@HardwareGeek said in The Official Funny Stuff Thread™:
I can't remember where I heard this, but it's very good advice: "If your escape plan involves a body of water, you should come up with a new plan."
@HardwareGeek said in The Official Funny Stuff Thread™:
I can't remember where I heard this, but it's very good advice: "If your escape plan involves a body of water, you should come up with a new plan."
@dkf said in Re: The Official Funny Getting Started with Python Thread™:
You have Xcode.
You're standing in a maze of twisty little passages, all alike.
In your hands is the venerable artefact called XCODE, of which many tales had been told, most using curse words many-syllabled and long-forgotten.
Scattered across these caves in a series of SCROLLS, the sacred SPELL OF RELEASE PROCESS is said to be hidden here. Only a being pure of HIG, APPLE TAX, and IN-APP PURCHASES can find them all! Are you up to the task?
Exits are due NORTH, EAST, WEST and SOUTH.
@sockpuppet7 said in Re: The Official Funny Getting Started with Python Thread™:
And that happened with official docs, not even random tutorials
Now that's a serious offence. Even if a typical software license (no matter whether open sores or EULA) screams at you in all caps that THERE IS NO WARRANTY FOR ANYTHING, this is something the actual developers could improve, as opposed to fixing all the random "here's what worked for me once in 2010" tutorials that Google would gladly offer you.
Assuming they want their product to be used, of course. Some people don't, and that's okay too.
@PJH So the problem was in the desktop icons themselves? No wonder we couldn't find anything.
Filed under: Why are desktop icons a third-party extension, again?, Is there a leftpad extension, too?
@jinpa said in Gnumeric formatting problem.:
I want Gnumeric to recognize them as minutes and seconds. However, Gnumeric thinks they're hours and minutes. And so when I change the format to minutes and seconds, Gnumeric thinks that they were already hours and minutes, and so converts that to minutes and seconds.
That sounds infuriating. I think there's no way in Gnumeric to reinterpret the same textual representation according to a different format. I hoped I could trick it by changing the format to text, then to mm:ss, but the first step already transformed 1:23 into 0.0576.
Even if I have the cells already formatted as minutes and seconds, as soon as I put a formula in there, it messes it up somehow and changes the format to hours and minutes (but gets the math wrong) and then when I change the formatting to minutes and seconds, it assumes it's already hours and minutes.
Hmm. This doesn't seem to happen for me in Gnumeric 1.12.32. I was able to set the m:ss format on a range of cells, then enter a formula on a time (also in m:ss format) and a bunch of integers. It seems to give the right answers if I manually redo the same calculation in minutes: times.gnumeric
@boomzilla Okay, sorry for the noise.
One more Hail Mary shot. The question title makes it sound as if it's nothing like your problem, but the answers are all about decoding UTF-8 bytes stored in a TEXT column. In plain SQL, on MS SQL Server.
At least it's consistently botched. right? It's not a mixture of encodings?
@boomzilla said in SQLServer Encoding WTF:
Users sometimes type an apostrophe and it gets stored as that special right single quote garbage, which works fine in the table where it's stored as nvarchar, but when that gets put into one of these XML documents, it ends up as
’.
That seems to be a UTF-8 apostrophe interpreted as CP-1252. You need to encode the text back into CP-1252 and interpret it as UTF-8 in order to make it work:
$ echo ’ | iconv -t cp1252
’
Or is it the question of "how to do it using $toolset", not "what should be done with it"?
@Zenith Do you also hear this in the voice of Tracy Grandstaff every time you read the phrase?
"It'll be stupid, and we're already doing something stupid." - "But this stupid thing will be our idea." This is exactly how several projects started that I'm now part of.
@Zenith How did MTV of all things produce so much good advice?
@boomzilla said in Re: The Quixotic Ideas Thread - Retiring Javascript:
Using the user's local file or what?
I bet it's either completely in RAM or in localStorage, which Stephan has been previously interested in and used in Fossil's wiki editor page and elsewhere.
Edit: they use emscripten's FS.createDataFile, which isn't documented well (or even at all), but seems to end up in RAM, as I see no non-default filesystem initialization.
