Not a button
-
-
And nothing whatsoever to do with the fact that there are people here with way too much free time that like to spam?

/cough/
/cough/
-
-
not hard
I find it mildly amusing that @boomzilla's passed me in post count. You know, if you'd stop chattering for a bit, you could drop the spoon in his lap.
-
'if you don't have anything of value to say keep quiet'
That's a barrier to post count.
-
possibly, but i doubt he'd keep it long. ;-)
also being quiet does not sound..... fun. y'know?
-
If I'm strapped for time, sometimes I open a lengthy topic and hit End. BAM THREAD AND POSTS READ.
-
Well topic read anyway. The pages that steer never on screen aren't read.... They just so showing in the typos list.
-
The pages that steer never on screen aren't read.... They just so showing in the typos list.
That last one is apt.
Shouldn't all your posts be typo lists?

-
Hmm....I made the last one on purpose.... Didn't notice the other two...
I need to spell check better....
As per usual not fogging speller for correcting my spelling.... Too easy of a target that is.
-
Not even trying for a
 just wanted to make the joke.
just wanted to make the joke.
-
Fair enough then. As you were.
/me walks of smartly to inspect a different barracks
-
I find it mildly amusing that @boomzilla's passed me in post count. You know, if you'd stop chattering for a bit, you could drop the spoon in his lap.
I think I'd rather keep my charter membership in the 5% club. Something no one else has.

