In other news today...
-
@Arantor said in In other news today...:
@Zecc I miss the old WinAmp 2 days, when it was a no-nonsense player that just worked and didn’t did every five minutes.
I hate it when stuff does did
-
@Arantor said in In other news today...:
In other news, compiling to WebAssembly might not be as secure as we thought…
WASM has a separate control stack, which means no stack smashing can change that, which makes it much less dangerous. But do they imply that a function can smash the data stack of the parent? Sounds like yes, and … um, it probably has to be able to¹ unless they add something like CHERI².
¹ The callee might be given a pointer to write to and the pointer might point into the caller's stack frame, so the callee must be able to write to caller's stack.
² CHERI gives each memory block a tag, stores it in pointers, and checks it on memory access, so if you overflow a block, it will immediately notice (unless you manage to hit a block that happens to use the same tag, because they are usually just one byte, but successive blocks can be trivially guaranteed to have different tags).
-
@Bulb they’re taking a more nuanced line than that. Certainly they’re saying “when you write in C/C++ there are protections you assume the compiler will apply for you, which aren’t translated into equivalents in WebAssmbly” and they’re suggesting that the “they’re not translated because they’re not necessary” may not be 100% ironclad.
As in, they’re suggesting that “here may be a chink in the armour but we’re not yet at workable exploit… but this needs research juuuuuuuuust in case it is.”
At least, that’s how I interpreted it but I live off in a happy lil world where none of this matters because of the bubble wrap that covers every sharp object except for all the ones it doesn’t. I swear if website devs had to use a language like C there would be many many fewer website and probably more done better.
-
@Arantor I read that. I am asking which are the cases they are still necessary.
-
@Bulb that’s just it, right now no ones entirely sure, except for the WebAssembly people who seem to be saying “no, it’s fine you don’t need that” as an absolute and this paper is “hold on there, are you sure?”
-
@Arantor said in In other news today...:
In other news, compiling to WebAssembly might not be as secure as we thought…
A virtual stack machine has a larger stack than a physical register machine! We're all doomed!
This article is such a load of bull. And the source paper is even worse. It conflates not crashing with exploit potential. Not a single practical exploit is presented. They delegate it to citation [11], which itself doesn't contain any security vulnerabilities beyond "the program overwrote its own memory by accident and is now calling a security-critical function with user-provided data". Which has nothing to do with WASM itself and everything to do with C being a shitty language that allows accidental overwrites of variables.
-
@Arantor quoted in In other news today...:
when you write in C/C++ there are protections you assume the compiler will apply for you
That statement's bugging me. I certainly don't write my C or C++ code under the assumption that the compiler will fix any buffer overflows for me. Doesn't mean I can 100% guarantee they can never happen (I don't consider myself infallible), but I don't assume there'll be any additional safety nets in case I mess it up and so I give my best to prevent them.
-
@Arantor Yes, they don't seem to know themselves, which is somewhat discrediting the article.
But I think I do know. Because, see, if you smash just the unrelated variables in the same stack frame, a stack canary won't catch that either, because a) there is only a canary at the end of the frame and b) it is only checked on return.
So for there to be any difference, the smashing must run over to the caller's stack frame. In the WASM case the return address is not run over in that process, because the control flow is in a separate stack that is not even accessible. But the caller's data stack has to be accessible because there are legitimate reasons to write to it. So a smash can overwrite it.
@Gąska said in In other news today...:
It conflates not crashing with exploit potential.
Indeed. Without evaluating the actual exploit potential it does not allow making much practical conclusions.
@Gąska said in In other news today...:
Which has nothing to do with WASM itself and everything to do with C being a shitty language that allows accidental overwrites of variables.
It has nothing to do with WASM itself, but something to do with clang codegen for it. It says there might still be a reason to generate stack canaries when targeting WASM, because there is still class of memory safety infractions they can catch.
-
-
-
@Bulb okay I may have misunderstood what canaries they mean. I was familiar with page-level stack canaries that trigger page fault when the program goes sufficiently far off the allocated stack space. This concept wouldn't make sense at all in WASM. But apparently they're talking about different kind of canaries - autogenerated, function-level stack integrity checks. These do make sense and could be implemented in WASM just fine, although for some reason they aren't. But anyway, the exploit potential is very low, and if you switch from C to Rust it goes down to zero.
And no, nobody has taken stack canaries for granted, ever, on any architecture. Most people probably aren't even aware they exist.
-
@Gąska So with neither stack canaries nor W^X (and possibly no ASLR either) an attacker could write malicious code into a data buffer, clobber the return address with the address of that code, and have it executed.
But WASM is supposed to be sandboxed. Which security barrier is being penetrated here? When would an attacker be able to feed malicious data into a WASM program but not just feed the user a malicious WASM program in the first place?
-
@Gąska said in In other news today...:
And no, nobody has taken stack canaries for granted, ever, on any architecture. Most people probably aren't even aware they exist.

