WTF Bites
-
@sebastian-galczynski I’m sure it does translate to functionality, just none you want or care about. But it presumably has functionality nonetheless.
Just think of the attack surface...

-
-
But it presumably has functionality nonetheless.

_Something_has to weigh down the spinny rust to ensure correct momentum, right?
-
But it presumably has functionality nonetheless.
If "being a large bulk of code that you never use" is functionality, then sure.
-
@dkf well, all those dependencies presumably do something, otherwise they wouldn’t be included. So it is functionality, just not in use because the JS ecosystem is a mess.
No one made any claims about usefulness of said functionality.
-
@Arantor It could be things like stacked polyfills all trying to fix the same thing, except it's been fixed in the runtime you're using anyway. Or some spare copies of node for shits and giggles.
-
@Arantor It could be things like stacked polyfills all trying to fix the same thing, except it's been fixed in the runtime you're using anyway. Or some spare copies of node for shits and giggles.
You also have an entire library in the
node_modulesdirectory but not all of that makes it into the build when you don't use it, at least in theory. I'm sure that mileage varies greatly there, but I have anode_modulesthat weighs in a 678MB but builds down to less than 7MB. Of course, the modules also often have regular code plus minimized versions, etc, etc, etc.
 , etc
, etc
-
@sebastian-galczynski I’m sure it does translate to functionality, just none you want or care about. But it presumably has functionality nonetheless.
Spyware, mostly.
-
WTF of my day: So, my bank offers to import financial data from other bank to get a general overview over all accounts in one place. That had been made possible in a safe way about two or three years back (before that was only possible through web scrapers).
Basically, you select your bank and then hand over your username and password (but not a 2FA token!).
Well, let's just say I'll reconsider trying that service. Because, y'see, when creating the password for the other account I used a password generator - 16 characters, special chars and so on.
And I have the strong feeling that their form does not deal well with special characters. Two signs of that:
a) If I enter the password and click on "continue", nothing happens. But the developer console shows an error related to the click.
b) I then used their contact form to write them about that problem. And the text area where you're supposed to enter your message yells at you if you use special characters (like an").My message to them included some pithy comments on the ineptitude of developers who still can't deal with SQL insertions without resorting to whitelists. Well, could also be cargo cult.
-
@sebastian-galczynski I’m sure it does translate to functionality, just none you want or care about. But it presumably has functionality nonetheless.
SpywareTelemetry, mostly.
-
@BernieTheBernie <insert the “they’re the same picture” meme from The Office>
-
Spyware, mostly.
It doesn't even have spyware, it's just a boring corprate CRUD app.
-
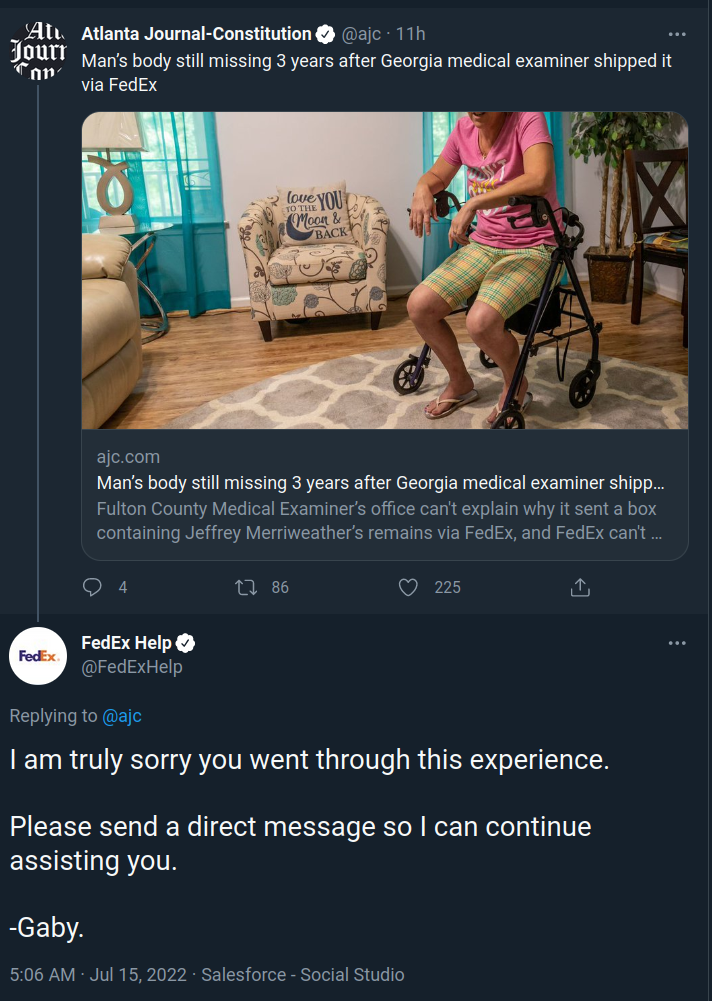
Salesforce is like the Electric Monk, only the monk believes in all kinds of stuff that you don't want to believe in yourself, and Salesforce is sorry for you when you have so much to be sorry about that hiring staff that could at least act sorry for it would be too expensive.
