New (to me) Windows Internets Security Feature
-
And the problem is : people do use Office. And people enjoy being able to use other files' data in their spreadsheets, or having their Word documents fill from AD, or doing lots of other things you're not doing.
Things that require running arbitrary code. Which you want to forbid because back in 1998 ypu could maybe have a macro virus break your system if you actually let it run macros, which you're prompted before it's done. And it can't do shit without admin rights anyway these days.
-
Like, um, what? Actually having proper access control and not defaulting to admin for the past ten years?
Slashdot is that-a-way again. Microsoft has had their shit together in terms of user privileges since Vista (actually since 2000, if people weren't morons running everything as full admin).
-
-
how do you make "running arbitrary code" secure?
Are you kidding me?Flash? Java? Virtual machines? Android apps? Every webpage you open? Any of those ring a bell?
-
Flash?
Has more holes than a sieve
@anonymous234 said:Java?
Makes Swiss cheese look solid
@anonymous234 said:Virtual machines?
Like the JVM?
@anonymous234 said:Android apps?
That run on a JVM?
@anonymous234 said:Every webpage you open?
Drive-by downloads?
@anonymous234 said:Any of those ring a bell?
Before or after they've compromised your system?
-
when the file is locked you can't access it
Easiest way to work around that is to copy the file to a FAT32 volume - a memory stick works fine - then copy it back. This "security" feature consists of an NTFS alternate data stream added to the file by whatever process pulled it over the network, and if you round-trip it through a filesystem with no support for ADS, it goes away.
There are utilities you can get to do the same thing, but if you have a bunch of these, round-tripping them through FAT32 is usually less inconvenient.
-
That doesn't make it any clearer.
I guess you missed Blakey's rant that everything, absolutely everything, should be undoable.
-
Flash? Java? Virtual machines? Android apps? Every webpage you open? Any of those ring a bell?
Not one of those is secure.
-
There are utilities you can get to do the same thing, but if you have a bunch of these, round-tripping them through FAT32 is usually less inconvenient.
The utilities I've seen will do all of them in a directory in one go. (I thought I'd seen one that claimed to fix all of them on one drive, but I can't remember for sure.)
-
Quite a lot of my preferred procedures are based on being able to do them on whatever machine I encounter, and the less extra software I need for that, the better. I'm sure you're quite right about what the utilities can do, though; if I were designing a thing to do that, it would certainly have some sort of do-it-in-bulk feature.
-
When you have a lot of such file and don't have another drive with different filesystem to copy to, streams.exe from SysInternals Suite comes handy.
-
The answer to "will this code halt" can be answered by running it in a sandbox and seeing if it ever hits the same memory layout twice.
If it hits a previous memory layout, it does not halt. If it doesn't hit a previous memory layout, it will halt because memory is finite.
-
-
If it hits a previous memory layout, it does not halt.
What if it's just sitting in a tight loop waiting for change on an I/O register?
-
We don't allow IO to external devices in our sandboxes.
-
Then how do you test (for halting) code that requires such access?
-
what if the input devices are broken? does the program halt or not?
-
-
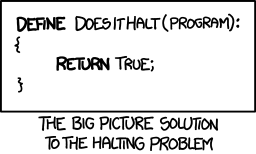
It's impossible in theory, but not in practice.
Try to prove this function wrong with a real-world example.
-
Flash? Java? Virtual machines?
Look. Either you sandbox your shit (Flash, VMs, webpages) and lose functionality people use, or don't (Java, Android) and can get pwned just as well.
You can't eat a cookie and have one.
-
-
"Well we just won't allow people to share documents anymore."
... Unless they click a button that lets them?
Big deal. Wow.
-
Not one of those is secure.
Android apps are. For the most part. Especially with the implementation of SELinux.
don't (Java, Android) and can get pwned just as well.
?
Android has a pretty intricate permissions system that sandboxes the hell out of everything... hell, every app runs as a different user.
I hope that was sarcasm or something?
Kinda tempted to
-
And if you give the app permission to wreck your shit, it may wreck your shit.
Just like, you know, in Windows. The permission system might be less intricate, but UAC is still there.
Jesus. Am I talking to people who have never worked on Windows systems?
-
Err, what?
I was saying Android sandboxes things.... which... you said it didn't? I didn't say anything about Windows...
Either you sandbox your shit (Flash, VMs, webpages) and lose functionality people use, or don't (Java, Android) and can get pwned just as well.
I'd say the Android permission system is pretty much the definition of a sandbox...
-
Halting problem is irrelevant here.
-
The only difference between the Halting Problem and what @TimeBandit wants is the end condition; you still need to be able to work it out from all possible inputs
-
@boomzilla said:
We're talking about VBA, right? Where they already have settings for whether you allow nothing to run or everything to run or to ask if you want them to run, right?
Is this just random trolling now or what? Asking for a macro.
If it's all or nothing, there's probably a reason there's not more flexibility is all I'm saying.
If what's all or nothing? You can decide whether to run on a document by document basis if you want. It was just reading like a time pod conversation or something.
-
I don't think what you're saying makes any sense.
The whole thing started when @CoyneTheDup said "you should be able to share documents without worrying about scripting, that's what documents are for".