-
@PleegWat said in In other news today...:
So with neither stack canaries nor W^X (and possibly no ASLR either) an attacker could write malicious code into a data buffer, clobber the return address with the address of that code, and have it executed.
Clobbering the return address is the hard part, as those are not stored on the same stack. (Yes, I bothered to read the article.)
-
-
@PleegWat said in In other news today...:
@Gąska So with neither stack canaries nor W^X (and possibly no ASLR either) an attacker could write malicious code into a data buffer, clobber the return address with the address of that code, and have it executed.
No they couldn't. In WASM, the execution stack and the executable code live in separate memory space from data, and cannot be directly accessed nor do they have memory addresses. The stack the article is talking about is only used for data storage. You can corrupt a whole lot in there, but you cannot corrupt function bytecode and you cannot corrupt return addresses. Neither W^X nor ASLR is needed (although ASLR would help for different reasons; but I don't think browser developers are thinking that far ahead. WASM development is going super slowly as it is.)
But WASM is supposed to be sandboxed. Which security barrier is being penetrated here?
Exactly none. The worst that can happen is trick the program to use a wrong argument for a function call which then gets used in a web query if stars align just right.
When would an attacker be able to feed malicious data into a WASM program but not just feed the user a malicious WASM program in the first place?
It's classic buffer overrun. Insufficiently sanitized input, unrestricted memcpy/strcpy, array gets written out of bounds which coincides with other important data in memory. The difference is that in WASM, the data stack lacks the critical elements that make buffer overruns on physical hardware so dangerous, in particular function return addresses.
-
@PleegWat said in In other news today...:
So with neither stack canaries nor W^X
Unless I missed something, WASM pretty much enforces W^X everywhere, and even R^X everywhere—the code and the control flow should not be accessible by any instructions of the VM at all.
-
And this is why I posted it here, I don’t know nearly enough about this and so ferried the article with “may” to cover my ass ;)
-
I would have asked for 50.
-
@DogsB And it does look like there's at least some overlap in the sort of product/service covered by the trademark application. If their trademark was for an entirely different sort of product (e.g., dish soap), the trademarks could coexist, because there's little chance of anyone confusing the two suppliers. Now, if the other Meta sold organic fertilizer, that could be a problem.
-
@ixvedeusi said in In other news today...:
@Arantor quoted in In other news today...:
when you write in C/C++ there are protections you assume the compiler will apply for you
That statement's bugging me. I certainly don't write my C or C++ code under the assumption that the compiler will fix any buffer overflows for me. Doesn't mean I can 100% guarantee they can never happen (I don't consider myself infallible), but I don't assume there'll be any additional safety nets in case I mess it up and so I give my best to prevent them.
I'd go further and I say of all mainstream languages C and C++ are the least safe, even after the compiler inserts all kinds of exploit prevention tricks. And UB is enough of a meme that "demons flying out of your nose" doesn't sound like the compiler applies kneepads for you.
-
@HardwareGeek said in In other news today...:
Now, if the other Meta sold organic fertilizer, that could be a problem.
Zuckerberg presumably produces inorganic fertilizer.
Filed under: Because he's a robot
-
@GuyWhoKilledBear said in In other news today...:
@HardwareGeek said in In other news today...:
Now, if the other Meta sold organic fertilizer, that could be a problem.
Zuckerberg presumably produces inorganic fertilizer.
Filed under: Because he's a robot
Zuckerberg
himitself, yes, but the service formerly known as Facebook is probably the largest producer (and consumer) of bovine manure on the planet.
-
@HardwareGeek said in In other news today...:
@GuyWhoKilledBear said in In other news today...:
@HardwareGeek said in In other news today...:
Now, if the other Meta sold organic fertilizer, that could be a problem.
Zuckerberg presumably produces inorganic fertilizer.
Filed under: Because he's a robot
Zuckerberg
himitself, yes, but the service formerly known as Facebook is probably the largest producer (and consumer) of bovine manure on the planet.Twatter and MSM is giving them a good fight for the title.
-
@Carnage If you lump all MSM together, yeah. If you take them individually, CNN and probably BBC (
 to look up viewer/listener numbers) are probably competitive, but I doubt any others are.
to look up viewer/listener numbers) are probably competitive, but I doubt any others are.
-

