Changing the lock on the front door when the back door is wide open...
-
I'm mildly infuriated at the insistence of my second-in-command (who I realize has actually very little power, if at all
 ) to urgently change passwords from the latest Twitter fiasco.
) to urgently change passwords from the latest Twitter fiasco.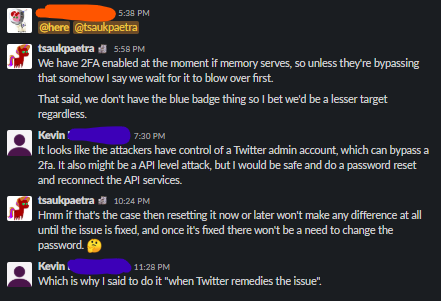
I'm like "Bro, did you even read?"
My response today:
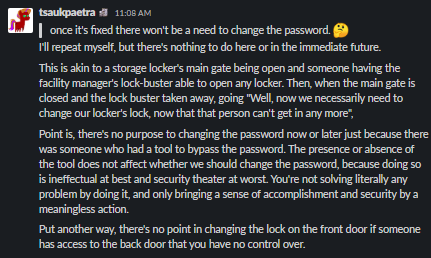
Thoughts? In my opinion, if they were using a tool to bypass account security, then resetting security at best does nothing to help with the situation, and at worst makes you think you done a good when nothing really changed about the situation.
Am I off base here?
-
@Tsaukpaetra said in Changing the lock on the front door when the back door is wide open...:
Am I off base here?
Not at all. Passwords are a solution to a different problem, and this problem has no bearing on them.
Incidentally, this is the reason behind the ubiquitous warnings that "<company> staff will never ask you for your password and if someone does ask, they're a hacker trying to hack you." Because insiders don't need your password when they have direct access to the database.
-
Please welcome your 2IC to the modern day as he steps out of his 1990's timepod. Make sure to hold his hand so he doesn't stumble as he catches his first glimpse of smartphones!
This was a real preventative measure back when websites stored passwords in plain text; if the attackers had enough access to get in the administrative side, they also (typically) had enough access to dump the database and get all of those credentials. Part of the breach recovery procedure was to force-reset everyone's passwords to ensure that any credentials that were taken become "stale" and unable to be used. However, with hashed and salted passwords as most frameworks now do by default, obtaining those credentials doesn't really do anything since they can't be directly used. Also, since this is Twitter, the internal tool they used doesn't give them access to any credentials.
-
Well yeah, do a double-check if you recognize all the API tokens issued for your account, because it's not obviously impossible an inside attacker could've added some. (But also note that upgrading password hash algorithms only works when the password is present, so who knows, maybe you're Twitter's customer #17 and your password is still triple ROT13, but that's pretty unrelated to the recent incident.)
-
Unless Twitter advises you to do so when they finished their internal investigation, changing password indeed seems pointless. API tokens may or may not have been easier to obtain for the attackers, but I'd also wait for more information before changing them.
@TwelveBaud said in Changing the lock on the front door when the back door is wide open...:
However, with hashed and salted passwords as most frameworks now do by default, obtaining those credentials doesn't really do anything since they can't be directly used. Also, since this is Twitter, the internal tool they used doesn't give them access to any credentials.
Ideally, yes. But remember why this page exists. Have you already forgotten about Facebook accidentally logging passwords in plain text?
a sense of accomplishment and security
You missed a good opportunity for an EA meme here. Shame on you.
-
There's no point changing the password until the rogue access is fixed, for sure. The 'hackers' aren't getting onto your account by having hacked your password.
However, I don't know enough about what they do have access to to know whether they could potentially find it somewhere, or add API keys to an account. Probably not, but changing account credentials and API keys is a low cost enough operation that I probably would suggest doing that after Twitter get the back door key back.
-
@bobjanova It sounds like the attack was more like running as a sufficiently privileged account that they could
chownfiles to be owned by you, but not with privileges enough to see or change your login credentials (we have a lot of systems configured like that at work by the Power ofGreyskullLDAP). Plenty of mischief possible, but password compromises not really among them, barring other stupidity of course.
-
@dfdub said in Changing the lock on the front door when the back door is wide open...:
You missed a good opportunity for an EA meme here. Shame on you
Sorry, not well versed enough on that. Something something microtransactions?
-
@dkf said in Changing the lock on the front door when the back door is wide open...:
barring other stupidity of course
That's why I'd take the cautious route and reset things that are easy to reset afterwards - it's really hard for an outsider to know just how stupid something like that might be.
-
@Tsaukpaetra said in Changing the lock on the front door when the back door is wide open...:
@dfdub said in Changing the lock on the front door when the back door is wide open...:
You missed a good opportunity for an EA meme here. Shame on you
Sorry, not well versed enough on that. Something something microtransactions?
"sense of pride and accomplishment", from the most downvoted comment on all of Reddit:
https://www.reddit.com/r/StarWarsBattlefront/comments/7cff0b/comment/dppum98
-
@dfdub
I’m a little disappointed it hasn’t hit -1,000,000
-
@izzion
Well, the thread was locked pretty quickly, which I think makes further downvotes impossible.
-
@dfdub said in Changing the lock on the front door when the back door is wide open...:
@izzion
Well, the thread was locked pretty quickly, which I think makes further downvotes impossible.I thought you could still vote in locked threads, just not reply
-
@hungrier
Well, the downvote button is hidden for me right now, but that might be because the post is also archived.
-
@dfdub FWIW I can see both buttons. But you're right about archiving, you can't do anything when it's older than some time span (6 months or a year, something like that)