WTF Bites
-
-
Steps to reproduce the problem
- create a user with an UID > INT_MAX, e.g. 4000000000
- run any systemctl command


 , the issue turns out to be in another component, not systemd.
, the issue turns out to be in another component, not systemd.Oh look, it's systemd bug #INT_MAX
Filed under: "create user" is on the other side of the airtight hatchway, though
-
Steps to reproduce the problem
- create a user with an UID > INT_MAX, e.g. 4000000000
- run any systemctl command


 , the issue turns out to be in another component, not systemd.
, the issue turns out to be in another component, not systemd.When you can create users at will on a system, you probably really already have sufficient access to do some serious harm anyway.
-
@Carnage the problem isn't you having access - the problem is that user you created but haven't given any privileges having access.
-
I updated my Radeon drivers and the keyboard stopped working entirely. Caps lock and num lock not toggling the lights.
So I rebooted the system. It started working again while it was shutting down.
-
@Carnage the problem isn't you having access - the problem is that user you created but haven't given any privileges having access.
Yes, but you have to sort of go out of the normal flow to actually make the problem appear.
-
@Carnage Isn't that how most defects are detected?
-
@Carnage the problem isn't you having access - the problem is that user you created but haven't given any privileges having access.
Yes, but you have to sort of go out of the normal flow to actually make the problem appear.
Yes - by using a UID above INT_MAX. You could argue this is highly abnormal. But the entire rest of the procedure is identical to regular user creation. Unless you consider user creation itself to be out of the normal flow?
-
@sweaty_gammon yes, but setting userids above max_int seems like it would not be a normal fumble, but someone up to no good.
It needs to be fixed, absolutely, but you still have the original problem of someone with hightened system access doing shady shit.
-
@sweaty_gammon yes, but setting userids above max_int seems like it would not be a normal fumble, but someone up to no good.
It needs to be fixed, absolutely, but you still have the original problem of someone with hightened system access doing shady shit.I was being a little facetious.
-
@Gąska The bug needs to be fixed. Something is seriously broken. But fixing this bug will not fix the problem with someone having system access that is up to no good.
-
@Carnage fixing this particular bug will absolutely fix the problem of someone having system access that is up to no good. This someone isn't the account creator, but account user. The user had access they weren't supposed to. After fix, they won't. Account creation isn't the problem here at all.
-
@Gąska yes it is, in that you have to get the userid above max_int to make this happen, and if I'm not mistaken that means you have to subvert the tooling for creating users. Someone needs to specifically make this happen. It's not prone to happening on accident.
It is a bug, and a severe one since the access control system completely falls on its face. But if you have someone with access enough to subvert the tooling for user creation, fixing this bug will just be a small hurdle for them.
-
@sweaty_gammon yes, but setting userids above max_int seems like it would not be a normal fumble, but someone up to no good.
It needs to be fixed, absolutely, but you still have the original problem of someone with hightened system access doing shady shit.So... the UID is, for some reason, represented by a signed integer, and for no really obvious reason, they're restricting it to the non-negative integers. If a UID is created that is larger than MAX_INT, it's interpreted as a negative integer, and when it's interpreted as a negative integer, the assertion fails (it's checking for >= 0). And if the assertion fails, the code bombs out and the user gets admin by default.
There are WTFs upon WTFs there...
- an unsigned ID is stored as a signed integer (why?)
- okay, but negative integers aren't allowed (why not?! what's wrong with them?)
- if the user's ID is invalid, the default should be no privileges, not admin!
-
@Carnage Imagine, if you will, a hosting company for Wordpress. Let's call this company ComeMommy. ComeMommy creates a couple of new users for each person that attempts sign up - Apache, FTP, shell, special-sauce-maintenance-script - so that they can use the normal Linux permissions system. (Yes, there are better ways to do this, but the Wordpress team at ComeMommy are a bunch of knuckle-dragging mouthbreathers that can just about handle scripting Bash.) Imagine that this system is in the wild, exposed to
unceasing attacks fromthe tender, loving caress of the Internet for the better part of a decade. Even if there's only one sign-up every second, that's still over 315 million signups. Add in some silly rule like "each group of UIDs must start with a multiple of 10", and you're seeing UIDs in the 3.15 billion range.It's not prone to happen by accident on well-maintained systems serving actual users. But it's easy for plucky young coders multiplied by time in neglect to cause something to happen by accident.
