Excuse me? Do you have any idea how telecommunication companies work?
-
-
@codejunkie T-Mobile Austria has to be a fake joke account right? Right? Even if that existed, it wouldn't be tweeting in English... right?
-
Sadly, it appears to be legit.
-
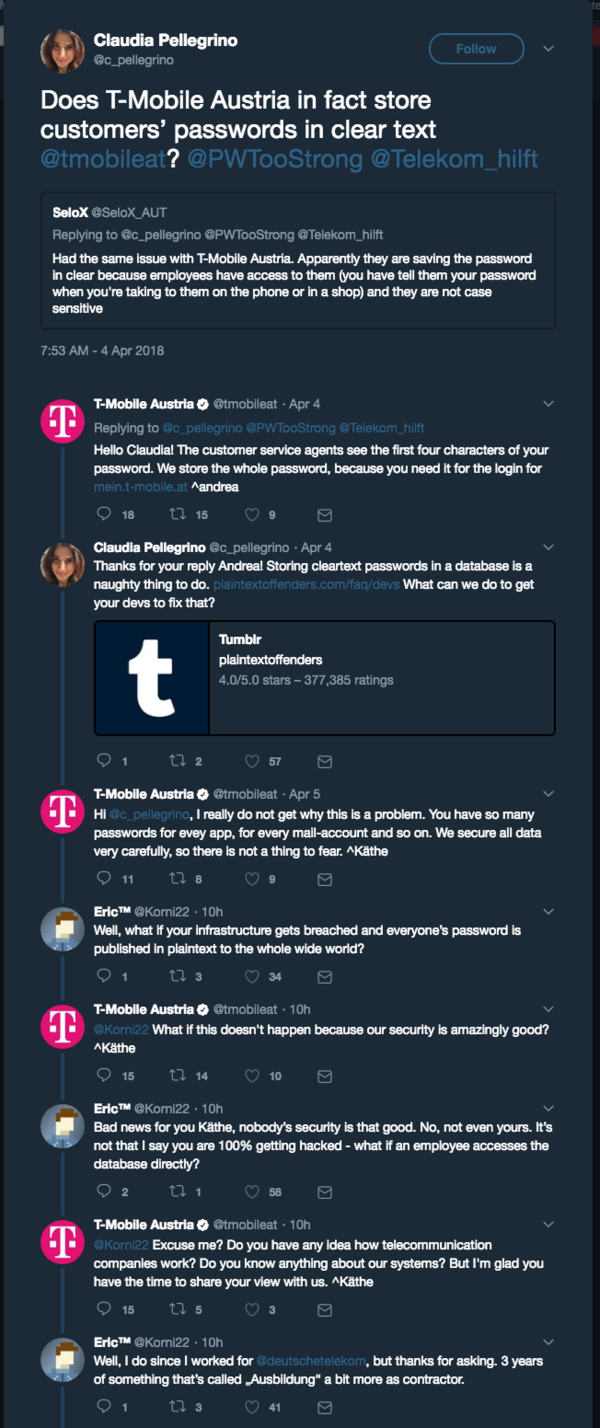
For context:
-
Taking bets on when T-Mobile gets major data leak.
-
Hell, they don't need a data breach. Their employees can be easily talked into moving a phone number to a new phone. In another state. (Happened to my coworker - and then all the 2FA shit is for shit. He discovered when his bank account was drained. Luckily, got that all restored. T-Mobile's solution - get a new phone number.)
-
Christ on a cupcake. There's 'incompetent' and then there's 'flat-out retarded'.
-
@dcon I used to work at phone dealership in USA, so I know first-hand how horribly insecure moving the number is.
