WTF Bites
-
@DCoder Worse, Clang also defines
__GNUC__/__GNUC_MINOR__and so on. You always need to check for Clang first. (Perhaps matters less now since the version Clang claims to be compatible with is 4.2.1, and actual GCC is in 8.x. GCC 4.9 is about the lowest version that I consider usable.)
-
@DCoder I've hit this about two years ago. And it gets worse, because the clang on apple has completely different versioning from clang anywhere else. There ain't clang 9.0.0 yet!
-
@DCoder I've hit this about two years ago. And it gets worse, because the clang on apple has complete different versioning from clang anywhere else. There ain't clang 9.0.0 yet!
And it's not even particularly easy to google what features "clang .
 .
. " actually supports.
" actually supports.
-
@topspin The C++11+ features are mostly detectable with specific
#defines, fortunately. But of course there may be bugs and for somewhat obvious reasons those tend not to have their own defines.
-
And it's not even particularly easy to google what features "clang .." actually supports.
I would say that all versions of .
 are deprecated now, though. They even moved on from .
are deprecated now, though. They even moved on from . to something new, so we're now on .
to something new, so we're now on . (sadly, because I liked the kitty names).
(sadly, because I liked the kitty names).
-
"One pump: one cream"
"Not to brag, but I'm a "two pumps = one cream" man myself."
"1 pump 1 (hazel) nut"
-
GCC 4.9 is about the lowest version that I consider usable.

$ g++ --version g++ (GCC) 4.4.7 20120313 (Red Hat 4.4.7-18)
-
@boomzilla Linux hipster.
-
@loopback0 said in WTF Bites:
@boomzilla Linux
hipsterenterprise developer.
-
@boomzilla said in WTF Bites:
GCC 4.9 is about the lowest version that I consider usable.

$ g++ --version g++ (GCC) 4.4.7 20120313 (Red Hat 4.4.7-18)Ugh.
I'm supporting gcc 4.8.5 because that at least has C++11 and there's a backport for it in the RedHat 6 developer toolset (and cursing my customers who run bullshit like RHEL 6 or SLES 11 from a decade ago). Maybe there's newer versions backported, but I haven't checked since.
-
RHEL 6
Yup. I know you C++ snobs wouldn't touch it, but it's not that bad, really.
-
@boomzilla On our build env, we still need to explicitly indicate on every run that we don't want the default RHEL5 build servers.
-
@boomzilla said in WTF Bites:
Yup. I know you C++ snobs wouldn't touch it, but it's not that bad, really.
Allegedly.
(4.9 is the minimum for two good reasons: it's where they got C11 support working, and it's where they got colorized output working.)
-
@boomzilla said in WTF Bites:
GCC 4.9 is about the lowest version that I consider usable.

$ g++ --version g++ (GCC) 4.4.7 20120313 (Red Hat 4.4.7-18)Upgrade your browser.
-
@boomzilla said in WTF Bites:
Yup. I know you C++ snobs wouldn't touch it, but it's not that bad, really.
Hello, Stockholm.

-
There's a page on Facebook about driving in my city that posts advisories about things like upcoming roadworks and detours and stuff. I made a post in the community section. Then I realized something else that I wanted to edit in, so I went back to do that.
The second I even hover over the "..." icon that presumably hides the Edit button I get a popup saying NO FUCK YOU YOU CAN'T DO THAT. When I dismiss it I can actually click the button, but the menu just shows a loading icon, presumably forever. I can't do anything with my post once I send it except comment on it, and the UX on that is exactly what I'd expect from a multi-billion Silicon Valley company. Sigh.
-
I was reading a story when I double clicked a word to remember my spot before getting up, and by pure chance I stumbled upon a pixel-perfect bug that I have replicated on video:
https://what.thedailywtf.com/assets/uploads/files/1552703407572-selection.mp4
-
My professor, to another student, right now:
No wonder it doesn't work. The permission file is encoded with UTF-8, when it should be ANSI.
(Note: the file only used ASCII characters.)
-
@Gąska BOM?
-
@Zecc no. Idiot professor.
-
My professor, to another student, right now:
No wonder it doesn't work. The permission file is encoded with UTF-8, when it should be ANSI.
