TIL (about the Dark Arts of HTML)
-
@anonymous234 said in TIL (about the Dark Arts of HTML):
@Zecc Those voices and shots of people in the control room make it seem like they are directing the thing in real time. Which is impossible since it takes signals 40 minutes to get back to Earth.
Actually, depending on the relative positions, it's between 4 and 24 minutes for one-way communications.
-
TIL that Silly String actually has military use:
Silly String and similar products have been used by the military to detect tripwires for explosive booby traps. The string is sprayed over the suspected area, and if the string falls to the ground, no tripwires are present since the string would catch on the tripwires (but is not heavy enough to activate the explosive).
How it was invented:
The partners initially wanted to create a can of aerosol that one would be able to spray on a broken/sprained leg or arm and use as an instant cast. After having gone through about 30 or 40 [nozzles to test], Fish came upon one that produced a nice string, which shot about 30 feet across the room. This incident inspired Fish to turn the product into a toy.
And finally how it amusingly flumoxed the person of the toy company they presented it to:
Fish sprayed the can all over the person he was meeting with and all over his office. This person became very upset and asked him to leave the premises. One day later, Fish received a Western Union Telegram asking him to send 24 cans of "Squibbly" for a market test immediately, signed by the same individual who had kicked him out. He called them back and explained that, after he had finished cleaning up his office, the two owners of Wham-O had come back to talk to him, and one had noticed a piece of the string on a lamp shade – he had overlooked it while cleaning up. He explained where the string came from and the owners quickly asked him to send samples over for a market test. Two weeks later, Wham-O signed a contract with Fish and Cox to license the product now known as Silly String.
-
-
-
-
@pie_flavor
It can't be coincidence that letter is signed with a signature that looks like a stylized cock, no?
-
-
@pie_flavor TIL that Bic was making a bit of a fuss over it:
This letter is by no means an official document, this is just a forged document used for humoristic purposes by Internet users. The Bic Group is now trying to contact the transmitter website to ask them to point out that it is a fake and a joke and by no means an official document from the Bic company and, if necessary, to remove it from their website.
Yes, release the lawyers, that'll save your reputation...
-
TIL the biblical God used to have problems defeating iron chariots.
-
@Gąska said in TIL (about the Dark Arts of HTML):
TIL the biblical God used to have problems defeating iron chariots.
Well, the fey (fairies, etc) were also supposed to have problems with iron… so the logical conclusion (applying Occam's razor) is that the biblical God was a fey.
-
Today's SMBC has taught me:
-
TIL C# allows Unicode identifiers.
-
@Gąska did you expect Shift-JIS identifiers?
-
@pie_flavor no, Mr. Flavor, I expected you to die!
-
@pie_flavor said in TIL (about the Dark Arts of HTML):
@Gąska did you expect Shift-JIS identifiers?
No, he must have expected EBCDIC.
-
@Gąska said in TIL (about the Dark Arts of HTML):
I expected you to die!
One day, like everybody else
-
@Gąska said in TIL (about the Dark Arts of HTML):
@pie_flavor no, Mr. Flavor, I expected you to die!
Quick, bring the centrifuge!
-
@DogsB said in OOP is TRWTF:
Reminds me of HashMaps in java. When you pull iterators out of them you can't guarantee the order of the items. Everywhere I've worked I've had to fix a bug related that.
This post reminded me of something I learned yesterday
Changed in version 3.7: Dictionary order is guaranteed to be insertion order.
-
@anonymous234 We're looking forward to when we can get our users to use that as a minimum version.