@topspin Part of the reason for GCC could be the need for a Fortran compiler. Flang exists, but is still experimental and seems to be completely absent from Apple's toolchain. They also don't support OpenMP.
So, ![]() was right, not only there's too much complexity in many modern application stacks, in many ways, the people responsible for the individual parts rarely care about backwards compatibility the way their consumers would prefer them to (cue the people in the comments complaining about Excel-reading packages from Tidyverse), and the number of the moving parts (e.g. packages in a typical dependency tree) is too damn high already and keeps rising. Random tutorials on the internet that only work for the author when they want to do one and only one thing without looking at the big picture don't help, either. At least it wasn't JavaScript, though.
was right, not only there's too much complexity in many modern application stacks, in many ways, the people responsible for the individual parts rarely care about backwards compatibility the way their consumers would prefer them to (cue the people in the comments complaining about Excel-reading packages from Tidyverse), and the number of the moving parts (e.g. packages in a typical dependency tree) is too damn high already and keeps rising. Random tutorials on the internet that only work for the author when they want to do one and only one thing without looking at the big picture don't help, either. At least it wasn't JavaScript, though.
But is it accidental complexity, the kind that can and should be abstracted away until there's one — and preferably only one — obvious way to do it, or is it essential complexity that will never go away because the abstractions are leaky and can't contain the complicated nature of the situations where Python is expected to be working? Perhaps the reason there's more than one way to do it is because they all have their relative merits in different situations?
Visual Basic (also mentioned in the comments) is very well-integrated, but it also doesn't have to run on tens of very different platforms, deployed in strange and sometimes necessary configurations. Interestingly, MATLAB is also well-integrated while also being more cross-platform, and most pieces of MATLAB software I've seen are very self-contained, either not depending on anything else besides MATLAB itself or bundling one or two dependencies in the private directory. Does it mean that you can have either simplicity or package management, but never both?
@Zerosquare said in Required reading for everyone!:
a specific reason for learning Ada
Mostly just curiosity. Have been writing too much R (where the errors are runtime) and seen too much Rust propaganda and decided to see if there's other languages where static type safety is a cornerstone. The previous book may have played a role too.
Also signed up for a microcontroller course where the chips are sufficiently beefy (STM32) for Ada to be useful; maybe I can do the course project in it.
A strange book. On the one hand, its goals are very noble: teach Ada to programming novices. Most people here are probably not the target audience. There aren't many books like this; people usually start with something else and approach Ada after being scarred by C++ with its undefined behaviour and Turing-complete templates or <insert modern language> with its runtime errors that could have been prevented at compile time by a stronger typing system.
On the other hand, the book feels... odd at times. For example, the author is very strict about never using goto (I guess there's less need for it in Ada than in C? e.g. goto cleanup; in fail paths can be replaced by destructors) and almost never importing package namespaces with use, preferring to spell the full name of every outside function and type. Some quotes:
The Current State of Software Development
To put this another way, everyone wants to try the latest Lamborghini. This is an exciting car; who would not want to drive one around town? However, when you actually get into this car, you find that while the clutch is amazing, the steering is flawed and difficult to control or it might have a very powerful engine, but that engine breaks down after driving just a few miles. As a result, while you have a very shiny tool, it is worthless if you want a very reliable and secure program.
Recursion is when a function (or procedure) keeps calling itself over and over until a specific condition has been met to stop it. It is similar to that of a loop.
type Custom_Float is delta 0.001 range -1.0 .. 1.0;
This is the specification for the custom float type.
(Note that numbers with a given delta are fixed-point, not floating point.)
Perhaps the things I didn't like were knowingly oversimplified for the sake of teaching programming novices. Maybe with another editing pass it would have been a better book, especially closer to the end, where instances of code not formatted as such in the middle of paragraphs start showing up. I realised that I sometimes sound like this book when I'm tired and trying to explain too much at the same time to a student.
