Hacking News
-
37C3 - Breaking "DRM" in Polish trains – 1:01:46
— media.ccc.deCCC talk about the polish train "DRM" by the polish hackers. (I think there was a post about the topic earlier.)
Audience question:
Have other train companies reached out to you about dodgy train behaviour?
No comment.
-
@LaoC said in Hacking News:
Watch out for the recording of this talk. If anything ever reeked of intentional backdooring on Apple's part it's this. They burned a few million dollars worth of 0days yesterday.
@cvi said in Hacking News:
CCC talk about the polish train "DRM" by the polish hackers. (I think there was a post about the topic earlier.)
And to (probably) conclude the Console Hacking series:
-
@TwelveBaud said in Hacking News:
Operation Triangulation:
Crazy exploit. Somebody had posted the flowchart elsewhere here, but that doesn't capture half of it. (Also crazy malware. They probably have more validation than most commercial software.)
-
BleepingComputer has contacted Google multiple times over a month with questions about these claims and how they plan to mitigate the issue, but we never received a response.

-
It was an outside job!
-
-
@cvi said in Hacking News:
Also crazy malware. They probably have more validation than most commercial software.
Well yeah. Their shit actually works!
-
@BernieTheBernie said in Hacking News:
The authorities of several towns in Northrhine-Westphalia are currently offline after a hacker put their IT provider Südwestfalen-IT out of service. Now you cannot marry there, cannot register a car, ...
Paywalled source in moon language:
And meanwhile we learned how the häckerz made it into the network: they guessed the vpn password of one guy, and then moved along...
-
@BernieTheBernie said in Hacking News:
hey guessed the vpn password of one guy,
All work VPNs I've ever used were 2-factor. Usually the second factor was a client certificate installed on the computer that was connecting.
and then moved along
Which still Shouldn't™ have been easy.
-
-
News from totally secure

glibchas some flaws.

Fortunately, that's an obscure hardly ever used library.
https://www.bleepingcomputer.com/news/security/new-linux-glibc-flaw-lets-attackers-get-root-on-major-distros/


(btw, a "shrugging penguin" emoticon would be hardly distinguishable from the "normal penguin"..., so )
)
-
@BernieTheBernie Well, it's in the syslog functions, which write to
/var/log/messagesand friends. Anyone's free to use it but I don't get the impression it's terribly common.The article doesn't say which program they exploited, but my money is on
sshdorsudo.
-
@BernieTheBernie said in Hacking News:
News from totally secure

glibchas some flaws.

Fortunately, that's an obscure hardly ever used library.
https://www.bleepingcomputer.com/news/security/new-linux-glibc-flaw-lets-attackers-get-root-on-major-distros/


Muh eyeballs!
-
The bug is due to a heap-based buffer overflow weakness accidentally introduced in glibc 2.37 in August 2022 and later backported to glibc 2.36
But people will still bitch that nobody needs Rust because good programmers can write good code in any language.
-
@Gustav there aren’t enough of those good coders, aka unicorns, out there.
-
@PleegWat said in Hacking News:
@BernieTheBernie Well, it's in the syslog functions, which write to
/var/log/messagesand friends.No, the functions don't write there, they write to
/dev/log(which is usually a unix domain socket). But that's irrelevant to the attack anyway. The important bit is that you can trigger the buffer overflow in some utility that runs with elevated privileges.The article doesn't say which program they exploited, but my money is on
sshdorsudo.The program must be SUID and the attacker must be able to launch it (because the overflow is triggered via arguments), so
sshddoes not qualify. But eithersuorsudois always there, always SUID and the PAM modules they call do the logging.
-
@Gustav said in Hacking News:
The bug is due to a heap-based buffer overflow weakness accidentally introduced in glibc 2.37 in August 2022 and later backported to glibc 2.36
But people will still bitch that nobody needs Rust because good programmers can write good code in any language.
 : We are switching to node.js. Eveything and everyone, today.
: We are switching to node.js. Eveything and everyone, today.
 : Wtf?! Are you insane?
: Wtf?! Are you insane?
 : Oh come on, you are a programmer, you can write in any language.
: Oh come on, you are a programmer, you can write in any language.
 : I quit.
: I quit.
-
@MrL But termination of an employment contract must be done on paper (
DIE PAPIERE!). And then you have to observe the termination periods, which can be several months long...
 may be able to torture you for that time!
may be able to torture you for that time!
-
@BernieTheBernie said in Hacking News:
@MrL But termination of an employment contract must be done on paper (
DIE PAPIERE!). And then you have to observe the termination periods, which can be several months long...
 may be able to torture you for that time!
may be able to torture you for that time!The silver lining in the dark cloud that is at-will employment

