that would surprise absolutely fucking no one, big banks report they don't have the IT infrastructure or technical know-how to create mobile payment products. (The article focuses on Canadian banks, but I would bet dollars to high-frequency donut futures that I could throw a dart at a map and hit a country with equally shitty banks).
There's some bitching and moaning about unfair regulations in the article too, but FUCK YOU, "too big to fail" assholes. How does unfair regulation result in me being able to sum up your entire shitty approach to online banking with a single screenshot:
http://i.imgur.com/gfhAXtY.png
-
Oommen said that if banks don’t improve their online user experience,
their ability to sell consumer credit products, car loans and mortgages
may become diminished.I think this article is not about security ...
-
-
My bank does not allow mobile browsers by security policy. They use the cell phone (or rather access to my account) as second component in their two-factor security scheme. Banking on the phone would violate that because the phone would see my password and the access tokens.
Of course, they block by user-agent string, so I can't use one phone as terminal and the other as access token. They also don't notice when my phone is tethered to my laptop and will happily let me do my banking through my phone connection.This is arguably more secure than doing it directly on the phone though.
-
@Lorne_Kates said:
(The article focuses on Canadian banks, but I would bet dollars to high-frequency donut futures that I could throw a dart at a map and hit a country with equally shitty banks)
I think Europe's a bit further ahead in the specific area of putting lipstick on the pig of banking APIs. Probably further behind in some other way though.
-
So my company provides downstream services to the financial and insurance industries. Let me tell you about the time a major investment bank sent us a dump of their complete account list including names, addresses, account numbers, credentials, balances, social security numbers, etc.
As a CSV. Unencrypted. Via email.
Nobody was fired. Nobody really even cared when it was pointed out. After all, we're a trusted vendor!
-
...
And which country do I never want to do banking business with ever?
(Almost certainly the one that holds my employer's head office)
-
@Lorne_Kates said:
encoding
What does encoding have to do with security? Do you mean encryption?
Sounds like you should be working for the banks.
-
So my company provides downstream services to the financial and insurance industries.
Sounds like you're about ready to do the same for healthcare. The practices on the ground by the medics are no better despite the efforts of many techies…
-
Murica!
I have a sizable list of banks, or financial entities and health insurers with whom I will not do business. It approaches unity with our client list.
-
When I said "insurance", I meant health insurance.
Or third biggest client category is, bizarrely, travel agencies. They are somewhat better. But only because they don't have your SSN to give us.
-
When I said "insurance", I meant health insurance.
I was thinking about the doctors and hospitals themselves. Take my advice, don't get sick.
-
I have a sizable list of banks, or financial entities and health insurers with whom I will not do business. It approaches unity with our client list.
Personally, I assume they're all guilty until proven innocent (which is never). Thus, I do the minimum necessary business with all of them...
-
Those are increasingly owned by insurers anyway. I know of several insurers that are spinning off their medicare and medicaid business lines into subsidiaries or new companies so the parent company can own hospitals.
-
What does encoding have to do with security? Do you mean encryption?
No, he means encoding the plain text to something that's not plain text, meaning setting your password as
robert' DROP TABLE users;won't do anything.Really you should be hashing the entire thing the moment you touch it, but we know some companies are... special....
-
@Lorne_Kates said:
But what if your bank card number happens to contain all of the digits? Then you have to use part of it if you want the extra security you get by having numbers in your password.
-
@Lorne_Kates said:
But what if your bank card number happens to contain all of the digits? Then you have to use part of it if you want the extra security you get by having numbers in your password.That's fine - just use special char.... oh wait.
-
I can't fathom the mentality that thinks
SpiderWebis a good example of a financial-grade password.
They should've usedSwordFish...
-
meh, banks can't even internet...
a few days ago i wanted to download my movements summary.
this is what the bank's site sent me
resumen.pdf (58 Bytes)
it is a text file with this content:
[ERROR]
ID=2167
MSG=No documents meet the search criteria
-
I don't see the problem. There's lots of numbers to choose from.
-
But only because they don't have your SSN to give us.
Ugh. Here, have a derailment. I took my cat to a new vet once, and the paperwork they gave me had a spot for SSN. I just left it blank to see what would happen, but the receptionist didn't say anything about it. I wonder how many people blithely filled it in.
-
I took my cat to a new vet once, and the paperwork they gave me had a spot for SSN.
For the cat?!
