Posts made by Medinoc
-
RE: So this might happen if one dares to use linuxposted in General
@djls45 Must be either something notepad2 does, or something Windows Explorer does for
IDropTarget-supporting programs only, because when I drag the shortcut to my (non-IDropTarget-supporting) test program*, it clearly tells me it received the.lnkfile on its command line.*This test program is actually a program to show the contents of files of several formats (text files, GDI+-supported images, executables etc., including shortcuts), and I've programmed it to handle shortcuts by showing me a dialog box that tells me it's a shortcut, tells me its target path, and asks me whether I want to open the shortcut itself or the target.
Edit: D'oh! By "drag onto text editor" I initially took that as "drag onto the EXE file in Windows Explorer", instead of "drag onto the open window". Of course the latter will only work if the editor supports
IDropTarget... (facepalm)
Good news is, my test program also also has "drop area" that supports IDropTarget... And when I drop the shortcut on it, it sees a.lnkfile (both in theFileGroupDescriptorWand in theHDROP), confirming that it's indeed notepad2 that follows the shortcut. -
RE: So this might happen if one dares to use linuxposted in General
So it's sent via whatever IPC
linuxthis desktop environment uses in place ofIDropTarget, I guess. -
RE: So this might happen if one dares to use linuxposted in General
I just tested with Windows's
.lnkshortcut files, and the result is the same, courtesy of Windows Explorer:- Right-clicking a shortcut to a directory, or a file with
NoOpenWithregistry value (such as an executable), doesn't even give you the "Open With..." option to try and open with a text editor. You still get "Send To..." though, which doesn't follow shortcuts. - Right-clicking a shortcut to a file gives you "Open With...", but opens the pointed file (I've tested with a program of mine, it directly receives the target path).
- Notepad++'s "Edit with Notepad++" extension also opens the target.
- "Send To..." however, gives the program a path to the shortcut itself. So to look at the entrails of just any file, even if it's a shortcut, you can add a shortcut to your favorite text/hex/whatever editor in
C:\Users\<username>\AppData\Roaming\Microsoft\Windows\SendTo. - "Properties" will show you the target path, unless it's one of those "special" Windows Installer shortcuts.
Now for
.url"internet shortcut" files:- Even with shift-right-click, I don't get a "Open With..." to check their entrails. This despite not having the
NoOpenWithvalue (it does however haveNeverShowExtandIsShortcut, as well as theFTA_Showbit inEditFlags; and I just found itsshell\Openkey contains a value namedLegacyDisablewhose meaning eludes me, but whose name is promising -- Edit: After checking this, I guess the Open I see in the context menu is actually provided by the context menu handler, and disabling the "open" verb removes "open with" as well) - No Notepad++ either.
- "Properties" will show you the target URL.
- Good news is, it still has "Send To", which doesn't follow them either, so you can look at their entrails. And this time, they're actually text files:
[{000214A0-0000-0000-C000-000000000046}] Prop3=19,2 [InternetShortcut] IDList= URL=http://go.microsoft.com/fwlink/p/?LinkId=255142 IconIndex=0 IconFile=%ProgramFiles%\Internet Explorer\Images\bing.icoIn fact, they're not that different from Linux's
.desktopfiles...And regarding those, one question remains: Who does the actual fetching? It's possible the file explorer fetches the URL to a temporary file, and invokes the program on this, but it's more probable that it passes the URL as argument to the text editor, and the text editor fetches. This too could be easy to test: Just make your own program, that displays its arguments in a message box. And if your Linux's message boxes allow selecting & copying the text, then problem solved, you now have your GUI for retrieving the shortcut's URL.
- Right-clicking a shortcut to a directory, or a file with
-
RE: Uber, the sociopathic company full of psychopaths, now with murder! (Because regulations aren't "Disruptive" enough!)posted in Side Bar WTF
@lolwhat said in Uber, the sociopathic company full of psychopaths, now with murder! (Because regulations aren't "Disruptive" enough!):
@Medinoc At the risk of driving even farther into Garage territory, 1) what are you talking about? And 2) name a US President who didn't make such sales.
Donald Trump explicitly invoked an ongoing arms sale to Saudi Arabia as a motive not to do anything, not even symbolic condemnation (or, say, the senate-approved withdrawal of military support), about the murder of Khashoggi.
-
RE: Uber, the sociopathic company full of psychopaths, now with murder! (Because regulations aren't "Disruptive" enough!)posted in Side Bar WTF
@topspin Well with a better US president the murder would have been a big mistake. But you got one for whom murder is OK as long as you buy millions worth of US weapons.
-
RE: DNS is optionalposted in Side Bar WTF
This discussion reminds me that we were recently instructed to switch ALL our machines, physical or virtual, from Windows 7 to Windows 10 (or Server equivalents) because Windows 7 extended support is about to expire.
-
RE: Stack Exchange experiences Stack Meltdown, by enforcing preferred pronouns in site-wide communicationsposted in Side Bar WTF
Looks like they did correct the code of conduct now: "they for everyone" and "username only" are no longer counted as misgendering.
