Remote Windows shell access acheived via hacking...
-
Notepad!
Might be overblown though..
The exact details of the bug have not been revealed yet, and Travis has informed Microsoft to allow them the usual 90 days to fix the issue before disclosure.
Most researchers, however, downplay the significance of the hack, noting that hackers will need to get targets to open files in Notepad first. This is unlikely to happen by default, except for the deprecated IE11.
“But today, post IE mitigations, there is no way to launch Notepad on a system unless you’re sitting at the computer,” Kaminsky said.
We note however that the top most-frequently used app in most developer’s computers is often Notepad, largely because it seemed the safest way to open unknown files. It appears those days may be over, at least for now.
-
Threatposts notes the hack is impressive.
“Notepad is exposing so little of an attack surface it’s notable that it is still enough to give an attacker the ability to run arbitrary code,” said Dan Kaminsky, chief scientist and founder at White Ops.
For one thing, Notepad is a common guinea pig. If a team is adding a new feature, they may ask Notepad to support the feature, in order to get some feedback on how well the feature works in a “real program”, rather than a unit test.
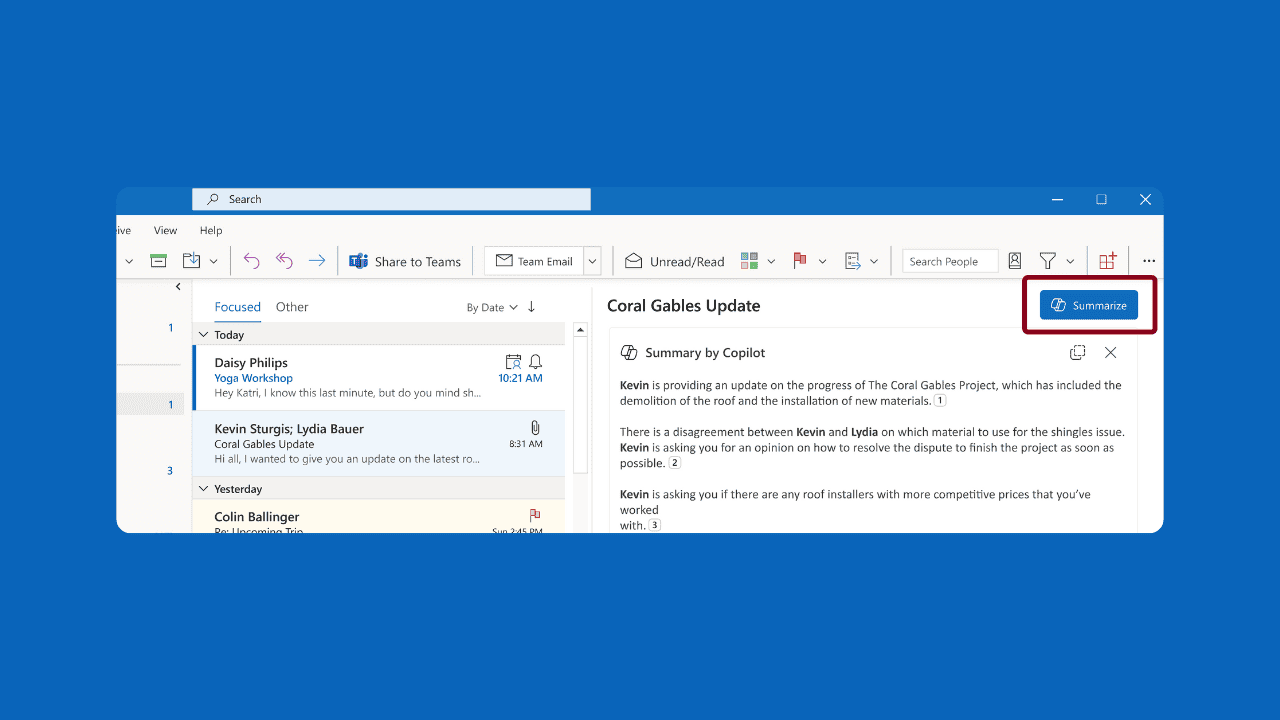
For example, did you know that you can type https://www.microsoft.com/ into Notepad’s File Open dialog?