-
@anonymous234 said in TIL (about the Dark Arts of HTML):
@DogsB said in OOP is TRWTF:
Reminds me of HashMaps in java. When you pull iterators out of them you can't guarantee the order of the items. Everywhere I've worked I've had to fix a bug related that.
This post reminded me of something I learned yesterday
Changed in version 3.7: Dictionary order is guaranteed to be insertion order.
 So they are complicating the dictionary—which is embedded deep in the foundation of everything—for the rare case where the order matters?
So they are complicating the dictionary—which is embedded deep in the foundation of everything—for the rare case where the order matters?What's happened to the ‘you don't pay for what you don't…’ oh, that was never a thing in Python in the first place…
-
@Bulb said in TIL (about the Dark Arts of HTML):
So they are complicating the dictionary—which is embedded deep in the foundation of everything—for the rare case where the order matters?
Well, CPython already did it that way. Most likely they just thought "who cares about other implementations lol".
-
@Bulb said in TIL (about the Dark Arts of HTML):
 So they are complicating the dictionary—which is embedded deep in the foundation of everything—for the rare case where the order matters?
So they are complicating the dictionary—which is embedded deep in the foundation of everything—for the rare case where the order matters?It apparently turns out that it's also faster on average.
-
-
@anonymous234 said in TIL (about the Dark Arts of HTML):
@DogsB said in OOP is TRWTF:
Reminds me of HashMaps in java. When you pull iterators out of them you can't guarantee the order of the items. Everywhere I've worked I've had to fix a bug related that.
This post reminded me of something I learned yesterday
Changed in version 3.7: Dictionary order is guaranteed to be insertion order.
Gah! My typo is following me.
-
TIL that a depressed cubic is not a downbeat dice.
And also, that the analytical formula to the roots of a cubic are a bit tricky to use in a symbolic equation.
-
@dkf said in TIL (about the Dark Arts of HTML):
@Bulb said in TIL (about the Dark Arts of HTML):
 So they are complicating the dictionary—which is embedded deep in the foundation of everything—for the rare case where the order matters?
So they are complicating the dictionary—which is embedded deep in the foundation of everything—for the rare case where the order matters?It apparently turns out that it's also faster on average.
How does that work though? Isn’t the storage order defined by the hash?
Do they need a second index which retains insertion order?
-
@topspin said in TIL (about the Dark Arts of HTML):
How does that work though? Isn’t the storage order defined by the hash?
Do they need a second index which retains insertion order?The way I've seen it done is to keep the entries also in doubly linked list that maintains the insertion order (at a memory cost of two pointers per entry). I've seen multiple implementations do it that way so, though I've not looked at Python's one, I'm pretty sure they're doing the same thing. Then operations that iterate over everything will use that linked list (insertions of new entries into it are cheap because they're always at the end), whereas other operations can use the hash table to go directly to what they're looking for.
I've no idea why that turns out to be a better implementation than what they were using before. It's possible that the issue there is that what they were using before was actually rather shit; that's entirely too easily done with hashing systems. The good thing about the insertion order is that it is non-random and not changed by rehashing so you also don't need anything like as much randomization in the hash function. (Some say you don't need any. Others disagree. It depends on primary use cases.)
-
@dkf said in TIL (about the Dark Arts of HTML):
The good thing about the insertion order is that it is non-random and not changed by rehashing so you also don't need anything like as much randomization in the hash function.
Randomization of hash function is usually sold as a defence against attacker forcing a slow-down or memory consumption increase¹ by carefully choosing keys that conflict. Since the other uses besides iteration are still affected, and since iteration wasn't affected by the attack in the first place, the need for randomization does not change.
¹ Most hashes are linked list or linear probing, where lookup grows to O(n²) when there are too many conflicts, but the memory consumption is still O(n), but there are other schemes like Cuckoo hashing that grows the table on double conflicts where the memory consumption grows instead (or both do when you force the very worst case).
-
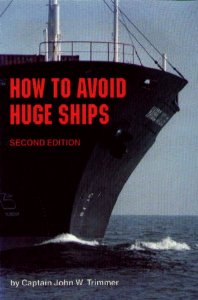
TIL "How to Avoid Huge Ships" is a serious guidebook for professionals, and not at all a silly parody.
-
-
@Gąska said in TIL (about the Dark Arts of HTML):
TIL "How to Avoid Huge Ships" is a serious guidebook for professionals, and not at all a silly parody.
Have you checked out the "Real books with weird titles" thread yet?
-
@JBert it's one thing to be real. It's another to be an in-depth technical instruction that's actually helpful.
-
@Bulb said in TIL (about the Dark Arts of HTML):
Most hashes are linked list or linear probing, where lookup grows to O(n²) when there are too many conflicts
You can make things resistant to that, but in the process you actually slow down the hashing. In use cases where the input values are non-adversarial (actually very common!) it's better to accelerate the hashing than to protect against evil edge cases. Java is relatively resistant to trouble in this area because it switches to hanging trees off the hash table bins instead of lists when the loading gets large enough, but there are definitely also use cases for keeping everything very simple to improve cache locality.
-
@dkf said in TIL (about the Dark Arts of HTML):
In use cases where the input values are non-adversarial (actually very common!) it's better to accelerate the hashing than to protect against evil edge cases.
… but most standard library implementations assume adversarial input these days, because common programmer won't remember to use any special variant when the values occasionally can be actually controlled by an adversary.
@dkf said in TIL (about the Dark Arts of HTML):
Java […] cache locality.
Those two things don't really go together.
-
@Bulb said in TIL (about the Dark Arts of HTML):
… but most standard library implementations assume adversarial input these days, because common programmer won't remember to use any special variant when the values occasionally can be actually controlled by an adversary.
Which is actually idiotic. It slows everything down for cases that are rare, and the best mitigations against adversaries (at least under common scenarios) are to stop them providing large numbers of keys in the first place. Providing strong mitigation for everyone is like telling everyone to carry around a large boat anchor while running sprint races “just in case you need to stop suddenly at sea”.