-
No, he means encoding the plain text to something that's not plain text, meaning setting your password as robert' DROP TABLE users; won't do anything.
Really you should be hashing the entire thing the moment you touch it, but we know some companies are... special....
Yes, this. At some point, they take the password, and send it to another part of the system. Maybe they take your login request, turn it into XML, and send it to some central authentication system.
So if your password has < or >, then their hand-baked, string-concating XML generator will break.
xml = "<user_auth_request><username>" . input("username") . "</username><password>" . input("password") . "</password></user_auth_request>"
Because object serialization is hard.
Some bank developers may get clever and try to "encode" the string with input("password").replace("<", "<").replace(">", ">"). But there's SO MANY special characters, and typing that many replaces is hard. Someone will make a typo eventually and break the system. .replace(">", "<").
Because regexes are hard. Because refactoring out common functions are hard. Because encode_base64 is hard.
Rather than just IMMEDIATELY hashing and/or escaping and/or encoding the password string into something universally safe and manageable, the bank instead comes up with a USER-RESTRICTING policy to solve this "hard" programming issue. Sure, it reduces security, but it's easier to program for.
I'm sure there's an anti-pattern for this. You come across a problem. The problem is caused because you're trying to do something special/clever/homemade. Rather than adopting universally-accepted solutions/libraries, you instead restrict user actions to conform with your shitty, shitty software.
Filed under: 500
-
-
@Lorne_Kates said:
input("password").replace("<", "<").replace(">", ">")
Discourse strikes again!
Or use triple backtick…
``` input("password").replace("<", "\<").replace(">", "\>") ```
-
@Lorne_Kates said:
input("password").replace("<", "<").replace(">", ">")
<_< >>
...
--Oh jesus backslash-fic-fucking Christ, can Discourse not do ANY fucking thing correct?
Filed under: 0 posts since last Discourse bug
-
For the cat?!
If it were for the cat my story would've been about the silly value I put there.
-
@Lorne_Kates said:
Just as scary as the implication of this rule is that we don't know how to use hashing or encoding-- so somewhere, your password is being handled in plaintext
Without trying to defend the bank, I fail to see how you came to the conclusion that they store the password in plaintext from what is mentioned in your initial post. I mean, yes, it would not actually be a surprise if it were, judging from the general level of security awareness (or abysmal lack thereof, rather) displayed in the quoted guidelines; but there's no actual evidence for it (like a "forgot my password" button that sends it back to you via email or something).
-
Maximum length.
-
Maximum length.
... which can easily be checked (and rejected) by validation after the user entered his password, but before writing it (hashed) to the DB. Next please.Unless you mean there's a varchar(12) password field in the DB... but that's not necessarily the case. The 12-character limit might just as well be a brain dead specification decided upon long before the first line of code was ever written.
-
The only obvious reason to impose a maximum length is because you can't handle longer passwords, likely because of a DB column size limitation for the plain password.
-
I can just as well imagine a clueless PHB sitting there, decreeing that passwords must not be longer than 12 characters because otherwise users would forget them too easily. And then it's hammered into the design to the unheard wailing of protest of programmers everywhere.
Doesn't mean they're stored in plaintext in the DB. There's still a chance left a developer with a shred of common sense chose to do the right thing when it came to actually implement this.
-
@Lorne_Kates said:
Oh jesus backslash-fic-fucking Christ, can Discourse not do ANY fucking thing correct?
I thought that was self-evident. Apparently I was wrong.
-
-
Without trying to defend the bank, I fail to see how you came to the conclusion that they store the password in plaintext from what is mentioned in your initial post.
As mentioned below, length restrictions. As I mentioned above, character restrictions. Combined with "what are the last 3 characters of your online banking password" questions asked on the phone.
If it isn't stored in plaintext, then it's certainly handled in plaintext (my XML example). Which means it's being LOGGED in plaintext somewhere, and transmitted in plaintext.
We'll just have to wait for the next banking databreach to be publicized to find out.
-
@Lorne_Kates said:
"what are the last 3 characters of your online banking password" questions asked on the phone.
 … Every bank and similar institution in this part of the world repeats the mantra “Employees of $bankname will never ask you for your password.”
… Every bank and similar institution in this part of the world repeats the mantra “Employees of $bankname will never ask you for your password.”
-
@Lorne_Kates said:
"what are the last 3 characters of your online banking password" questions asked on the phone.