I liked this book a lot. It has lots of relevant comparisons with other languages ("Packages look similar to, but are semantically very different from, header files in C/C++"; "Ada's variant records are very similar to Sum types in functional languages such as OCaml or Haskell"; "Hashed maps are similar to dictionaries in Python and hashes in Perl.") and teaches the language approximately the same way I learned the other languages. The progression from imperative language constructs to subprograms, modules, type shenanigans, followed by advanced or Ada-specific concepts like tasks, contracts and interoperability with C feels very natural.
In the end, neither book mentions Unicode support, which (at least in gnat) requires some non-default options to the compiler in order to work with anything other than Latin-1. That has to be learned elsewhere.
Banks. Do I really need to say more?
Well, to be precise, let's take this bank. I call their phone number and they tell me to press 2 for infromation in English. Then they tell me to e-mail international@mps.it instead of calling them on the phone. Fine, I do that too. Guess what happens next?
550 5.1.1 RESOLVER.ADR.RecipNotFound
I've got a fairly simple website: a few static pages, one form, one POST endpoint generating some data, some JS to handle and present the response as an interactive plot. It works on Dancer2 reverse-proxied by nginx; additionally, nginx is set up to serve the public/ directory by itself and ask the browsers to cache it:
root /srv/whatever/public;
location / {
try_files $uri @proxy;
expires 1d;
}
Some time ago, I added a new <input> into the form and made appropriate changes to the JavaScript and the server-side parts. Some time later (both much more than one day ago), I added a catch-all error handler to let me know when the client-side JavaScript crashes:
window.addEventListener('error', function(e) { try {
// snip: tell user we fucked up
var req = new XMLHttpRequest();
req.open('POST', '/log_error');
req.send(e.filename + ':' + e.lineno + ':' + e.colno + ': ' + e.message);
} catch (e) {}}, { passive: true });
I was looking through the HTTP logs and saw a user access the website, followed by a bunch of POST /log_error requests. The user never sends the "generate and plot the data" request, which is the sole purpose of the website.
The error is the same in all cases: Cannot set properties of null in an input update handler. The relevant piece of code is doing the equivalent of document.getElementById('a_certain_input').disabled = a_complicated_conditional;. But the <input> is there, and no one complained about it before.
I take a look at the logs again. There's a GET for every CSS and JS file and for every image on the page, but not for the HTML page itself. The user must be running the old version of the page, which doesn't have the <input> yet. Why would the browser (Opera 89.0.4447.71 on 64-bit Windows 10, according to the User-Agent header) download all the dependencies of a page, but not the page itself, when they have the same cache expiration date? How could I have prevented this?
On a related note, what are decent deployment strategies for such websites? For now, it's served straight from a VCS checkout, with a cron job taking care of periodically pulling changes, recompiling the backend executable and restarting the Dancer app if needed. I did this to encourage my colleagues to contribute (they did commit the documentation page updates once or twice) and I'm careful not to serve the VCS files, so it's been working mostly fine. The problem is that it's hard to integrate cache-busting in such a scheme. Additionally, the rare cases when I need to update the dependency of the backend executable and the website itself at the same time are an extreme pain in the ass, since they live in separate repos and have been built separately until now.
@Tsaukpaetra said in Florida Man goes to...:
For a second there I had concerns arm was a euphemism.
- Fishing for carp?
- No, catfish.
- Do they bite well?
- (With a vacant expression) you could say that.
@GuyWhoKilledBear said in Tales from Coronavee-rooss Italy, mamma mia!:
The T3 tests, which were taken about 145 days after vaccination (about 5 months), shows an average of a 16% decrease in sperm concentration and a 20% decrease in motility.
The study has been performed on only 37 people, not all of whom even stuck around for the third sampling, if I'm reading table 1 correctly. Medical data is full of noise, since just about every measurable thing about a human is affected by many factors that the scientists performing an experiment on the person can't control. Here, let me compute a mean of a sample of 37 numbers from a standard normal distribution with a true mean of 0:
> mean(rnorm(37, mean = 0))
[1] -0.4859884
> mean(rnorm(37, mean = 0))
[1] -0.05791935
> mean(rnorm(37, mean = 0))
[1] 0.08271239
> mean(rnorm(37, mean = 0))
[1] 0.04107656
> mean(rnorm(37, mean = 0))
[1] -0.02372143
Look at that -0.486! Surely with an average like this the expectation couldn't have been 0? That's, like, half of the true standard deviation right here!