-
RE: Newest tactics in asshole web designsposted in Side Bar WTF
@topspin I have the same problem when I sleep at my parents' house: If I don't think of it before going to bed I promptly get back up to move a clock to an unoccupied room.
-
RE: Newest tactics in asshole web designsposted in Side Bar WTF
Wow, if Edge still has this idiotic "Forward all Web Notifications to Windows notification API without adding anything like \"FROM EDGE WEB BROWSER\" to their title" misfeature, this is going to be a disaster.
Edit: Looks like they at least corrected that. Well, partially:
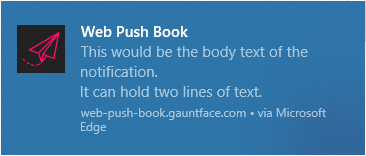
To me, "(site name) via Microsoft Edge" should be bigger than the title, and come before it.
Edit2: And the icon should be Edge's, rather than let a website set it. -
RE: Close enough securityposted in Side Bar WTF
@acrow said in Close enough security:
@loopback0 said in Close enough security:
@acrow said in Close enough security:
For single-user systems, the main point of the separation would be that the browser binary can only be altered with admin rights.
Chrome quite happily installs itself in a directory that doesn't require admin privileges to do anything to it.
Do you mean it allows to install, or by default installs in such a location?
AFAIK it does so by default, or at least it always does it when a non-administrator user downloads it.
-
RE: Close enough securityposted in Side Bar WTF
@topspin I honestly don't know. Does a Galaxy S5 mini count as "old as fuck" nowadays?
-
RE: Close enough securityposted in Side Bar WTF
@Zerosquare Which is why I never use e-mail apps, etc.* on my smartphone: Everything sensitive is opened in a (passworded) private session on the browser, and when outside I log out as soon as I'm done. And my phone is of the kind that ejects the battery when dropped.
*Especially e-mail apps, which usually lack an option not to memorize your password, on account of needing it to check for new mail every X minutes.
-
RE: Chipotle using Angular to reinvent standard HTML badlyposted in Side Bar WTF
@JBert Hm, sounds actually pretty good. A bit confusing that it uses the same graphical assets as the necromancy one, though (before reading your and @TwelveBaud 's messages I thought this was a split thread).
-
RE: Checking mobile users in web pages, with the largest regex up to dateposted in Side Bar WTF
@error said in Checking mobile users in web pages, with the largest regex up to date:
Anyone can access any mailbox @mailinator.com. Whenever a site forces you to give an email address, you can type in whateveryouwant@mailinator.com, go open that mailbox, click to confirm, and forget all about it.
Only to discover the website has blacklisted mailinator (and other receive-only e-mail services) because trolls and spammers use them to register on various forums and post their drivel. I recently learned there are blacklist libraries dedicated to that.
Edit: Looks like I was
 'd quite a bit in saying that. Not enough good reply chains.
'd quite a bit in saying that. Not enough good reply chains. -
RE: The Most Absurd Thing You've Ever Coded/Builtposted in Side Bar WTF
@error When I saw the facebox I thought "This has to be the Onion, right? please?" Hovering the link restored some of my faith in humanity.
-
RE: The Most Absurd Thing You've Ever Coded/Builtposted in Side Bar WTF
@Gurth said in The Most Absurd Thing You've Ever Coded/Built:
Some years ago I had a hard time explaining to someone that if you connected the shafts of an electric motor and a dynamo, then connected them electrically, they wouldn’t keep running. Unfortunately we never did get round to building it.
I remember we had a demonstration of that in physics class: A motor whose shaft is connected to a dynamo, a power source, and a lamp. When you connect the lamp to the dynamo, it slows down the motor, showing the energy is consumed and motor/dynamo couples are not infinite energy generators/multipliers like dwarven pump/waterwheel combos.
-
RE: Close enough securityposted in Side Bar WTF
@JBert Ah, they merely reverse the case. I incorrectly remembered from an older, similar article that they had an all-lowercase version too (and that would lower entropy by as many bits as the password contains letters!)
-
RE: The Most Absurd Thing You've Ever Coded/Builtposted in Side Bar WTF
@levicki said in The Most Absurd Thing You've Ever Coded/Built:
@Mason_Wheeler said in The Most Absurd Thing You've Ever Coded/Built:
Modern disk-oriented archival formats apply compression to individual files and then join the results together into an archive, so extracting subsets of the archive is trivial.
Those that are worth using don't, because storing individual files is reducing the compression ratio for no good reason.
(snip picture)
Solid archiving is a thing, if your computer isn't manly enough to handle it then I guess you can keep using that crap called ZIP and I'll stick to using LZMA2 compression and solid archives with large dictionary sizes to actually, you know, compress things.On the other hand, I don't think modern solid archivers compress the file list along with the rest, so unlike compressed tarballs you don't need to read and decompress the whole file to get the file list.