Anyone posted the Lenovo malware news yet?
-
Well NOW THEY HAVE.
Isn't Lenovo the brand all the crazy-security-conscious Lunix users buy? Why did it take so long for this to be detected?
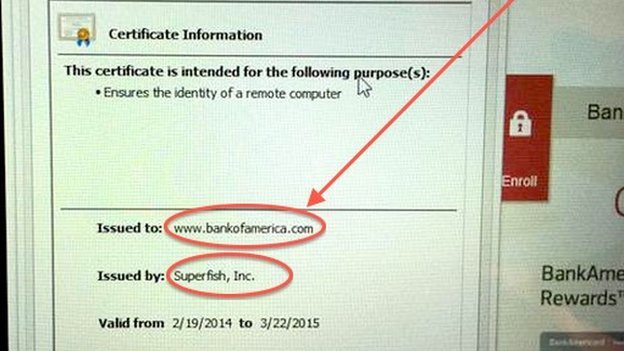
This "screenshot" (alas no wooden table) from the article is particularly damning:
-
-
Ah, so that explains the screenshot I've been seeing for the last day or so!
I really need to keep up with tech news better…
-
Isn't Lenovo the brand all the crazy-security-conscious Lunix users buy? Why did it take so long for this to be detected?
That is what I was wondering. I was just starting to come around to them as a brand.
-
Isn't Lenovo the brand all the crazy-security-conscious Lunix users buy?
I liked them because the hardware is decent for the price. I mostly scrap the pre-installed OS most of the time anyway. Because I'm a masochist and want to set up the shit I like to use myself, not because I'm paranoid.
-
Isn't Lenovo the brand all the crazy-security-conscious Lunix users buy? Why did it take so long for this to be detected?
Yes, "Why didn't Linux users detect the certificates Lenovo installed in Windows?"Also, it doesn't sound like it was there for all that long. The article says Lenovo says that it was shipped only starting in October last year. I can't put a particularly tight upper bound on that, but I have one I bought about a year before that, and mine doesn't seem to have it installed.
It does make me want to vet all my computers' root certs though...
-
and people wonder why the first thing i do whenever i get a new computer is to zero fill the harddrive and reinstall from official microsoft install media.....
-
Well NOW THEY HAVE.
Posted previously in the Evil Ideas thread:
http://what.thedailywtf.com/t/the-evil-ideas-thread/1353/776?u=boomzilla
http://what.thedailywtf.com/t/the-evil-ideas-thread/1353/777?u=boomzilla
-
Definitely legit that this is being flagged as malware; I can't think of any acceptable reasons to use certificates like that.
-
Isn't Lenovo the brand all the crazy-security-conscious Lunix users buy?
There are lots of ThinkPad-lovers that don't use Linux.
-
and people wonder why the first thing i do whenever i get a new computer is to zero fill the harddrive and reinstall from official microsoft install media.....
I go one step further and scratch-build my PCs; the first PC I built was for my AVCE in ICT
-
oh for desktops that's what i do too, but laptops? someone else can build. i'll just brainwash at the end.
-
-
-
:thatisthejoke.gif:
To badger or not to badger, that is the question...
-
Seems a faff by the time I've reinstalled it and downloaded all the drivers. I just remove the bloatware.
Should probably check the Lenovo I bought 6 weeks ago. I did remove everything Lenovo installed from it though.
-
Isn't Lenovo the brand all the crazy-security-conscious Lunix users buy? Why did it take so long for this to be detected?
Because the first thing crazy-security-conscious Lunix users do is delete Windows.
Also, I think they are generally more attached to the ThinkPad brand, which used to be owned by IBM, than to Lenovo itself.
-
laptops? someone else can build
Not sure you can scratch-build laptops. Then again, I've never actually bought one either; just taken the ones my parents no longer need when they upgrade.
-
Also, I think they are generally more attached to the ThinkPad brand, which used to be owned by IBM, than to Lenovo itself.
At this point, it's been Lenovo longer that it's been IBM. (I wager, I'm too lazy to actually look it up.)
-
I just remove the bloatware.
the bloatware is easy to remove. the rootkit that the vendor may have helpfully preinstalled, not so much. i prefer to be sure and the only way to be sure is DBAN
-
Also, if there's something we've learned in the last year is that everything is backdoored and/or stupidly vulnerable.
