The Official Funny Stuff Thread™
-
@Zecc Working from home has a lot of advantages
-

-
@Benjamin-Hall Can confirm. (Hence turning on the radar beacon and mouse trails)
-
@TimeBandit said in The Official Funny Stuff Thread™:
@Zecc Working from home has a lot of advantages
...until you click the "share screen" button, one millisecond before remembering what your wallpaper looks like.
-
-
-

-
Pangeos Terayacht: An $8 Billion Engineering Disaster
-
@Benjamin-Hall I have this Corsair mouse that randomly loses connection. Well, sort of...the laser is still on but that's it. The cursor vanishes. I have to wait for two notifications, one that says USB recognized the device, whereupon the cursor reappears, and another that says a 3.0 port would be faster, whereupon the cursor actually moves again. So I usually just spin the mouse around until I see the cursor and get back to business.
God I need to learn soldering so I can fix the button in my Microsoft mouse.
-
@Zenith it’s kind of ironic that the only good things Microsoft has ever produced were mice and keyboards.

-
@Zenith said in The Official Funny Stuff Thread™:
another that says a 3.0 port would be faster
Maybe you move your mouse too quickly if you need a 3.0 port

-
@TimeBandit Who the fuck knows. All I know is this $50 gaming mouse would be a fucking disaster to play actual games with whether it's Counterstrike or Age of Empires.
-
-
-
-
-

-

-
@boomzilla But this month only has weekend remaining and after next month it's vacation month.
-
When you try to sneak out of work early but run into the boss
-
-
-
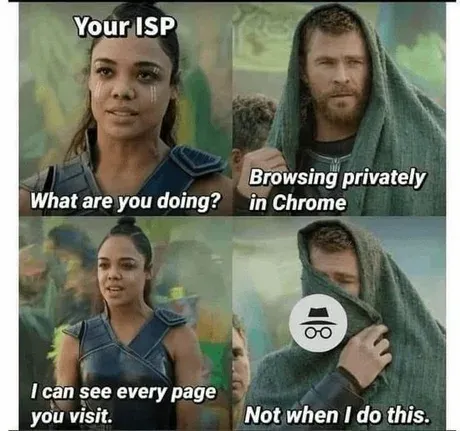
@error No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
Some people recommend VPNs but to me in this usecase that just feels like moving your data somewhere that's more likely to have nosy people.
-
@PleegWat said in The Official Funny Stuff Thread™:
No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
 I only use it to keep my local history and cache clean.
I only use it to keep my local history and cache clean.
-
@error said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
 I only use it to keep my local history and cache clean.
I only use it to keep my local history and cache clean.Combos with the tissue box that's to keep your keyboard clean

