In other news today...
-
@TimeBandit said in In other news today...:
We already have one
-
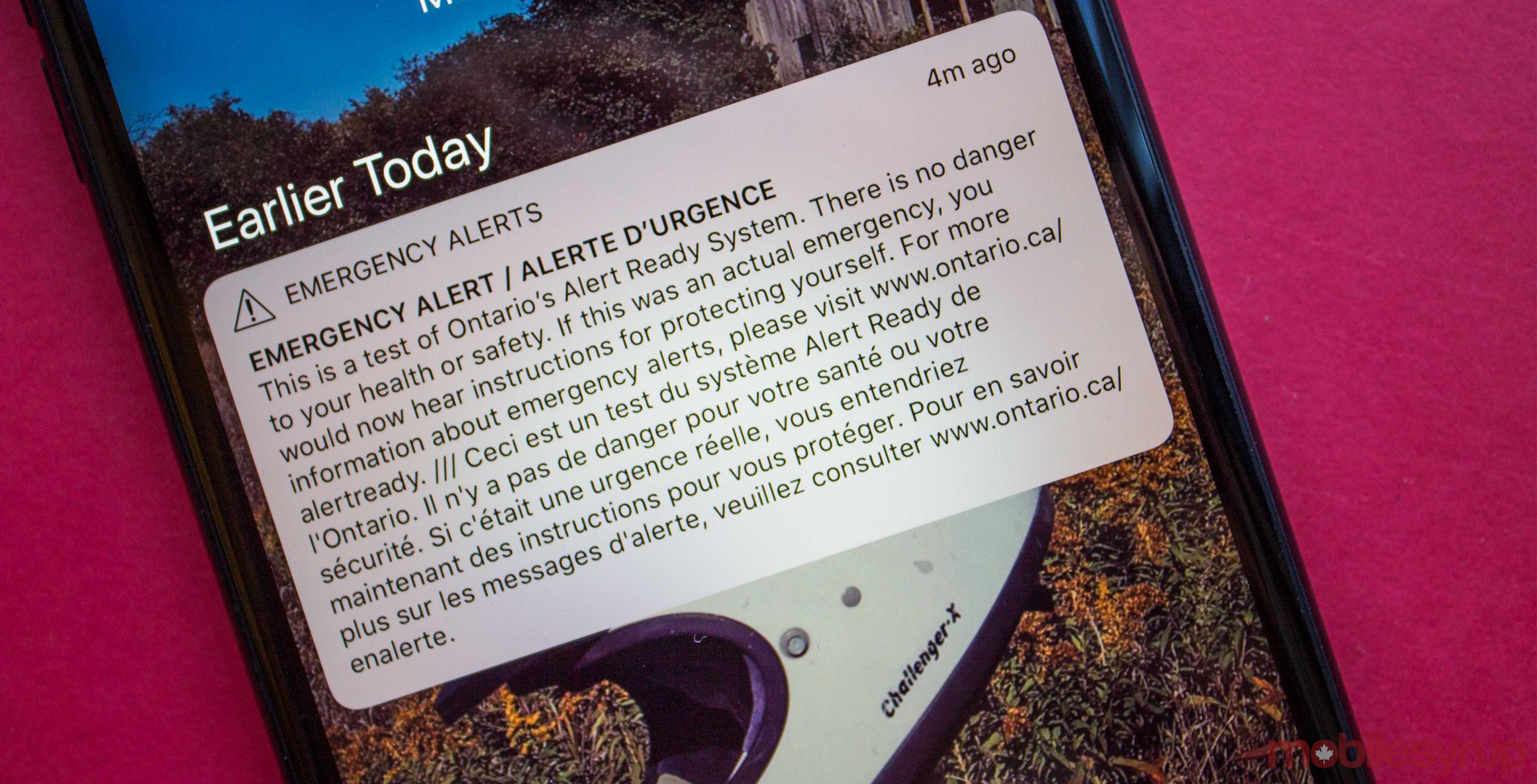
TLDR: Something, or maybe nothing, happened at a nuclear plant early Sunday morning and a scary emergency alert was sent out to the public all over Ontario, and reportedly parts of Quebec. Another alert was sent later retracting it, and there's no graphite on the ground or radiation levels above 3.6 roentgens.
Anyway, after they investigate the mystery of who fat-fingered the alert broadcast, I wish they would investigate the different levels that the emergency alert system offers instead of putting everything at the top-level non-disableable setting.
-
@hungrier said in In other news today...:
there's no graphite on the ground
Until someone drops a pencil...
-
@Mason_Wheeler said in In other news today...:
@hungrier said in In other news today...:
there's no graphite on the ground
Until someone drops a pencil...
They'll probably send out another alert
-
-