When a statistical test says that the difference is not significant, it means: it could have increased, or it could have decreased, the data is so noisy we just can't tell. This is what is meant by positive numbers in the 95% confidence interval for everything about the sperm in the T3 group: the true mean could even have increased.
It would have been easier to discuss this study if the researchers published the whole dataset, but we don't have a culture of "share all of the data and code all the time" yet. The IRB could also have a problem with publishing raw sperm counts for privacy reasons.
Surprisingly, "Just use Rust" is not the answer to all of the problems discussed in the book, just to a few of the chapters. 
Was pleasantly surprised that there already were equivalents of sanitizing compilers in 2001, just not as evenly distributed as nowadays. Is there a modern coutnerpart to this book? The kind I could give to a student so that they wouldn't implement website authentication entirely in client-side JavaScript?
@DogsB The Invisible Sun trilogy, especially its first book, was even more catching for me. Felt like a new Halting State book, except with geopolitics instead of hackers.
@martijntje Poor Harald Gormsson would've never guessed why would people be cursing his name centuries after his death.
@DogsB said in In other news today...:
I probably won’t buy anything with software in it.
I would like it to be possible next time we're about to buy a car, but I think it's going to be terribly hard. I haven't been looking close, but every new car I've recently been in has got something smart inside it that probably requires a SIM card and regular software updates.
Well, unless the chip shortage makes it mandatory. Be careful about what you wish for!
@Mason_Wheeler said in PyPad:
How do you lose a phone number?
I got that SIM card when I went to another country for an internship. Before I left the country, I made sure to top it up. I regularly turned it on and checked the balance, but one day, it just decided not to register with the network and never worked again. Last time I checked, they just didn't have offices around here.
@sebastian-galczynski said in PyPad:
That device is usually a SIM card issued by the operator, who should give you a copy after verifying your ID. In theory. Because we already have problems with people getting such a duplicate SIM with a photocopied passport o no ID whatsoever.
My experience here is similar to @topspin's. Tying something to a phone number makes things extremely hard by the time I inevitably lose that number for bullshit reasons. I've been taking care of my phone numbers and I still lost one; thankfully, no accounts I couldn't live without were tied to it. A friend of mine who's not so careful and moved to a different country is currently on number 9 and has lost their WhatsApp and social network accounts at least once.
@loopback0 said in PyPad:
Apps like Authy have the option for backups or sync across multiple devices. Also most services I've got 2FA setup for offer recovery codes.
True, shared TOTP secrets I can at least back up, and PyPI does send two hardware tokens per developer for exactly this purpose. Formally, syncing the TOTP secrets from the phone to the computer makes it less than two-factor auth, but that's okay, I won't argue no true Scotsman here.
this already happens to Google Chrome extensions today so… not like it’s a new as-yet unencountered problem.
Exactly! Not sure about packages becoming malware after legitimately being transferred, but "legitimate developer uploading malware" includes typosquatting, which has already happened on PyPI.
I'd like to see some statistics on this, though. Maybe things like typosquatting are much rarer or have less expected impact than hackers taking over accounts of "critical" developers. I don't know.
Austria, Belgium, Canada, France, Germany, Italy, Japan, Spain, Switzerland, United Kingdom, and the United States
I personally know more developers from outside these countries than ones living in these countries, but I suppose that PyPI have done their homework and chose the places where the developers of the "critical" packages actually live.
The option to use a TOTP app of the developer's choice sounds reasonable too. It's not like Google where you have to link an Android phone or a phone number. One can still be pseudonymous and keep their privacy if they want to.
I wonder what their solution will be to the situation when the malefactors buy or otherwise legitimately take over packages ("would you like me to take this package you're clearly not interested in maintaining? I'll even pay for it...") and then put malware inside it. Or hell, sometimes it's the legitimate developer of the package deciding to put malware inside because this was the plan all along, or because they are fed up with being a maintainer or because they heard something in the news and publishing malware sounded like a good idea.
