The Official Funny Stuff Thread™
-
-
@Zecc said in The Official Funny Stuff Thread™:
@DogsB said in The Official Funny Stuff Thread™:
There's also the curious case of personal information in the url.
AIUI middle-men shouldn't see the URL.
Except for the various ways that they can by pretending to be a proxy of some sort.
-
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@dangeRuss It offers a way for the attacker to become a man in the middle. That by itself is not a full attack, but it removes a layer of defense.
Right but without being able to decrypt https traffic, what's the point?
A lot of stuff is not encrypted and there is quite a bit you can learn about someone from their unencrypted information.
Additionally, most people don't pay attention to cert errors on anything (a few pay attention to it on important sites). So they can get plenty out of phishing sites.
It is not uncommon for targeted attacks to read through all your social media to better attack you, this can give them more information for an even better attack.
-

-
@topspin said in The Official Funny Stuff Thread™:
@Zenith it’s kind of ironic that the only good things Microsoft has ever produced were mice and keyboards.

But they no longer make the best keyboard... the 4000. (the 'v' key decided to die while doing some heavy copy/paste)
-
@dcon Mine still works fine. (At least everything that matters still works. One of the single-key equivalents of Alt+
 /
/ doesn't, but obviously there are both keyboard and mouse equivalents.) I can't read half the keycaps, and the vinyl on the wrist/palm pad has all worn off, but it still works. The problem is that I want 4000s for my other computers, too, but I can't get them without paying 10x the original price.
doesn't, but obviously there are both keyboard and mouse equivalents.) I can't read half the keycaps, and the vinyl on the wrist/palm pad has all worn off, but it still works. The problem is that I want 4000s for my other computers, too, but I can't get them without paying 10x the original price.
-
@HardwareGeek said in The Official Funny Stuff Thread™:
I can't read half the keycaps
Same. I still have one left... on the desktop computer. For now, I'm reduced to using the work laptop's keyboard. Which, of course, means I get to randomly have the touchpad activate and "something happens".
Funny foof:
-
When you have the best dog, you have to take him for a walk so you can show him off.
-
@Dragoon said in The Official Funny Stuff Thread™:
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@dangeRuss It offers a way for the attacker to become a man in the middle. That by itself is not a full attack, but it removes a layer of defense.
Right but without being able to decrypt https traffic, what's the point?
A lot of stuff is not encrypted and there is quite a bit you can learn about someone from their unencrypted information.
Additionally, most people don't pay attention to cert errors on anything (a few pay attention to it on important sites). So they can get plenty out of phishing sites.
It is not uncommon for targeted attacks to read through all your social media to better attack you, this can give them more information for an even better attack.
Like what? Most sites require https, what else wouldn't be encrypted? The proxy is an interesting one, but I don't think that would really work. And while most people might ignore cert errors, I'm not one of them, and browsers have made it really hard to bypass those lately.
I've actually studied computer security and done labs on WEP cracking, MITM, buffer overflow privilege escalation, etc, so I'm pretty familiar with everything, and iust a little confused about all this panic.
-
-
@Tsaukpaetra said in The Official Funny Stuff Thread™:
@dangeRuss said in The Official Funny Stuff Thread™:
panic
panic = profit
True, but wanted to see what you, properly informed people had to say.
-
-
@dangeRuss said in The Official Funny Stuff Thread™:
@Dragoon said in The Official Funny Stuff Thread™:
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@dangeRuss It offers a way for the attacker to become a man in the middle. That by itself is not a full attack, but it removes a layer of defense.
Right but without being able to decrypt https traffic, what's the point?
A lot of stuff is not encrypted and there is quite a bit you can learn about someone from their unencrypted information.
Additionally, most people don't pay attention to cert errors on anything (a few pay attention to it on important sites). So they can get plenty out of phishing sites.
It is not uncommon for targeted attacks to read through all your social media to better attack you, this can give them more information for an even better attack.