-
"lmao you can't hack us idiot we got Norton"
-
@anonymous234 fool, everyone knows McAfee is superior! not even the hackers can uninstall it
-
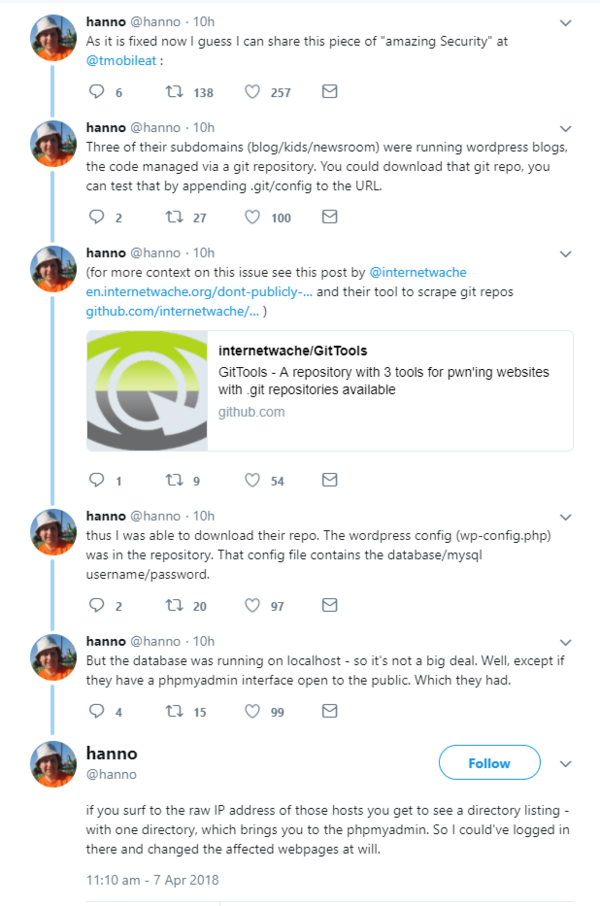
Bonus round: The Streisand Effect in action — security researchers are taking note of this and giving them "free penetration tests"

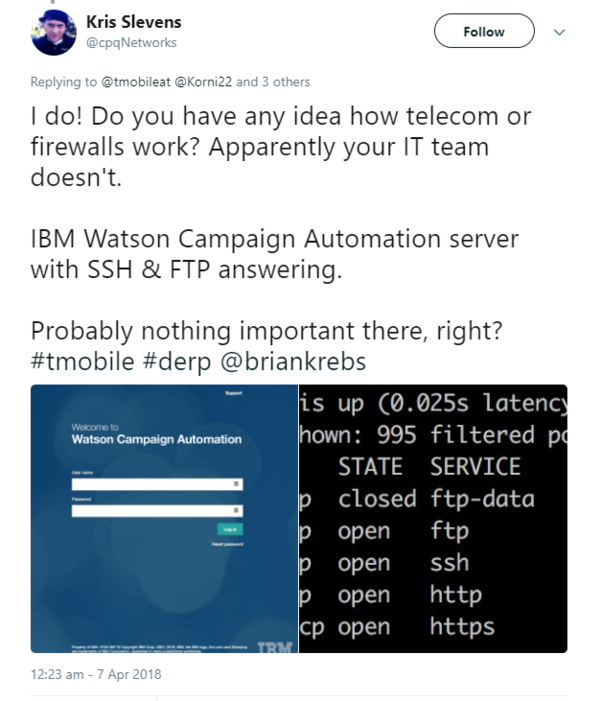
Source: @cpqNetworks
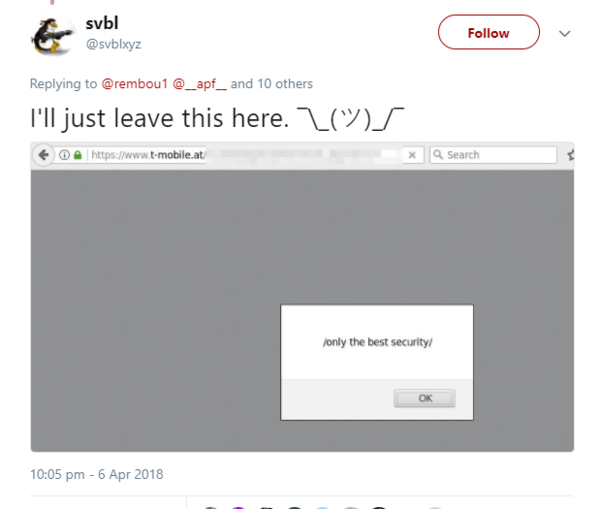
Source: @svblxyz
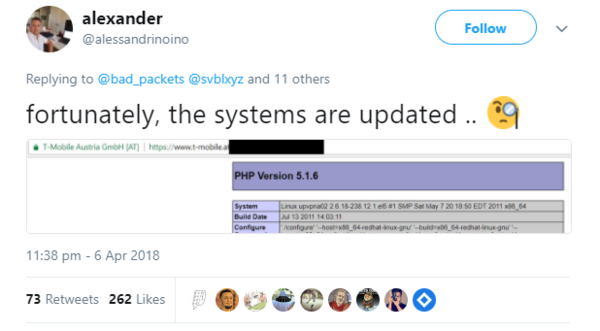
Source: @alessandrinoino
(For reference: PHP 5.1.6 is the last release of 5.1.x line, it was released on 24 Aug 2006 and end-of-lifed on 02 Nov 2006 with the release of 5.2.0 . They appear to be running it on RHEL 5.6, which was released on 13 Jan 2011 and dropped from support on 31 Jul 2013.)