Another question for me would be account recovery. If you lose the password or the TOTP device, what do you do next? This can make the situation back into a single-factor authentication scenario.
@sebastian-galczynski said in PyPad:
You can't delete a package from Debian because you had a bad day.
True. One could file a bug against ftp.debian.org with scary-looking codewords like ROM; outdated; RC buggy; orphaned, but that only gets it out of the next release.
@dkf said in Is it safe to use __SECRET_INTERNALS_DO_NOT_USE_OR_YOU_WILL_BE_FIRED ?:
C is not a language based around <...> bondage and discipline
But some amount of S&M is definitely present.
@topspin said in Enter the Monorepo:
WhyTF are short names still a thing?!
Say, you want to launch a child process on Windows and pass it a path to a file. CreateProcess only accepts one command line that the child is supposed to parse (and maybe split into char ** argv, maybe do something completely different). The rules are somewhat different depending on the runtime that the child is using. For years, your software has been relying on the short name containing no spaces instead of quoting the path. Enter Windows 10, which sometimes comes installed on volumes with short names disabled. Boom! Now it doesn't work.
@topspin Since you're asking, "I'll revert back to you" instead of "reply" or "get back" is considered here a stereotypical Indian response. You're using it in a different sense, but a combination of "revert" and "back" in close proximity is enough to trigger the pattern detection.
I'm too lazy to actually read TFA. Have they used Microsoft Git Virtual File System or rolled their own?
Because Windows apparently also lives in a Git monorepo, with so many commits per unit of time that pull requests used to be subject to race conditions.
@acrow said in Many eyes make security vulnerabilities shallow:
Hiding in a .so library only until you can infect the kernel, maybe? Intercept the root password if someone types it in, and get the keys to the kingdom that way.
Alternatively, if the kernel module is discovered and removed, but the investigation fails to notice your dynamic library, you could squawk out a warning that the hack has been discovered.
These are all sensible scenarios. I can even imagine situations where LD_PRELOAD is an only option, for example, when the target is a container (which isn't supposed to load modules, right?) and you don't want to compromise the host machine, or when the kernel has module support disabled or refuses to load them for some other reason.
I should be arguing against the presentation of the backdoor as undetectable, not the technique itself.
@acrow said in Many eyes make security vulnerabilities shallow:
It would still be possible to hide in the filesystem by installing a kernel module to hide the files.
I agree, but once you have a kernel module in the system, why bother using a less stealthy technique? DeOffence in depth?
@Gribnit I think that the mechanic has checked that. @acrow's guess of an air bubble seems most likely for now, given how the problem seemed to solve itself and never reappeared despite multiple traffic jams we had to sit through since. But @Carnage may still be right and we may end up replacing the other cylinder, too.
I know it's much easier to justify post-factum than to actually detect such infection in practice, but when I was given a backdoored machine as a demonstration, it had an actual kernel module as a rootkit, not a shared object to $LD_PRELOAD. We had to take apart a filesystem image of the machine in order to find where it was hiding.
Any statically linked binary would defeat $LD_PRELOAD. Running a binary with a wrong architecture (i686/amd64) would even be noisy about it. (ERROR: ld.so: object 'rootkit.so' from LD_PRELOAD cannot be preloaded: ignored.)
Gentoo's sandbox comes with an $LD_PRELOAD library to guard well-behaving applications from modifying parts of the filesystem they are not supposed to touch. They handle statically linked binaries by means of ptrace (i.e. acting as a debugger), but a dynamically linked binary could thwart it by performing a syscall instruction manually.
@dkf said in In other news today...:
FWIW, I have read the SQLite source and wouldn't want to contribute.
The one time I wanted to contribute to Fossil, it was one of the first highlights of the Era of COVID, luxuries like air mail weren't readily available, and my CLA got stuck for a few months waiting for a mail flight. Good times.