-

-
@izzion said in The Official Funny Stuff Thread™:
keep your keyboard clean
@error_bot xkcd optical illusion
-
xkcd said in https://xkcd.com/237/ :
Keyboards are Disgusting
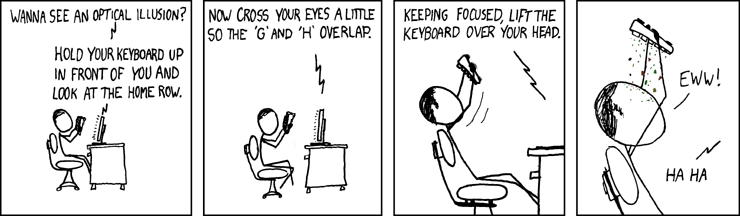
(via https://www.explainxkcd.com/wiki/index.php?search=optical+illusion&title=Special%3ASearch&fulltext=1)
-
-
@PleegWat said in The Official Funny Stuff Thread™:
@error No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
Some people recommend VPNs but to me in this usecase that just feels like moving your data somewhere that's more likely to have nosy people.
Exactly. Its like going "hey FBI, I'm doing shady shit over here". I would be really surprised if FBI/NSA didn't have backdoor and/or wire taps at most of the VPN endpoints.
-
@error How much cash do you think he carries in that utility belt?
...What? You think he'd pay with a card and risk his identity getting traced?
-
-
@acrow He's probably got his own bank through which he can special-issue a card.
-
@djls45 I don't think that would help, since the card would still have to be issued in someone's name. The way to make a card hard to trace rather is to set up some shell companies with hidden intermediaries abroad to hold the account.
-
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@error No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
Some people recommend VPNs but to me in this usecase that just feels like moving your data somewhere that's more likely to have nosy people.
Exactly. Its like going "hey FBI, I'm doing shady shit over here". I would be really surprised if FBI/NSA didn't have backdoor and/or wire taps at most of the VPN endpoints.
They don't really need them, they have legal rights to everything they want through the anti terrorism laws and the corporations they ask for the information can't say they've been asked for it. At least within US borders.
But they also control enough TOR nodes to track traffic through that network, so if you really want to be anonymous, you need to buy a second hand computer with cash, a second hand phone with cash, and a prepaid card with cash (and if you are not allowed to get one without using credentials, pay some kids to buy it for you I suppose). Then you do not bring any of this to anywhere you "normally" hang out even if it's turned off. Especially the phone. And you do not bring your normal gear with you when you want to use your anonymous gear.And even then, you'll probably be caught if what you're up to is interesting enough for the TLAs.
-
@djls45 This wouldn't work, unfortunately, as the bank would be just one step in the paper and money trail. Both of which can be followed backwards to whomever gave the order. That is, Wayne himself. But wait, there is a better way, if you'll bear with me a moment.
I actually liked how they explain Batman's hiding the manufacturing of his equipment by mixing it with the Wayne Enterprises R&D department's orders in the new movies. Also, like Alfred said about the mask: "Order one, and there's all kinds of scrutiny. Order 10,000 and no-one bats an eye." (IIRC)
Once a company orders the physical components to an internal warehouse, or better yet to a lab, their final fate is completely up to the company employees, and tracking their use from the outside is essentially impossible.I work for a fairly small company, and we order €50k-€100k worth of parts for R&D every year. Some of it spends years as prototypes. Some are used to emergency-modify shelf-products and end up on a customer site for years. Some are consumed and end up on the trash heap in a couple of weeks. Some are tools, or are made into company-internal tools and equipment. If government wanted to conclusively figure out whether we were doing something secret without asking us, they'd have to sort through our trash resistor-by-resistor for years and would probably still come up as "inconclusive".
Anyways, the Batmobile is probably listed as a forklift somewhere in Wayne Enterprises ledgers to fudge the fuel and tyre orders. To finish with a joke.
-
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@error No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
Some people recommend VPNs but to me in this usecase that just feels like moving your data somewhere that's more likely to have nosy people.
Exactly. Its like going "hey FBI, I'm doing shady shit over here". I would be really surprised if FBI/NSA didn't have backdoor and/or wire taps at most of the VPN endpoints.
Yeah. For that reason, if you want to use VPN to hide your stuff from dodgy wifi, it's probably best to run an endpoint at home. Or use your work's, if it's for work purposes.
-
@acrow said in The Official Funny Stuff Thread™:
I work for a fairly small company, and we order €50k-€100k worth of parts for R&D every year. Some of it spends years as prototypes. Some are used to emergency-modify shelf-products and end up on a customer site for years. Some are consumed and end up on the trash heap in a couple of weeks. Some are tools, or are made into company-internal tools and equipment. Some end up in personal projects of people working in R&D, but if you ask them, they'll deny it.

-
@Zerosquare said in The Official Funny Stuff Thread™:
@acrow said in The Official Funny Stuff Thread™:
I work for a fairly small company, and we order €50k-€100k worth of parts for R&D every year. Some of it spends years as prototypes. Some are used to emergency-modify shelf-products and end up on a customer site for years. Some are consumed and end up on the trash heap in a couple of weeks. Some are tools, or are made into company-internal tools and equipment. Some end up in personal projects of people working in R&D, but if you ask them, they'll deny it.

 Do you have any idea how much it saves in both the training and R&R activity budgets? These people self-train, in their own time, and it costs way less than courses do. We still get the benefit of their new skills. And they consider it recreational, too, so we can skimp on the company cruises. It's a win-win.
Do you have any idea how much it saves in both the training and R&R activity budgets? These people self-train, in their own time, and it costs way less than courses do. We still get the benefit of their new skills. And they consider it recreational, too, so we can skimp on the company cruises. It's a win-win.
-
@acrow said in The Official Funny Stuff Thread™:
@Zerosquare said in The Official Funny Stuff Thread™:
@acrow said in The Official Funny Stuff Thread™:
I work for a fairly small company, and we order €50k-€100k worth of parts for R&D every year. Some of it spends years as prototypes. Some are used to emergency-modify shelf-products and end up on a customer site for years. Some are consumed and end up on the trash heap in a couple of weeks. Some are tools, or are made into company-internal tools and equipment. Some end up in personal projects of people working in R&D, but if you ask them, they'll deny it.