Also this...
-
@Bulb said in In other news today...:
@PleegWat said in In other news today...:
So with neither stack canaries nor W^X
Unless I missed something, WASM pretty much enforces W^X everywhere, and even R^X everywhere—the code and the control flow should not be accessible by any instructions of the VM at all.
There are a few ways of hardening things. One of the cheaper methods is to only model 32 bit address arithmetic yet have all pages containing code and execution info (return addresses, etc) be separated by 4GB or more of unmapped pages (pretty cheap to do). Guaranteeing that arithmetic is just 32 bit is easy for a compiler to do, and you will never be able to reach from the space you've got (hidden) addresses to to the space that you want to corrupt. I wouldn't claim that would guarantee safety, but reaching over such a chasm would be tricky indeed. (It would also mean that code addresses really are different things to data addresses, something that has been in the C and C++ specs for ages.)
Not many processors can directly enforce R^X; their memory management hardware isn't made that way.
-
@Gąska said in In other news today...:
@Karla said in In other news today...:
I have so many tabs open, I organize by browser
With all due respect, this is the most retarded way of organizing tabs I've ever heard of.
Well, it works for my retarded brain.
-
This old video of our prime minister is doing the rounds in news again it seems.
https://www.youtube.com/watch?v=blVSx9xlCpoI guess it's doing the rounds because he stepped down, so digging up all the memorable stuff he did to commemorate his time as our glorious leader is "news" now.
I like how the reporters arm pops. And I think that a lot of politicians would like to do this to a lot of reporters.
-
@Carnage said in In other news today...:
And I think that a lot of politicians would like to do this to a lot of reporters.
This case, however, looks like an agreed demonstration of a (very useful defensive) grapple.
-
@Bulb said in In other news today...:
@Carnage said in In other news today...:
And I think that a lot of politicians would like to do this to a lot of reporters.
This case, however, looks like an agreed demonstration of a (very useful defensive) grapple.
Yeah, somewhat agreed. The reporter had no idea what the PM was gonna do, or how hard he'd do it.
It's somewhat useful in a 1v1 scenario at least. I've never done jiu jitsu, but it does look like his form is a bit meh.
-
@Karla said in In other news today...:
@Gąska said in In other news today...:
@Karla said in In other news today...:
I have so many tabs open, I organize by browser
With all due respect, this is the most retarded way of organizing tabs I've ever heard of.
Well, it works for my retarded brain.
Me too.
I use browsers for different things.
Personal : ff,
work stuff : edge,
admin : chome
dev : ie/chome
-
@hungrier said in In other news today...:
@Arantor said in In other news today...:
didn’t did
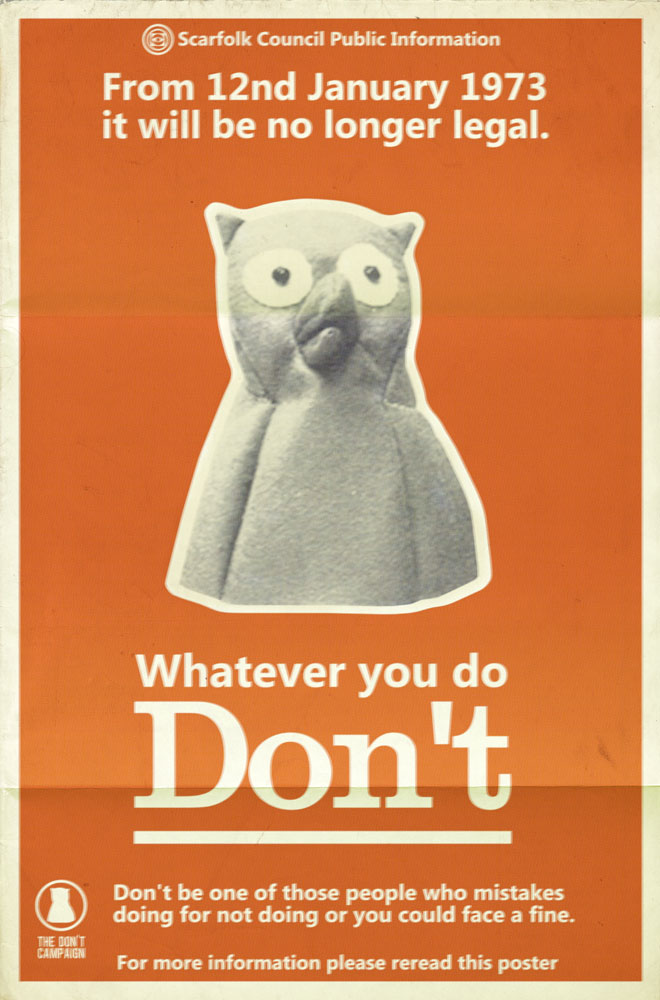
 How do you pronounce "12nd"?
How do you pronounce "12nd"? Twelvend?One second?Ten second? I am
-
@BernieTheBernie said in In other news today...:
How do you pronounce "12nd"?
Twelvety-second.
...no wait that's the 122nd. This is only the Onety-second.
-
@BernieTheBernie said in In other news today...:
@hungrier said in In other news today...:
@Arantor said in In other news today...:
didn’t did
 How do you pronounce "12nd"?
How do you pronounce "12nd"?Don't
-
@BernieTheBernie said in In other news today...:
@hungrier said in In other news today...:
@Arantor said in In other news today...:
didn’t did
 How do you pronounce "12nd"?
How do you pronounce "12nd"? Twelvend?One second?Ten second? I am
twecond.
-
-
@TimeBandit said in In other news today...:
@DogsB said in In other news today...:
dev : ie/chome
IE