Like what? Most sites require https, what else wouldn't be encrypted? The proxy is an interesting one, but I don't think that would really work. And while most people might ignore cert errors, I'm not one of them, and browsers have made it really hard to bypass those lately.
I've actually studied computer security and done labs on WEP cracking, MITM, buffer overflow privilege escalation, etc, so I'm pretty familiar with everything, and iust a little confused about all this panic.
Well, some of it is certainly from old information. It was a serious threat 10ish years ago. It still is, under the right circumstances. Which are becoming rarer in first world countries but are still prevalent in other regions.
So as is always the case, somebody that knows about the issue suggests some level of caution and when that finally gets to grandmas ear it is the biggest threat ever imagined and you should never trust wifi in a public space.
-
@Dragoon said in The Official Funny Stuff Thread™:
@dangeRuss said in The Official Funny Stuff Thread™:
@Dragoon said in The Official Funny Stuff Thread™:
@dangeRuss said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@dangeRuss It offers a way for the attacker to become a man in the middle. That by itself is not a full attack, but it removes a layer of defense.
Right but without being able to decrypt https traffic, what's the point?
A lot of stuff is not encrypted and there is quite a bit you can learn about someone from their unencrypted information.
Additionally, most people don't pay attention to cert errors on anything (a few pay attention to it on important sites). So they can get plenty out of phishing sites.
It is not uncommon for targeted attacks to read through all your social media to better attack you, this can give them more information for an even better attack.
Like what? Most sites require https, what else wouldn't be encrypted? The proxy is an interesting one, but I don't think that would really work. And while most people might ignore cert errors, I'm not one of them, and browsers have made it really hard to bypass those lately.
I've actually studied computer security and done labs on WEP cracking, MITM, buffer overflow privilege escalation, etc, so I'm pretty familiar with everything, and iust a little confused about all this panic.
Well, some of it is certainly from old information. It was a serious threat 10ish years ago. It still is, under the right circumstances. Which are becoming rarer in first world countries but are still prevalent in other regions.
So as is always the case, somebody that knows about the issue suggests some level of caution and when that finally gets to grandmas ear it is the biggest threat ever imagined and you should never trust wifi in a public space.
I also wouldn't be surprised if some brain dead anti-virus software that does MITM to be able to "protect you" from web threats actually ignored the invalid certs.
-
It used to be easy to get certificates from trusted CAs, but I'm fairly certain it's less easy these days. Probably still not a huge problem to do, but not worth the slim pickings of a random public wifi. Specific public wifi with a high ratio of juicy targets, maybe.
And adding self signed certs to the trust store should not be possible barring some exploit, since that'd entirely invalidate the whole idea of trust stores.Attacks like SSLstrip could possibly help here, but then you are actively downgrading the client to HTTP, and that should possibly be something to be wary of. There are also tools for bypassing HSTS with SSLstrip attacks, so if there is a MiTM they can do some naughty things to you. Especially if your browser is hiding the https:// part of the url. Modern browsers do their best to prevent these shenanigans though.
-
@PleegWat said in The Official Funny Stuff Thread™:
@error No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
And DNS-over-HTTPS to some privacy-conscious service so as not to leak your domain names.
-
@LaoC said in The Official Funny Stuff Thread™:
DNS-over-HTTPS
DNS-over-HTTPS does not necessarily solve anything here, since at least traditionally the network you are connecting to will tell you which DNS server to use via DHCP.
@Carnage said in The Official Funny Stuff Thread™:
tools for bypassing HSTS
I read an article recently about the newly proposed HTTPS record type in DNS. This would declare the fact a URL uses HTTPS directly in the DNS record, communicating encryption preference before the client even connects to the server, as well as allowing better control over the lifetime of these announcements. Naturally this would require DNS records to be appropriately signed, to prevent tampering by a man-in-the-middle.
-