(Note: the file only used ASCII characters.)
That's astounding...
-
A curious question about Linux and emoji appears:
Are you allowed to put emoji in Linux network device names? Asking for a friend.
… gets answered by the OP themselves:
Yes!
root@lodestar:~# ip link add name eth✨ type veth peer name eth🎉 root@lodestar:~# ip link show dev eth✨ 10: eth✨@eth🎉: <BROADCAST,MULTICAST> mtu 1500 qdisc noop state DOWN mode DEFAULT group default qlen 1000 link/ether c6:6a:14:3d:ad:45 brd ff:ff:ff:ff:ff:ffSource: @geofft
… And explained by the person responsible:
Sit back, and hear a story about how you can name an ethernet device ✨🌈✨🌈, but not holà, and it's ALL MY FAULT.
Way back in the day I maintained the initscripts package for Red Hat.
It did network device renaming (poorly. in shell. I'm sorry) for persistent device names.When testing it, I, being me, would of course use silly names. One day I decided to name a device "foo bar".
All sorts of random tools parsing things like /proc/net/dev promptly broke.I sent a patch somewhere for one of them. [David S. Miller] saw it, and more or less said, "nah, screw that."
All fine and dandy, right? You can name your device anything you want, as long as it doesn't have a space, right?
But wait...... the kernel, being the kernel, is not a normal C program. It doesn't use your normal ctypes from libc. It has to have its own.
And so the kernel literally has its own table, from 0-255, saying which bytes are spaces.
Since it's checking those fancy multi-byte characters at a byte by byte level... well, you can have eth🦖🦖, but not dejàvu. Or Poof, but not Рoof.†
Sorry about that.Source: @bill_nottingham
† that's not a regular Poof, it's a "U+0420 CYRILLIC CAPITAL LETTER ER". The second byte in its UTF-8 representation is 0xA0, or "non-breaking white space".
$ echo -n 'Рoof' | xxd 00000000: d0a0 6f6f 66 ..oof
-
(Non-IT related) WTF of my day: So, I had signed up to one of those speed dating thingies. Setting was supposed to be 7 on 7 with a maximum age of 42.
I was jokingly stating to one of my friends that this was a good thing because the women are not allowed to run away and with only 7 minutes for each encounter it would be over soon. And that I'd also keep my expectations low.
Yeah.
Seems that I have to set my expectations even lower.

So, I arrived at the location (which looked really sketchy from the outside at first glance) to find myself with 4 other male compatriots and 5 women at the time this event was supposed to begin. Okay, only 5 on 5. But not a big deal, right?
Well, you remember how I joked that the women were not allowed to run away? Well, ten minutes later all the women had left because of, and I quote, "only five guys".
Though, to be honest, it might also have been my fellow guys. Now, I would rate myself as at least average looking (it's a bit difficult to get an objective opinion on that), I do know how to dress for such an occasion, don't have a dad bod and also don't have any weird metal in my face or something. One other fellow was able to match that.
The other three: One was a bit on the heavy side and also had those flesh-tunnel ear insets, another looked about 55 (remember the maximum age?) and the last one looked more like someone you'd see in a redlight district.Good grief.
-
Signing up for a particular scholarship.
Is it really that hard to write portable code for a high level virtual machine that hides hardware quirks and low-level details like memory allocation behind layers and layers of abstractions?
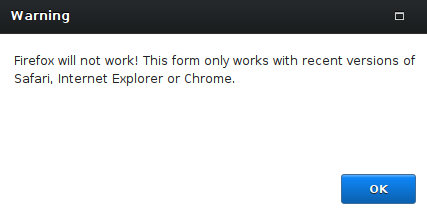
Of course it is.
-
scholarship.
Banking, schools, and government. Nowhere else can you find this level of silliness.
-
@pie_flavor said in WTF Bites:
scholarship.
Banking, schools, and government. Nowhere else can you find this level of silliness.
Don't forget the vast array of internal web applications in any company that still requires IE6.
-
@pie_flavor said in WTF Bites:
scholarship.
Banking, schools, and government. Nowhere else can you find this level of silliness.