-
@BernieTheBernie said in Hacking News:
@MrL But termination of an employment contract must be done on paper (
DIE PAPIERE!). And then you have to observe the termination periods, which can be several months long...
 may be able to torture you for that time!
may be able to torture you for that time!Of course, reputedly, if $CORP fires you they don't trust you anymore so they'll send you on gardening leave until the date of termination.
-
@PleegWat said in Hacking News:
reputedly, if $CORP fires you they don't trust you anymore so they'll send you on gardening leave
Some won't trust you if you give notice that you plan to leave voluntarily, because leaving is disloyal, don't you know, and they'll give you 10 minutes to clean out your desk (watched, because you can't be trusted to not steal company property) then march you straight to the door. Ask me how I know.
-
@HardwareGeek In this case, first thing after you give notice is offer you a raise.
-
@PleegWat That would be a sane response to a valued employee leaving. If you were assuming this employer was sane, you'd be wrong. I think my primary value to them was being the only permanent US resident among an otherwise entirely H1-B engineering staff. Oh, well; import another $person_of_certain_ethnicity.
-
@HardwareGeek said in Hacking News:
Oh, well; import another $person_of_certain_ethnicity.
:company: That makes us very happy. Another DIE
 ticked.
ticked.
-
@dcon It's not really diverse when 95% of the company is that ethnicity, even if it is a minority in the US.
-
@HardwareGeek said in Hacking News:
@dcon It's not really diverse when 95% of the company is that ethnicity, even if it is a minority in the US.
You're forgetting, being white is evil. Anything else is bettererererer.
-
@BernieTheBernie said in Hacking News:
 may be able to torture you for that time!
may be able to torture you for that time! : I read a fascinating article lately about insider threats in IT. Really frightening stuff. Oh, sorry, my mind is wandering, I wanted to talk about mutually agreed ceasing of providing work during termination period. With pay.
: I read a fascinating article lately about insider threats in IT. Really frightening stuff. Oh, sorry, my mind is wandering, I wanted to talk about mutually agreed ceasing of providing work during termination period. With pay.
