Moar Cooties
-
@boomzilla said in Moar Cooties:
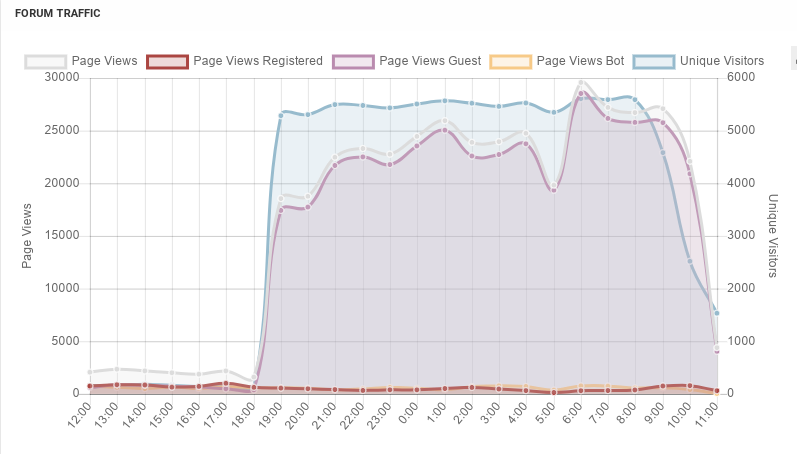
the surge is from guests
Would it be possible to auto-block guests that defeat the caching pattern?
 , I know, but it seems like we've had at least two high-impact instances of this in the past few weeks.
, I know, but it seems like we've had at least two high-impact instances of this in the past few weeks.
-
@lolwhat said in Moar Cooties:
@boomzilla said in Moar Cooties:
the surge is from guests
Would it be possible to auto-block guests that defeat the caching pattern?
 , I know, but it seems like we've had at least two high-impact instances of this in the past few weeks.
, I know, but it seems like we've had at least two high-impact instances of this in the past few weeks.The problem is that it's really distributed. A particular IP address doesn't make many requests. But they're using lots of IP addresses to make requests.
Ah...now I've blocked the shadier countries on this list:
-
I do believe I'm starting to make a dent (famous last words):
-
@discobot has been vomiting hilariously these past couple of days., since
/user/:slugcontains posts and therefore is affected. I'm almost motivated to finally implement caching.
-
403s over the last half hour or so:- 14:50 - 14:59 2700
- 15:00 - 15:09 4806
- 15:10 - 15:19 9733
- 15:20 - 15:25 8595
-
@discobot http 403
-
-
@boomzilla said in Moar Cooties:
403s over the last half hour or so:- 14:50 - 14:59 2700
- 15:00 - 15:09 4806
- 15:10 - 15:19 9733
- 15:20 - 15:25 8595
- 15:20 - 15:29 13464
- 15:30 - 15:39 22076
Fucking hell...up to 333 IP blocks added today (mostly
/24s).
-
@boomzilla Rat bastards aren't going away, are they...
-
@lolwhat I wonder if the Chicoms noticed a post about HK around here somewhere.
-
Load average is finally starting to come down:
10.15, 14.86, 30.04
-
@boomzilla said in Moar Cooties:
@boomzilla said in Moar Cooties:
403s over the last half hour or so:- 14:50 - 14:59 2700
- 15:00 - 15:09 4806
- 15:10 - 15:19 9733
- 15:20 - 15:25 8595
- 15:20 - 15:29 13464
- 15:30 - 15:39 22076
Fucking hell...up to 333 IP blocks added today (mostly
/24s).- 15:40 - 15:49 37678
-
@cheong Are you still able to access?
-
@lolwhat if he can't it's not because I blacklisted his IP address.
Damn...I was having flashbacks to discodays there, things were so slow.
-
@dkf said in Moar Cooties:
Not when those requests are defeating the caching pattern.
If you need caching to answer a GET request every 20 minutes, you should run your webserver on something more powerful than a toaster

-
@TimeBandit said in Moar Cooties:
@dkf said in Moar Cooties:
Not when those requests are defeating the caching pattern.
If you need caching to answer a GET request every 20 minutes, you should run your webserver on something more powerful than a toaster

What are you talking about?
-
@TimeBandit Discourse reigns supreme, as always - put another Docker instance on a toaster with a dial-up, and point all the Estonian traffic at that.
(/s)
-
@boomzilla said in Moar Cooties:
What are you talking about?
I would go back up thread and put the whole context here but

