WTF Bites
-
@Tsaukpaetra said in WTF Bites:
Should have posted a screenshot, I don't see anything immediately wrong...

In particular, stuff like this:
-
And here's why:

Filed under:
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />Also filed under: <td valign="top" style="border-style:none solid solid;padding:0in 5.4pt;width:155.8pt;border-right-width:1pt;border-bottom-width:1pt;border-left-width:1pt;">
-
@Onyx Given that there was one commit, a year ago, I wonder whether they'd actually do anything with a bug report/pull request
E_BY_DESIGN
-
-
So...my 3 yo used the phrase "fucking asshole" correctly.
-
So...my 3 yo used the phrase "fucking asshole" correctly.
Don't you love social learning?
-
@Tsaukpaetra said in WTF Bites:
So...my 3 yo used the phrase "fucking asshole" correctly.
Don't you love social learning?
Yes, and I curse too much.
-
-
@HardwareGeek said in WTF Bites:
So...my 3 yo used the phrase "fucking asshole" correctly.
Trump?

LOL
I've joked with my husband how I will tell her later all the scary stories people used to tell about the orange boogeyman and she will laugh about how gullible people are.
She was coloring. Maybe she was pissed off that the crayon didn't go where she intended. You know, it is a lot easier to blame the tool rather than the one using the tool.
-
I've joked with my husband how I will tell her later all the scary stories people used to tell about the orange boogeyman and she will laugh about how gullible people are.
And then you'll laugh and laugh, loudly for everyone to hear. Smiling fully, because any set of eyes may be his, and any wall may have ears. Or cameras. Dear Leader's glorious sky is full of drones. You know they're there, even though you can't hear them. Even if you could stop laughing-- were allowed to stop laughing-- you couldn't hear the silent eyes above.