From there, remote attackers can gain complete control over the modems, allowing them to change DNS settings, make the modem part of a botnet, and carry out a variety of other nefarious actions.
Meanwhile, I can't even reboot my cable modem remotely
-
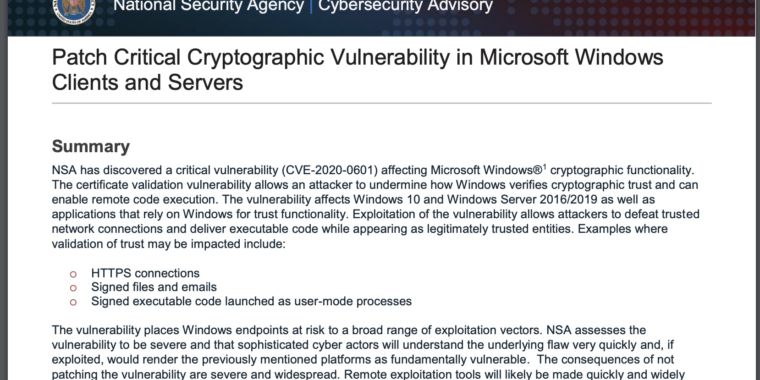
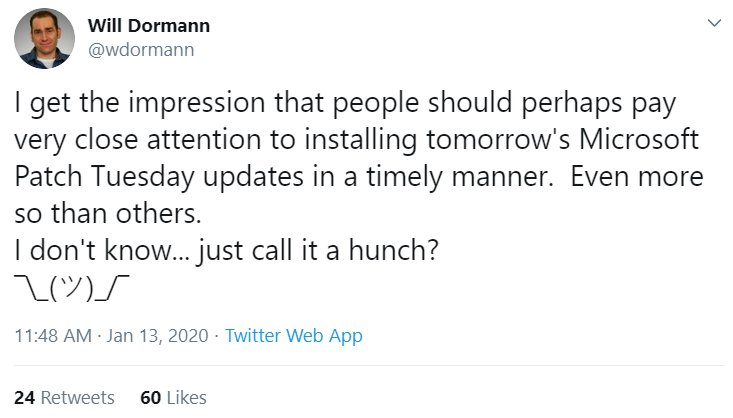
According to sources, the vulnerability in question resides in a Windows component known as crypt32.dll, a Windows module that Microsoft says handles “certificate and cryptographic messaging functions in the CryptoAPI.”
The NSA’s Neuberger said in a media call this morning that the agency did indeed report this vulnerability to Microsoft, and that this was the first time Microsoft will have credited NSA for reporting a security flaw.
You got it wrong. It was NSA that requested their critical flaw be fixed. Everybody update now, so they can tune in again. See, their programming had a 2020 bug, before New Year's the lead asked "Did you run the tests? Is everything okay?" and a dev answered "I-ran, sir!" and that was it, until yesterday all the tape reels stopped spinning