-
Not seeing any more IP ranges jumping out at me.
load average: 2.70, 4.27, 12.39- 15:50 - 15:59 29808
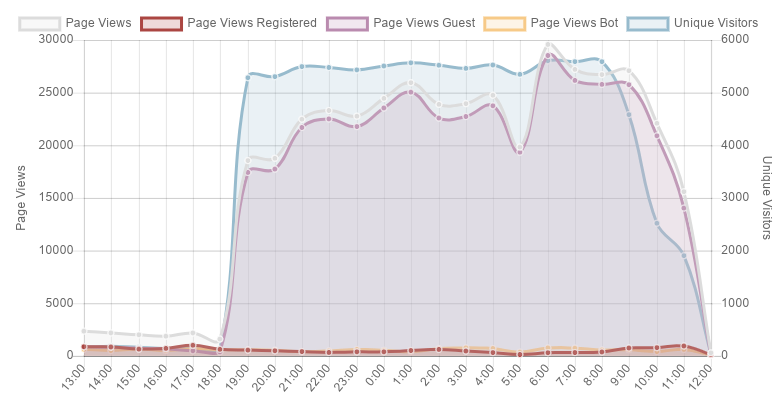
The last hour looks a lot better:
-
@pie_flavor said in Moar Cooties:
@TimeBandit Discourse reigns supreme, as always - put another Docker instance on a toaster with a dial-up, and point all the
Estonian/t/1000 traffic at that.
(/s)
-
@pie_flavor said in Moar Cooties:
Discourse reigns supreme, as always
Only on Earth-73.
On Earth-47, it sucks really hard

-
@pie_flavor said in Moar Cooties:
@TimeBandit Discourse reigns supreme, as always - put another Docker instance on a toaster with a dial-up, and point all the Estonian traffic at that.
(/s)Firstly, I was not aware discourse had clustering capabilities.
Secondly, paying rent and power for all those toasters must cost significantly more than a single nodebb server.
-
@PleegWat said in Moar Cooties:
Secondly, paying rent and power for all those toasters must cost significantly more than a single nodebb server.
Put all the hosting for

 in
in  . The waste heat will
. The waste heat will 




-
@PleegWat Of course it does.
-
-
@HardwareGeek said in Moar Cooties:
Put all the hosting for

 in
in  . The waste heat will
. The waste heat will 




Fun fact: this forum is hosted in

-
@lolwhat said in Moar Cooties:
@cheong Are you still able to access?
I'm still here.
We neither use "China Unicom" nor "China Telecom" here, so the IP range is different.
-
-
-
@TimeBandit
Freezing cooties does not kill them, merely places them in hibernation. You're like Cootiephoid Mary.
-
@loopback0 said in Moar Cooties:
The evidence suggests otherwise.
Evidence must have been collected before the first coffee