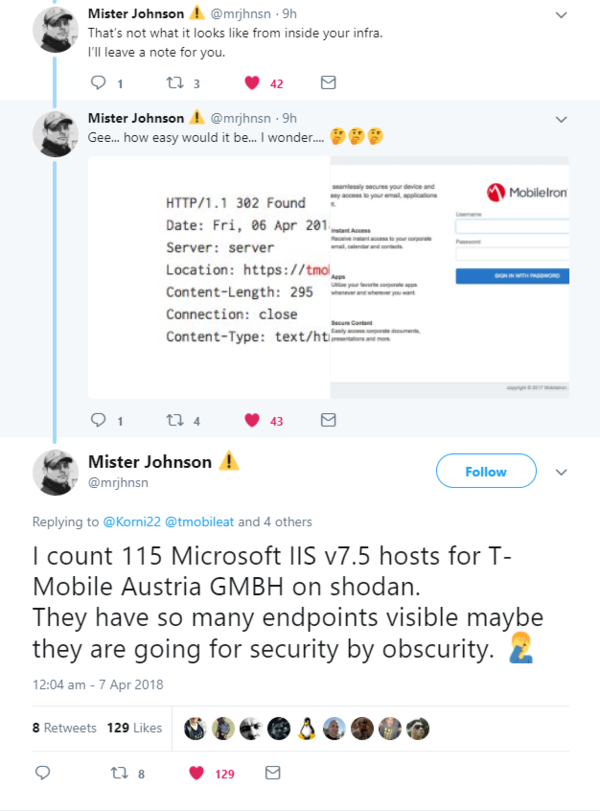
Source: @mrjhnsn
And of course the mic drops:

Source: @robin7331
-
T-Mobile. Ah, I remember my days of working in telco and interacting with those turdmuchers fondly. The fond bit is that I no longer interact with them. As I got to fix the mess that various telcos made for themselves with their servers, I know for a fact that T-mobile isn't really any worse than the rest in this particular instance. There is an impressive lack of IT skills in telco. Or was, it's been a few years now.
-
@carnage said in Excuse me? Do you have any idea how telecommunication companies work?:
There is an impressive lack of IT skills in
telcoour industry in general.FTFY
-
@carnage said in Excuse me? Do you have any idea how telecommunication companies work?:
Ah, I remember my days of working in telco and interacting with those turdmuchers fondly.
I see. So you I guess it's safe to say you have a pretty good idea of how telecommunications companies work!
-
Then there are other ways to profit from this:
EDIT: And yes, I know that Verizon Wireless might or might not serve Austria, but it does look like they're trying to steal customers
-
@gąska said in Excuse me? Do you have any idea how telecommunication companies work?:
@carnage said in Excuse me? Do you have any idea how telecommunication companies work?:
There is an impressive lack of IT skills in
telcoour industry in general.FTFY
Not that IT in general is a shining beacon of sanity, but telco is worse in my experience.
-
@carnage Telcos make billions while providing the shittiest service imaginable by exploiting government granted monopolies (frequency allocations) and network effects (the ridiculously overpriced century old telephone network). They are all scum.
-
As someone who deals with telcos daily, I can just nod in dismay at all of this.
For the record, their local branch here is no better, they have no idea what they are doing, on every level of the process. Sales reps have no idea what they are selling, their managers have no idea on gathering customer requirements, and their techs are (mostly) clueless about anything past "well, the router responds to ping!".
Every install I ever did for any of their clients had some sort of an issue that took 1-2 days to resolve in the best case scenario, and it was always for a different reason. And no, me providing them with precise information about the problem, down to sending them traces with parameters they set wrong in red fucking letters didn't help much.
-
@lb_ Time to find out if T-Mobile US is in any way similar; if it is, I'm jumping ship.