-
@LaoC said in The Official Funny Stuff Thread™:
@PleegWat said in The Official Funny Stuff Thread™:
@error No, private mode is for masking what the website owner sees. For masking from your ISP you use TLS.
And DNS-over-HTTPS to some privacy-conscious service so as not to leak your domain names.
You also need to use ESNI, but half the world still does not support TLS1.3, so you can't, or can't most of the time.
-
@PleegWat said in The Official Funny Stuff Thread™:
@LaoC said in The Official Funny Stuff Thread™:
DNS-over-HTTPS
DNS-over-HTTPS does not necessarily solve anything here, since at least traditionally the network you are connecting to will tell you which DNS server to use via DHCP.
Obviously. Which is why I didn't end my sentence there.
@Carnage said in The Official Funny Stuff Thread™:
tools for bypassing HSTS
I read an article recently about the newly proposed HTTPS record type in DNS. This would declare the fact a URL uses HTTPS directly in the DNS record, communicating encryption preference before the client even connects to the server, as well as allowing better control over the lifetime of these announcements. Naturally this would require DNS records to be appropriately signed, to prevent tampering by a man-in-the-middle.
DANE is 12 years old and works for everything that uses TLS. I used to have some TLSA records for a mail server but few systems actually use them so for the last two years or so I haven't bothered.
-
-

-
-
....

-
-
@Gern_Blaanston said in The Official Funny Stuff Thread™:
....

-
When people drop in unexpectedly
-
....

-
If you ever feel powerless, just remember:
A single one of your pubic hairs can shut down an entire restaurant.
-

-
@Gern_Blaanston said in The Official Funny Stuff Thread™:
....

She's looking very Brittish in that photo.
-
@Carnage
init? right on love!
-

-
SICKERS
NICKERS
-
-

-
-

-
-
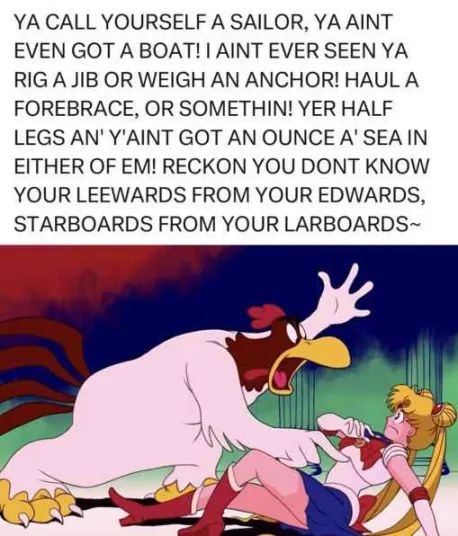
@izzion said in The Official Funny Stuff Thread™:
@Mason_Wheeler's meme said:
Starboards from your larboards
shudders in o11s
I'm not sure what you mean by “o11s” and going ducks ain't helpin'…
Anyway, and under risk of
 ing, larboard is a legitimate antonym to starboard, though port is preferred because it does not sound similar.
ing, larboard is a legitimate antonym to starboard, though port is preferred because it does not sound similar.Leewards from Edwards on the other hand …
-
America's Airborne Beavers - Operation Beaver Drop
-
@Bulb said in The Official Funny Stuff Thread™:
America's Airborne Beavers - Operation Beaver Drop
Awesome
-
@Bulb said in The Official Funny Stuff Thread™:
America's Airborne Beavers - Operation Beaver Drop
Maxim 11: Everything is air-droppable at least once.
-
@Mason_Wheeler DB Cooper, if he reads this, may want to disagree.
-
@da-Doctah said in The Official Funny Stuff Thread™:
@Mason_Wheeler DB Cooper, if he reads this, may want to disagree.
DB Cooper was only air-dropped once.
-
@hungrier said in The Official Funny Stuff Thread™:

Btw, Wikipedia has an article about it (only in moon language available):
-
Work smarter, not harder
-
@Gern_Blaanston said in The Official Funny Stuff Thread™:
@da-Doctah said in The Official Funny Stuff Thread™:
@Mason_Wheeler DB Cooper, if he reads this, may want to disagree.
DB Cooper was only air-dropped once.
Actually it seems he jumped twice. There was another similar hijacking half a year later or so and it was almost certainly him again, trying once more after he failed to hold on to the money in the first attempt.
There is a reconstruction showing it was not possible (and all the rest of the story) (and the second part on how FBI killed him after another crime (though they didn't know it was the same guy)).
-

-

Uhm, AliExpress, I don't think burning people's stomachs with a laser cutter counts as "repair".
 Guericke-Einhorn – Wikipedia
Guericke-Einhorn – Wikipedia