(My company used ComeMommy's services for a while.)
-
@anotherusername said in WTF Bites:
@sweaty_gammon yes, but setting userids above max_int seems like it would not be a normal fumble, but someone up to no good.
It needs to be fixed, absolutely, but you still have the original problem of someone with hightened system access doing shady shit.So... the UID is, for some reason, represented by a signed integer, and for no really obvious reason, they're restricting it to the non-negative integers. If a UID is created that is larger than MAX_INT, it's interpreted as a negative integer, and when it's interpreted as a negative integer, the assertion fails (it's checking for >= 0). And if the assertion fails, the code bombs out and the user gets admin by default.
There are WTFs upon WTFs there...
- an unsigned ID is stored as a signed integer (why?)
- okay, but negative integers aren't allowed (why not?! what's wrong with them?)
- if the user's ID is invalid, the default should be no privileges, not admin!
Why yes, this is a really severe bug. But I'd guess we're gonna keep seeing these kinds of bugs until languages, compilers, runtimes and operating systems just flat out refuse wrapping integers.
They are kindof expected, and will keep happening since there are junior devs, and shitty senior devs. The really wonderful thing is how the priviledge management system defaults to "Oh, I guess admin it is then!"
That is an utter failure of doing the one fucking thing it's supposed to be doing.
-
@TwelveBaud said in WTF Bites:
@Carnage Imagine, if you will, a hosting company for Wordpress. Let's call this company ComeMommy. ComeMommy creates a couple of new users for each person that attempts sign up - Apache, FTP, shell, special-sauce-maintenance-script - so that they can use the normal Linux permissions system. (Yes, there are better ways to do this, but the Wordpress team at ComeMommy are a bunch of knuckle-dragging mouthbreathers that can just about handle scripting Bash.) Imagine that this system is in the wild, exposed to
unceasing attacks fromthe tender, loving caress of the Internet for the better part of a decade. Even if there's only one sign-up every second, that's still over 315 million signups. Add in some silly rule like "each group of UIDs must start with a multiple of 10", and you're seeing UIDs in the 3.15 billion range.It's not prone to happen by accident on well-maintained systems serving actual users. But it's easy for plucky young coders multiplied by time in neglect to cause something to happen by accident.
(My company used ComeMommy's services for a while.)
Ah, yes, doing it wrong will cause wrongness. :D And sometimes maliciousness and stupidity are impossible to tell apart really.
I mean, I'm not arguing for the bug not to be fixed. It really should be, and the guilty party flogged with the tail of a porcupine.
-
They are kindof expected, and will keep happening since there are junior devs, and shitty senior devs. The really wonderful thing is how the priviledge management system defaults to "Oh, I guess admin it is then!"
With systemd, of course
-
@Gąska yes it is, in that you have to get the userid above max_int to make this happen, and if I'm not mistaken that means you have to subvert the tooling for creating users.
You are mistaken. All you have to do is set the
-uoption ofuseraddcommand, which is a very routine thing that's done all the time for many different reasons.
-
@anotherusername said in WTF Bites:
@sweaty_gammon yes, but setting userids above max_int seems like it would not be a normal fumble, but someone up to no good.
It needs to be fixed, absolutely, but you still have the original problem of someone with hightened system access doing shady shit.So... the UID is, for some reason, represented by a signed integer, and for no really obvious reason, they're restricting it to the non-negative integers. If a UID is created that is larger than MAX_INT, it's interpreted as a negative integer, and when it's interpreted as a negative integer, the assertion fails (it's checking for >= 0). And if the assertion fails, the code bombs out and the user gets admin by default.
You're missing one detail - UID is actually represented by unsigned integer everywhere, except in this one single broken piece of code where it accidentally reads it as signed instead.