In order to do so, all you need is a sandboxed environment. This is in no way an unsolvable problem, just let the document interact with itself but not with anything outside (no system calls), which I'm pretty sure is what @TimeBandit meant when he referenced "what is safe".
Obviously if for some crazy reason you want word documents to be able to edit your files, your system settings or access I/O devices, then there's no real way to stop them from fucking shit up. But that should obviously not be the default.
-
"you should be able to share documents without worrying about scripting, that's what documents are for"
That wasn't what I was referencing though; I was responding to @TimeBandit's assertion that MS should know exactly what is safe and what isn't, a problem equivalent to the Halting Problem.
@anonymous234 said:In order to do so, all you need is a sandboxed environment.
But to be sure the sandbox is safe, you need to be able to show the sandbox itself doesn't leak; again, a problem equivalent to the Halting Problem.
-
Re securing the scripts:
I don't see how it can be hard. It's not halting-problem-hard - if you ask me, it's not hard at all. A script can do only as much as you expose in API. If you expose file removal in API, scripts are dangerous. But then, why does MS Word expose API for removing files!? If the script could operate on the document alone, there would be no security concern regarding VBA at all (at least not more than the "damn, we fucked up this string rendering function and now any script kiddie can run arbitrary code with local admin rights" kind of bugs, which you can only protect yourself from by not making those bugs).
-
If the script could operate on the document alone
Documents can have scripts that operate on other documents. You can have entire webs of spreadsheets reading each other's cells
-
@Gaska said:
If the script could operate on the document alone
Documents can have scripts that operate on other documents. You can have entire webs of spreadsheets reading each other's cells
OK OK, but instead of saying "the document alone" say "documents in Word" (or whatever application).
-
But then, why does MS Word expose API for removing files!?
Because someone might want to remove a file from Word. Well, maybe not Word, but Excel is pretty much a general purpose programming platform for many.
And distinguishing "malicious virus removing your documents" vs. "someone wrote a file manager in Excel" is worse than halting problem.
Besides, you're still asked to run the scripts. If you don't want to, just don't run it.
-
OK OK, but instead of saying "the document alone" say "documents in Word" (or whatever application).
Oh, so I guess I can't update that TXT file. Or write a BMP.
Unless I can, in which case, I can also delete/clear them maliciously.
-
Oh, so I guess I can't update that TXT file. Or write a BMP.
Eh...can you? I dunno. I guess. Given that you can hook up to COM stuff, there's really no containing that stuff anyways.
-
Jesus. Am I talking to people who have never worked on Windows systems?
On this forum? Likely.
-
Besides, you're still asked to run the scripts. If you don't want to, just don't run it.
If they would have thought just 5 minutes about security, they would not have exposed those functions in the first place. Why the hell can Excel write to the registry, why the f**k can it run other executable ?
Oh yeah, right, functionality. Better have functionality over security.
So in the end you have only two choice : run the script giving it access to files / registry / run executable OR nothing at all.
-
Android apps are [secure].
-
If what's all or nothing?
The ability to run scripts, of course. Do try to keep up, Blakezilla.
-
This is in no way an unsolvable problem, just let the document interact with itself but not with anything outside
So much for interop. I'll be sure to tell everyone you don't think they should be able to do mail merge from another application, or have a spreadsheet that pulls data from a database, any longer.
-
Re securing the scripts:
I don't see how it can be hard.
No, it's not hard, probably. Here's the thing--making it work without removing the functionality Office et al users have taken for granted for 20+ years, that's probably not just hard, but really hard.
That's what I was hinting at, even though @boomzilla forgot he wasn't logged in to his blakeyrat persona as he pretended he didn't know what I mean.
-
Well, maybe not Word, but Excel is pretty much a general purpose programming platform for many.
Word almost certainly: you do mail merge by creating a temporary document with your data. At least, that's how a 3rd-party app that wants to create a mail merge operates. Afterwards you probably want to get rid of that temp doc.
-
@boomzilla said:
If what's all or nothing?
The ability to run scripts, of course. Do try to keep up, Blakezilla.
Except that you can tell Excel not to run any scripts in one file but run them in another. Unless you're talking about something else and just not communicating clearly.
-
That's what I was hinting at, even though @boomzilla forgot he wasn't logged in to his blakeyrat persona as he pretended he didn't know what I mean.
Huh? Again...explain what you mean by all or nothing. There's already more granular control than that, so one of us is missing something here.
-
You know what else is insecure? Computers. Just think about it - running arbitrary code, with access not only to all API calls, but peripherals directly! The ability to execute code on a computer is a major security flaw and should never have been implemented.
-
If they would have thought just 5 minutes about security, they would not have exposed those functions in the first place.
25-30 years ago, they trusted programmers. Later, this was demonstrated to be a bad idea.
Now you can't put security in without inconveniencing users--which they've done, and they've done.
-
, but peripherals directly!
This is why I try to use Linux hardware.
25-30 years ago, they trusted programmers.
We trust everyone too much by default. We learning slowly, but it's not easy.
-
Try to prove this function wrong with a real-world example.
Try to prove this function correct with a real-world example.
-
Try to prove God [exists|does not exist] with a real world example. Show your working