Don't forget the vast array of internal web applications in any company that still requires IE6.
I actually wonder how many of those are still in the wild.
-
@Lorne-Kates Too many, whatever the number.
-
@Lorne-Kates said in WTF Bites:
@pie_flavor said in WTF Bites:
scholarship.
Banking, schools, and government. Nowhere else can you find this level of silliness.
Don't forget the vast array of internal web applications in any company that still requires IE6.
I actually wonder how many of those are still in the wild.
I know of three at three different places.
-
When doing a
yum updateon a server with PHP 7.2 and MSSQL drivers installed, it stops and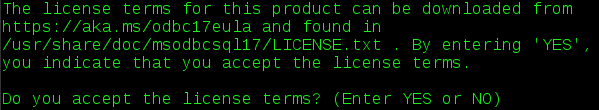
I already accepted the license when I installed it, so fuck off

Also, this will interact nicely with update automation tools
-
@TimeBandit maybe they've altered the license?
-
@Gąska
yum updateis not the right place to make me accept it.Here, we usually do updates using Ansible, which will just freeze at that license prompt.
-
@TimeBandit said in WTF Bites:
@Gąska
yum updateis not the right place to make me accept it.There really isn't any right place to do it. There's only two options - periodically break people's CIs with license prompts, or don't collect explicit consents and expose yourself to lawsuits.
-
expose yourself to lawsuits
The original license already state that it's impossible
DISCLAIMER OF WARRANTY. THE SOFTWARE IS LICENSED “AS-IS.” YOU BEAR THE RISK OF USING IT. MICROSOFT GIVES NO EXPRESS WARRANTIES, GUARANTEES OR CONDITIONS.