yeah, most of the codebase is stuck in 2008ish.
-
You'd say he escaped from a madhouse because he's just that good at escaping:
-
Meanwhile, here I am
 to remove it from Windows 10.
to remove it from Windows 10.
-
@Zecc To be fair, they didn't say they were getting rid of OneDrive, just no longer providing support.
I'm still waiting for them to bring out a replacement for the org chart tool that ended after Windows 3.
-
-
@da-Doctah said in In other news today...:
org chart tool
apparently 'we' are big enough that 'we' bought a teams plug-in to 'dynamically' show the org chart. Dynamically, based on AD account creation as opposed to once per year when HR updates it.
Oh here it is ... https://teamorgchart.com/website/index

Who taught this was a great name for their initiative ...
G-Cloud sounds more like it is powered by PornHub UK ...
Also: unrelated related: the Church Porn Couple was identified but no official charges where made (yet) and the altar was cleaned and declared holy again
-
@Luhmann said in In other news today...:
Who taught this was a great name for their initiative ...
It's Government so there would have been a meeting with lots of people and it would have been a worthwhile spend of public money.
-
@Luhmann said in In other news today...:
@da-Doctah said in In other news today...:
org chart tool
apparently 'we' are big enough that 'we' bought a teams plug-in to 'dynamically' show the org chart. Dynamically, based on AD account creation as opposed to once per year when HR updates it.
Oh here it is ... https://teamorgchart.com/website/index

Who taught this was a great name for their initiative ...
G-Cloud sounds more like it is powered by PornHub UK ...
Theory: your CEO thought it's something else than it actually is, and now had to come up with a cover story justifying the purchase.
-
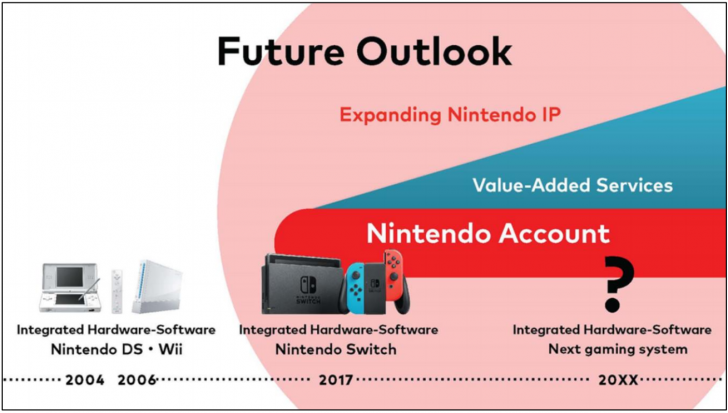
Today in the news: Nintendo announces that they will release a new console sometime within the next 79 years.
Relevant image:
-
@Gąska
We are not that big that the CEO doesn't start the dance on the company party ...that might be a different

Our company division from the North side was already flabbergasted by the idea of a company event with a dance floor
-
@Luhmann said in In other news today...:
G-Cloud sounds more like it is powered by PornHub UK ...
Eh...sounds pretty cromulent to me for what it is. Without context I would have assumed it was some kind of cloud aimed at government contracts.
-
-






 Watch: Illusionist escapes straitjacket 300 times in eight hours - UPI.com
Watch: Illusionist escapes straitjacket 300 times in eight hours - UPI.com