-
into an entry point for full system access.
Ugh. Nowhere does it say that. That would also require a more severe kernel bug.
As far as
Notepad is exposing so little of an attack surface it’s notable that it is still enough to give an attacker the ability to run arbitrary code
goes, my money is on Unicode handling.
-
Also from OP:
We note however that the top most-frequently used app in most developer’s computers is often Notepad, largely because it seemed the safest way to open unknown files.
Has the author ever met a developer?
-
And the comments section immediately dropped into an "OSS is better because you can see the bugs" war.
-
@dcon s/bugs/backdoors/
And they're mostly right.
-
Hm... I could find multiple "press" "articles" about this exploit, but not a single Reddit post... Weird.
Anyway, I'm backing up my copy of Notepad so I can see the exploit live.
Edit: last modified: 2018-04-12.
-
@Gąska said in Remote Windows shell access acheived via hacking...:
Hm... I could find multiple "press" "articles" about this exploit, but not a single Reddit post... Weird.
That's where I found the link.
https://www.reddit.com/r/netsec/comments/bwsz9c/googles_project_zero_hacks_windows_notepad_to/
-
@topspin said in Remote Windows shell access acheived via hacking...:
my money is on Unicode handling.
Could be Unicode. But there's also this:
With this lock in place, I cannot open the file with:
WordPad
Notepad++
Programmatically with C#
From the command line with the type command
Internet ExplorerI can open it with Notepad.
How the heck is Notepad able to open a locked file that nothing else can?Based on Raymond Chen's explanation of how Notepad opens files, it could be some sort of memory-handling error.
-
@El_Heffe I love how those 2 articles also link to each other!
-
@Gąska said in Remote Windows shell access acheived via hacking...:
For example, did you know that you can type https://www.microsoft.com/ into Notepad’s File Open dialog?
Uh, yeah, you can do that in any file open dialog using the Windows Standard API, and it will trigger a background download using Internet Explorer and transparently navigate to the Temporary Internet Files folder and select the result and close the dialog.
-
@Tsaukpaetra um... you know that the API for file dialog only returns filename? That's definitely not a standard behavior. At least not in raw WinAPI.
-
@Gąska said in Remote Windows shell access acheived via hacking...:
@Tsaukpaetra um... you know that the API for file dialog only returns filename? That's definitely not a standard behavior. At least not in raw WinAPI.
It's something handled by the Common Controls File Dialog, the Shell, and the libraries behind them, which have been added to many times over the years. All the application sees is the normal return from (whichever version of) it.
-
@Gąska said in Remote Windows shell access acheived via hacking...:
@Tsaukpaetra um... you know that the API for file dialog only returns filename? That's definitely not a standard behavior. At least not in raw WinAPI.
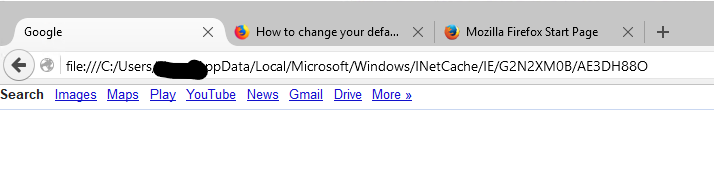
It's standard behaviour in every single program that uses an open file dialog that looks like this:
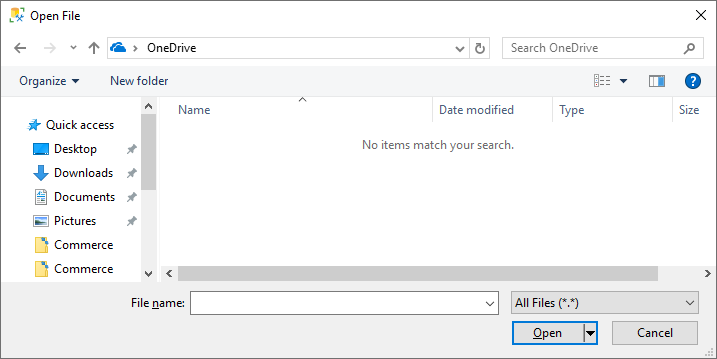
Just because it returns a file name that ends up being in Temporary Internet Files doesn't mean it's not standard behavior.

