WTF Bites
-
Emergency message system in the phone network is being used to spam users by their operators in some cities
-
Status: Oh, fuck no!
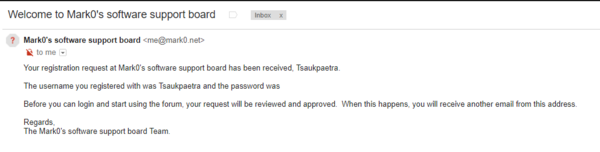
Goddammit SMF Forums, now I gotta re-sanitize that password block...
-
Doesn't matter. No one answers in the first 10 seconds anyways. Or they hang up.
Tele-marketing companies usually call more people that they can handle, because they know some of them won't pick up, so it saves time.
If you overdo it, it results in them actually getting more calls through that they can handle. So they hang up on you.
Also they sometimes just call random numbers to see if there's anything on the other side and add them to a database.
-
@sockpuppet7 said in WTF Bites:
Emergency message system in the phone network is being used to spam users by their operators in some cities
Inspired by Facebook doing the same?
-
@dcoder Sometimes those 2FA systems get in a weird state where it's taking so long to process failed requests that you can't do a successful negotiation before the temporary auth token times out. Or I guess that's what happened yesterday morning with the system we have at work.
 Only fix I know is to give up for a while and do something else…
Only fix I know is to give up for a while and do something else…
-
@sockpuppet7 said in WTF Bites:
Emergency message system in the phone network is being used to spam users by their operators in some cities
Inspired by Facebook doing the same?
That's hilarious if only Twitter didn't already do that. Or maybe Facebook was testing the waters for how its users would react to Twitter-like functionality?
-
@tsaukpaetra said in WTF Bites:
Status: Oh, fuck no!
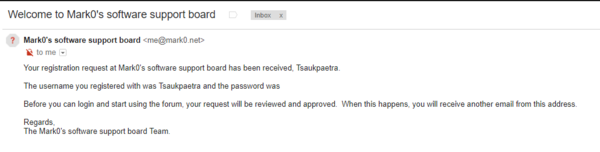
Goddammit SMF Forums, now I gotta re-sanitize that password block...
Wait, do you have something which strips out passwords or is this an SMF email template bug (hinting at password placeholder which is no longer there)?
-
@jbert Or it's an edited image.
-
@tsaukpaetra said in WTF Bites:
Status: Oh, fuck no!
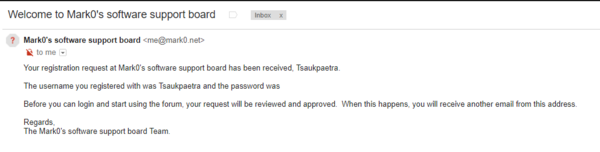
Goddammit SMF Forums, now I gotta re-sanitize that password block...
Wait, do you have something which strips out passwords or is this an SMF email template bug (hinting at password placeholder which is no longer there)?
It's not obvious but I used in l337 haxor fotoshoppe skillz to erase the part of the image that had password secure 2016 symbol.
-
Inspired by Facebook doing the same?
But that is SMS, it is blockeable. The emergency system is something to warn about missiles/earthquakes/etc, and VIVO (aka Telefonica) is abusing it as unblockeable spam.
-
@sockpuppet7 This time Facebook was spamming you through phone numbers you provided for 2fa security purposes, not your regular contact numbers. Blocking SMS on those numbers kind of kills the point of having them as security channels.
-
No path sanitization is implemented, thus malicious user is able to read content of any file from the server using simple curl command (adjust number of ../ to reflect your system):
curl -v --path-as-is http://127.0.0.1:8080/../../../../../../etc/passwd
-
@dcoder There's a(nother) reason I will never give FB my phone number.
-
@dcoder I just disabled notifications for the SMS service, because that's mostly spam. When I expect some 2fa auth or whatever I open it to see the code.
-
@sockpuppet7 said in WTF Bites:
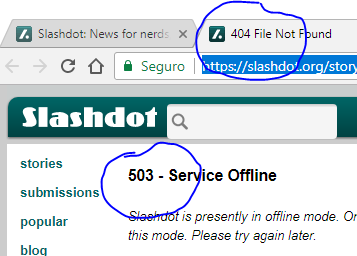
still happening at https://slashdot.org/story/18/02/28/1725238/end-of-flash-its-usage-among-chrome-users-has-declined-from-80-in-2014-to-under-8-as-of-early-2018 at the time of this post
I LOL'd when I saw the title:
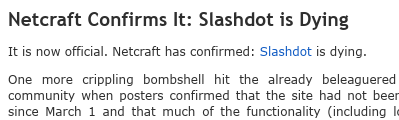
-
Sometimes those 2FA systems get in a weird state where it's taking so long to process failed requests that you can't do a successful negotiation before the temporary auth token times out.