-
@jbert said in Excuse me? Do you have any idea how telecommunication companies work?:
Then there are other ways to profit from this:
Indeed. Very similar story when Bank of America announced debit card fees, I switched to another bank that looked good; when I was on hold with them, one of the messages was basically, "Hey, apropos of nothing... we've never charged debit card fees and we never, ever will. Just in case you were wondering. :>"
-
-
@dcoder I think T-Mobile <Austr
alia is learning that shoddy security sometimes works, but only if you don't make yourself a target. Claiming superior security makes you a target.
-
@heterodox I suspect T-Mobile Austria is learning that lesson too. At least I hope they are...
-
@dcoder Inb4 they sue this guy and everyone else in that twitter thread for hacking.
-
@anonymous234 said in Excuse me? Do you have any idea how telecommunication companies work?:
@dcoder Inb4 they sue this guy and everyone else in that twitter thread for hacking.
INB4
-
@heterodox said in Excuse me? Do you have any idea how telecommunication companies work?:
@dcoder I think T-Mobile <Austr
alia is learning that shoddy security sometimes works, but only if you don't make yourself a target. Claiming superior security makes you a target.I can guarantee that T-Mobile Australia is not learning that lesson because T-Mobile Australia doesn't exist. The quota of telco stupidity in Australia is filled wholly by Telstra. And I know for a fact that they keep passwords in plaintext too because they'll happily text it to you should you forget it...
-
@deadfast Betcha they don't when this is all over.
-
@pie_flavor said in Excuse me? Do you have any idea how telecommunication companies work?:
@deadfast Betcha they don't when this is all over.
Hahaha. Don't hold your breath.
-
@Deadfast I would suspect it's been that way since 1975/07/01. If nothing has made them change yet, I doubt anything will.
-
Continuing the "telecom companies suck" trend, Vodafone Portugal brazenly MITMs all your traffic "for security reasons", and whitelists their own scripts:
@VodafonePT is rewriting CSP headers to whitelist http://vodafone.pt and http://jquery.com in the script-src directive. Basically, it means that this is a terrible company, using MITM technics. Don't let them do that.
cc @JornalNoticias
Source: @JackyHallyday
Basically, if your site is security-conscious and uses Content Security Policy to say "on this page, do not execute any javascript from sources other than www.goodsite.com and www.jquery.com", Vodafone will quietly change those headers to say "yeah, allow javascript from vodafone.pt as well".
One more reason to run everything over TLS with strict certificate checking?
-
@dcoder said in Excuse me? Do you have any idea how telecommunication companies work?:
Continuing the "telecom companies suck" trend, Vodafone Portugal brazenly MITMs all your traffic "for security reasons", and whitelists their own scripts:
@VodafonePT is rewriting CSP headers to whitelist http://vodafone.pt and http://jquery.com in the script-src directive. Basically, it means that this is a terrible company, using MITM technics. Don't let them do that.
cc @JornalNoticias
Source: @JackyHallyday
Basically, if your site is security-conscious and uses Content Security Policy to say "on this page, do not execute any javascript from sources other than www.goodsite.com and www.jquery.com", Vodafone will quietly change those headers to say "yeah, allow javascript from vodafone.pt as well".
One more reason to run everything over TLS with strict certificate checking?
Similarly, Optus will inject your phone number to certain websites.
-
Looks like there's a new PR person active to do the cleanup:
-
@jbert said in Excuse me? Do you have any idea how telecommunication companies work?:
Looks like there's a new PR person active to do the cleanup:
It's interresting how nothing in that tweet actually disputes that they are saving passwords in plaintext.
Dtabases encrypted? Well, that's gonna do fuck all if someone breaches security to the point of having access to the database. At that point they probably also have access to encryption keys.And considering the complete trainwreck of security that has been unveiled after the support drone idiot taunted the combined forces of the internet by proclaiming T-Mobile to be unassailable, I'd say that the database is most definately not encrypted.
-
TMOBILEAT uses NEW PR! It's not very effective...
@carnage said in Excuse me? Do you have any idea how telecommunication companies work?:
It's interresting how nothing in that tweet actually disputes that they are saving passwords in plaintext.
Quite. "Databases are encrypted" is code for "We either STILL don't understand or we don't care about our users' concerns, pivot pivot and hope they go away."
-
Meanwhile, over the border in Deutschland:
individual passwords are reversibly encrypted
-
@pjh said in Excuse me? Do you have any idea how telecommunication companies work?:
Meanwhile, over the border in Deutschland:
individual passwords are reversibly encrypted
Well, that's just great!