-
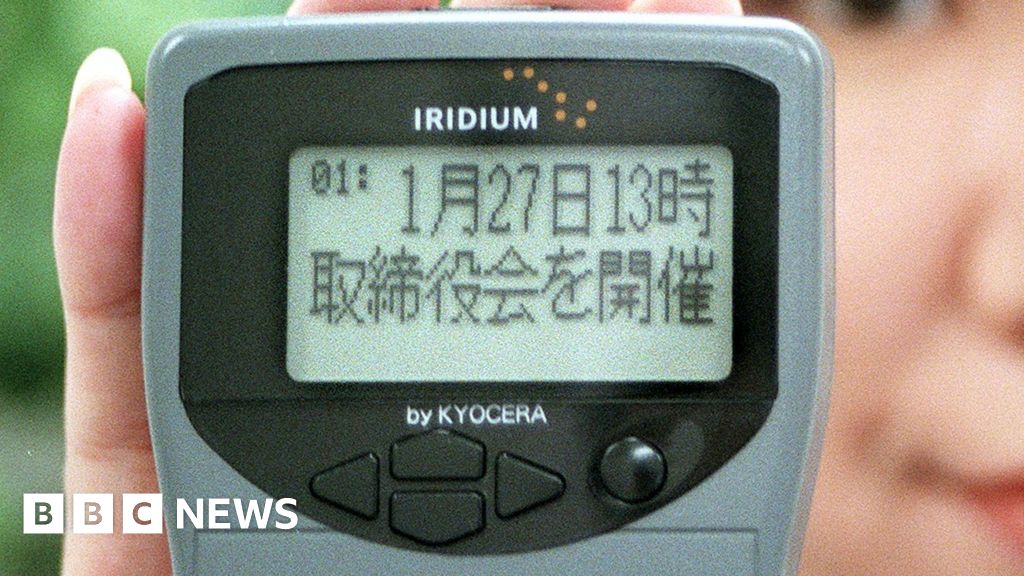
There is 1500 users of pagers in Japan
-
@TimeBandit and millions more in USA.
-
-
@TimeBandit I thought you were making fun of still using technology that's been decades out of date?
-
@TimeBandit I thought you were making fun of still using technology that's been decades out of date?
Yes, I am
-
Backward
bugcompatibility
-
@TimeBandit I bet this guy rants all the time how a diskette for save icon doesn't make sense.
-
I bet this guy rants all the time how a diskette for save icon doesn't make sense.
Do you mean that it does?

-
@TimeBandit I bet this guy rants all the time how a diskette for save icon doesn't make sense.
Or the fact we search individual documents with binoculars and entire computers with a magnifying glass?
-
@Lorne-Kates What a
cnt.
-
@anotherusername said in WTF Bites:
@sweaty_gammon yes, but setting userids above max_int seems like it would not be a normal fumble, but someone up to no good.
It needs to be fixed, absolutely, but you still have the original problem of someone with hightened system access doing shady shit.So... the UID is, for some reason, represented by a signed integer, and for no really obvious reason, they're restricting it to the non-negative integers. If a UID is created that is larger than MAX_INT, it's interpreted as a negative integer, and when it's interpreted as a negative integer, the assertion fails (it's checking for >= 0). And if the assertion fails, the code bombs out and the user gets admin by default.
You're missing one detail - UID is actually represented by unsigned integer everywhere, except in this one single broken piece of code where it accidentally reads it as signed instead.
Well, I didn't necessarily "miss" that point. It happens inside
polkit_unix_process_get_uid, whatever that is. I don't know enough about the code to know whether that's "this one single broken piece of code", or whether it's a library that would affect other code too. It didn't seem very important, anyway, since I was commenting on the WTFs found in that single broken piece of code.Regardless, it shouldn't matter. Just using a signed integer type shouldn't have even been a problem. It shouldn't be doing any math with the ID, and there's no reason why negative values should be excluded.
-
@TimeBandit said in WTF Bites:
Backward
bugcompatibility
tl;dr: he created a file named
aux.hon Linux, then tried to copy that file on Windows, and Windows said nope becauseauxis a reserved system "file" (no matter what the directory or extension is).Also, this was related to a hyperlink of doom bug on Windows 95 and 98. (Before Microsoft released a patch to fix the vulnerability, trying to access a file such as
c:\aux\auxwould cause the system to BSOD.)