The style does feel rather dense to me, too, both visually and in terms of information. (Tab stops at two spaces? That's a lot of indentation levels to cram in one line.) Feels like it might take me 100% of my smarts to write code like this, which doesn't leave any spare smarts for debugging.
@topspin said in In other news today...:
Even with their clarification that you're not expected to follow "The Code", I'm not sure if they actually think that's a code you should try to
livedevelop by
I can't be sure, of course, but it's not unlikely that this is the code that D. Richard Hipp follows for himself and it all was just a giant misunderstanding on his part. SQLite makes a big point about being developed cathedral-style, with rare outside contributions being rewritten from scratch, so the code (he thought) was really just for him and a few colleagues.
Interesting how going from forum rules to code of conduct changes the attitude towards the object in question. It must be in the connotations.
@acrow said in In other news today...:
philosophy is bad grounds for building your life on. Moral codes work better.
I don't think I agree in general (I could waste everyone's time trying to present an adversarial example here, or nit-picking on what exactly can be "good" grounds for a life, measures of "success" and so on), but it's probably true that if you already have a well-tested but still relevant moral code and a society that mostly follows, it will probably serve you well.
How do you develop such a code, that's an entirely different question. Your point is probably that any attempts at taking shortcuts here lead to philosophical navel-gazing and reductio ad absurdum, you have to let it evolve. Utilitarian position as I see it is making it into a calculus problem: everyone's needs is a function f(parameters), now optimise parameters until everything is Pareto optimal. Which probably could work well, but you have to somehow work around the fact that people's f's themselves can be changed by means of Facebook targeted ads and special chemicals in the water supply. It's probably best not to take extreme positions.
This thread needs more utilitarian ethics, trolley problems and prisoner's dilemmas to test them on.
Seriously, deriving ethics ab initio is really hard.
@Carnage Thanks for the reply!
@Zecc Oh no! How do I reset the firewall settings?
@izzion At least all my files are actually where I left them 
Status: confused. We all like car analogies[citation needed], so here's a car story that needs to be explained with computer analogies instead.
A 10-year-old Citroen starts misbehaving in traffic jams. The longer the jam, the worse it gets: first, the clutch gets squeaky; later, it gets hard to engage the first gear. One time the clutch pedal somehow got stuck in the middle position. Thankfully, it was possible to manually pull it up and succeed to get this thing moving on the next try without annoying our fellow jam-sitters too much.
It was annual service time anyway. The mechanic tells us it may be the dust cap of the clutch cylinder, since there's evidence of brake fluid slowly leaking from it, we okay the replacement and drive the car home without any problems. Maybe the clutch feels a bit softer than usual?
A few days later, it's my relative's turn to drive. He presses the clutch pedal (feels really soft now), starts the engine and finds out that the pedal does nothing; the car's in gear no matter what he does. He brakes and stalls and decides to try again. Somehow avoiding damage to either the car or the curb, after a few tries, he realises that the clutch is now working as it's supposed to be, and it hasn't misbehaved since.
 is going on?
is going on?
NFC. Image sharpening?
I feel like there's some joke to be made about blurry clowns, creepy low-resolution houses and whatever their method reconstructs in the figure 6 instead of peppers, but it currently escapes me.
Well, yes, sharpening and other reconstruction of the image after it has been run through a transformation that can be expressed as a matrix product. The  part is that the matrix doesn't have an inverse, making the problem ill-posed.
part is that the matrix doesn't have an inverse, making the problem ill-posed.
Exercise: suggest appropriate captions for the following completely normal, not creepy at all figures and try to guess what happened between them without peeking at the original preprint.

Figure 1.

Figure 3.
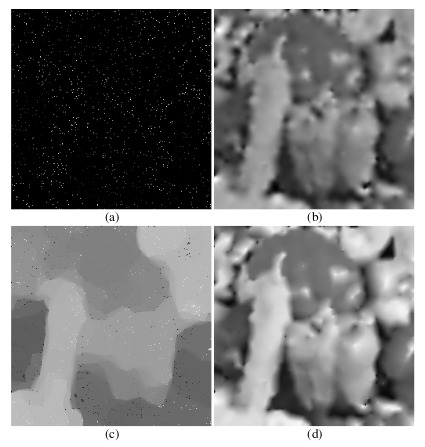
Figure 6. 