-
Salesforce is like the Electric Monk
In the sense that neither of them are FedEx?
-
@loopback0 said in WTF Bites:
In the sense that neither of them are FedEx?
How do you know that for sure?
-
@loopback0 said in WTF Bites:
Salesforce is like the Electric Monk
In the sense that neither of them are FedEx?
-
@LaoC Oh, right. My bad.
-
As if JavaScript wasn't bad enough. Now instead of running JavaScript in your browser, you compile a whole javascript engine into webasm, which then gets executed by your browser's engine, to run JavaScript.
 And I assume this isn't just a Doom inside Doom joke.
And I assume this isn't just a Doom inside Doom joke.What the fuck is wrong with these people?!
-
@topspin But has anybody tried to compile the webasm runtime to webasm yet?
(Rhetoric question. No need to answer. I'm happier not knowing for sure.)
-
What the fuck is wrong with these people?!
Real programming languages are too hard so they made do.
-
What the fuck is wrong with these people?!
Real programming languages are too hard so they made do.
Yeah, but now they can write JavaScript instead of … drum roll … JavaScript.
-
@topspin no, they can write super mega awesomely mucho faster JavaScript because WebAsm.
At least in their head.
-
What the fuck is wrong with these people?!
Real programming languages are too hard so they made do.
Making sure the Front Page has content for years to come...
-
Real programming languages are too hard so they made do.
Making sure the Front Page has content for years to come...
 About a half of the Front Page content is about C#
About a half of the Front Page content is about C#

-
What the fuck is wrong with these people?!
Real programming languages are too hard so they made do.
Making sure the Front Page has content for years to come...
The what?
Filed under: Obligatory
-
@Applied-Mediocrity I don't know how much of that is obfuscation by way of Inedo, though.
But it's also true enough that C# is in the kinds of places where you get lots of engineers and that means lots of varying skill levels.
I'm sure if you dug into my code you'd find some too - but you'd have to be, basically, me because there's only half a dozen other people total worldwide with access to some of the repos.
-
@loopback0 the mythical legend that begat this place.
-
@Arantor Varying skill levels and, perhaps, the nature of ASP.NET. Since it's not compiled (well, it is, but not by you), it can result into churning it and mashing F5 "until morale improves" practices, often directly in prod. Which is my one chief complaint against all [web-]scripting languages.
Now then, you have inspired me with your honesty, so I'll admit that, since C# compiles very fast, I've been known to do that with compiled programs, too. To dig into my code, you'll have to access a poorly secured FTP server, though.
-
@Applied-Mediocrity I mean, I'm in PHP land so guaranteed there's going to be some awfulness there, but I also recognise that I've had to do my fair share of ass-pull solutions for everyone else's shit over the years and just doubled down on it. And I'm positive I've made bad decisions that I've learned from.
I think that's the difference though: we have some understanding that there is a wrong way to do it and 'just until it works' isn't the highest bar to clear, and we can usually recognise bad habits waiting to happen and try to stop them before they do.
But I've certainly worked with programmers who genuinely have no idea, and are demonstrably doing it wrong, even when they have set themselves up with all the best will in the world.
-
What the fuck is wrong with these people?!
Real programming languages are too hard so they made do.
That sort of thing shouldn't be allowed to escape one's Personal Home Page.
-
UEFI (and its handling by the linux world) keeps on giving.
Time to update kernel. Kernel updated, reboot. WTF? Why is there only the old kernel in GRUB?
Run grub-install, reboot
Empty grub prompt. &^$%$*$&$&$&
boot from pendrive, mount everything, chroot, reinstall grub
Only old kernel againEventually I looked more closely at the output of
df. Somehow Debian's installer didn't add the /boot partition to fstab (but it did add /boot/efi). I've been installing the new kernel into an invisible directory on the encrypted root filesystem, while the correct destination stayed untouched. Somehow grub-install didn't notice that the grub.cfg is on an unreachable (by grub) partition encrypted with luks2.
-
@sebastian-galczynski said in WTF Bites:
invisible directory
Yeah that's the fun thing about requiring an existing directory to point the Mount to. If it fails, there's no way for a script that's just looking to see if the folder exists to know about it.
-
-
@BernieTheBernie
In Polish, "grub" is pronounced the same as "grób", which means "grave". Not sure what's better.
-
@sebastian-galczynski The polish word is obviously derived from german "Grube" (pit, hole; sometimes also used with the meaning of grave).
Anyways, make sure you feed your linux grub well, so as it can develop into a wonderful bug!

-
@BernieTheBernie said in WTF Bites:
@sebastian-galczynski The polish word is obviously derived from german "Grube" (pit, hole; sometimes also used with the meaning of grave).
 both goes straight up to PIE, with almost no change over millenia (*ghrebh- or *gʰrobʰos).
both goes straight up to PIE, with almost no change over millenia (*ghrebh- or *gʰrobʰos).