For instance, this is me opening "google" in SSMS:
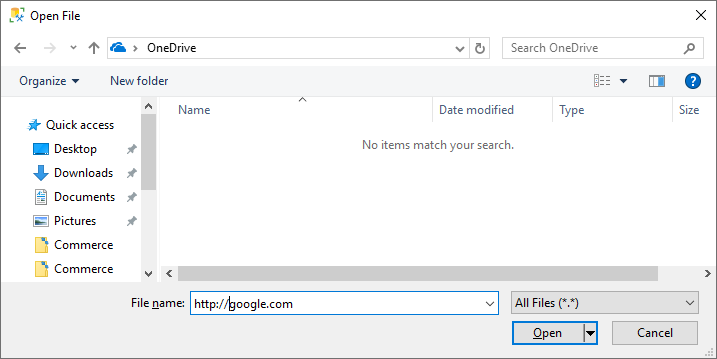
Which does this:
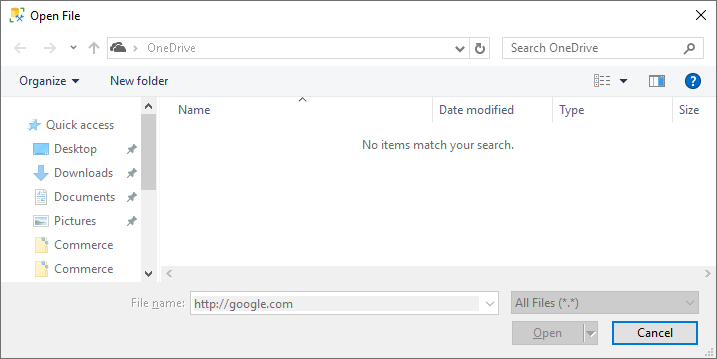
Which results in this:

Think it's just Microsoft that does it? Let's try um... Audacity!
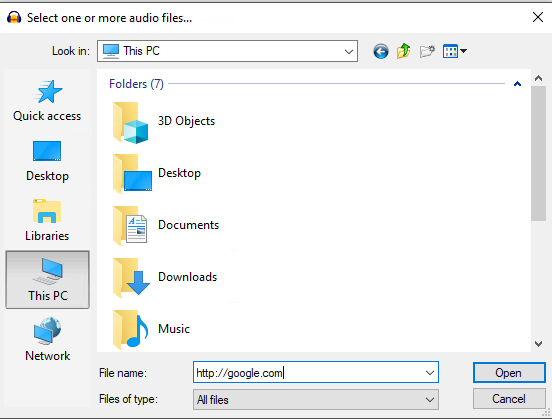
Good so far...
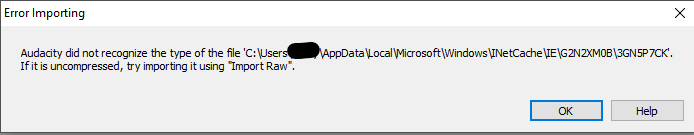
Oh, well... shit. Turns out html is not, in fact, an audio file Audacity can understand. Who knew?What about Firefox?
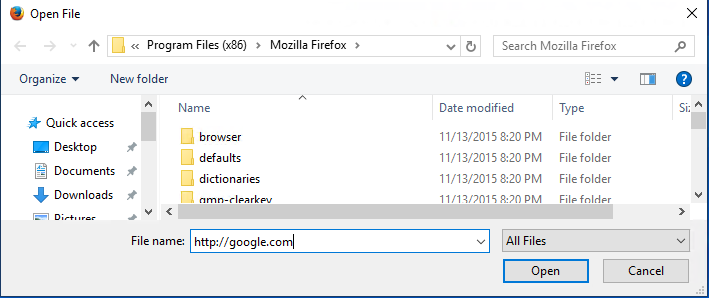
Crossing fingers...