The other option is to make it GPL or BSD and don't fuck automation tools

-
@TimeBandit maybe they've altered the license?
Pray they don’t alter it any further.
-
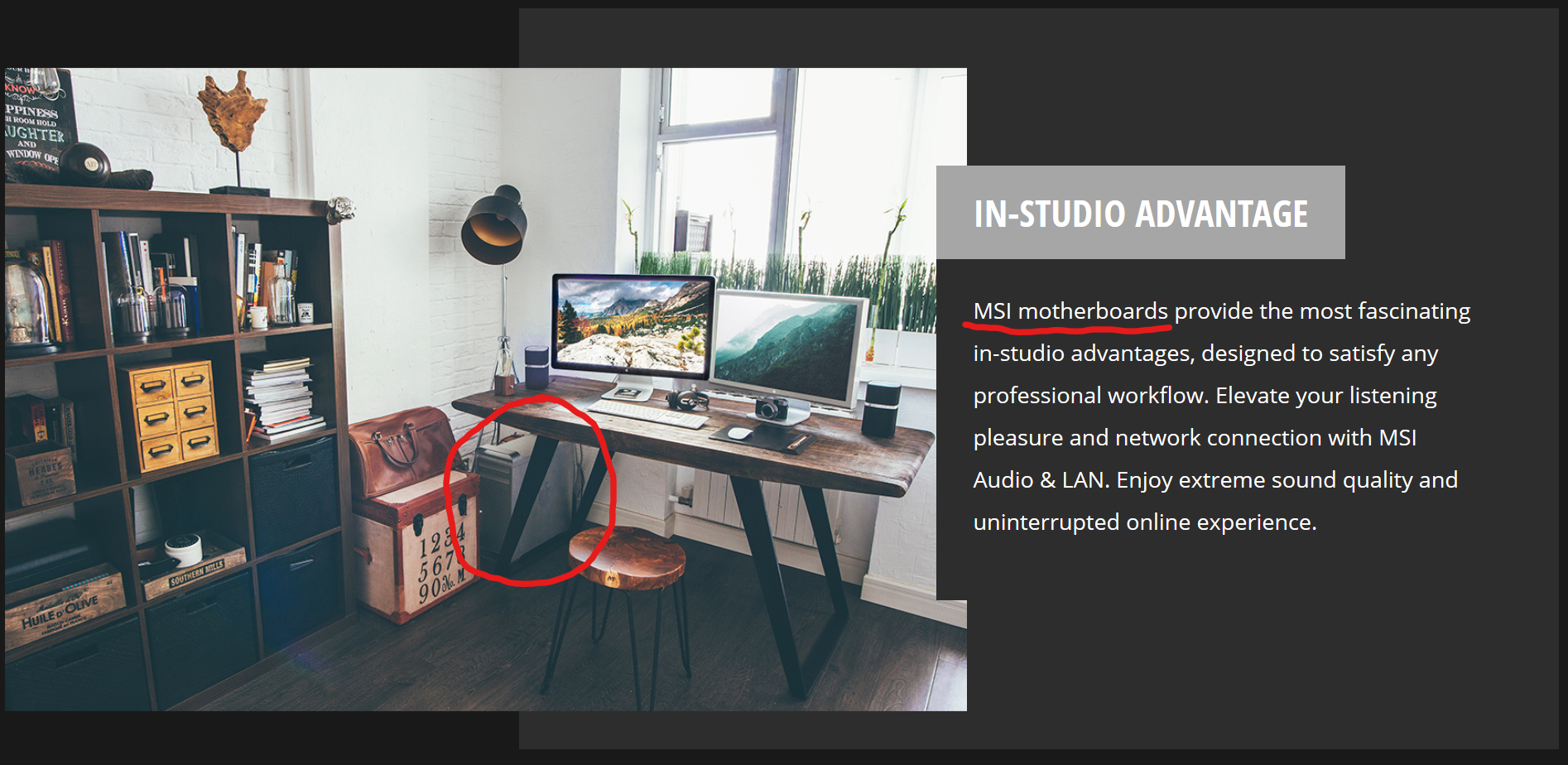
MSI choose to advertise their high-end motherboards with a picture of a studio with what's definitely not an MSI computer. Or even a recent computer.
-
@TimeBandit said in WTF Bites:
this will interact nicely with update automation tools
There are decent tools for automating interactive sessions. (GUI automation is a dumpster fire though; too many variables…)
-
I was reading a story when I double clicked a word to remember my spot before getting up, and by pure chance I stumbled upon a pixel-perfect bug that I have replicated on video:
https://what.thedailywtf.com/assets/uploads/files/1552703407572-selection.mp4
That's quite a bug...
-
Input #0, mov,mp4,m4a,3gp,3g2,mj2, from 'https://what.thedailywtf.com/assets/uploads/files/1552703407572-selection.mp4': Metadata: major_brand : isom minor_version : 512 compatible_brands: isomiso2avc1mp41 encoder : Lavf58.26.100 Duration: 00:00:15.76, start: 0.000000, bitrate: 157 kb/s Stream #0:0(und): Video: h264 (High 4:4:4 Predictive) (avc1 / 0x31637661), yuv420p, 1280x720, 156 kb/s, 25 fps, 25 tbr, 12800 tbn, 50 tbc (default) Metadata: handler_name : VideoHandlerHow about a webm that's twice as large instead?
https://what.thedailywtf.com/assets/uploads/files/1552952516147-selection.webm
-
MSI choose to advertise their high-end motherboards with a picture of a studio with what's definitely not an MSI computer. Or even a recent computer.