 Do you have any idea how much it saves in both the training and R&R activity budgets? These people self-train, in their own time, and it costs way less than courses do. We still get the benefit of their new skills. And they consider it recreational, too, so we can skimp on the company cruises. It's a win-win.
Do you have any idea how much it saves in both the training and R&R activity budgets? These people self-train, in their own time, and it costs way less than courses do. We still get the benefit of their new skills. And they consider it recreational, too, so we can skimp on the company cruises. It's a win-win.Gah, hanzoed me, but I would like to throw in: if the company can prove it was their resources, then they can claim the idea is theirs.
Reminds me of a friend of mine who worked at AWS. They would have prizes for employees that submitted good ideas. Little gold, silver and bronze trinkets and special platinum ones for when an idea was implemented. Employees were delighted to receive them. Never fucking occurred to them that Amazon was generating millions in lieu of painted trinkets.
-
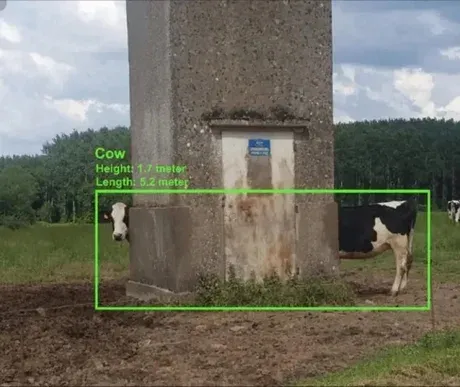
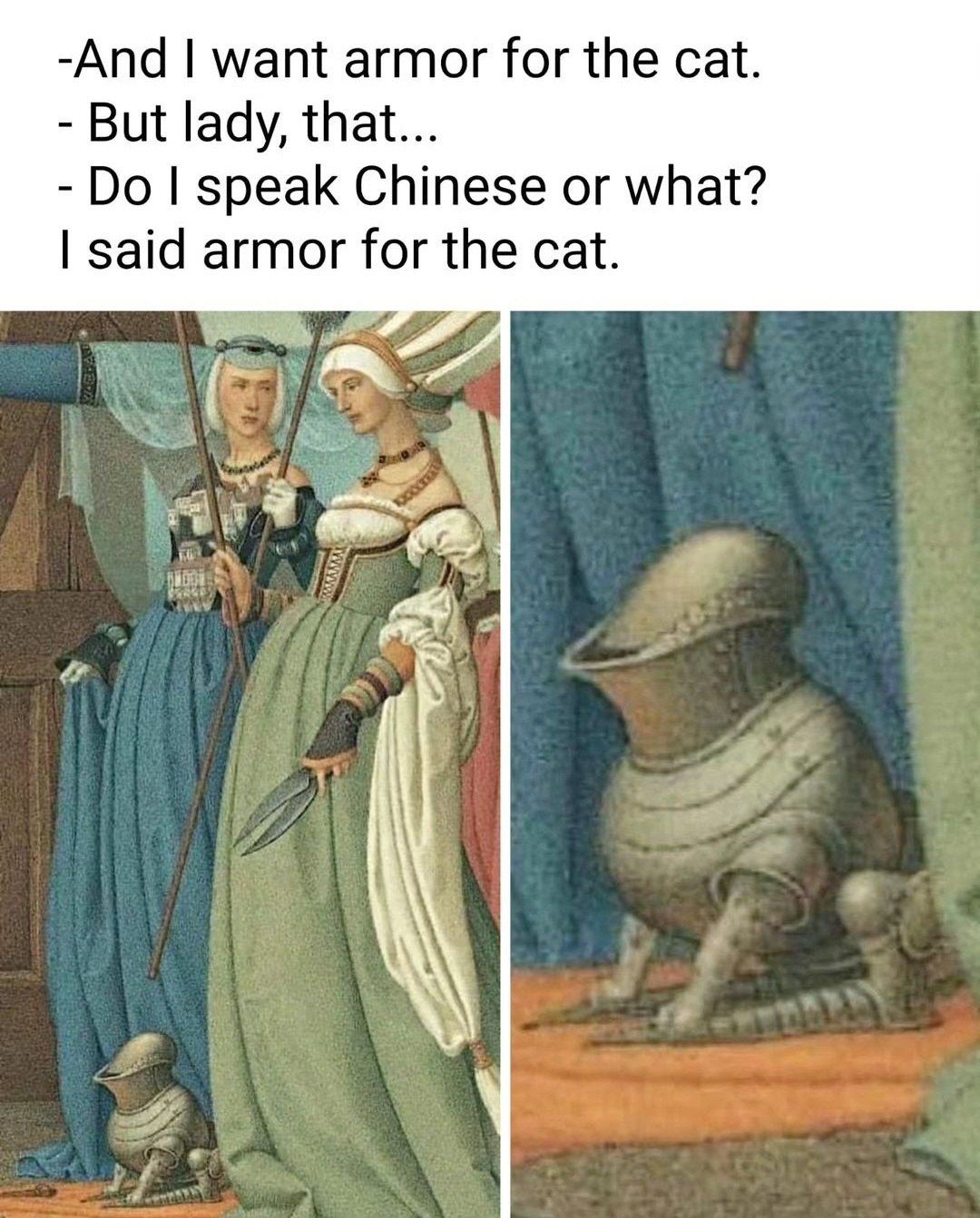
@Bulb said in The Official Funny Stuff Thread™:
@Gern_Blaanston said in The Official Funny Stuff Thread™:
I'm fairly confident it's a dog though.