-
Is that a challenge?
-
Is that a challenge?
if it is it is one we can only win by knocking him out of 5%. none of the other original 5%ers are still holding that badge (both @frostcat and i have technically never left the top 5% but we have had to hand in the badge and take up the spoon so according to @boomzilla that doesn't count)
-
In other news, cheers! I won the 2⁹ badge today.
-
I won the 2⁹ badge today.
get thee to the thread of bite sized confections so that we might celebrate that glorious win!
-
BAM THREAD AND POSTS READ.
BAM no, you dont get credit for reading the posts you skipped. And now dicsourse will never give you a way to find those posts that you skipped ever again.
-
get thee to the thread of bite sized confections so that we might celebrate that glorious win!
We have a Maltesers thread?
Filed under: Can't be cupcakes, they're too big for bite-sized
-
Well crap. They should warn users about that. Maybe a toaster window?
-
I'm like Mr. Ed. I only speak when I have something to say.
Mr. Ed - Intro (Opening Theme) – 00:42
— PsychoDad1860Fuck yeah Mr. Ed.
-
-
Try installing Windows Server .
"Your password does not meet the password policy set on this system, please consult with your Administrator"
OMG WTF BBQ I AM TRYING TO CREATE THE ADMINISTRATOR.
Follow up on my issue by the way.
The omission of providing the password requirements? It's deliberate. Because this makes the whole thing more secure, somehow.
Yeah, I have that in writing. Maybe it's just me but a rate limiter on the amount of password attempts inside a minute would work better and not annoy people.
-
Oh, and another thing, just fresh from today:
They installed a new web filter at my school. This thing blocks Wikipedia because it uses redirects (e.g. something like from www.wikipedia.de to de.wikipedia.org - don't remember the exact offending redirect). It does this shit with other login pages as well - you cannot login to www.live.com, for example. Though in the case of login pages, it will simply swallow any login attempts silently.
But I found out how to work around that. Whenever the page runs across such a redirect, it displays an info page instead with a link to a browser setting which installs a custom "Google Safe Search".
So, if you want to access Wikipedia (or, indeed, any other page reliably) your workflow runs this way:
- Try something until you run into this info page
- Install the Google Safe Search
- Change the default search to this
provider - Use the browsers search feature to search for "Wikipedia"
- Click on the first result
- Repeat Step 4&5 as needed (if you search for www.live.com and then use the search result to login, it will work. I'm pretty sure there's either a MITM attack or problems with the certificates involved)
Of course, since we're using something akin to DeepFreeze and the moron didn't change the image accordingly, I had to repeat that about 80 times today.
Bonus points: Google's search suggestions becomes slow as molasses because this filter also filters the AJAX calls to the search API. And image search becomes largely unusable.
Oh, and Dropbox? Inaccessible. Because it's a "Filesharing" site.
-
If I had to put up with that BS I'd root my phone so I could tether.
-
Well, let's put it this way: If you can find a working network port then a switch and an access point will solve quite a number of problems.
-
That's certainly true.
-
To give you an idea of the level of proficiency those guys sport:
They took down the semi-public WLAN*) for a week because someone connected with a WindowsXP laptop infected with Conficker. And they were absolutely stumped as to how to deal with this device.
I was then praised as a genius when I suggested using either nmap to actively scan or port replication to a server running something like Snort with appropriate rules.
*) semi-public: Anyone with an account can login. That includes pupils.
-
-
And in The Matrix so it's got the 'cool' factor too?
-
Sounds like said filter is easily DDOSable if its so slow. hint hint
-
Sounds like said filter is easily DDOSable if its so slow. hint hint
I'm not sure if 25 clients are sufficient but I think I can get my pupils to act in concert. For science, of course!
-
Today's update on the filter issue: Turns out that our IT support wasn't the one fat-fingering the rules, it was the company producing the filter. We're not the only school hit by the morons.
Of course, a rollback is not possible.
-
Generally, individual businesses don't set up their own filtering rules because that would require them having knowledge of every website they don't want their employees going on.
<Source: my butt>
-
Do individual businesses have the ability to whitelist sites that they know they need? Or could the filter operator just lock them out of something business-critical? (Naturally, if there's a whitelist then there's the possibility of it being abused…)
-
Generally, individual businesses don't set up their own filtering rules because that would require them having knowledge of every website they don't want their employees going on.
<Source: my butt>
I think you're confusing "rules" and "stuff the rules apply to".
For instance, you have a list of rules you can subscribe to:
- No Porn
- No Filesharing
- No Hatespeech
And then you have someone supply the actual content for those rules.
-
So, another update: They got rid of the company that installed this moronic filter I was talking about.
Naturally, they had to contract someone else. How do I know this?
Because this morning, upon hooking my laptop into the WLAN, first my Dropbox sync utility displayed a red cross, OneNote stated that "I don't have the permissions to access my account" and then Chrome told me that it was unhappy about the Gmail certificate...
... yeah. Turns out that they tried a serious MITM attack - upon inspecting the offered certificate, I was greeted by the new company's name instead of Microsoft, Google or Dropbox. Our administrator (who sadly doesn't have direct control over those morons) wasn't too happy either.
Half an hour later, that particular "feature" was turned off.
Only that they now had broken DNS - only about 5% of all DNS lookups actually succeeded.
-
Only that they now had broken DNS - only about 5% of all DNS lookups actually succeeded.
...don't use them for DNS either?
-
...don't use them for DNS either?
Well, that was my first instinct but there was this small problem:
Using
ipconfig /allyielded this gem:DNS Servers . . . . . . . . . . : 8.8.8.8 8.8.4.4Thus I dare say that they botched the iptables rules...
-
[root@NCL-DEVELOPER bin]# dig google.com @208.67.222.222 -p5353 ; <<>> DiG 9.3.6-P1-RedHat-9.3.6-25.P1.el5_11.2 <<>> google.com @208.67.222.222 -p5353 ;; global options: printcmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 26203 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0 ;; QUESTION SECTION: ;google.com. IN A ;; ANSWER SECTION: google.com. 286 IN A 216.58.209.238 ;; Query time: 19 msec ;; SERVER: 208.67.222.222#5353(208.67.222.222) ;; WHEN: Mon Feb 16 16:40:01 2015 ;; MSG SIZE rcvd: 44 [root@NCL-DEVELOPER bin]#I'm assuming if they're incompetent enough to screw up MITM and DNS, they're incompetent enough to just consider port 53 traffic...
-
Will consider that one if they haven't fixed it by tomorrow. Thanks :)
-
Oh, that reminds me ...
Could you make the FAQ link a relative link? Or is that impossible?
-
Could you make the FAQ link a relative link? Or is that impossible?
This?:
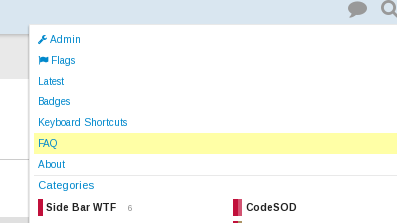
I have no control over that (beyond mucking around with it like what happens with the CSS styles.)
Why?
-
It's a weird story.
It had to do with a failing DNS server, not having enough rights to change the one the machine used and manually using nslookup.
-
And you can't make a hosts entry either, I assume?
-
And you can't make a hosts entry either, I assume?
I naturally presumed that, since changing DNS usually requires the same Windows permissions as modifying
%SystemRoot%\system32\drivers\etc\hosts(or whatever it is this year.)I'm assuming Windows, since
HOSTALIASESis generally a thing under Linux.
Edit: Having re-read the post, the other reason I assumed that was because of
ipconfiginstead ofifconfig...
-
DNS over port 5353 worked just fine, by the way.
While I was playing with that, I noticed another problem: Usually, after selecting the public WiFi, you are redirected to a captive portal to log in.
Well, currently you're shit out of luck if you don't know the IP adress of the portal because that thing neither opens on its own after WiFi selection nor does it redirect you to the portal inside a browser...... well, on the other hand, you're finally able to log in with more than one device at the same time.
-
Well, currently you're shit out of luck if you don't know the IP adress of the portal because that thing neither opens on its own after WiFi selection nor does it redirect you to the portal inside a browser...
I thought that pop-up was because modern OSes do a trial connect (a HEAD or GET or something) to some “well-known” service to see if they can get out; if not, they repeat the request and pop up the window with the results. Or is it something that's actually delivered by DHCP (and which is broken in your case)? That would actually make some sense…
-
I'm not too sure how it works but it did work for a while. And if you didn't get the captive portal right after connecting, you'd at least get it after trying to access the first outside webpage.
In fact, the redirect part still works - it's just that the portal page never comes up for some reason.
-
I thought that pop-up was because modern OSes do a trial connect (a HEAD or GET or something) to some “well-known” service to see if they can get out; if not, they repeat the request and pop up the window with the results.
* Windows 7 SP1+ and Windows Phone 7+ checkdns:dns.msftncsi.comandhttp://www.msftncsi.com.- iOS 4+ and OS X 10.7+ check
http://www.apple.com/library/test/success.html. - Android checks
http://clients3.google.com/generate_204andhttp://www.google.com/blank.htmland "something else". - Firefox checks
http://detectportal.firefox.com/success.txt, though it only matters on the Flame right now.
If those give back incorrect information but otherwise succeed, you're behind a captive portal.
- HTTP response code 511 is as-of-2015 reserved for captive portals, but no one uses it.
- DHCP option code 72 is as-of-1997 reserved for sending clients WWW addresses, but no one uses it.
- The IETF is considering a proposal to specify a DHCP option code specifically for captive portals, but since there is no such code yet, no one uses it.
- iOS 4+ and OS X 10.7+ check