Deja Vu: "Malicious JavaScript in a popular NPM package" edition
-
TL;DR:
- Developer loses interest in a popular package.
- Random dev offers to be a maintainer.
- Main dev initiates github's ownership transfer process.
- Because random dev already has their own fork of this package, the transfer process fails halfway through:
-
- random dev can now publish new versions of the package,
-
- main dev can not publish anymore,
-
- main dev is still listed as the package owner.
- Random dev pushes a new version with suspicious encrypted code only in the minified source.
- Time goes by.
- Someone notices and opens an issue.
- Original dev shrugs
if you feel so strongly about it, contact npm support
.
-
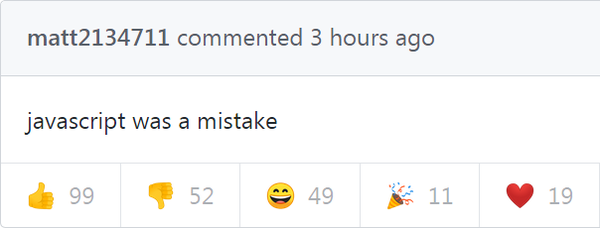
@DCoder Open sores is tah gratest!
-
-
@DCoder said in Deja Vu: "Malicious JavaScript in a popular NPM package" edition:
Time goes by.
2-3 months.
MONTHS.
-
@DCoder said in Deja Vu: "Malicious JavaScript in a popular NPM package" edition:
Because random dev already has their own fork of this package, the transfer process fails halfway through:

-
@dkf said in Deja Vu: "Malicious JavaScript in a popular NPM package" edition:
@DCoder said in Deja Vu: "Malicious JavaScript in a popular NPM package" edition:
Because random dev already has their own fork of this package, the transfer process fails halfway through:

Okay, so when attacking the npm ecosystem, be sure to fork the package under attack prior, so the patsy draws all the flack. Check.
-
Straight from the GitHub bug page:
-