Wait, what? I typed in the full URL and everything! Hrmmm
-
@topspin said in Remote Windows shell access acheived via hacking...:
goes, my money is on Unicode handling.
Given the nature of notepad, if the bug is not in how notepad loads the file but in how it sets data in the edit control, it could affect other applications as well.
But the bug is not posed that way, so it should be somewhere between file reading and encoding detection.
-
@Tsaukpaetra okay, you got me. Must be post-XP RTM addition. I wish it was documented somewhere.
-
@Gąska said in Remote Windows shell access acheived via hacking...:
I wish it was documented somewhere.
Oh, MSDN probably mentioned it for a few minutes or so...
-
@Tsaukpaetra well, it doesn't now. I checked before posting.
-
choco install notepad3
-
@Gąska said in Remote Windows shell access acheived via hacking...:
For example, did you know that you can type https://www.microsoft.com/ into Notepad’s File Open dialog?
You can do that into any place that accepts text.

Jokes aside, you can also type URLs in File Explorer's address bar and it'll open your browser. This is, of course, not very different from typing the path to a random file and have Explorer open the default handler application.
-
@Gąska said in Remote Windows shell access acheived via hacking...:
@Tsaukpaetra well, it doesn't now. I checked before posting.
It probably exists, but somebody's ADD kicked in and they changed the URL, again.
-
@Zecc said in Remote Windows shell access acheived via hacking...:
@Gąska said in Remote Windows shell access acheived via hacking...:
For example, did you know that you can type https://www.microsoft.com/ into Notepad’s File Open dialog?
Jokes aside, you can also type URLs in File Explorer's address bar and it'll open your browser.
I think it was back in the Windows XP days, typing a URL into the Windows Explorer (AKA File Explorer) address bar didn't open your browser, it would actually display the webpage in Windows Explorer, due to Windows Explorer and Internet Explorer (at that time) just being two parts of the same program.
-
@topspin said in Remote Windows shell access acheived via hacking...:
into an entry point for full system access.
Ugh. Nowhere does it say that. That would also require a more severe kernel bug.
It doesn't say it's a vector for privilege escalation. It just says it can move the attacker down the attack chain, which is true. I wonder if the exploit works if the Command Prompt is "disabled".
Edit: Someone points out in the comments:
https://pbs.twimg.com/media/D7L1e_8XYAEssLi.pngI'm not saying it's that, but it makes a good point that Notepad's attack surface is probably much greater than we think it is with the common controls, context menus, the shell, etc... I'd be surprised if it's not the shell that's the problem and Notepad's the demonstration app just because it's so innocuous.
-
@heterodox said in Remote Windows shell access acheived via hacking...:
It doesn't say it's a vector for privilege escalation.
"An entry point for full system access" reads like privilege escalation to me. Which was probably made up on the spot (due to ignorance) and is nowhere to be found in what Project Zero claims.
-
@topspin said in [Remote Windows shell access acheived via hacking...]
"An entry point for full system access" reads like privilege escalation to me. Which was probably made up on the spot (due to ignorance) and is nowhere to be found in what Project Zero claims.
I'm still curious on how it works. Since notepad itself don't run with full admin right, the process it spawns directly (say, to run application inside "Open file" dialog) will just have the same right.
Since the article mentions "memory corruption flaw", I think the only liable target is clipboard access, where the system has to ask what format your application can provide, then request it. Maybe the flaw lies somewhere on how it handles different format requests.
-
@topspin said in Remote Windows shell access acheived via hacking...:
@heterodox said in Remote Windows shell access acheived via hacking...:
It doesn't say it's a vector for privilege escalation.
