@pcooper said in Is there a guide to certificate algorithms?:
If you're looking for something a little more authoritative than what I as a random person on the Internet says, then I'd suggest looking at Mozilla's configuration recommendations:
Thanks, that's what I was looking for.
If you're a bit more paranoid, it's worth noting that the NSA's guidance as of a few years ago was to use P-384 or 3072-bit RSA for securing government systems, as they didn't seem to think P-256 or 2048-bit RSA was good enough, though I haven't seen any compelling reasons as to why.
Yeah, the Mozilla page says there ain't much of a difference and P-256 should be enough.
It's also worth knowing that ECDSA uses curves that have parameters hand-picked by NIST, and so doesn't qualify as a "Safe Curve". I figure if the US government recommends the military use it for important things then it can't be too bad, but just throwing that out there.
Perhaps they are confident they are the only ones who know the weakness  .
.
That's the main argument I'm aware of for using Ed25519 instead, but it isn't generally supported by CAs/browsers/etc. for "normal" TLS yet (which I'm guessing isn't due to a vast conspiracy, but one never knows…).
My guess is that some of the implementors didn't want to bother with the separate imlementations that curve uses.
 Why tf is it so sluggish?
Why tf is it so sluggish?
 Who in their right mind does that‽
Who in their right mind does that‽ .
.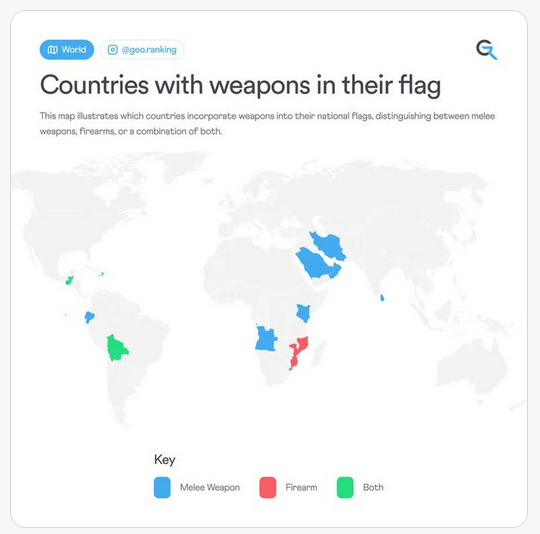
 … apparently Bolivia has a civil flag, that is just red, yellow and green stripe, and a state flag, which additionally has the coat of arms on it. TIL.
… apparently Bolivia has a civil flag, that is just red, yellow and green stripe, and a state flag, which additionally has the coat of arms on it. TIL.
 is anyone thinking there's a
is anyone thinking there's a