Hah! We have some users who still have to use password authentication. Our customer decided that (basically) once a day they need to request a PIN that we send them via email. The pin is good for 10 or 20 minutes. It goes through our customer's Exchange servers, which they have inconveniently running in some centralized (and completely retarded) data center so that it routinely takes 30 minutes for an email to escape the gravity of their stupidity.
-
@boomzilla said in WTF Bites:
Hah! We have some users who still have to use password authentication. Our customer decided that (basically) once a day they need to request a PIN that we send them via email. The pin is good for 10 or 20 minutes. It goes through our customer's Exchange servers, which they have inconveniently running in some centralized (and completely retarded) data center so that it routinely takes 30 minutes for an email to escape the gravity of their stupidity.
That sounds like our email, except that the only service of note that we protect with the 2FA system is the Exchange service. We've experimented with putting other services behind that particular firewall, and all it causes is miserable failures. I have other, more productive things to do than debug that stuff.
-
In Visual Studio 2017, I tried to right click -> Peek Definition on a preprocessor macro that was defined in the project settings as opposed to a line of code. The peek code window came up as normal, but it just contained this...
-
From a job position:
[name redacted] is a rapidly growing start-up company developing a new way of browsing. We are basing our browser on the blockchain technology. Our browser is currently in beta stage, and available for your phone, tablet and computer.
Well, er, good luck with that.
-
???
-
-
@anonymous234 said in WTF Bites:
From a job position:
[name redacted] is a rapidly growing start-up company developing a new way of browsing. We are basing our browser on the blockchain technology. Our browser is currently in beta stage, and available for your phone, tablet and computer.
Well, er, good luck with that.
I can just imagine that browser's feature list:
- It comes with cryptojacking built-in
- It puts your porn site history in an "anonimized" blockchain ledger
- You need Tabcoins to open fresh windows and tabs, because they're in limited supply they will help you combat addiction
-
-
Did you know that textbox is scrollable? It's true!
-
@ben_lubar said in WTF Bites:
Namely, if another network says "please send this message claiming to be from Ben Lubar to Ben Lubar" the response should just be "no".
potstables -t nat -A PREROUTING --src-is-dst -j DNAT --to-destination $COPS
-
@anonymous234 said in WTF Bites:
[name redacted] is a rapidly growing start-up company developing a new way of browsing. We are basing our browser on the blockchain technology. Our browser is currently in beta stage, and available for your phone, tablet and computer.
Well, er, good luck with that.
BLOCKCHAIN!!!!!11 What could possibly be not to like?!
-
I guess this one is easy to agree to.
-
@pie_flavor said in WTF Bites:
Not seeing the problem there - they're three distinct programs. (One for editing ebooks, one for viewing them, and one for cataloging them.)
-
@unperverted-vixen Mostly just the name. 'The calibre e-book editor' vs 'Calibre Editor', etc.
-
How to properly implement tooltips:
-
What even do I put in this box
https://i.imgur.com/hQoJJVV.png
-
@pie_flavor said in WTF Bites:
What even do I put in this box
https://i.imgur.com/hQoJJVV.pngYou're supposed to put your If your gender identity is different than your legally assigned sex, your room selection process will be based on your gender identity. If you prefer to select a room based on your legally assigned sex, please let us know by calling the housing office at (408) 795-5600 or email us at uhs-frontdesk@sjsu.edu and ask to speak to or leave a message for Rachel Delucchi, Assistant Director for Administrative and Conference Services into the box.
-
@ben_lubar said in WTF Bites:
???
I've just realised that Bill Maher is a left-leaning commentator. He's leaning to his left in pretty much every single one of those stills (some more obviously than others)…
-
@pie_flavor said in WTF Bites:
How to properly implement tooltips:
I'm confused. What are you demonstrating here? An off-by-one error?
-
@tsaukpaetra I am demonstrating the incorrect way to implement tooltips. Either they should appear and disappear with no animation, or there should be both a fade-in and a fade-out with a delay before the fade-in begins. Otherwise you end up with that silliness.