-
-
@TimeBandit (didn't read)
For compatibility reasons, every browser is going to have a client hint that looks like
Google Chrome Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/58.0.3029.110 Safari/537.36
-
@hungrier said in In other news today...:
Google Chrome Mozilla/5.0 (
Windows NT 10.0; Win64; x64X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/58.0.3029.110 Safari/537.36FTFM

-
@hungrier There only needs to be two variations.
Mozilla/5.0 (Not IE)
Mozilla/5.0 (IE)
-
@hungrier We're all safe, since the exploit requires a OS nobody use
Note: Windows 10 is not currently supported, you must use a Linux based OS

-
@loopback0 said in In other news today...:
@hungrier There only needs to be two variations.
Boomzilla/5.0 (Not alt)
Boomzilla/5.0 (alt)FTF

-
@TimeBandit The modems are looking for a particular user agent string

-
I think this may have been posted
 (well, not this exact article, but the same vulnerability)
(well, not this exact article, but the same vulnerability)
-
-
Article @Dragoon linked to said:
And please spare me the complaints that I supposedly do not have anything better to suggest, because that is a false accusation. I have said many times that looking at the history of physics teaches us that resolving inconsistencies has been a reliable path to breakthroughs, so that’s what we should focus on. I may be on the wrong track with this, of course. But for all I can tell at this moment in history I am the only physicist who has at least come up with an idea for what to do.
Really? Because I must've missed where she mentioned that idea.
What is her suggestion for experiments to run that are both a lot cheaper than the stupendously complicated collider experiments and likely to produce new insight into the fundamentals of physics beyond the standard model?
Pointing out that we know it's incomplete because gravity and quantum mechanics don't fit in a single theory isn't revolutionary. We already know that."Let's resolve the inconsistencies" is easier said than done. Everyone's been trying.
-
@topspin said in In other news today...:
Really? Because I must've missed where she mentioned that idea.
Yeah, I couldn't find it either. I think she is just bitter she never got to work on any of those billion $ projects.
-
@hungrier said in In other news today...:
no attacks in wild—yet
I think that can be said of almost all of the big scares lately....
-
https://aux.avclub.com/animorphs-comes-to-graphic-novels-in-this-exclusive-fir-1840994257
Animorphs is going comical!

-
@Dragoon said in In other news today...:
@topspin said in In other news today...:
Really? Because I must've missed where she mentioned that idea.
Yeah, I couldn't find it either. I think she is just bitter she never got to work on any of those billion $ projects.
The majority of the article was exactly content free. The paragraph that wasn't, it still read like it said "We should do something sensible. Not saying what, but we should do it." That simply isn't ever going to be actionable. It all reminds me of the other times I've had (minor) dealings with social scientists; lots of words, but nothing you can do with them. My guess is she's a Philosopher, and a second rate one at that...
But at least I didn't see any annoying Quantcast popup over the top, so there's something in its favour I guess.
-
@hungrier said in In other news today...:
The JavaScript then opens a websocket connection to the vulnerable cable modem and exploits […]
WTF? Shouldn't the same origin policy not allow that?
… or is the exploit already triggered by the preflight (the HEAD request sent to ask whether it is allowed by CORS)? Or do they allow any origin, which would be a massive WTF of it's own?
-
@Bulb said in In other news today...:
@hungrier said in In other news today...:
The JavaScript then opens a websocket connection to the vulnerable cable modem and exploits […]
WTF? Shouldn't the same origin policy not allow that?
… or is the exploit already triggered by the preflight (the HEAD request sent to ask whether it is allowed by CORS)? Or do they allow any origin, which would be a massive WTF of it's own?
Isn't CORS not applied if it doesn't set the necessary headers?
-
@Tsaukpaetra said in In other news today...:
Isn't CORS not applied if it doesn't set the necessary headers?
It is the browser that sets the headers. JavaScript can't prevent it.
-
@Bulb said in In other news today...:
@Tsaukpaetra said in In other news today...:
Isn't CORS not applied if it doesn't set the necessary headers?
It is the browser that sets the headers. JavaScript can't prevent it.
No, what I mean is, if the cable modem doesn't send the access control origin whatever, the browser will happily send shit to it if it's deemed "not requiring secure".
At least, I thought that's what happened, can't find anything that says what happens when the header is not present...
-
@Tsaukpaetra said in In other news today...:
No, what I mean is, if the cable modem doesn't send the access control origin whatever, the browser will happily send shit to it if it's deemed "not requiring secure".
No, it's the other way around there. If it does not send access control, it is same origin only. The header didn't even exist when the same origin policy was created, so the default is same origin only.
-
@Dragoon said in In other news today...:
The major cause of this stagnation is that physics has changed