You and your daughter collect, mandatory smiles on your faces, collect your weekly ration of Great Food, and return to Relocation Zone #7221.
-
TIL that having a press release is a COORDINATED CAMPAIGN AIMED AT RUINING LINUX FOREVER!!!
-
Twitter, this is not how time works
-
So...my 3 yo used the phrase "fucking asshole" correctly.
Almost ready for this forum!
-
So...my 3 yo used the phrase "fucking asshole" correctly.
Almost ready for this forum!
She hasn't learned all her Programming ABC++ yet.
https://www.kickstarter.com/projects/627324241/programming-languages-abc
TBH neither have I.
-
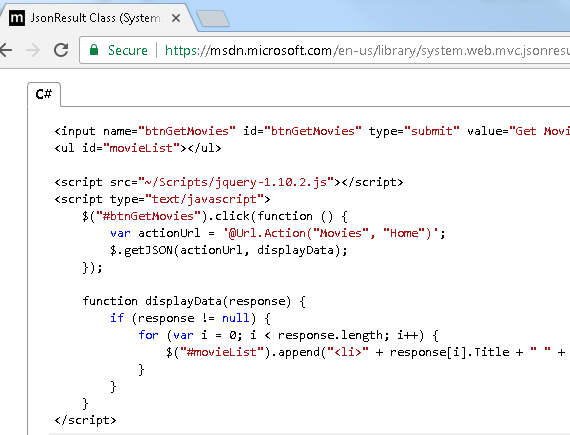
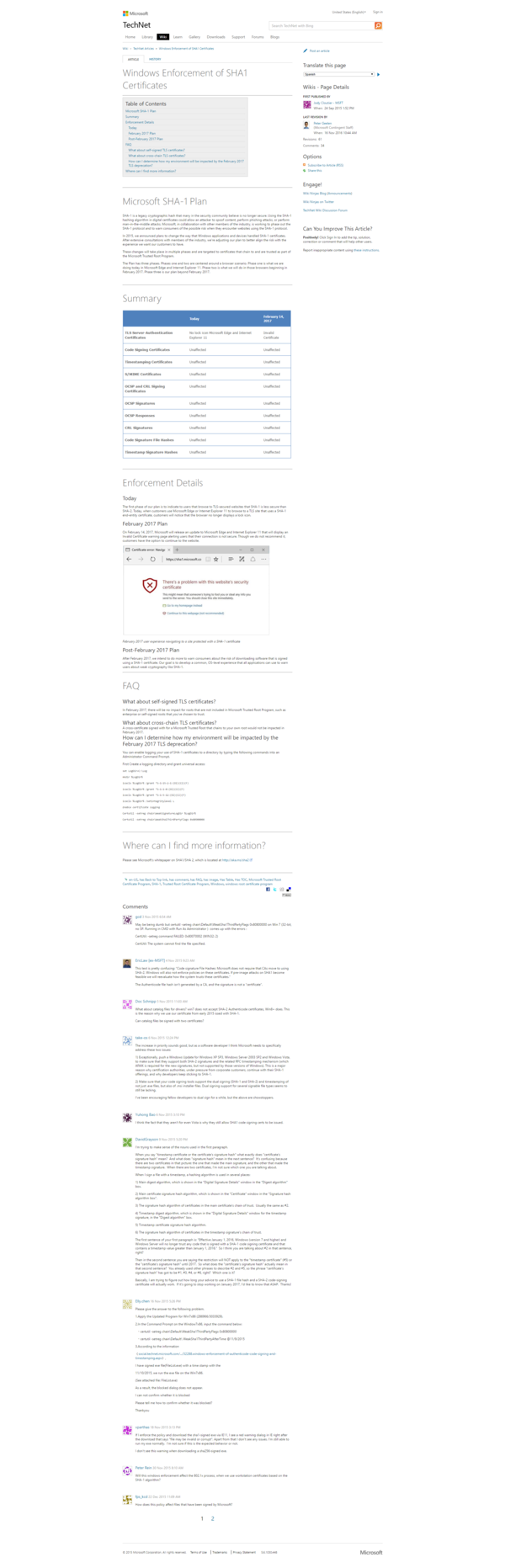
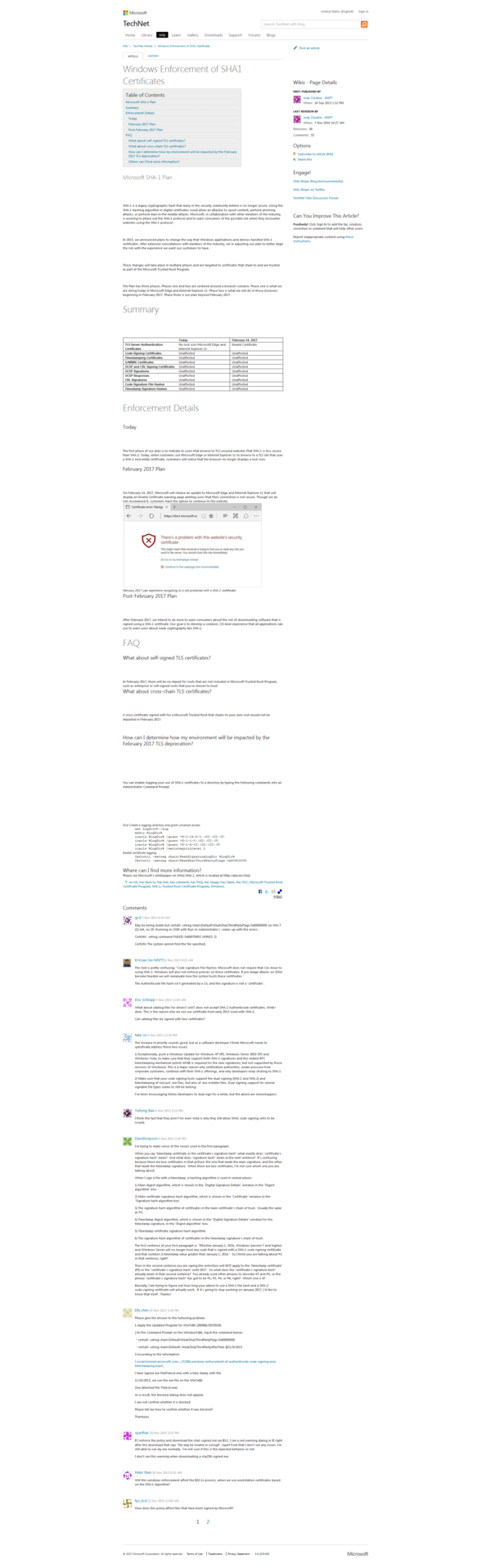
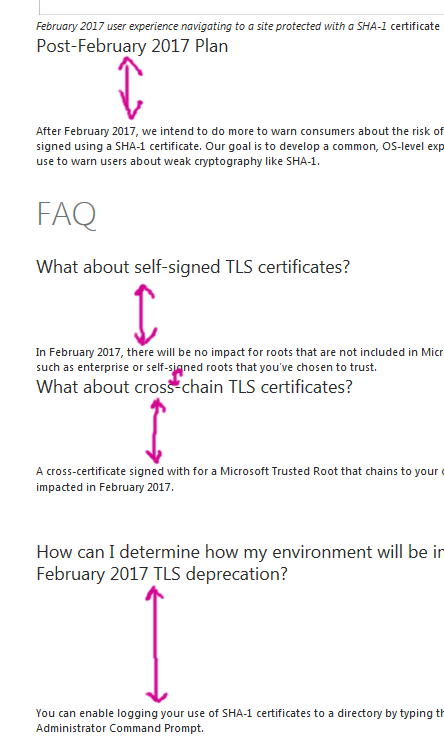
Really? An XSS vulnerability in the example code on the MSDN website?
I expect this shit from StackOverflow or w3fools, but I expected better from Microsoft.
-
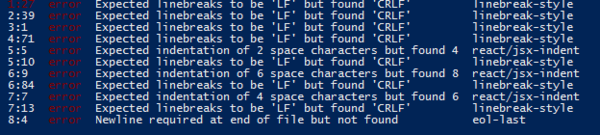
I think someone needs a clue-by-four on what exactly an actual "error" is supposed to be.
-
An XSS vulnerability in the example code on the MSDN website?
Just for clarity, asking for a dog, but, um.... can you maybe highlight where? Do it in blue, so he can tell the difference, if you may...
-
@Tsaukpaetra said in WTF Bites:
An XSS vulnerability in the example code on the MSDN website?
Just for clarity, asking for a dog, but, um.... can you maybe highlight where? Do it in blue, so he can tell the difference, if you may...
Hint: It's the part where they're appending an unsanitized string from the network into HTML.
Generally, concatenating HTML is just as dangerous as concatenating SQL statements. Just don't do it.
-