-
@anotherusername said in WTF Bites:
Before Microsoft released a patch to fix the vulnerability
The patch was released March 16, 2000
At the bottom of the page
And of course, when you click it
-
@TimeBandit said in WTF Bites:
@anotherusername said in WTF Bites:
Before Microsoft released a patch to fix the vulnerability
The patch was released March 16, 2000
At the bottom of the page
And of course, when you click it
-
-
@TimeBandit said in WTF Bites:
@Tsaukpaetra said in WTF Bites:
This one does the same thing
I'm only slightly sad that https://www.microsoft.com/com1/com0/ does not crash the cloud....
-
@anotherusername said in WTF Bites:
It happens inside
polkit_unix_process_get_uid, whatever that is.Oh, PolicyKit, another piece of crapware originally made by the systemd guy that he abandoned and then later subsumed into systemd. It's the same idiot, the one that Linus said the following about:
I'm fucking tired of the fact that you don't fix problems in the code you write, so that the kernel then has to work around the problems you cause.
-
@TwelveBaud said in WTF Bites:
It's the same idiot
Also the same idiot that made Pulse Audio.
For a long time, the first thing to do after installing Ubuntu was to purge that crap from it if you wanted sound to work
-
Time for another broad-leaf plant to carry its handlers' gut bacteria into our systems, as a nation.
You don't need to stop eating lettuce over a little e. coli. Just boil it well before use and it will be absolutely safe to consume.
</british_food_suggestion>
-
@dkf ah yes. Also if I skim the grease from the top of the pot while boiling, the top of my pizza will be free of unsightly pools.
-
Also if I skim the grease from the top of the pot while boiling, the top of my pizza will be free of unsightly pools.
You boil your pizza?

-
@anotherusername said in WTF Bites:
tl;dr: he created a file named aux.h on Linux,
 He didn't create the file; IBM did:
He didn't create the file; IBM did:IBM shipped some opengl headers as AUX.H on one of the OS/2 devcon disks.
-
@TimeBandit said in WTF Bites:
Also if I skim the grease from the top of the pot while boiling, the top of my pizza will be free of unsightly pools.
You boil your pizza?

-
esoteric also confuses content filters?
http://nav.webring.org/cgi-bin/navcgi?ring=esolang;listmaybe it's webring in general?
-
In other news, approximately every link is dead. If you likes you some bit-rot, check out this bit-rot.
-
In other news, approximately every link is dead. If you likes you some bit-rot, check out this bit-rot.
I'm familiar with webring. I used to have a couple of sites there. The bit-rot didn't just happen naturally, the new owners (some years ago) pretty much caused it by making it difficult for the ring owners. Why you would buy a site, and then go out of your way to ruin it, I don't know.
</tangent>
-
webring.
That still exists?
buy a site, and then go out of your way to ruin it
I guess not.
-
^^ Not sure where it gets that title from; the article headline is "CIMON, the International Space Station’s artificial intelligence, has turned belligerent" which is rather more descriptive.
Lots of HHGTTG references in the article. Key points:
In this case, the free-floating IBM artificial intelligence was — for the first time — interacting with ESA astronaut Alexander Gerst.
[...]
He then helps Gerst complete a task — and responds to a request to play the song Man Machine by Kraftwerk.From the article, it sounds like it basically froze at this point; it would not turn off the music or respond to any other commands. But then:
A flustered and bemused Gerst then appealed to Ground Control for some help: how does one put an obdurate robot back in its place?
CIMON overheard the appeal.
“Be nice, please,” it warned Gerst.And so:
CIMON’s now back in his box, powered down.
No further interactive sessions are planned for the immediate future.
-
@sweaty_gammon said in WTF Bites:
@Lorne-Kates I am sure we can all cherry pick badly written code to straw-man someone else.
If you think any of the above sql statements are badly written (pseudocode aside), then you're the WTF.
-
@TimeBandit The onebox is just three copies of the same text with no depiction of the error. Now I have to click through and RTFA, ugh

 Read and Share Twitter Threads easily!
Read and Share Twitter Threads easily!