-
@Tsaukpaetra said in In other news today...:
No, what I mean is, if the cable modem doesn't send the access control origin whatever, the browser will happily send shit to it if it's deemed "not requiring secure".
Think about it. You'd be depending on the remote peer to do the right thing.
-
@Tsaukpaetra said in In other news today...:
@Bulb said in In other news today...:
@Tsaukpaetra said in In other news today...:
Isn't CORS not applied if it doesn't set the necessary headers?
It is the browser that sets the headers. JavaScript can't prevent it.
No, what I mean is, if the cable modem doesn't send the access control origin whatever, the browser will happily send shit to it if it's deemed "not requiring secure".
At least, I thought that's what happened, can't find anything that says what happens when the header is not present...
CORS checks are something the browser does automatically to protect the end user when a script from domain A connects to server B. Server B can then respond "yes, I know site A" or simply return something else (or no CORS response at all). If the latter, it's the browser which goes all "Danger, Will Robinson!".
Of course, some services might want to be reached, so some give a CORS response which was the site given in the "Origin" request header. If server B doesn't check that site A is part of a trusted sites list then all bets are off.
-
@Zecc said in In other news today...:
@Tsaukpaetra said in In other news today...:
No, what I mean is, if the cable modem doesn't send the access control origin whatever, the browser will happily send shit to it if it's deemed "not requiring secure".
Think about it. You'd be depending on the remote peer to do the right thing.
I may be getting a little to used to all the
 .
.For instance:
Which has a dev commenting...
Hi.
Encryption is negotiated by the client. Curious why do you need to explicitly disable ciphers if you're the admin with the control of which encryption will be used?
Thanks!
In other words, "Well the client is responsible for telling the server whether it wants to be secure. Shirley you control all possible clients talking to your system?"
-
@Tsaukpaetra Face, meet palm.
-
@Bulb Supposedly websockets aren't protected by CORS
Normally, a mechanism called cross-origin resource sharing prevents a Web application from one origin (such as malicious.example.com) from working on a different origin (such as 192.168.100.1, the address used by most or all of the vulnerable modems).
Websockets, however, aren't protected by CORS, as the mechanism is usually called. As a result, the modems will accept the remote JavaScript, thereby allowing attackers to reach the endpoint and serve it code.
-
@hungrier said in In other news today...:
Supposedly websockets aren't protected by CORS










































































































































They implemented a
 session protocol as a HTTP Upgrade. Making same-origin-policy and CORS apply to it are about the only sensible reasons to do that complex wank. So
session protocol as a HTTP Upgrade. Making same-origin-policy and CORS apply to it are about the only sensible reasons to do that complex wank. So  .
.
-
@hungrier … ok, dug a bit more about it
The thing seems to be that SOP and CORS don't actually solve that much, and cause extra round-trips that often slow things down. So the browser just sends the origin and the server can check it if it wants. These routers probably should.
-
Rogers’ CTO Jorge Fernandes stated, “5G is not just another G. It is a global technology that requires local development to deliver the best social and economic benefits to Canadians. Through our multi-year program we will invest in our wireless network and partner with leaders to drive innovative use cases for Canadian consumers and businesses.”