@Tsaukpaetra said in WTF Bites:
An XSS vulnerability in the example code on the MSDN website?
Just for clarity, asking for a dog, but, um.... can you maybe highlight where? Do it in blue, so he can tell the difference, if you may...
Hint: It's the part where they're appending an unsanitized string from the network into HTML.
Generally, concatenating HTML is just as dangerous as concatenating SQL statements. Just don't do it.
How do we know it's an unsanitized string from the network? Especially arbitrarily sourced? Seems to me that if you're interfering with the host already, you don't need an XSS attack...
-
@Tsaukpaetra Because a couple of lines above it they use jquery to pull the data in from the remote server. You can't rely on the network being secure, even if the host machine otherwise is...
-
@Tsaukpaetra said in WTF Bites:
@Tsaukpaetra said in WTF Bites:
An XSS vulnerability in the example code on the MSDN website?
Just for clarity, asking for a dog, but, um.... can you maybe highlight where? Do it in blue, so he can tell the difference, if you may...
Hint: It's the part where they're appending an unsanitized string from the network into HTML.
Generally, concatenating HTML is just as dangerous as concatenating SQL statements. Just don't do it.
How do we know it's an unsanitized string from the network? Especially arbitrarily sourced? Seems to me that if you're interfering with the host already, you don't need an XSS attack...
I know it's unsantized because no escape function is called. I know it's from the network because
$.getJSONfetches data from the network. And even if you trust that you will never get malicious data from that service (which you can't), it still fails in hilarious ways with perfectly valid data sets.Bad code is bad.