-
@pie_flavor said in WTF Bites:
What even do I put in this box
https://i.imgur.com/hQoJJVV.png335451693C48FC787DD14C7619CAC194B7BF132C
-
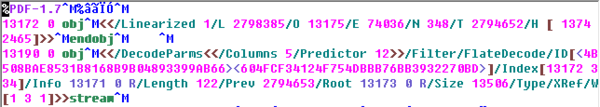
I'm still looking for a house to rent. My son and I went to an open house yesterday; the house was nice — far from ideal, but good enough to put in an application. It was being shown by the current tenant (not the landlord, which was a bit odd), and he didn't have any rental applications, so the landlord emailed me an application this morning. I forward one to my son (he's over 18, so he has to apply and sign the lease, too) and go to work.
Come the end of the day, "Oh, [expletive]. I forgot to fill out that application. It's probably too late, because they're making a decision tonight, but let's open it and see if I can just paste in the info from the last one I filled out.
WARNING: The type of the attachment does not match the expected type. Expected application/pdf; received application/octet-stream.Hmm, the sender's client probably just messed up the MIME type, or maybe he tried to compress it but didn't add the
.zip. I'll try to figure out what it is, because I do want to try to rent the house.Point Explorer to Downloads, sort by timestamp so it's at the top of the list. No preview. Click on a different PDF; it takes a second or two, but it previews fine. Click on the rental application; no preview.
That's a bit concerning. Right-click; open in Notepad++. Complete gibberish. A valid PDF has a lot of gibberesh in it, but it also has recognizable text: it starts with "%PDF-version", it has recognizeable tokens like "obj", "endobj", "/Metadata", "/Preferences", "/Contents", etc. This is pure binary; not a recognizeable word in sight.
Copy the file over to a Linux box. Run
file./home/HardwareGeek/tmp/Rental\ Application.pdf: data. It can't figure out what kind of file it is, either; it doesn't start with any recognizeable file header.Call my son. "Did you do anything with that rental application I forwarded to you this morning?"
"No, but I'll get right on it."
"Don't. It's probably too late anyway, but the application is supposed to a PDF, but it's not. I don't know what it is, but it's not a PDF. Just delete it."
"Aw, I really liked that house."
-
-
@hardwaregeek said in WTF Bites:
"Don't. It's probably too late anyway, but the application is supposed to a PDF, but it's not. I don't know what it is, but it's not a PDF. Just delete it."
Sounds like there might be an infestation of cryptolocker out there…
-
@tsaukpaetra said in WTF Bites:
scammers have been spoofing my cell number
I got an email at work the other day, supposedly from my work email address, with the subject line "k!ss my @ss!". I chose not to click on the embedded link.
One better: When getting a plan with multiple lines at once - say, a family plan - those lines tend to be assigned numbers that are numerically close to each other.
Not here. Generally they'll give you a handful of mostly dissimilar numbers to choose from and you pick the one you like best; so if you're doing multiple numbers at once, they won't normally be in a cluster.
-
@tsaukpaetra said in WTF Bites:
@hardwaregeek said in WTF Bites:
Complete gibberish
Sample?
Hex dump of the first 256 bytes:
000000 af 4b 5c 32 bc 85 f5 8a 31 99 95 20 4d 78 d6 82 000010 df fe 37 37 ca 00 5f 83 35 3f 6f b2 21 bb db f2 000020 ac ea 66 0b cd e3 36 d0 ec 5b f9 1f d5 ba b7 f5 000030 f0 51 6a 09 79 99 fd 36 a4 f0 28 5f 2f 6c 1a 43 000040 09 df 20 50 d4 82 79 0c 38 08 63 01 1d 71 f9 3d 000050 62 e8 a9 c1 d2 da 55 65 c9 29 b5 68 ac 94 11 bc 000060 29 94 e6 ab 79 2a 90 db 33 5f bf 51 de bb 28 6d 000070 55 c8 2d a9 f2 13 c2 6c 05 b7 c2 65 b5 bc 4f 93 000080 3b 52 9c 8c 64 be 7f 57 b2 42 dc ab a5 aa 62 b6 000090 bc 54 2f fc b1 63 fd 57 6f 99 3d 33 01 a1 14 d9 0000a0 f2 f2 06 43 ef 1c 31 00 dd 89 6c fa 5c 4a e1 c9 0000b0 01 61 64 3b 73 a0 cd a7 e6 8c 98 fb dd e5 9d 80 0000c0 dc 0b 09 17 ca f9 73 08 12 df 5c 53 62 cc 3f ab 0000d0 01 a5 40 6d e3 ba ca 5f 74 6d d2 76 c7 59 fa ac 0000e0 2d 50 09 fb bc c5 30 8c a4 27 ee d6 f8 f3 7b ec 0000f0 d5 ed 4c 9d ab b9 ae 1a f5 b1 57 82 cf 34 f1 f2What it looks like in vim:
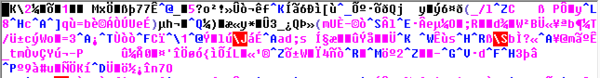
Edit: For comparison, this is the start of a valid PDF in vim:
-
@hardwaregeek said in WTF Bites:
"Don't. It's probably too late anyway, but the application is supposed to a PDF, but it's not. I don't know what it is, but it's not a PDF. Just delete it."