"An entry point for full system access" reads like privilege escalation to me. Which was probably made up on the spot (due to ignorance) and is nowhere to be found in what Project Zero claims.
 Well, it is "an entry point"! Open cmd, run "runas ... "
Well, it is "an entry point"! Open cmd, run "runas ... "
-
@dcon said in Remote Windows shell access acheived via hacking...:
 Well, it is "an entry point"! Open cmd, run "runas ... "
Well, it is "an entry point"! Open cmd, run "runas ... "That's the distinction I was making, which makes me a
 I suppose. If you have a viable privilege escalation script, but you need to get to cmd to run it, then the notepad vulnerability provides an "entry point" for full system access.
I suppose. If you have a viable privilege escalation script, but you need to get to cmd to run it, then the notepad vulnerability provides an "entry point" for full system access.
-
@heterodox Under that definition running a computer that’s not air-gapped is an entry point for full system access.
-
@cheong A program that runs in the background and executes any command you send it would be considered "full system access" by most people.
Given that it would let me quietly steal all your browser information, log your keyboard input, read and delete your personal documents, spy your webcam and microphone, and install my own scripts to run on startup, it's a pretty reasonable definition.
Now if I wanted to upgrade your GPU drivers, Windows' "airtight hatch" security would totally stop me.
-
@topspin said in Remote Windows shell access acheived via hacking...:
@heterodox Under that definition running a computer that’s not air-gapped is an entry point for full system access.
Sure. Much less of one than a vulnerability that allows escaping a limited shell or set of programs (or allows arbitrary code execution -- we don't know the scope of the vulnerability yet is the point).
-
Maybe it's like the old joke about the Polish computer virus. It's a text file that tells you to delete your files and forward the virus to everyone on your contact list.
-
@Gąska said in Remote Windows shell access acheived via hacking...:
@Tsaukpaetra well, it doesn't now. I checked before posting.
I think Windows told me about that feature during the install when I shows lots of marketing wankery when I installed it a few years ago. I actually used it to circumvent some "security" preventing me from downloading files with the browser.
-
@levicki said in Remote Windows shell access acheived via hacking...:
My guess is that, since Notepad is "reading" the file by using CreateFileMapping() and MapViewOfFile(), that there is some way to make the mapped view executable, corrupt stack and make it jump to that code.
No. Tavis referred to CFG gadgets which means the mapped view wouldn't need to be made executable. I'd anticipate the exploit works with DEP on, ASLR on, and all guards on, which is much, much trickier than your guess. But if anyone could do it, with Notepad no less, it'd be him, so.
-
@levicki said in Remote Windows shell access acheived via hacking...:
take it easy on downvote button.
It doesn't get much use outside the garage and feels a little jealous at how much attention upvote-button gets from my tender finger...
-
@levicki said in Remote Windows shell access acheived via hacking...:
or he found a way to cause Notepad.exe to execute existing bits and pieces of its own code in such order so as to accomplish what he did.
I understood what you were saying.
So either he found a way to subvert that, or he found a way to cause Notepad.exe to execute existing bits and pieces of its own code in such order so as to accomplish what he did.
You didn't include the second possibility in your initial post. It's that one.
Therefore, that he also had to bypass Control Flow Guard (which is a compiler software protection feature turned on when compiling Notepad.exe) has nothing to do with what I was saying so next time take it easy on downvote button.
I didn't downvote you. In general, I don't downvote people.
-
@LaoC said in WTF is happening with Windows 10? And nothing else:
Where @taviso touches Windows, expect the 42 virgin nasal demons of the apocalypse to appear and leave but smoking cinders:
@Zerosquare said in WTF is happening with Windows 10? And nothing else:
@LaoC: Wow. This is a pretty huge and dangerous oversight.
@dkf said in WTF is happening with Windows 10? And nothing else:
@LaoC So the input method system in Windows is even more of a steaming pile of shit than it is under X11? That's… actually amazing, as I didn't think that was possible.