-
@dkf Here's a compromise: make the default version "safe", provide an explicitly "unsafe" version for those who think they're good enough to know the difference.
That won't stop some smart guys from using unsafe on everything and then getting pwnt anyway, but it will at least help the rest.Personally I'd make people pass an online exam before they can use the unsafe ones, but that's just me being a technofascist.
-
@anonymous234 Enjoy carrying around that
 just in case!
just in case!(In most cases, why allow an adversarial attacker the ability to pass enough keys in the first place for it to make a difference? Limit the total message size and message rate from each host and you stop most trouble.)
-
@anonymous234 said in TIL (about the Dark Arts of HTML):
Here's a compromise: make the default version "safe", provide an explicitly "unsafe" version for those who think they're good enough to know the difference.
That won't stop some smart guys from using unsafe on everything and then getting pwnt anywayBut it might at least stop those same smart guys from writing their own, half-assed, bug-riddled and insecure container implementation because "everyone knows the standard library hash map is slooow!"
@dkf said in TIL (about the Dark Arts of HTML):
Limit the total message size and message rate from each host and you stop most trouble.
Yeah, well, that would require some actual thinking.
-
AFDAIL that brown sugar doesn't really dissolve in tequila.
-
@Gąska said in TIL (about the Dark Arts of HTML):
@JBert it's one thing to be real. It's another to be an in-depth technical instruction that's actually helpful.
Certain ships of the US Navy would probably have done well to have this on board.
-
Apparently, Android doesn't accept power in USB host mode with one of these y-cables:

-
@hungrier said in TIL (about the Dark Arts of HTML):
Apparently, Android doesn't accept power in USB host mode with one of these y-cables:

Correct. USB Host Mode normally doesn't, even though technically there's no reason for it not to.
-
@Tsaukpaetra It doesn't even work without another USB device connected. I thought it would be a no-brainer to at least pass through the power, but it doesn't.
My e-reader readily accepts power with it, and the Playstation Classic does as well with a non-OTG firmware. It should work with an OTG firmware as well, since the people making the hacked firmwares know what's up
-
TIL YouTube has polls.
-
@Gąska said in TIL (about the Dark Arts of HTML):
TIL YouTube has polls.
Yes. A much more useful feature than in-video annotations, wouldn't you say?

-
TIL the TCP packet checksum is only 16 bits long, so a randomly corrupted packet still has a 1 in 65536 chance of going undetected.
To make things worse, the checksum is just the sum of all 16-bit chunks in the packet, meaning you can swap any two of them and it won't be detected.
-
@anonymous234 One in 65535. The value 0 is not used (I believe if 0 is computed, 1 is stored).
-
@anonymous234 said in TIL (about the Dark Arts of HTML):
TIL the TCP packet checksum is only 16 bits long, so a randomly corrupted packet still has a 1 in 65536 chance of going undetected.
I hope you didn't learn it during bug investigation.
-
@Gąska In that case, I expect IPSec adds cryptographic checksums? Note I haven't checked.
-
@dkf said in TIL (about the Dark Arts of HTML):
@mott555 said in TIL (about the Dark Arts of HTML):
Specifically, I found this interesting, regarding the moon Nix and the way it rotates:
Nix can flip its entire pole. It could actually be possible to spend a day on Nix in which the sun rises in the east and sets in the north. It is almost random-looking in the way it rotates.
I wonder if anyone's written on Tumblr about it…
I'd like to see them try and not have it be misidentified as porn.


 The Pirate Who Penned the First English-Language Guacamole Recipe
The Pirate Who Penned the First English-Language Guacamole Recipe