The entire Wordpress ecosystem was nearly well and truly fucked
-
Summary:
- Wordpress' autoupdate server allows the client to dictate the hashing algorithm for accepting "authenticated" updates
- It allows an extremely crypto-insecure algo to be chosen
- Once authenticated, you can do command injection on the server itself
- Autoupdate doesn't use any authentication or signing when distributing updates
- Thus, every single Wordpress site (~27% of all sites in existence) could have been compromised at once
:/
-
@Lorne-Kates Meh, at least it's not Discourse!
Filed Under: 27% of websites being Discourse is more scary than anything you just described!
-
@Kuro said in The entire Wordpress ecosystem was nearly well and truly fucked:
at least it's not Discourse!
What if you could exploit the letter avatar CDN to hack all Discourse installations at once?
-
@hungrier said in The entire Wordpress ecosystem was nearly well and truly fucked:
What if you could exploit the letter avatar CDN to hack all Discourse installations at once?
You'd be given a knighthood?
-
And yet I am still routinely told how wonderful WP is.
-
@Arantor said in The entire Wordpress ecosystem was nearly well and truly fucked:
And yet I am still routinely told how wonderful WP is.
It is, kind of, if you know wtf you're doing.
The
 is giving the webserver write access to its folders.
is giving the webserver write access to its folders.WordPress auto-update sounds as much retarded as Win10 auto-update
-
@TimeBandit except that it may or may not spontaneously break parts of your site without warning... wait that sounds like Win10 substituting 'site' and 'computer'.
It is as retarded as Win10 because you have to make yourself kinda insecure to be able to use it and it
COMPLAINBITCHes so much if you don't let it have its way - at least that's been my experience.I'm also not even clear what they've changed, other than the core theme, in the last few years of updates.
-
@Arantor said in The entire Wordpress ecosystem was nearly well and truly fucked:
It is as retarded as Win10 because you have to make yourself kinda insecure to be able to use it and it
COMPLAINBITCHes so much if you don't let it have its way - at least that's been my experience.We use WordPress here, and you can be sure that the webserver can't write anywhere except wp-upload.
I manage a couple Moodle install (please God help me), and there is the same functionality to update it automagically.
I'll let you guess if I let that thing update itself.
-
@Arantor said in The entire Wordpress ecosystem was nearly well and truly fucked:
I'm also not even clear what they've changed, other than the core theme, in the last few years of updates.
Mostly, they've been fixing bugs and security holes. By introducing new and more unlikely bugs and security holes.
-
@Arantor said in The entire Wordpress ecosystem was nearly well and truly fucked:
@TimeBandit except that it may or may not spontaneously break parts of your site without warning... wait that sounds like Win10 substituting 'site' and 'computer'.
At least it's opt-out.
They do do an ok job at making sure they don't HORRIBLY break backwards compatibility. I have had a couple plugins break because the plug-ins did things The Stupid Way, and newer versions of Wordpress don't allow The Stupid Way.
Normally, plug-ins are updated because the authors pay attention to the dev-branches, so if there is a breaking update, the updated plug-in auto-updates too any everything's dunkin' donuts.
But sometimes a plug-in is unmaintained, and gets broken and never fixed.
Needless to say, Wordpress chose between "break some plugins" and "leave critical vulnerabilities open"-- especially since so many wordpress sites aren't run by-- ah-- competent IT people.
-
@Lorne-Kates said in The entire Wordpress ecosystem was nearly well and truly fucked:
dunkin' donuts
E_TIM_HORTENS_HAS_BETTER_DONUTS
-
Yeah, but what's your alternative? There's a reason it's 27% of the web. It's a security nightmare, but it's usable as shit compared to the alternatives.
-
@Yamikuronue said in The entire Wordpress ecosystem was nearly well and truly fucked:
but what's your alternative?
Get a competent coder to clone the Wordpress interface from scratch?
Fork Wordpress and gradually improve its (code) design?
Fork some other system and gradually change its UI to make it like Wordpress?You'd think with 1/3rd of the web at stake, there would be someone willing to throw some money at one of those options.
-
@anonymous234 None of that help the little guy who just needs a damn blog, tomorrow. I'm looking at a choice between something like Jekyll, because I'm blessed with the IT skills to make that happen, or something like Wordpress, and I don't want to spend a year writing my own Wordpress before I can go live. And Jekyll can't schedule posts.
It's the same with Php: I can invest thousands in getting .net coders to do a website, or I can pay the kid down the street $50 to whip me up a couple pages in PhP. Only now we're getting competition in that space with your neo-dreamweaver drag-and-drop bootstrap sitebuilders.
-
WordPress itself provides no signature verification of the software being installed. It will trust any URL and any package that is supplied by api.wordpress.org.
They could at least sign the releases with public key cryptography.
That way the distribution servers can be completely compromised, but you can't make a malicious release unless you steal the priv key from the lead developer's machine.
-
Also I am surprised that exploits of automatic update systems are not more common.
Sure they may be guarded, but its such a perfect vector of attack.
-
@Adynathos said in The entire Wordpress ecosystem was nearly well and truly fucked:
Also I am surprised that exploits of automatic update systems are not more common.
And you know they aren't how?
-
@pydsigner said in The entire Wordpress ecosystem was nearly well and truly fucked:
And you know they aren't how?
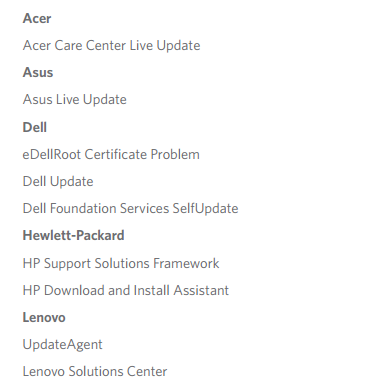
I would expect news like this:
- Windows update delivers malware (not written by Microsoft this time)
- majority of users of [popular program] compromised through automatic updates
Maybe it happens but doesn't get much attention...
-
@Yamikuronue said in The entire Wordpress ecosystem was nearly well and truly fucked:
I can invest thousands in getting .net coders to do a website
Sounds like you need to shop around a bit. OK, you may not be able to get down to $50, but a couple hundred should be able to get you something.
-
@RaceProUK said in The entire Wordpress ecosystem was nearly well and truly fucked:
@Yamikuronue said in The entire Wordpress ecosystem was nearly well and truly fucked:
I can invest thousands in getting .net coders to do a website
Sounds like you need to shop around a bit. OK, you may not be able to get down to $50, but a couple hundred should be able to get you something.
Both "something" and what @Yamikuronue wants are a bit vague so