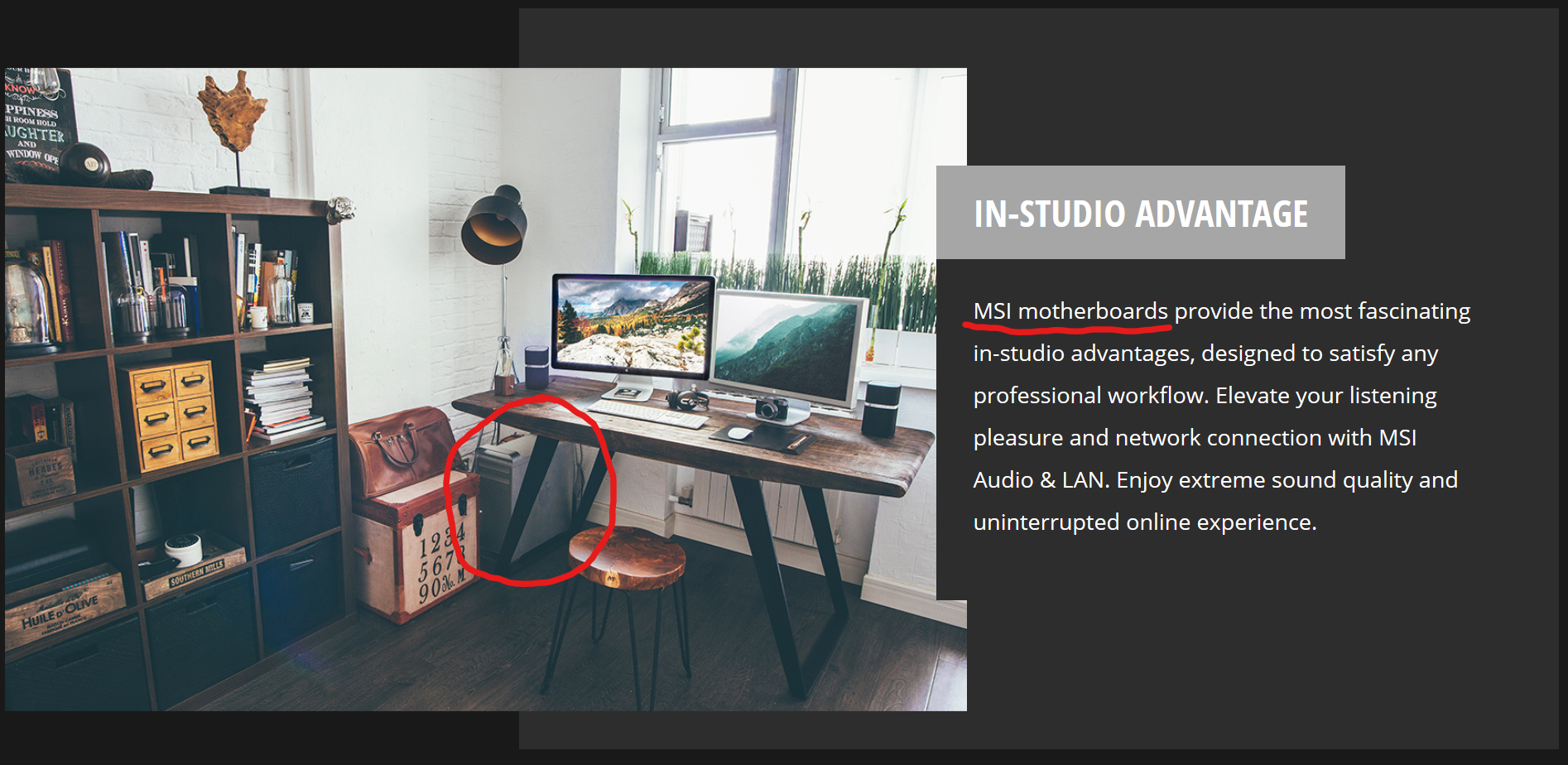
It's possible to modify a PowerMac case to fit a standard ATX motherboard, presumably that's possible on a Mac Pro too.
However ain't no-one using Windows/Linux hardware also using a Mac keyboard.
-
@loopback0 said in WTF Bites:
MSI choose to advertise their high-end motherboards with a picture of a studio with what's definitely not an MSI computer. Or even a recent computer.