The NSA (and every other government probably, as well as hacker groups) has been intercepting shipments of hardware and software to swap it for backdoored versions since forever. Every freaking device today seems to be able to contain undetectable and unremovable backdoors in its firmware. You can infect USB drives' firmwares just by plugging the into a computer for 5 seconds and make them infect every computer they ever touch. Routers have a new severe vulnerability every month. 90% of Android phones only get updated for a few months (if at all) so good luck when they inevitably find a vulnerability in yours too. And to top it out every computer today now comes with an absurdly complex firmware (with network functions) permanently running in the background (UEFI).
I think at this point Lenovo might as well install TeamViewer or another remote desktop tool on their computers, configured to accept connections from everyone.
-
I made a PC out of pine cones and magnets once. But it didn't work. Also I made the whole thing up. And now I can't think of any sensible way to
-
We use Lenovos at work, and I like mine enough that I probably would have bought one for myself (except the trackpad, yuck). Our IT reimages the disks to a standard corporate configuration; I assume this scrubs nasty hidden stuff, but I don't know enough about the process to know for certain. In any case, mine is too old to be affected by this (but I checked the certificate for my bank's web site to be safe).
-
And now I can't think of any sensible way to
Well you better think of a way to, it's the law.
-
only starting in October last year
It was happening in September.
https://pbs.twimg.com/media/B-N31ImIYAAZ3CP.png:large?.png
-
Look, Ma, I'm a certificate authority!
-----BEGIN RSA PRIVATE KEY----- MIICXgIBAAKBgQDo80oYdl8ZP7HPWOl/QwcJlYA1xQ/+cTEngZkSJiCl349q/EJV Oe4JOInZ4DbErAGCW9U55vmPB4jf/u72oRTOqXRF2P3wF1cqguF6LhKTWqyK1xVj 0bebVYAPWLwcSe0gYt22TKU66xw9oP96cabTEHgzrkvCHP2SSqHD50GkLQIDAQAB AoGBAKepW14J7F5e0ppa8wvOcUU7neCVafKHA4rcoxBF8t+P7UhiMVfn7uQiFk2D K8gXyKpLcEdRb7K7CI+3i8RkoXTRDEZU5XPMJnZsE5LWgNQ+pi3HwMEdR0vD2Iyv vIH3tq6mNKgDu+vozm8DWsEP96jrhVbo1U1rzyEtX46afo79AkEA/VXanGaqj4ua EsqfY6n/7+MTm4iPOM7qfoyI4EppJXZklc/FbcV2lAjY2Jl9U6X7WnqCPn+/zg44 6lKWTnhAawJBAOtmi6nw8WjY6uyXZosE/0r4SkSSo20EJbBCJcgdofKT+VCGB4hp h6XwGdls0ca+qa5ZE1a196dpwwVre0hm88cCQQDrUm3QbHmw/39uRzOJs6dfYPKc vlwz69jdFpQqrFRBjVlf4/FDx3IfjpxHj0RgiEUUxcnoXmh/8qwh1fdzCrbjAkB4 afg/chTLQUrKw5ecvW2p9+Blu20Fsv1kcDHLb/0LjU4XNrhbuz+8TlmqstOMCrPZ j48o5+RLKvqrpxNlMeS5AkEA6qIdW/yp5N8b1j2OxYZ9u5O//BvspwRITGM60Cps yemZE/ua8wm34SKvDHf5uxcmofShW17PLICrsLJ7P35y/A== -----END RSA PRIVATE KEY-----Public key signed with Superfish cert:
-
The NSA (and every other government probably, as well as hacker groups) has been intercepting shipments of hardware and software to swap it for backdoored versions since forever.

-
Yeah, seriously. The mind control rays made that operation obsolete.
-
It's simple, relatively cheap and very effective, so why wouldn't they do it?
Forgot about fake software updates too, very easy if you have the software manufacturer and ISP on your side.
-
Welcome to reality.
-
Forgot about fake software updates too, very easy if you have the software manufacturer and ISP on your side.
No need. As long as the major Certificate Authorities are on your side, you can MITM update traffic and serve pre-compromised updates. The Equation Group has been confirmed to have been doing everything mentioned in this thread for quite a long time.Superfish now makes this wonderful capability available to script kiddies too.
-
It was happening in September.
I'm not surprised, which is why I explicitly specified that Lenovo claimed it started in October. My point is that it wasn't around (at least on all models) a year and a half ago. By point of comparison, it took around that long for Apple'sgoto failbug to be discovered, and that is arguably a worse bug than even this. It's a little surprising it took this long, but not that surprising, to be honest.