-
@pydsigner Given the mention of WordPress, I'm thinking a food mixer :P
-
@RaceProUK said in The entire Wordpress ecosystem was nearly well and truly fucked:
@pydsigner Given the mention of WordPress, I'm thinking a food mixer :P
But will it ble--
[sig] Killing Memes Since 2010

-
@Yamikuronue said in The entire Wordpress ecosystem was nearly well and truly fucked:
Yeah, but what's your alternative? There's a reason it's 27% of the web.
I'm content with having a danish pastry as an alternative to a donut, whatever 27% of the web says.
Filed under: Fun with context
-
@Adynathos But precisely because it's such an obvious vector of attack, any competent company will make sure it's properly designed.
And contrary to popular belief, not everything can be hacked. Use a secure public-key algorithm, don't have any bugs on your checking code (which should be less than 3 lines), let one of them security companies hold the private key on your behalf, profit.
-
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
let one of them security companies hold the private key on your behalf
WUT?
-
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
And contrary to popular belief, not everything can be hacked
All software can be hacked, simply because it's software. The best you can hope for is that it's not worth people's time to try.
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
let one of them security companies hold the private key on your behalf
You can have my private key when you pry it from my cold dead paws!
-
@dkf I don't know if that's a thing so I kinda assumed it was.
The private key is, well, key to the system. If it leaks, you're fucked. If you're a small company, keeping a file completely private for years/decades can be very hard (what's stopping someone from breaking in at night into your server room and taking your hard drives?) so I'd rather let someone else do it. And then use some other form of authentication (like another key that can be revoked and re-issued) to talk to them.
Yes, I know, big companies bad, trust bad, all that, but in the end of the day I don't think VeriSign will risk their reputation, which is literally the most important thing a security company has, to hack a few computers.
-
@RaceProUK said in The entire Wordpress ecosystem was nearly well and truly fucked:
All software can be hacked, simply because it's software.
Hack this then
#include <stdio.h> int main (void) { printf ("Hello, world!\n"); return 0; }
-
@TimeBandit Not worth my time :P
-
@RaceProUK said in The entire Wordpress ecosystem was nearly well and truly fucked:
@TimeBandit Not worth my time :P
Of course, you are busy catching up months' worth of posting here !
-
@RaceProUK said in The entire Wordpress ecosystem was nearly well and truly fucked:
You can have my private key when you pry it from my cold dead paws!
That is the right attitude for your personal keys, but I would not want to be the person responsible for securing a company's key.
I think paying the security company to hold it is not necessarily for security but for the peace of mind:
When the key is leaked, it is their fault - while your decision to trust them is justifiable, because they had a good reputation. That is what you can tell your boss and your customers.
-
@Adynathos Ah, blame-shifting: quite useful

-
$ gcc TimeBandit.c $ LD_PRELOAD=./hax.so ./a.out Pwnt!Does that count? (hax.so replaces
puts()called byprintf(), and does something else)
-
@TimeBandit said in The entire Wordpress ecosystem was nearly well and truly fucked:
I manage a couple Moodle install (please God help me), and there is the same functionality to update it automagically.
Academic software that's not from the IT department:

One of those is where where I found my first remote exploit, to root with a bit of luck.
-
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
The private key is, well, key to the system. If it leaks, you're fucked. If you're a small company, keeping a file completely private for years/decades can be very hard (what's stopping someone from breaking in at night into your server room and taking your hard drives?) so I'd rather let someone else do it.
Uh ... the passphrase? Not that it kept them from taking my drives but it keeps the drives from being anything but an empty hard drive to them.
Inb4 bus factor :)
-
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
If you're a small company, keeping a file completely private for years/decades can be very hard (what's stopping someone from breaking in at night into your server room and taking your hard drives?) so I'd rather let someone else do it. And then use some other form of authentication (like another key that can be revoked and re-issued) to talk to them.
You use two keys, one you keep in a safe when not in use and you use it to sign the other one which is your production key. Or rather you sign the public key, of course. The point being that the high security private key is hardly ever used, and the business will need a way to keep other things secure too (such as the petty cash for office supplies).
Hacking something that's on an unplugged memory stick in a sealed metal box is a bit tricky…
-
@TimeBandit said in The entire Wordpress ecosystem was nearly well and truly fucked:
@RaceProUK said in The entire Wordpress ecosystem was nearly well and truly fucked:
All software can be hacked, simply because it's software.
Hack this then
#include <stdio.h> int main (void) { printf ("Hello, world!\n"); return 0; }
Step 1: compromise stdio.h....
-
@TimeBandit said in The entire Wordpress ecosystem was nearly well and truly fucked:
@RaceProUK said in The entire Wordpress ecosystem was nearly well and truly fucked:
All software can be hacked, simply because it's software.
Hack this then
[...]

On an ideal CPU this would probably be kinda hard. However, that's not what it will run on.
-
@Lorne-Kates said in The entire Wordpress ecosystem was nearly well and truly fucked:
Step 1: compromise stdio.h....
Pffff... better just compromise the compiler
-
@TimeBandit said in The entire Wordpress ecosystem was nearly well and truly fucked:
@Lorne-Kates said in The entire Wordpress ecosystem was nearly well and truly fucked:
Step 1: compromise stdio.h....
Pffff... better just compromise the compiler
Pfffff... better just compromise Ken Thompson.
-
@Lorne-Kates said in The entire Wordpress ecosystem was nearly well and truly fucked:
Pfffff... better just compromise Ken Thompson

-
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
@Adynathos But precisely because it's such an obvious vector of attack, any competent company will make sure it's properly designed.
Yup. Oh wait.
In my opinion, it's because MitM attacks are not attractive to script kiddies, plain and simple; even on wireless, they take real work and knowledge. So while this is an attractive vector, it's one more likely to be exploited by advanced threat agents such as governments, whose successes are rarely publicized.
-
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
what's stopping someone from breaking in at night into your server room and taking your hard drives?
Besides disk encryption?
Guns. I have lots of guns.
-
@Adynathos I've always assumed that Windows Update is designed to only work with updates signed by a particular code signing key.
That's why, when Windows Update itself is updated, you have to install that update first before you can install other Windows Updates.
Or at least you had to in Windows XP and older, not sure if that still applies in Windows 7 and newer.
-
@Polygeekery said in The entire Wordpress ecosystem was nearly well and truly fucked:
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
what's stopping someone from breaking in at night into your server room and taking your hard drives?
Besides disk encryption?
Guns. I have lots of guns.
How about... Locked doors? Those seem to be slightly more effective than guns, especially while you're sleeping.
-
@Polygeekery said in The entire Wordpress ecosystem was nearly well and truly fucked:
@anonymous234 said in The entire Wordpress ecosystem was nearly well and truly fucked:
what's stopping someone from breaking in at night into your server room and taking your hard drives?
Besides disk encryption?
Guns. I have lots of guns.
Good luck, I'm behind seven bullet-proof vests.
-
@Lorne-Kates said in The entire Wordpress ecosystem was nearly well and truly fucked:
@Polygeekery said in The entire Wordpress ecosystem was nearly well and truly fucked:
Guns. I have lots of guns.
Good luck, I'm behind seven bullet-proof vests.
But what if he shoots you with eight bullets?
-
@ben_lubar said in The entire Wordpress ecosystem was nearly well and truly fucked:
Locked doors? Those seem to be slightly more effective than guns, especially while you're sleeping.
Tie a gun to a post, aimed at an unlocked door, and wire it to it so that the gun fires when the door is opened. Sleep soundly until the gun wakes you up.
Important safety tip: Keep in mind that you’ve done this when you want to use the door yourself.
Less important tip unless you want to keep your family, friends, and neighbours: Tell them about this security measure.
-
@Gurth said in The entire Wordpress ecosystem was nearly well and truly fucked:
Tie a gun to a post,
Or a grenade. Nothing quite like explosive for ensuring that people don't mess with (what fragments are left of) your stuff.
-