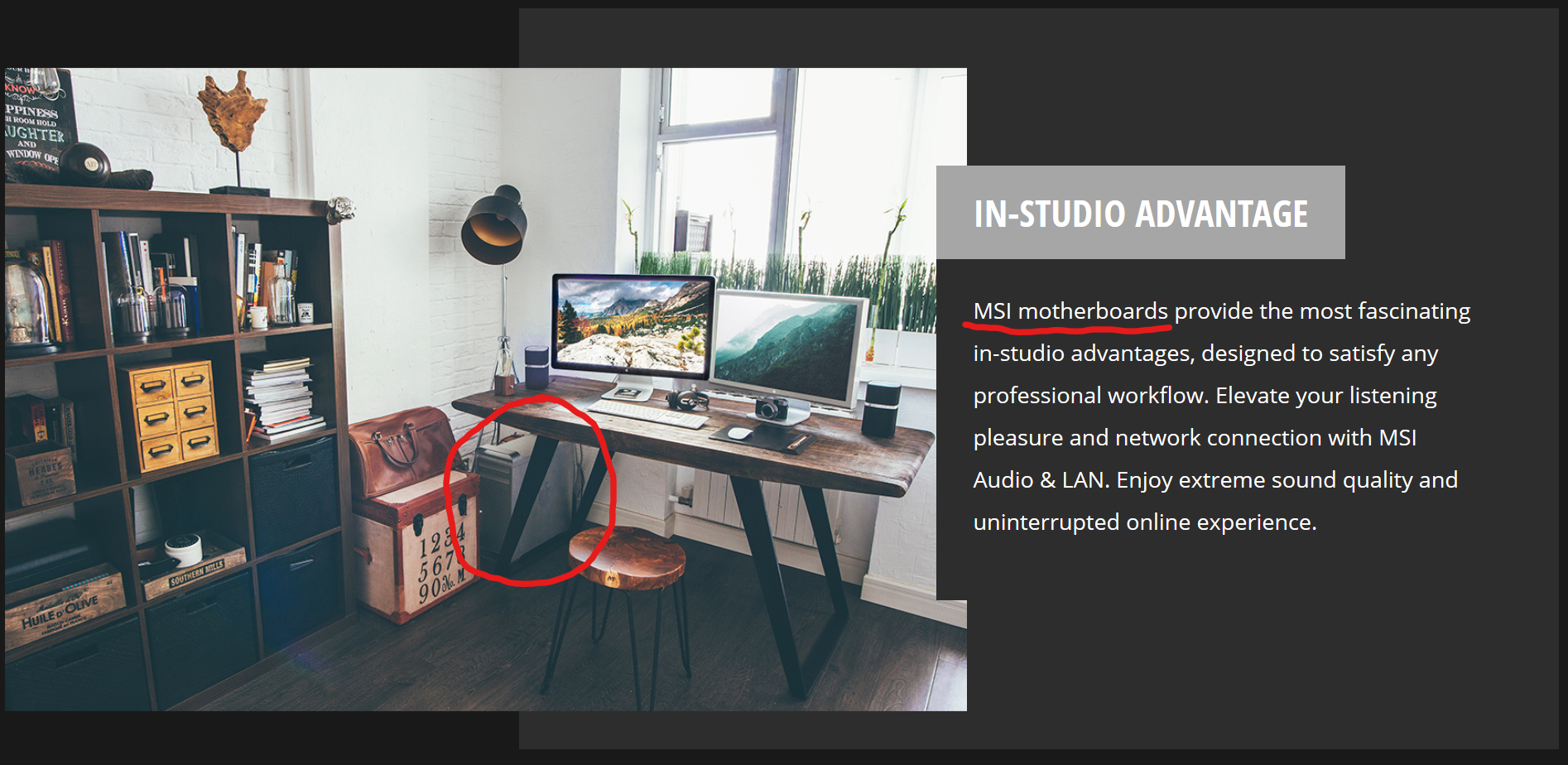
It's possible to modify a PowerMac case to fit a standard ATX motherboard, presumably that's possible on a Mac Pro too.
However ain't no-one using Windows/Linux hardware also using a Mac keyboard.
I have a friend who does use Apple like keyboards for everything because he likes them.
-
@TimeBandit said in WTF Bites:
@Gąska
yum updateis not the right place to make me accept it.There really isn't any right place to do it. There's only two options - periodically break people's CIs with license prompts, or don't collect explicit consents and expose yourself to lawsuits.
@TimeBandit said in WTF Bites:
@Gąska
yum updateis not the right place to make me accept it.Here, we usually do updates using Ansible, which will just freeze at that license prompt.
If done reasonably, there is a variable that you can set in advance to automatically approve it, so whoever writes the script/ansible playbook/whatever to install it on the server bakes the consent in it. We've recently done it that way for Oracle Java in a Yocto-based build—though I think in that case it does not even ask and just fails unless you've set the variable, because everybody expects the build to run automatically.
-
-
My WTF of the day. In my large corporate we have among many services, one single Java service that could be called "critical" to the business.