-
@PleegWat said in The Official Funny Stuff Thread™:
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@error No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
Some people recommend VPNs but to me in this usecase that just feels like moving your data somewhere that's more likely to have nosy people.
Exactly. Its like going "hey FBI, I'm doing shady shit over here". I would be really surprised if FBI/NSA didn't have backdoor and/or wire taps at most of the VPN endpoints.
Yeah. For that reason, if you want to use VPN to hide your stuff from dodgy wifi, it's probably best to run an endpoint at home. Or use your work's, if it's for work purposes.
I'm always confused about people talking about dodgy wifi. Let's say I'm in a starbucks and some guy set up an ARP spoofer, and I go to my bank and login. Sure, all my traffic is routed through the hackers PC, and he can see that I looked up bank.com in the DNS, but unless I ignore the certificate warning, or some idiot anti-virus software does it for me, what is the risk exactly?
-
@dangeRuss It offers a way for the attacker to become a man in the middle. That by itself is not a full attack, but it removes a layer of defense.
-
@PleegWat said in The Official Funny Stuff Thread™:
@dangeRuss It offers a way for the attacker to become a man in the middle. That by itself is not a full attack, but it removes a layer of defense.
Right but without being able to decrypt https traffic, what's the point?
-
@acrow said in The Official Funny Stuff Thread™:
@error How much cash do you think he carries in that utility belt?
...What? You think he'd pay with a card and risk his identity getting traced?
Mugging Batman goes in the Bad Ideas Thread.
-
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@dangeRuss It offers a way for the attacker to become a man in the middle. That by itself is not a full attack, but it removes a layer of defense.
Right but without being able to decrypt https traffic, what's the point?
Downgrade attacks were funny for a while but have gone out of vogue. You should be able to replay the packets in your own browser and then pick up from the victim left off. There's also the curious case of personal information in the url.
There are countermeasures that are a pain in the hole if you have a VPN. If you're seeing multiple cloudflare bot checks while on a train around the country or after turning off and on the VPN, that's what you're looking at.
-
@error said in The Official Funny Stuff Thread™:
@acrow said in The Official Funny Stuff Thread™:
@error How much cash do you think he carries in that utility belt?
...What? You think he'd pay with a card and risk his identity getting traced?
Mugging Batman goes in the Bad Ideas Thread.
And deprive us of content for this thread?
 Much shame.
Much shame.
-
-
-
@DogsB said in The Official Funny Stuff Thread™:
There's also the curious case of personal information in the url.
AIUI middle-men shouldn't see the URL. At most, only the domain name being resolved followed by a TLS connection to that IP being created.