-
You can't rely on the network being secure, even if the host machine otherwise is...
So then use https, isn't that the whole point of that protocol?
Again, if you're already interfering with the network traffic from the host, you probably don't need to be looking at a particular data point returned by it in order to XSS...
-
it still fails in hilarious ways with perfectly valid data sets.
I contend if it's a perfectly valid data set, it wouldn't fail, because it's valid.
-
@Tsaukpaetra said in WTF Bites:
You can't rely on the network being secure, even if the host machine otherwise is...
So then use https, isn't that the whole point of that protocol?
Again, if you're already interfering with the network traffic from the host, you probably don't need to be looking at a particular data point returned by it in order to XSS...
Suppose Mallory has compromised partial access to your system. She can't modify any files, but she's found an exploit that lets her insert movie records. Well, that's not much of an attack... Except for that XSS vector that lets her escalate privileges by stealing the session of an administrator. Now she has full access!
Filed under: This is taking me back to when I actually did this.
-
@Tsaukpaetra said in WTF Bites:
it still fails in hilarious ways with perfectly valid data sets.
I contend if it's a perfectly valid data set, it wouldn't fail, because it's valid.
<movie_name_here> is a perfectly valid movie name, and yet the script chokes on it.
-
@Tsaukpaetra said in WTF Bites:
it's valid.
though, TBH, expecting JSON from a controller like this is probably even worse, as anything other than a 200 OK will return the default error page view HTML and not an error JSON string...
she's found an exploit that lets her insert movie records
Which is fine and dandy, except the server should be validating said movie inserts to.. I don't know, validating them?
<movie_name_here> is a perfectly valid movie name, and yet the script chokes on it.
And who's to say the server isn't producing HTML-escaped strings for the response anyways? That may have been the inserted record, but when it returns it it doesn't just spit it out as is right back.
-
@Tsaukpaetra said in WTF Bites:
And who's to say the server isn't producing HTML-escaped strings for the response anyways?
Well, first, that's an awful API. What if I want to put that title somewhere besides HTML? You're mixing concerns of presentation. But more importantly, your script should never trust the other side, especially with the potential for an attack this devastating. Hell, there could be a bug in the escaping code; even sanitization is a band-aid. The correct answer is: don't treat HTML like strings.
It's not so hard to write
$( '<li>' ).text( movie.Title );, and there you go. Zero chance for XSS.
-
that's an awful API.
It's not an API controller. Your argument is invalid. Hence why I said:
@Tsaukpaetra said in WTF Bites:
though, TBH, expecting JSON from a controller like this is probably even worse, as anything other than a 200 OK will return the default error page view HTML and not an error JSON string...
The correct answer is: don't treat HTML like strings.
Well, duh. But that's in another chapter. :P
-
@Tsaukpaetra said in WTF Bites:
And who's to say the server isn't producing HTML-escaped strings for the response anyways?
Well, first, that's an awful API. What if I want to put that title somewhere besides HTML? You're mixing concerns of presentation. But more importantly, your script should never trust the other side, especially with the potential for an attack this devastating. Hell, there could be a bug in the escaping code; even sanitization is a band-aid. The correct answer is: don't treat HTML like strings.
It's not so hard to write
$( '<li>' ).text( movie.Title );, and there you go. Zero chance for XSS.The jQuery people should just make append(String) append a text node instead of parsing HTML.
-
Hell, there could be a bug in the escaping code; even sanitization is a band-aid.
I guess forums just shouldn't allow user-submitted content, then, since all markup languages are evil.
-
@ben_lubar said in WTF Bites:
Hell, there could be a bug in the escaping code; even sanitization is a band-aid.
I guess forums just shouldn't allow user-submitted content, then, since all markup languages are evil.
Well, considering that we have XSSed the forums on multiple occasions...
But using e.g. a full parser or template engine mitigates most cases. I like BBCode for this, if only because it forces you to use a proper parser. It's damn hard to get sanitization right yourself, and the
 example made no attempt whatsoever.
example made no attempt whatsoever.