Our core business is selling streaming video. This service is the one that does that.
I discovered yesterday that I can crash it with just 3 concurrent requests to a specific URL - albeit, unused, but it is exposed. The only good thing here is that it is internal, so a DDOS would have to be specifically crafted to make use of the bug. The bad news is that my 3 year old child could do the DDOS by mashing the keyboard.
-
Spotify sent me an email: we detected unusual activity on your account. We won't say what it was, so fuck you if you thought you might be able to determine if your password got compromised. It just was unusual. Trust us. We're trustworthy, right? Anyway, so we reset your password. I mean, we did reset your password, but here is a huge green button that you can click to reset your password. Cause you know that resetting means resetting means invalidating, right? Yeah. Words don't have meaning, just ask @Gąska. Ah, right, so back to your password. Did you click the link? And? What? You're bewildered cause the link is no longer valid? Hey, we said we reset your password so you could reset your password, no one said that you could actually reset your password. Anyway, here, just input your email and we'll send you a new link that will reset your password for sure.
We hope you had fun with our completely unambiguous security procedures. Hope you'll use our service again and recommend it to your friends.
I got that email a while back. It ticked every red flag for "check this isn't a phishing mail": no username, just "hi Spotify user", direct link in the email, saying it might have been to do with a leak from another service where I use the same password which hints at plaintext password storage. I contacted their Twitter support who completely failed to understand my reservations
-
@scudsucker said in WTF Bites:
The bad news is that my 3 year old child could do the DDOS by mashing the keyboard.
Sounds like you've written the DDOS attack are and waiting for someone else to press Enter.
-
@Zecc It appears some dev back in 2013 wrote the DDOS vector. I am apparently just the first to try to load test it.
"Load" test. FFS, I started with 1500 concurrent requests, as that is roughly double what I'd expect at maximum load. Then I tried 1000. Then 500. Then 200.... etc etc until eventually 5, 4, 3... until I could prove that 2 concurrent requests works, but 3 does not.
-
Spotify sent me an email: we detected unusual activity on your account. We won't say what it was, so fuck you if you thought you might be able to determine if your password got compromised. It just was unusual. Trust us. We're trustworthy, right? Anyway, so we reset your password. I mean, we did reset your password, but here is a huge green button that you can click to reset your password. Cause you know that resetting means resetting means invalidating, right? Yeah. Words don't have meaning, just ask @Gąska. Ah, right, so back to your password. Did you click the link? And? What? You're bewildered cause the link is no longer valid? Hey, we said we reset your password so you could reset your password, no one said that you could actually reset your password. Anyway, here, just input your email and we'll send you a new link that will reset your password for sure.
We hope you had fun with our completely unambiguous security procedures. Hope you'll use our service again and recommend it to your friends.
I got that email a while back. It ticked every red flag for "check this isn't a phishing mail": no username, just "hi Spotify user", direct link in the email, saying it might have been to do with a leak from another service where I use the same password which hints at plaintext password storage. I contacted their Twitter support who completely failed to understand my reservations
Umm... that's fucked up. In my case at least it contained my username and all.
-
@scudsucker said in WTF Bites:
@Zecc It appears some dev back in 2013 wrote the DDOS vector. I am apparently just the first to try to load test it.
"Load" test. FFS, I started with 1500 concurrent requests, as that is roughly double what I'd expect at maximum load. Then I tried 1000. Then 500. Then 200.... etc etc until eventually 5, 4, 3... until I could prove that 2 concurrent requests works, but 3 does not.
Who would ever need to send more than 2 simultaneous requests?
-
Ugh.
I'm supporting gcc 4.8.5 because that at least has C++11 and there's a backport for it in the RedHat 6 developer toolset (and cursing my customers who run bullshit like RHEL 6 or SLES 11 from a decade ago). Maybe there's newer versions backported, but I haven't checked since.I got these feels too, bro.
$ g++ --version g++ (GCC) 4.8.5 20150623 (Red Hat 4.8.5-36)We also have a custom build system called Buildme (it's a meta-build system, because it generates GNU Makefiles) and all our "helper build scripts" use the C Shell, which is also the default shell used everywhere. We also use SVN for version control.
Life feels great.