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Holy
 on a crapstick
on a crapstick
-
I can just as well imagine a clueless PHB sitting there, decreeing that passwords must not be longer than 12 characters because otherwise users would forget them too easily.
That's my guess, too. The programmers could implement password handling correctly, and the PHB would never know. The PHB might possibly be just barely smart enough to try entering a password like "123456789!@#$abcdef" to make sure that it fails, and then yelling at the programmers if it works.
-
Children are like pets, taking them to the vet just makes sense.
-
@Weng said:
But only because they don't have your SSN to give us.
Ugh. Here, have a derailment. I took my cat to a new vet once, and the paperwork they gave me had a spot for SSN. I just left it blank to see what would happen, but the receptionist didn't say anything about it. I wonder how many people blithely filled it in.
How else will they file any non-payment debt with the
mafiacredit agencies?
-
Hey, I thought that was my bank! But now I can do you one better:
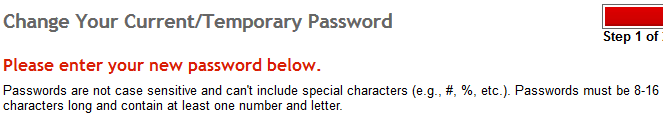
^^^ "Passwords are not case sensitive..."
At least they're 8-16 characters. That makes up for reducing the alphabet down by nearly half, right?
-
… Every bank and similar institution in this part of the world repeats the mantra “Employees of $bankname will never ask you for your password.”
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Holy on a crapstick
Oh, but they're not asking you for your password. They're just asking you for the last 3 digits of your "online password" of security verification. This is when you call THEM
^^^ "Passwords are not case sensitive..."
And my bank account is not decimal point sensitive. $1,000,000,000, please.
.
-
How else will they file any non-payment debt with the mafiacredit agencies?
Since I paid cash, that wasn't my concern.
-
I'm beginning to think that if a bank is about to fail, they can get a bailout, but they have to hand over control of their company to some random person on the internet.
Because seriously, it's not like it will be that much worse on average.
-
I'm beginning to think that if a bank is about to fail, they can get a bailout, but they have to hand over control of their company to some random person on the internet.
Bank of America: HANG IN THERE KITTY!!!!11!!bbq
-
I took my cat to a new vet once, and the paperwork they gave me had a spot for SSN.
I don't want to do another "Australia is better than the US", but... it's illegal for the vet to even ask for my Tax File Number (TFN) here. And cats don't have one. The people who can ask for it are:
- The Tax Office, on my tax return.
- My employer, who will withhold taxes from my wages and uses the TFN to report those withheld taxes to the Tax Office.
- The bank, who will withhold taxes from any interest paid to me, blah blah report them to the Tax Office.
And except for the Tax Office, I am not required to supply my TFN when an employer or the bank asks. It's in my interest to do so, otherwise they are required to withhold taxes at the highest marginal rate and I will be giving the government an interest-free loan until tax return time, but it's not required.
-
My bank does not allow mobile browsers by security policy.
My bank has a mobile banking app. I'm pretty sure it uses PhoenGap or some other shitty browser-based "application" library because it feels... ugh. Anyway, you can't use your nice, secure, long online banking password with it. For "extra security", instead you can only use a four-digit PIN. keyspace of 10,000 instead of millions for a decent length password.
My bank also likes to call me and ask for my name and date of birth. The poor person on the other end doesn't know what to do when I tell them they're a random caller and ask them to prove who they are before I give them the exact information they need to perform identity theft.
Banks are fucking retarded.
-
I don't want to do another "Australia is better than the US", but... it's illegal for the vet to even ask for my Tax File Number (TFN) here.
In theory, it's illegal to use SSNs for 99.9% of the stuff they're used for here. Or at least, that's what they were originally. By now, everyone's SSN has been spread around all over the place, it's hardly worth considering private.
-
-
@gleemonk said:
My bank does not allow mobile browsers by security policy.
My bank has [many stupid policies]
Banks are fucking retarded.
Mine isn't. It used to be a credit union and is still structured like one. CEO Phylip Doughty has been quietly and competently managing it ever since it was Ed Credit, and has consistently shown all the signs of Clue.
It's recently got rid of the world's best online banking website in favour of something the everything-is-a-phone brain worms have clearly been chewing through, but that's about as bad as it ever gets. I honestly can't complain about anything else.
 Numerals in Unicode - Wikipedia
Numerals in Unicode - Wikipedia