@levicki said in WTF is happening with Windows 10? And nothing else:
@Zerosquare said in WTF is happening with Windows 10? And nothing else:
@LaoC: Wow. This is a pretty huge and dangerous oversight.
Who said it's an oversight?
@Carnage said in WTF is happening with Windows 10? And nothing else:
@LaoC I'm kinda curious if MS got a proper heads up about it, and if they've had time to put some mitigation in place...
@heterodox said in WTF is happening with Windows 10? And nothing else:
@Carnage said in WTF is happening with Windows 10? And nothing else:
@LaoC I'm kinda curious if MS got a proper heads up about it, and if they've had time to put some mitigation in place...
He did and they did. (Tavis is a responsible researcher, and I recall seeing his "popping a shell in Notepad" tweet months ago (WTDWTF thread here)).
@topspin said in WTF is happening with Windows 10? And nothing else:
Article @LaoC linked to said in WTF is happening with Windows 10? And nothing else:
It wouldn’t make sense if an unprivileged window could just send commands to a highly privileged window, and that’s what UIPI, User Interface Privilege Isolation, prevents.
Which reminds me: Do Linux/X or macOS have that yet?
Last I heard they didn't, but I could be wrong.
@levicki said in WTF is happening with Windows 10? And nothing else:
@Carnage said in WTF is happening with Windows 10? And nothing else:
@LaoC I'm kinda curious if MS got a proper heads up about it, and if they've had time to put some mitigation in place...
Better question is whether they put proper mitigation in place?
@LaoC said in WTF is happening with Windows 10? And nothing else:
@topspin said in WTF is happening with Windows 10? And nothing else:
Article @LaoC linked to said in WTF is happening with Windows 10? And nothing else:
It wouldn’t make sense if an unprivileged window could just send commands to a highly privileged window, and that’s what UIPI, User Interface Privilege Isolation, prevents.
Which reminds me: Do Linux/X or macOS have that yet?
Wayland has it by default; X11 has had a security extension called XACE for a couple of years now and apparently SELinux can use it, but I have no clue how to even activate it; my understanding is that individual applications have to support it, so it's as good as nonexistent.
Well, it looks a whole lot worse than the OP of this thread made it out to be. Almost any process can be compromised, including the login process and the admin consent dialog process. So much for "Most researchers, however, downplay the significance of the hack, noting that hackers will need to get targets to open files in Notepad first." Notepad was just the testing ground.
So, an unprivledged user running an AppContainer sandboxed app could interfere with other users on the system (including injecting text into admin command prompts) and run processes with system permissions. Amazing.
-
@LB_ said in Remote Windows shell access acheived via hacking...:
@LaoC said in WTF is happening with Windows 10? And nothing else:
Where @taviso touches Windows, expect the 42 virgin nasal demons of the apocalypse to appear and leave but smoking cinders:
@Zerosquare said in WTF is happening with Windows 10? And nothing else:
@LaoC: Wow. This is a pretty huge and dangerous oversight.
@dkf said in WTF is happening with Windows 10? And nothing else:
@LaoC So the input method system in Windows is even more of a steaming pile of shit than it is under X11? That's… actually amazing, as I didn't think that was possible.
@levicki said in WTF is happening with Windows 10? And nothing else:
@Zerosquare said in WTF is happening with Windows 10? And nothing else:
@LaoC: Wow. This is a pretty huge and dangerous oversight.
Who said it's an oversight?
@Carnage said in WTF is happening with Windows 10? And nothing else:
@LaoC I'm kinda curious if MS got a proper heads up about it, and if they've had time to put some mitigation in place...
@heterodox said in WTF is happening with Windows 10? And nothing else:
@Carnage said in WTF is happening with Windows 10? And nothing else:
@LaoC I'm kinda curious if MS got a proper heads up about it, and if they've had time to put some mitigation in place...
He did and they did. (Tavis is a responsible researcher, and I recall seeing his "popping a shell in Notepad" tweet months ago (WTDWTF thread here)).