-
@Kamil-Podlesak said in WTF Bites:
@BernieTheBernie said in WTF Bites:
@sebastian-galczynski The polish word is obviously derived from german "Grube" (pit, hole; sometimes also used with the meaning of grave).
 both goes straight up to PIE, with almost no change over millenia (*ghrebh- or *gʰrobʰos).
both goes straight up to PIE, with almost no change over millenia (*ghrebh- or *gʰrobʰos).Phew, you stopped a German invasion.
-
I've been binge watching through The Firm TV series on Amazon Prime
The key piece of evidence at the apex of the plot is quite the "realistic" evidence
- After having found and lost many pieces of evidence, the hero's team has to stage a daring raid on the bad guy's law firm
- To access a SCIF that's protected by a keypad with an 8 digit TOTP that only two people they know of have the security token, they use peanut oil to incapacitate the big bad guy (who they know is severely allergic, and they stole his epi pen from him first)
- At which point the other part of the team gets into the SCIF only to discover that the super secret computer with all the incriminating evidence on it does not, in fact, have an accessible USB port
- So they call their paroled felon Russian hacker friend, show him a few pictures, and the hacker's like "oh yeah, just search for a number you know is incriminating and see which drive blinks"
- Which drive? Well, there's 10 of them, just there in the server that's embedded in the wall like a Dogs Playing Poker picture
- And they do their search and just one drive light blinks. So the Russian hacker is all "just rip that drive out and take it with you"
- Russian hacker gets his hands on it and is all like "well, there's military grade encryption on it, it might take a little bit to crack"
- Within a day he's all "well, I haven't cracked it yet but there's some files on it that look like some kind of formula"
- And as the plot develops, the bad guy is super worried about the feds getting the drive because they can crack it in a few hours.
Someone needs to teach the big bad guy and his tech team how to set up a RAID. And maybe invest in a server cabinet or two. Oh, and use standard off the shelf encryption with its recommended settings so that maybe the feds can't casually crack the encryption on your drives that should be unreadable on their own anyway.
-
-
-
I've been binge watching through The Firm TV series on Amazon Prime
The key piece of evidence at the apex of the plot is quite the "realistic" evidence
- After having found and lost many pieces of evidence, the hero's team has to stage a daring raid on the bad guy's law firm
- To access a SCIF that's protected by a keypad with an 8 digit TOTP that only two people they know of have the security token, they use peanut oil to incapacitate the big bad guy (who they know is severely allergic, and they stole his epi pen from him first)
- At which point the other part of the team gets into the SCIF only to discover that the super secret computer with all the incriminating evidence on it does not, in fact, have an accessible USB port
- So they call their paroled felon Russian hacker friend, show him a few pictures, and the hacker's like "oh yeah, just search for a number you know is incriminating and see which drive blinks"
- Which drive? Well, there's 10 of them, just there in the server that's embedded in the wall like a Dogs Playing Poker picture
- And they do their search and just one drive light blinks. So the Russian hacker is all "just rip that drive out and take it with you"
- Russian hacker gets his hands on it and is all like "well, there's military grade encryption on it, it might take a little bit to crack"
- Within a day he's all "well, I haven't cracked it yet but there's some files on it that look like some kind of formula"
- And as the plot develops, the bad guy is super worried about the feds getting the drive because they can crack it in a few hours.
Someone needs to teach the big bad guy and his tech team how to set up a RAID. And maybe invest in a server cabinet or two. Oh, and use standard off the shelf encryption with its recommended settings so that maybe the feds can't casually crack the encryption on your drives that should be unreadable on their own anyway.
I see the era of realistic hacking on tv is upon us.
-
@MrL super accurate technical stuff has been in the police procedural show for years.
I give you:
-
@MrL super accurate technical stuff has been in the police procedural show for years.
I give you:
Nice, I didn't know that one.
[insert obligatory NCIS duo hacking clip]
-
insert obligatory NCIS duo hacking clip
 It's called "Two Idiots One Keyboard"
It's called "Two Idiots One Keyboard"
-
insert obligatory NCIS duo hacking clip
 It's called "Two Idiots One Keyboard"
It's called "Two Idiots One Keyboard"OMG I didn't ask for help.
-
@MrL the other genius clip in NCIS is when Abby is all “we’re being hacked” and Gibbs just unplugs the computer as though she’s not on a terminal connected to a server but on the server itself.
May even be the same scene now that I think about it.
-
@Arantor That is the same scene. The two idiots are hacking on one keyboard, and the other guy walks in eating a sandwich or something and unplugs them
-
@hungrier it has been a long time since I watched NCIS (main series) while it was still watchable but season by season the good characters left and so did I. (It might be a stupid show but it’s easy in the brain)
-
@Arantor That is the same scene. The two idiots are hacking on one keyboard, and the other guy walks in eating a sandwich or something and unplugs them
A friend of mine has a kid who learned what typing was from that scene, and then got to play on HackerTyper and now... wants to "hack" along when they are typing. Bahaha.
-
there's military grade encryption on it
AKA triple-ROT13
13Lis a 64-bit seed... that's 2^24 times stronger than bank-grade.