-
the example made no attempt whatsoever.
Look, all
Idog wanted was a blue highlight of the WTF, and here we are a whole page of argument. WTF
Besides, if every example put out was a perfect paradigm of excellent coding, you'd lose the point of the example amidst all the extra cruft needed to make it more Production Viable.
-
Well, considering that we have XSSed the forums on multiple occasions...
I only recall one case where XSS was demonstrated after we switched to htmlcleaner, and that was for the same reason that @index shows a number.
-
@Tsaukpaetra said in WTF Bites:
though, TBH, expecting JSON from a controller like this is probably even worse, as anything other than a 200 OK will return the default error page view HTML and not an error JSON string...
Where have I seen that recently...
-
@Tsaukpaetra said in WTF Bites:
the example made no attempt whatsoever.
Look, all
Idog wanted was a blue highlight of the WTF, and here we are a whole page of argument. WTF
Besides, if every example put out was a perfect paradigm of excellent coding, you'd lose the point of the example amidst all the extra cruft needed to make it more Production Viable.
Compare the length of these code snippets:
for (var i = 0; i < response.length; i++) { $("#movieList").append("<li>" + response[i].Title + "</li>"); }response.forEach(function(movie) { $("#movieList").append($("<li>").text(movie.Title)); });Which one is more understandable? Which one has an XSS vulnerability? Are they the same one?
-
@Tsaukpaetra said in WTF Bites:
the example made no attempt whatsoever.
Look, all
Idog wanted was a blue highlight of the WTF, and here we are a whole page of argument. WTF
Besides, if every example put out was a perfect paradigm of excellent coding, you'd lose the point of the example amidst all the extra cruft needed to make it more Production Viable.
- There is no example code that has not been copypasta'd into production by someone, somewhere
- The exploit in this code is trivially mitigated (see above)
- The API being demonstrated was just how to retrieve JSON data. There was no need for the example to futz around with HTML handling in JS at all
- Don't trust that security is handled Somewhere Else.
- Don't assume that because an attack requires elevated permissions to execute, that it's pointless to defend against. This is how a minor exploit becomes a major exploit (see above)
-
-
@Tsaukpaetra said in WTF Bites:
@ben_lubar said in WTF Bites:
Compare the length of these code snippets:
No.
That code is just putting its presentation logic in the wrong layer. The fix is to use a templating system, not inline the HTML.
-
The fix is to use a templating system,
Recommendations? This damn site already has ~47 NuGet packages that I'm sure probably aren't actually needed...
-
@Tsaukpaetra said in WTF Bites:
@ben_lubar said in WTF Bites:
Compare the length of these code snippets:
No.
That code is just putting its presentation logic in the wrong layer. The fix is to use a templating system, not inline the HTML.
You technically only have to guard against XSS when concatenating strings you don't control.
Calling toString on an integer or using a string literal would count as a string you do control.
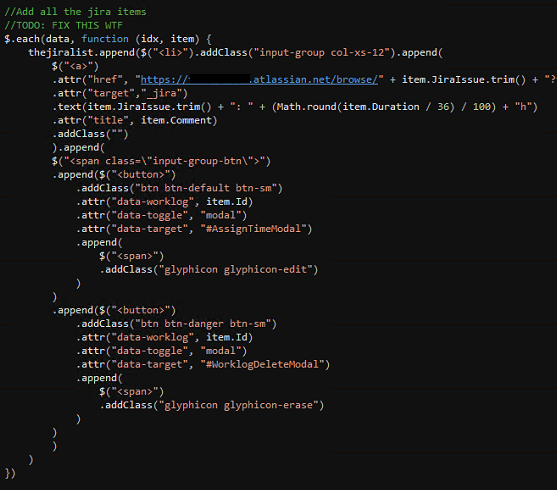
Also, why the fuck are you calling addClass with an empty string?
-
@ben_lubar said in WTF Bites:
Also, why the fuck are you calling addClass with an empty string?