-
Fuck me, that Okta hack was … fruitful.
Anyone else for multi-factor identity management in the
multi-factor identity management in the 
 ?
?
-
@LaoC said in Hacking News:
Anyone else for
 multi-factor identity management in the
multi-factor identity management in the 
 ?
?It's not like you've got alternatives. Any organization beyond a few people needs some central identity management, and if you want to use the the identity to access third party services over the infernet, it has to be in the
 .
.
-
-
Ivanti Connect Secure ...
is absofuckinglutely secure.
CISA issued an emergency directive.
-
@Zerosquare said in Hacking News:
@Bulb said in Hacking News:
infernet
If it's a typo, I like it.
And what if it's not a typo?
-
Then it's pretty clever.
-
-
The Internet of Shit offers well expected surprises. Like hardcoded passwords which are easy to get. For example, in the heat pumps Alpha Innotec or Novelan. Their password is
eschi.
Article in moon language:
It has a link to github (
 ):
):
-
-
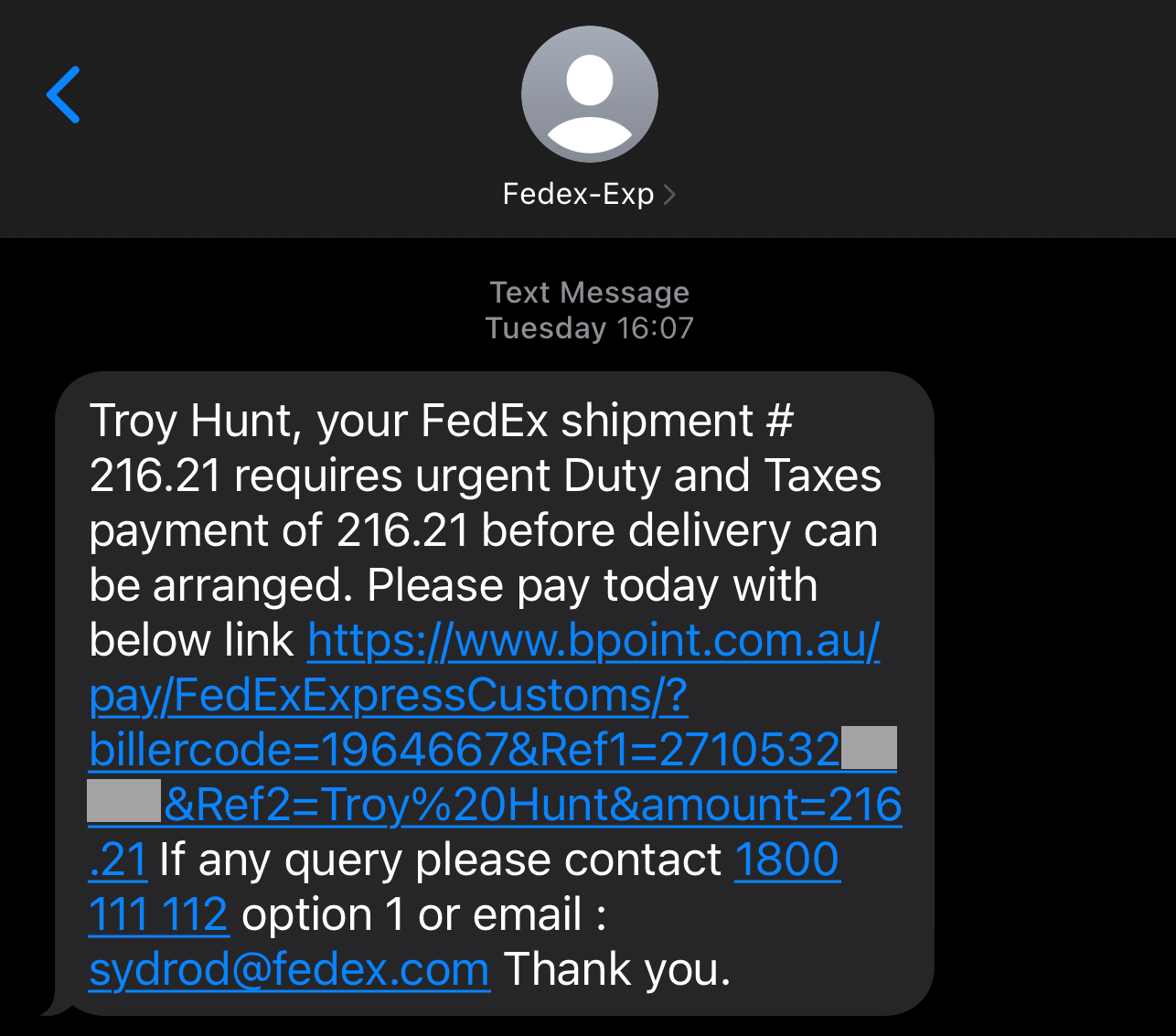
What makes this situation so ridiculous is that while we're all watching for scammers attempting to imitate legitimate organisations, FedEx is out there imitating scammers! Here we are in the era of burgeoning AI-driven scams that are becoming increasingly hard for humans to identify, and FedEx is like "here, hold my beer" as they one-up the scammers at their own game and do a perfect job of being completely indistinguishable from them.
-
-
Why would you invest a lot of your energy into hacking sites or machines, when you can have others do the job for you?
How?
Easy.
Deposit your malware on github, in a fork of a popular software.
-
@BernieTheBernie Imagine if GitHub started selling their hosted source code to train AI.
-
@Zecc said in Hacking News:
@BernieTheBernie Imagine if GitHub started selling their hosted source code to train AI.
They don't have to, it's already owned by Microsoft.
Which conveniently let's them ignore the "license? what license?" issue.
-
@Zecc said in Hacking News:
@BernieTheBernie Imagine if GitHub started selling their hosted source code to train AI.
Then uploading malware would be sabotage