-
-
http://arstechnica.com/tech-policy/2014/05/photos-of-an-nsa-upgrade-factory-show-cisco-router-getting-implant/
It's simple, relatively cheap and very effective, so why wouldn't they do it?
Because there are so many holes in that methodology. I mean, honestly, let's look at it:
- They'd have to have the cooperation of all shipping companies. That's a low of companies that would need to be in on it without spilling the secret.
- Identifying packages would be a PITA. I mean the obvious ones would be no big deal, if the box says Cisco, that makes it easy. But what about all those boxes that don't clearly state on the outside what is in the box? Does that mean that all boxes must be intercepted and examined? That's a lot of packages …
- But wait! What about items purchase in box stores! Can't allow that loophole! Better intercept the packages before they even make it to the retailers.
- Each product is going to require slightly different modifications. Having all the necessary tools on hand in a single warehouse would be a logistics nightmare.
No, it makes much more sense to have the manufacturers include the backdoor themselves. Then there's no need to intercept and modify anything!
-
They'd have to have the cooperation of all shipping companies. That's a low of companies that would need to be in on it without spilling the secret.
Why would they need to intercept every package? They only need to be successful once. Get a UPS driver on the payroll and look through his truck every once in a while. If you get a hit against your database, hack that shipment. It's even easier if you hack into UPS and know all of their shipments before they're picked up.
-
Why would they need to intercept every package? They only need to be successful once. Get a UPS driver on the payroll and look through his truck every once in a while. If you get a hit against your database, hack that shipment. It's even easier if you hack into UPS and know all of their shipments before they're picked up.
Well, if they're trying to put a backdoor into all hardware and software …
Of course, if they're just doing it to target specific individuals or companies, then that's different.
-
Well, if they're trying to put a backdoor into all hardware and software
That's an unrealistic goal that no one had suggested.
-
-
Also just found this great article
https://firstlook.org/theintercept/2015/02/19/great-sim-heist/
-
This is a great example of the problem with the NSA today. I have no problem if they put spyware in anyone's router. That includes mine. I'm OK as long as they have some sort of effective oversight. The SIM breach, along with the infiltration of CAs, allows them to spy first and ask for permission afterwards.
They are simultaneously chipping away at oversight while building up a huge bag of tricks. It's only a matter of time before someone who works at the NSA decides to use this stuff for their personal projects. Either to ruin an ex-girlfriend or in some money-making scheme.
As long as they fight oversight, I'm not OK with this crap. If they install adult supervision, then they can have their toys without hearing us whine. Superfish is a great example of how an innocently intentioned hack can end up causing serious unintended side effects.
-
I have no problem if they put spyware in anyone's router.
??????????????????????????????????????????????????????????
I'm okay with the government having exactly the same privileges online as offline. If they can't put listening devices in my house, they shouldn't be allowed to hijack my internet connection. If they can't read letters mailed to my house, they shouldn't be reading my email.
Why would you be okay with spyware being put on your computer, even if it is by the government?
-
Why would you be okay with spyware being put on your computer,even if it is by the government?
why would you object that?
-
If they can't put listening devices in my house
They can.... with a warrant. That's what I'm OK with.
-
Can they do it by intercepting a package being delivered to my house and putting a listening device inside without me knowing? Because that's what I'm getting at.
-
They can.... with a warrant. That's what I'm OK with.
The FISA courts have an insanely low number of rejections for warrants. I think on that front we have put the fox in charge of the hen house.
-
Can they do it by intercepting a package being delivered to my house and putting a listening device inside without me knowing? Because that's what I'm getting at.
Yes. The US allows very invasive surveillance with a warrant.
-
The FISA courts have an insanely low number of rejections for warrants.
I specifically said I'm OK with "effective oversight". Today's FISA implementation does not qualify as effective.
-
Today's FISA implementation does not qualify as effective.
It wouldn't even qualify as oversight.
-
Why would you be okay with spyware being put on your computer, even if it is by the government?
Shhh... dude, they'll hear you
-
Your argument is compelling, but you only used 58 question marks. An even 60 would have definitely swayed me.

 Photos of an NSA “upgrade” factory show Cisco router getting implant
Photos of an NSA “upgrade” factory show Cisco router getting implant