-
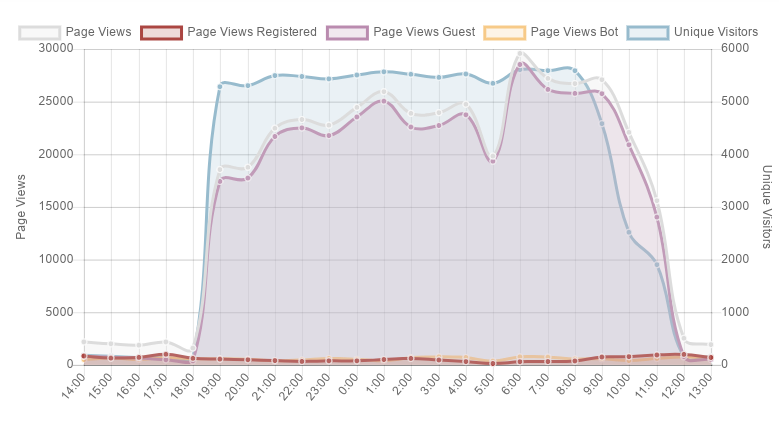
They're still trying. Over 180K 403s in the last hour. Traffic seems to have gone back to normal.
-
@boomzilla said in Moar Cooties:
@lolwhat I wonder if the Chicoms noticed a post about HK around here somewhere.
I assume they'd just blackhole the whole site, right? The only thing they care about is not letting any information get into China.
-
@topspin no clue.
-
@boomzilla said in Moar Cooties:
The problem is that it's really distributed. A particular IP address doesn't make many requests. But they're using lots of IP addresses to make requests.
This all seems really weird. Did someone misconfigure their botnet to attack the wrong site?
I mean, what would there be to gain in intentionally DOSing this place.Out of curiosity, are there any patterns the suspicious requests have in common? Maybe user agent string or something.
-
@topspin said in Moar Cooties:
@boomzilla said in Moar Cooties:
The problem is that it's really distributed. A particular IP address doesn't make many requests. But they're using lots of IP addresses to make requests.
This all seems really weird. Did someone misconfigure their botnet to attack the wrong site?
I mean, what would there be to gain in intentionally DOSing this place.Out of curiosity, are there any patterns the suspicious requests have in common? Maybe user agent string or something.
There were a handful of culprits that kept showing up in whois output, but the user agents seemed to be a variety of browsers and platforms. Except they only ever sent a GET and never any websocket traffic like you get when someone is actually browsing (even guests).
Still over 190K 403s in the last hour, and I still don't see anything obvious getting through.
-
@topspin Basically, I'd run this:
grep -i "2019:13:.* 200 " access.log | cut -f1 -d" " | cut -d. -f1,2,3,4 | sort | uniq -c...updating the time as time went on, and then I'd see lots of stuff like this:
9 95.85.70.126 7 95.85.70.137 9 95.85.70.155 8 95.85.70.16 6 95.85.70.162 6 95.85.70.164 5 95.85.70.187 5 95.85.70.188 4 95.85.70.189 6 95.85.70.190 5 95.85.70.211 7 95.85.70.218 8 95.85.70.22 10 95.85.70.223 3 95.85.70.225 4 95.85.70.231 7 95.85.70.232 8 95.85.70.234 12 95.85.70.235 11 95.85.70.237 7 95.85.70.247 7 95.85.70.253 7 95.85.70.36 6 95.85.70.37 5 95.85.70.42 7 95.85.70.45 3 95.85.70.54 8 95.85.70.64 5 95.85.70.70 10 95.85.70.77 1 95.85.70.80 4 95.85.70.87 4 95.85.70.93 7 95.85.71.107 3 95.85.71.113 8 95.85.71.115 7 95.85.71.117 5 95.85.71.120 5 95.85.71.123 5 95.85.71.124 3 95.85.71.131 3 95.85.71.141 1 95.85.71.142 2 95.85.71.144 2 95.85.71.156And that's a tiny sample of one particular block. Really obvious once you know what you're looking at.
-
-
@loopback0 yes. That was one of the names that showed up over and over.
-
@boomzilla That is a lot of similar IPs.
I'm going to show my ignorance here by asking a really dumb question: Can those be spoofed? I assume they can't, but I don't know at what point exactly the handshake happens. So I'm not sure if you can make a GET request with a spoofed IP if that gets through (and the reply just doesn't reach the target) or if you'd never even see the request because the ACK gets dropped before.
-
Maybe we should ask @apapadimoulis if he's gotten any "That's a nice website you have there..." emails.
-
@loopback0 said in Moar Cooties:
route: 95.85.70.0/24
descr: QualityNetwork OU
origin: AS57172"Quality" Cooties.
Postal code appears to be in Prague, east-central area.
According to cleantalk.org, some specific addresses in the /24 are known to have spam activity on 200+ websites.
-
@topspin said in Moar Cooties:
Can those be spoofed?
I don't believe so, just from the way that TCP works (or so the interwebs tell me).
-
@HardwareGeek said in Moar Cooties:
@loopback0 said in Moar Cooties:
route: 95.85.70.0/24
descr: QualityNetwork OU
origin: AS57172"Quality" Cooties.
Postal code appears to be in Prague, east-central area.
According to cleantalk.org, some specific addresses in the /24 are known to have spam activity on 200+ websites.Also:
person: QUALITY NETWORK CORP
address: Office 14, Trinity House, Victoria, Mahe, Seychelles. SC-12Saw that address a lot.
-
@boomzilla said in Moar Cooties:
@topspin said in Moar Cooties:
Can those be spoofed?
I don't believe so, just from the way that TCP works (or so the interwebs tell me).
I assumed so, too, simply because HTTP is on a higher layer than TCP. But as I said before, I don't really know.
-
@acrow said in Moar Cooties:
Times 25k clients.
That's about 14 request per second, it's not that much

-
@topspin said in Moar Cooties:
I mean, what would there be to gain in intentionally DOSing this place.
Someone is trying to increase programmer productivity?
-
@dcon said in Moar Cooties:
@topspin said in Moar Cooties:
I mean, what would there be to gain in intentionally DOSing this place.
Someone is trying to increase programmer productivity?
My boss doesn't have the skills to pull of a DDOS.

-
@boomzilla said in Moar Cooties:
@HardwareGeek said in Moar Cooties:
@loopback0 said in Moar Cooties:
route: 95.85.70.0/24
descr: QualityNetwork OU
origin: AS57172"Quality" Cooties.
Postal code appears to be in Prague, east-central area.
According to cleantalk.org, some specific addresses in the /24 are known to have spam activity on 200+ websites.Also:
person: QUALITY NETWORK CORP
address: Office 14, Trinity House, Victoria, Mahe, Seychelles. SC-12Saw that address a lot.
Yeah the first search of mine had that address but the country they were based in was listed as Russia.
-
@topspin
That's what the boss's nephew is for.Filed under: Script kiddie
 Setting up a cluster?
Setting up a cluster?


