This time it's Mozilla. They apparently forgot to regenerate some certificates used in signing add-ons and they all stopped working.
https://www.reddit.com/r/firefox/comments/bkfte9/if_you_have_issues_with_your_addons_being_marked/
This time it's Mozilla. They apparently forgot to regenerate some certificates used in signing add-ons and they all stopped working.
https://www.reddit.com/r/firefox/comments/bkfte9/if_you_have_issues_with_your_addons_being_marked/
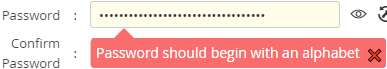
So our company procured, after years of selection and testing, a tool to manage shared passwords (where a team needs access to systems that cannot be easily connected to the federated authentication). So I tried to add the secrets for the service principal and the technical user in there and
 ⸘Warum, kurwa‽
⸘Warum, kurwa‽
… the “password” in this case is a “client secret” and is (hopefully) randomly generated by the Azure API, so I can't choose whether it will start with a digit or not.
PS: Note the bonus Engrish.
@Polygeekery I doubt you'll make friends that way, because:
@sh_code It's not JavaScript that's kidding you:
http://pubs.opengroup.org/onlinepubs/9699919799/basedefs/time.h.html:
The <time.h> header shall declare the tm structure, which shall include at least the following members:
int tm_sec Seconds [0,60].
int tm_min Minutes [0,59].
int tm_hour Hour [0,23].
int tm_mday Day of month [1,31].
int tm_mon Month of year [0,11].
int tm_year Years since 1900.
int tm_wday Day of week [0,6] (Sunday =0).
int tm_yday Day of year [0,365].
int tm_isdst Daylight Savings flag.
Javascript just passes those values on.
I would, however, grant you that the getDate for day and getDay for day-of-week is somewhat silly.
@obeselymorbid Healthy Living hasn't been available in most of the world for almost two years now 
I just got
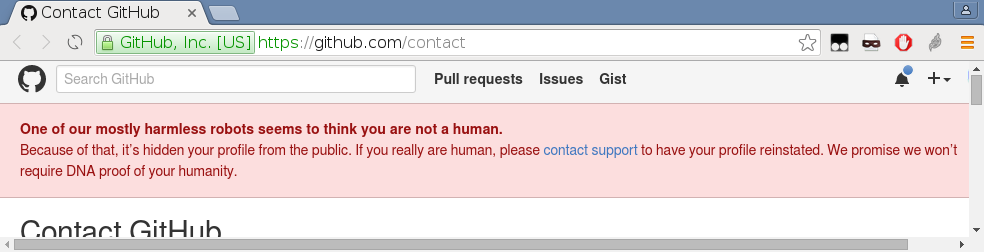
from GitHub.
How on $planet does GitHub suddenly decide that an account that exists for some years, has repositories, has comments in many bug reports that are not being marked as spam, has integrated merge requests and is member of two organizations is not a human?
@kazitor said in I, ChatGPT:
If your model is still kinda shit after ingesting a million times more words than anyone could ever read in their lifetime, maybe your model actually is kinda shit.
Wasn't overtraining actually a thing? I think there was an effect when beyond certain point, more training was making the models worse.
@HardwareGeek said in Nope:
@Bulb When the idiot who did this electrocutes himself, that will probably trigger the breaker... eventually, but not before he earns his well-deserved Darwin Award.
He most likely won't. If he touched one of the contacts with one hand and the other contact with the other hand, that could be fatal, but otherwise unlikely. When you are not touching any conductive grounding, touching a live 240 V is a non-event.
@izzion said in I, ChatGPT:
GPT is search engine with a sexy new coat of paint, news at 11.
There the AI is also built by someone who started with building a search engine, is based on that search engine core, and has a very sexy ‘coat’.
@topspin Why? A dual socket normally has just one cable running to it and the slots above each other are just connected with a solid piece of metal. So no breaker outside the socket can distinguish this horror from a normal C-type (without ground) plug, and there are no breakers inside the socket.
… so I read the original article.
@dkf In my case the enterprise and organization are already set up (and I believe there is a self-service for setting up an enterprise now). And I have an Entra/M364 account that is supposed to go with it. So I created an account with that e-mail and accepted the invitation to the organization, but the account didn't connect.
And I don't know whether I should have done something else, or whether I was sent the wrong type of invitation or whether it simply doesn't work because glucose.
@boomzilla said in Hacking News:
The researchers believe it affects all VPN applications when they’re connected to a hostile network and that there are no ways to prevent such attacks except when the user's VPN runs on Linux or Android.
...
Interestingly, Android is the only operating system that fully immunizes VPN apps from the attack because it doesn't implement option 121. For all other OSes, there are no complete fixes. When apps run on Linux there’s a setting that minimizes the effects, but even then TunnelVision can be used to exploit a side channel that can be used to de-anonymize destination traffic and perform targeted denial-of-service attacks. Network firewalls can also be configured to deny inbound and outbound traffic to and from the physical interface. This remedy is problematic for two reasons: (1) a VPN user connecting to an untrusted network has no ability to control the firewall and (2) it opens the same side channel present with the Linux mitigation.
The most effective fixes are to run the VPN inside of a virtual machine whose network adapter isn’t in bridged mode or to connect the VPN to the Internet through the Wi-Fi network of a cellular device. The research, from Leviathan Security researchers Lizzie Moratti and Dani Cronce, is available here.
They give little details, but I think I understand what they are doing: they advertise additional route or routes via DHCP (that's what the option 121 is) so that the traffic that should be routed to the virtual network interface created by the VPN software is routed to the physical network anyway.
Except … that should be fairly trivial for the VPN software to prevent. Just instead of simply setting up a default route through the virtual device, read the existing routing table—that was filled by DHCP with the option 121—and create higher priority routes for all ranges except the one IP address of the gateway to which the encapsulated packets are going.
Since the Cisco AnyConnect I use to connect to work breaks routing to the internal 172.16/12 subnet used by WSL2 and virtual machines unless being explicitly told to route it outside itself, I am somewhat confident it already does override the whole routing, making any funny DHCP-defined routes irrelevant.
Of course the attack does not affect VPNs to private networks anyway, because the bypass has no way to get into the target network, so the VPN just breaks, but no traffic can be observed.
And then there is the strange talk about side-channel. If you prevent the bypass by setting up firewall, your connection will simply break instead of being observable, but I don't see how that could create a side-channel, and I don't know what other work-around they mean.
Also, on Linux you can set up the virtual interface in a namespace and attach your session to that namespace, which is equivalent to the VM solution, which doesn't seem to be supposed to open any side-channel.
Anyway, I'd expect any good VPN software to already neutralize this, and if it doesn't, it is extremely simple-minded.
@dkf Well, I am … supposed to join such organization, so we are probably doing something wrong. Because I was invited into the organization that does belong to an enterprise, but I still don't see the enterprise anywhere despite seeing the organization, and I can't change the account to an enterprise one or something.
Also, GitHub has been owned by Microsoft for, what, over 5 years now, and Microsoft tells everybody to use GitHub for code hosting, but it still does not federate with MS365 accounts.  .
.
… at least I found somewhere that by using a ‘work’ Microsoft e-mail the accounts will connect, but they ain't doing that.