Sounds like there might be an infestation of cryptolocker out there…
Or something, yeah. The landlord/property manager claims to be a professonal with a well-known national real estate company. But if that were true, you'd think he'd be competent enough to send an actual application to a prospective renter. Also, if that were true, why was the house being shown by the tenant and not the pro?
Anyway, I'm sure glad my web mail client warned me about the file type mismatch. I'm not sure my phone or my desktop mail client would have done so, and I'm not going to risk finding out.
-
@hardwaregeek said in WTF Bites:
[Hex dump of the first 256 bytes]
Weird.
Hljs is highlighting that is if that were bash. Okay, sure, why not?
It explains why it highlights
cd.It does not explain why it highlights
fc. Or why it doesn't highlight other well-known commands likebcanddf.
-
It does not explain why it highlights
fc.It's a builtin.
bash$ help fc fc: fc [-e ename] [-nlr] [first] [last] or fc -s [pat=rep] [cmd] fc is used to list or edit and re-execute commands from the history list. FIRST and LAST can be numbers specifying the range, or FIRST can be a string, which means the most recent command beginning with that string. -e ENAME selects which editor to use. Default is FCEDIT, then EDITOR, then vi. -l means list lines instead of editing. -n means no line numbers listed. -r means reverse the order of the lines (making it newest listed first). With the `fc -s [pat=rep ...] [command]' format, the command is re-executed after the substitution OLD=NEW is performed. A useful alias to use with this is r='fc -s', so that typing `r cc' runs the last command beginning with `cc' and typing `r' re-executes the last command.I don't think I've ever (deliberately ;) ) used it…
-
It does not explain why it highlights
fc.It's a builtin.
bash$ help fc fc: fc [-e ename] [-nlr] [first] [last] or fc -s [pat=rep] [cmd] fc is used to list or edit and re-execute commands from the history list. FIRST and LAST can be numbers specifying the range, or FIRST can be a string, which means the most recent command beginning with that string. -e ENAME selects which editor to use. Default is FCEDIT, then EDITOR, then vi. -l means list lines instead of editing. -n means no line numbers listed. -r means reverse the order of the lines (making it newest listed first). With the `fc -s [pat=rep ...] [command]' format, the command is re-executed after the substitution OLD=NEW is performed. A useful alias to use with this is r='fc -s', so that typing `r cc' runs the last command beginning with `cc' and typing `r' re-executes the last command.I don't think I've ever (deliberately ;) ) used it…
TiL.
-
-
Fuck you, Netflix.
https://i.imgur.com/5bPstAV.png
https://i.imgur.com/v2Ay8P3.png
-
It does not explain why it highlights
fc.It's a builtin.
bash$ help fc fc: fc [-e ename] [-nlr] [first] [last] or fc -s [pat=rep] [cmd] fc is used to list or edit and re-execute commands from the history list. FIRST and LAST can be numbers specifying the range, or FIRST can be a string, which means the most recent command beginning with that string. -e ENAME selects which editor to use. Default is FCEDIT, then EDITOR, then vi. -l means list lines instead of editing. -n means no line numbers listed. -r means reverse the order of the lines (making it newest listed first). With the `fc -s [pat=rep ...] [command]' format, the command is re-executed after the substitution OLD=NEW is performed. A useful alias to use with this is r='fc -s', so that typing `r cc' runs the last command beginning with `cc' and typing `r' re-executes the last command.I don't think I've ever (deliberately ;) ) used it…
Wow, that would have been really useful to know about back when I was regularly running
history | grep
-
@ben_lubar Are you aware of Ctrl+R?
-
@ben_lubar Are you aware of Ctrl+R?
After I found out about ^Q and ^S (in the most painful possible order) I decided to try to stay away from not-killing-the-current-command key combinations. I use ^\, ^Z, ^D, and ^C regularly, though.
 Naked Security – Sophos News
Naked Security – Sophos News

 2018-03-05_20-21-50.mp4
2018-03-05_20-21-50.mp4