-
@hungrier I wonder if I can make a similar argument to my boss about getting more RAM for my machine.
32G is not just another 16G. It is a technology that requires a local investment to deliver the best economic and ergonomic benefits to my work. Through this one-time purchase you will invest into my work machine which will drive innovative use cases and allow me to run Firefox for much longer without restarting it due to it gobbling up all available RAM.
Or something.
-
The plan is laid out in a post titled "Building a more private Web: A path towards making third party cookies obsolete." It articulates a shift from a stance Chrome developers took in August, when they warned that the blocking of support for third-party cookies—which allow advertisers to track people as they move from site to site—would encourage the use of an alternative tracking method.
Instead, Google's August post unveiled the "privacy sandbox," a proposed set of open standards that would serve as an alternative to the blocking of third-party cookies.
Chrome Engineering Director Justin Schuh said on Tuesday that adoption of the privacy sandbox will allow Chrome to drop support of the cookies altogether.
Maybe I'm
 but to me that seems to imply that the new "privacy sandbox" is so effective at tracking and potentially monetizing individual users that it makes third-party tracking cookies obsolete. And maybe it just so happens that whatever advertising-related information they can get is locked down such that only a certain G based company would be able to access it.
but to me that seems to imply that the new "privacy sandbox" is so effective at tracking and potentially monetizing individual users that it makes third-party tracking cookies obsolete. And maybe it just so happens that whatever advertising-related information they can get is locked down such that only a certain G based company would be able to access it.
-
@Bulb said in In other news today...:
@hungrier said in In other news today...:
The JavaScript then opens a websocket connection to the vulnerable cable modem and exploits […]
WTF? Shouldn't the same origin policy not allow that?
… or is the exploit already triggered by the preflight (the HEAD request sent to ask whether it is allowed by CORS)? Or do they allow any origin, which would be a massive WTF of it's own?
If you un-
 long enough to RFTA, it covers that:
long enough to RFTA, it covers that:Websockets, however, aren't protected by CORS, as the mechanism is usually called. As a result, the modems will accept the remote JavaScript, thereby allowing attackers to reach the endpoint and serve it code. While Cabe Haunt accesses modems through a browser, the attack can come from any place where running code can reach an IP on the local network.
Edit: Dammit, I stopped checking for
 one post too soon...
one post too soon...
-
-
@hungrier said in In other news today...:
Rogers’ CTO Jorge Fernandes stated, “5G is not just another G. It is a global technology that requires local development to deliver the best social and economic benefits to Canadians. Through our multi-year program we will invest in our wireless network and partner with leaders to drive innovative use cases for Canadian consumers and businesses.”

-
Phone deals thread



This phone has screens on both the front and back, which allows it to
- have a screen that takes up the entire front face
- eschew the notch that's common on modern phones
- also eschew any selfie camera, instead using the main cameras and rear screen for video calls and/or taking pictures of your own face
If it had a 3.5mm headphone socket and/or microSD support it'd be perfect
-
@hungrier 5G is another big "this will change the world forever" marketing buzzword kind of thing, like blockchains and IoT and The Cloud and NoSQL and Web 2.0s and Apps and APIs and... well, there are more examples but you get the idea.
Which is weird because at least those things were, well, things. 5G is just the exact same thing we have but faster.
-
@hungrier With those pictures, I can't tell for either the phone or for the people if it's an actual photograph or just renders.

-
@anonymous234 said in In other news today...:
Which is weird because at least those things were, well, things. 5G is just the exact same thing we have but faster.
The Cloud
Servers, but not yours.
NoSQL
Database, but without structure
Web 2.0
The web, just
slowermoreadsJavascriptIoT
The same shit as before, but with remote exploits.
-
@topspin said in In other news today...:
The Cloud
Servers, but not yours.
Also private clouds, which are servers but yours. It's exactly the thing we had before.
-
@loopback0 said in In other news today...:
It's exactly the thing we had before.
...but with more fancy buzzwords!

-
@Mason_Wheeler Relevant:
in my phone interview today, I got what seemed to be a genuine laugh when I said something like "as a non-traditional teacher, I get sick of buzzwords real fast".
Like so many other things, I'm allergic to buzzwords.
-
-
-
 Exploit that gives remote access affects ~200 million cable modems
Exploit that gives remote access affects ~200 million cable modems

 Google to phase out user-agent strings in Chrome
Google to phase out user-agent strings in Chrome