Now let's hope they anger the internet hive-mind and get their systems probed and prodded and all their dirty laundry hung to try in public as well, because I am certain that they are no better than their Austrian counterpart. And if that is the case, the encryption is worth precisely fuck all. And I'd not be the least surprised if you can grab the keys from some JS frontend that is accessable publicly. :D
-
Meanwhile, re my earlier question:
“T-Mobile US applies strong security controls to customer passwords or PIN codes,” T-Mo told me in an e-mailed statement. “T-Mobile US customer care representatives cannot see passwords, and we do not store passwords in plain text.”
Now T-Mobile Austria has poisoned the well for everyone, because I note that does not specifically say that passwords are hashed.
-
@heterodox quoted in Excuse me? Do you have any idea how telecommunication companies work?:
T-Mobile US customer care representatives cannot see passwords
But I bet other employees can. From the German Tweet above, they imply much the same thing:
Our customer service does not have access to plaintext passwords.
-
@jbert said in Excuse me? Do you have any idea how telecommunication companies work?:
Looks like there's a new PR person active to do the cleanup:
Top fucking kek. There is no data breach, huh? If I were you, I would classify all the white hats who helpfully pointed out the myriad ways they could cause a data breach easily, especially the ones who were a button click away, as 'having a data breach', because a single one of them actually clicking that button instead of mocking you for it on Twitter would have been a data breach.
-
@dcoder said in Excuse me? Do you have any idea how telecommunication companies work?:
using MITM technics.
The company that makes record players?
... oh I guess he meant techniques.
-
@blakeyrat said in Excuse me? Do you have any idea how telecommunication companies work?:
@dcoder said in Excuse me? Do you have any idea how telecommunication companies work?:
using MITM technics.
The company that makes record players?
... oh I guess he meant techniques.
Man in the middle record players
You need to hire someone to hold up the record and spin it under the needle
-
I'm patiently waiting for them to get compromised

-
@ben_lubar said in Excuse me? Do you have any idea how telecommunication companies work?:
Man in the middle record
players
-
@zmaster said in Excuse me? Do you have any idea how telecommunication companies work?:
I'm patiently waiting for them to get compromised

Don't worry. The moment the tweet detailing that their database was connected to the public internet was published, they were compromised by a host of nefarious groups. That they have not discovered it yet means fuck all, and is entirely in line with how they have their systems set up.
Coincidentally, while I was a magicworker that dealt with telcos I came across a problem one of the largest ones in the world had with their systems, that they were not communicating as expected. The timing was strange, and they kept getting warnings from the systems. I got logged in, and after a small bit of digging discovered that their internal network routing was completely fubard, and no internal network worked because the routing system had broken down a couple of months ago so a new one was plugged in and never configured.
So how did their internal systems work at all you wonder? Each and every machine had a network card connected directly to the internet. The servers, holding every last bit of information the company had about customers was talking to eachother, unencrypted, over the open internet. Anyone that took the time to listen in and reverse engineer the data could send requests to the systems for any information they pleased, as they also had not activated any of the security measures. Because that would have been too hard.Telcos, I do not trust them to be secure (rather, I trust them to not be secure) , because I've seen how fucking dumb they are first hand.
-
-
@deadfast This is actually really convenient. This way if you know somebody who uses Optus and you have their phone number you can basically get free services that are billed to that person.
A phone number is a fine way of identifying somebody, since they are designed to be kept secret. I mean, you're not giving out your phone number to anyone you don't completely and implicitly trust?
-
@martijntje the security of a phone number comes from the fact that you are the only one able to receive and make calls/text messages through that number. It's not just that you know the number - you are in physical possession of the only communications device with that number, so the only way they could authenticate as you via phone is if they physically steal the phone from you.
That's the theory.
-
@gąska said in Excuse me? Do you have any idea how telecommunication companies work?:
That's the theory.
... And unfortunately, that theory is incorrect. Landlines are generally insecure for obvious reasons. Also, most switches - landline, mobile, VoIP, whatever - are software switches now; thus, if you have the right social engineering skills and/or access to a network with a given phone number, you can forward/redirect/intercept calls to/from that number without having to physically do anything.
-
@lolwhat not to mention having two lines with the exact same phone number ACTUALLY HAPPENS.
-
@lolwhat And I don't think mobile voice/SMS is eve encrypted so you can eavesdrop it if you're near the device?

 T-Mobile US does not store customer passwords in plain text
T-Mobile US does not store customer passwords in plain text

 T-Mobile bug let anyone see any customer's account details
T-Mobile bug let anyone see any customer's account details