@topspin said in WTF is happening with Windows 10? And nothing else:
Article @LaoC linked to said in WTF is happening with Windows 10? And nothing else:
It wouldn’t make sense if an unprivileged window could just send commands to a highly privileged window, and that’s what UIPI, User Interface Privilege Isolation, prevents.
Which reminds me: Do Linux/X or macOS have that yet?
Last I heard they didn't, but I could be wrong.
@levicki said in WTF is happening with Windows 10? And nothing else:
@Carnage said in WTF is happening with Windows 10? And nothing else:
@LaoC I'm kinda curious if MS got a proper heads up about it, and if they've had time to put some mitigation in place...
Better question is whether they put proper mitigation in place?
@LaoC said in WTF is happening with Windows 10? And nothing else:
@topspin said in WTF is happening with Windows 10? And nothing else:
Article @LaoC linked to said in WTF is happening with Windows 10? And nothing else:
It wouldn’t make sense if an unprivileged window could just send commands to a highly privileged window, and that’s what UIPI, User Interface Privilege Isolation, prevents.
Which reminds me: Do Linux/X or macOS have that yet?
Wayland has it by default; X11 has had a security extension called XACE for a couple of years now and apparently SELinux can use it, but I have no clue how to even activate it; my understanding is that individual applications have to support it, so it's as good as nonexistent.
Well, it looks a whole lot worse than the OP of this thread made it out to be. Almost any process can be compromised, including the login process and the admin consent dialog process. So much for "Most researchers, however, downplay the significance of the hack, noting that hackers will need to get targets to open files in Notepad first." Notepad was just the testing ground.
So, an unprivledged user running an AppContainer sandboxed app could interfere with other users on the system (including injecting text into admin command prompts) and run processes with system permissions. Amazing.
Yes, someone really herped the derp with this one.
-
@LB_ said in Remote Windows shell access acheived via hacking...:
Well, it looks a whole lot worse than the OP of this thread made it out to be.
No, its even worse than that, as it is hard to fix without breaking usability completely for a very large fraction of users (those who use complex input methods) and it was largely invisible to western developers precisely because they don't use that steaming pile of complexity.
-
@dkf said in Remote Windows shell access acheived via hacking...:
western developers
I was once looking at it in a bid to write an IME. Got precisely nowhere...
-
@LaoC said in WTF is happening with Windows 10? And nothing else:
@topspin said in WTF is happening with Windows 10? And nothing else:
@dkf said in WTF is happening with Windows 10? And nothing else:
@LaoC So the input method system in Windows is even more of a steaming pile of shit than it is under X11?
Hate to be arguing for Windows, but I'm going to go with "No" on that one.
There is no access control in CTF, so you could connect to another user's active session and take over any application, or wait for an Administrator to login and compromise their session.
Taking over an admin's applications on another active session is quite a bit worse than X11 though. Applications are not isolated in any meaningful sense, but sessions are.
I had only read the intro to the article earlier and just now got around to finishing it.
Well, hot damn, this is really bad! This does compromise everything, doesn't it.How did they manage to implement things like UIPI and not realize this is a hole you can drive a truck through? Only explanation I can come up with this is they themselves don't even know all the parts of the system even exist.
Did they actually manage to fix this one in 90 days? Because the last time we talked about the 90 day limit it was about something like a trivial bug in a crypto cipher, which may be hard to find and have severe consequences, but is simple to fix and unit test for regressions. This one sounds like you have to change a whole lot more in the IME architecture.
What I didn't understand from a technical side:
The article explains how the kernel forces every window to connect to the CTF service and that can be used as a proxy to send messages to other programs, bypassing the UIPI whitelist, and even make notepad create arbitrary COM objects. But after the messages got send to notepad by means of CTF, what makes notepad actually process these (presumably unexpected) messages to create COM objects? Is it the DefWindowProc handler that does all the dirty work?
-
So my takeaway from this is to never reuse a Microsoft library again?