I know I'm late to the party, but this sounds like an overzealous firewall that blocks the ICMP messages required to discover a safe MTU value for a TCP connection.
A workaround for that is called MSS clamping, which sets maximum packet size for a connection based on a value from the TCP header, not using ICMP in the process. There's a lot of HOWTOs on the Internet if you search for --clamp-mss-to-pmtu.
@DogsB said in In other news today...:
I think I broke @Gribnit. That was actually lucid and on point.
Some time ago, I was re-reading certain books (by David Foster Wallace, Joseph Heller and/or Kurt Vonnegut). For a short period of time, not only @Gribnit's posts made sense, the references almost coincided with my progress through the books as I read them, doubtlessly looking completely nonsensical to someone not acquainted with the material.
@Zecc I'm used to GIMP too, and it's definitely overkill here. We'll try Paint.NET, thanks. Although...
Okay, we'll still try it.
Does anyone know a photo editing application with functionality close to that of PowerPoint 2010 image enhancement features? Not less and not much more.
My relative prepares figures for a textbook by pasting them in PowerPoint, cropping/changing contrast/whatever, then saving the result as a new image. This... mostly works, but occasionally, PowerPoint manages to destroy the aspect ratio of the image. Which application would be easier to adapt to after PowerPoint? IrfanView is not the answer, apparently, or at least needs further training.
For a few months, GMail has been warning anyone still using a classic e-mail client without OAuth support that they will be shutting down the "insecure" log-in option, because, apparently, my e-mail client can be easily phished into giving away my account password or something. I'm left with the option of upgrading to something that supports OAuth (which, for e-mail, is so under-specified that one has to hard-code additional per-provider information in order to get it to work, not to mention that Google keeps inflicting breaking updates in the name of security, too) or enabling 2FA on my account in order to use app passwords.
That latter option sounds easy as pie, right? Just plop a secret code into a TOTP generator app and be done with it? Ha-ha, no, this is Google we're talking about. My options are tying it to my phone number (and phone companies never lock people out of their phone numbers, or sell their location data, or tie the phone number to their government ID), adding a smartphone (while smartphones never break or get stolen; also, my smartphone is older than some people currently going to school and I'm not buying a new one on my current income) or using a hardware cryptographic token that I'll subsequently have to lug around with me all the time like some kind of Gollum (do they come in ring variety?), because that's a thing that everyone has, or can buy for pocket money at their favourite corner store.
Once I've done that, then I can plop a secret key into a TOTP generator app, but the primary second factor is likely to stay there. That would be making my account hell of a lot easier to get locked out of for almost no added security (I can still be phished unless I go with the hardware token that authenticates the web site at the same time as the website authenticates me, or so I'm told).
Oh, and that OAuth thingy? Someone has to create a client ID for your e-mail client, and if the client's developers don't want to bother (and I really can't blame them), it's up to you, in just, er, a few easy steps! And it can always be revoked by a bot for no particular reason, just like your YouTube videos or Android apps! It's almost as if they wanted to make it as hard as possible to use anything but approved™ e-mail clients! (Or a browser, preferably, Chrome.)
Sadly, a lot of GMail alternatives can be just as bad. Not even paid options can guarantee you that you won't get locked out because $BOFH_excuse_of_the_day, with the added nagging feeling that you are a few missed payments away from being denied your online identity. And those usually happen at the worst possible time, e.g. when you're in the middle of switching countries. About the only thing I can trust to keep working is my alumnus e-mail, but (1) it's too close to my real-world identity and (2) it won't ever keep up with the mail volume or the spam load. Also, with my university self-hosting it, I always suspect it of losing messages.
There ain't no such thing as a free lunch, of course, but even paid lunch tastes terrible. One could think that we should be moving towards decentralised identity, but those are always troubled by spam & Sybil attacks and, as cryptocurrencies have shown us, always centralise in the end. Time to take one step closer to enlightenment and learn to live with temporary, disposable online identities?