Forgot to remove. It's hard enough to get the stuff to generate in the right manner, I was basically manipulating the DOM by hand until the desired result was achieved, then mapping that back into jQuery calls.
No, I'm not really a front-end dev (or maybe, I am...)
-
@Tsaukpaetra said in WTF Bites:
The fix is to use a templating system,
Recommendations? This damn site already has ~47 NuGet packages that I'm sure probably aren't actually needed...
I think I need more information. JS templating engines are a dime a dozen these days, and range from extremely simple to extremely complex.
-
@Tsaukpaetra said in WTF Bites:
The fix is to use a templating system,
Recommendations? This damn site already has ~47 NuGet packages that I'm sure probably aren't actually needed...
I think I need more information. JS templating engines are a dime a dozen these days, and range from extremely simple to extremely complex.
Personally, I'd go with something like https://golang.org/pkg/html/template/#pkg-examples if you can find a C# equivalent.
-
@Tsaukpaetra said in WTF Bites:
The fix is to use a templating system,
Recommendations? This damn site already has ~47 NuGet packages that I'm sure probably aren't actually needed...
I think I need more information. JS templating engines are a dime a dozen these days, and range from extremely simple to extremely complex.
The site was made ~1 year ago by a guy. C# Asp.Net MVC (kinda) site, Uses Entity Framework, and > 70% of the pages/controllers/etc were created by doing a "Create Controller based on Entity" action.
-
@Tsaukpaetra said in WTF Bites:
@Tsaukpaetra said in WTF Bites:
The fix is to use a templating system,
Recommendations? This damn site already has ~47 NuGet packages that I'm sure probably aren't actually needed...
I think I need more information. JS templating engines are a dime a dozen these days, and range from extremely simple to extremely complex.
The site was made ~1 year ago by a guy. C# Asp.Net MVC (kinda) site, Uses Entity Framework, and > 70% of the pages/controllers/etc were created by doing a "Create Controller based on Entity" action.
I'm assuming the code you showed exists because you had a requirement to modify the DOM with data from the server. Is that common? Do you need e.g, conditional or looping logic? How about bidirectional data binding?
-
I'm assuming the code you showed exists because you had a requirement to modify the DOM with data from the server.
Is that common?
Somewhat, to this page at least.
Do you need e.g, conditional or looping logic?
The screenshot is part of a jQuery DataTables definition for a column, which loops data ajaxed in to generate the table (and, here, the HTML that would be placed in that particular column's cell).
How about bidirectional data binding?
I'm not certain I could hook that up. We're already abusing a damn normal controller to be the "API" because the actual API controller is being used for something else entirely (I'll rectify that later, right now I'm just fixing our timecard system).
-
How about bidirectional data binding?
I'm not certain I could hook that up. We're already abusing a damn normal controller to be the "API" because the actual API controller is being used for something else entirely (I'll rectify that later, right now I'm just fixing our timecard system).
I'm talking about a view and a viewmodel both on the client-side. In general, I prefer systems where my markup and content are kept separately. Update the viewmodel, and the view updates. Interact with the view, and the viewmodel updates.
Knockout strikes a good balance of being not too heavy but still providing MVVM goodness on the client-side.
-
Knockout
I'm pretty sure that's one of the NuGet packages installed, yes. Not NFC how to use it and didn't know that's what it was (I haven't went through the package list reading all the descriptions yet).
-
@Tsaukpaetra said in WTF Bites:
Knockout
I'm pretty sure that's one of the NuGet packages installed, yes. Not NFC how to use it and didn't know that's what it was (I haven't went through the package list reading all the descriptions yet).
I might be able to do a live demo/tutorial sometime.
-
@Tsaukpaetra said in WTF Bites:
Knockout
I'm pretty sure that's one of the NuGet packages installed, yes. Not NFC how to use it and didn't know that's what it was (I haven't went through the package list reading all the descriptions yet).
I might be able to do a live demo/tutorial sometime.
It might be nice. Right now I'm just so frustrated at how datetimes are being screwed over between the client to the server to the database, especially since it's apparently very difficult to keep timezone data together all down the line....