-
I feel I’ve read something similar before.
-
I heard Apex Legends players were hacked through a vulnerability in the game's kernel-mode anti-cheat program (which makes their entire Windows install thoroughly compromised).
This kind of shit is (part of) why I don't play MMORPGs. If your game needs to run a Big Brother with admin access or worse, that's vulnerabilities waiting to happen.
-
@Medinoc said in Hacking News:
I heard Apex Legends players were hacked through a vulnerability in the game's kernel-mode anti-cheat program (which makes their entire Windows install thoroughly compromised).
This kind of shit is why I don't play MMORPGs. If your game needs to run a Big Brother with admin access or worse, that's vulnerabilities waiting to happen.Fortunately it's Easy Anti-Cheat which isn't widely used...

-
@Medinoc said in Hacking News:
I heard Apex Legends players were hacked through a vulnerability in the game's kernel-mode anti-cheat program (which makes their entire Windows install thoroughly compromised).
This kind of shit is (part of) why I don't play MMORPGs. If your game needs to run a Big Brother with admin access or worse, that's vulnerabilities waiting to happen. It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)
It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)
-
@izzion said in Hacking News:
@Medinoc said in Hacking News:
I heard Apex Legends players were hacked through a vulnerability in the game's kernel-mode anti-cheat program (which makes their entire Windows install thoroughly compromised).
This kind of shit is (part of) why I don't play MMORPGs. If your game needs to run a Big Brother with admin access or worse, that's vulnerabilities waiting to happen. It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)
It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)WoW has long has its own anti-cheat (warden). I'm not sure what privileges it runs with.
-
@PleegWat said in Hacking News:
@izzion said in Hacking News:
@Medinoc said in Hacking News:
I heard Apex Legends players were hacked through a vulnerability in the game's kernel-mode anti-cheat program (which makes their entire Windows install thoroughly compromised).
This kind of shit is (part of) why I don't play MMORPGs. If your game needs to run a Big Brother with admin access or worse, that's vulnerabilities waiting to happen. It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)
It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)WoW has long has its own anti-cheat (warden). I'm not sure what privileges it runs with.
 Further proof that FFXIV is the most superior game, then.
Further proof that FFXIV is the most superior game, then.
-
@izzion said in Hacking News:
@Medinoc said in Hacking News:
I heard Apex Legends players were hacked through a vulnerability in the game's kernel-mode anti-cheat program (which makes their entire Windows install thoroughly compromised).
This kind of shit is (part of) why I don't play MMORPGs. If your game needs to run a Big Brother with admin access or worse, that's vulnerabilities waiting to happen. It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)
It’s mostly shooters and MOBAs that run anti-cheats. The two biggest MMOs either have extensive mod support (WOW) or mostly have a don’t ask don’t tell implementation of their no third party programs rule (FFXIV)AFAIK Star Wars The Old Republic uses an anti-cheat. I know it at least runs something that demands administrative privileges.
-
The latest edition of Nature has an article for scientist making them aware of the threat of hackers. It is sometimes fun to read, like
“As the camera panned around to one of the nurses at the control desk, there was a piece of paper giving the password — and you could read it on screen,” he says. “The Wi-Fi password was right there, on TV.”
 4-year campaign backdoored iPhones using possibly the most advanced exploit ever
4-year campaign backdoored iPhones using possibly the most advanced exploit ever






 Thanks FedEx, This is Why we Keep Getting Phished
Thanks FedEx, This is Why we Keep Getting Phished