Certification that's Impossible to Verify is TRWTF
-
Our company is planning a new dev project and part of it will be outsourced (Yes! WTF#1, but not TRWTF). Said dev company claims various accreditation, so I ask them to produce it. Lo and behold, they actually do. They provide me with photos of all the certificates. Notbad.jpg.
So, first up: they are claiming compliance with ISO XYZ, certified by company A? Alright; time to go to Company A's website and check this. What? No way to verify a certificate with a registration number or certificate ID? Bah... I'll fire off an email to them.
Second: they claim compliance with ISO ABC certified by company B. Same process, and this time I'm greeted with a website that was last touched in around 2000, but it just about works. I am able to enter the certificate number and... I just get back an empty form. Is that correct? I try a few more things. Then, just for the hell of it, I try entering
' OR 1=1--and I am presented with a Connection Reset browser error. Nice! Getting somewhere... I go back and change it to' OR 1<2and...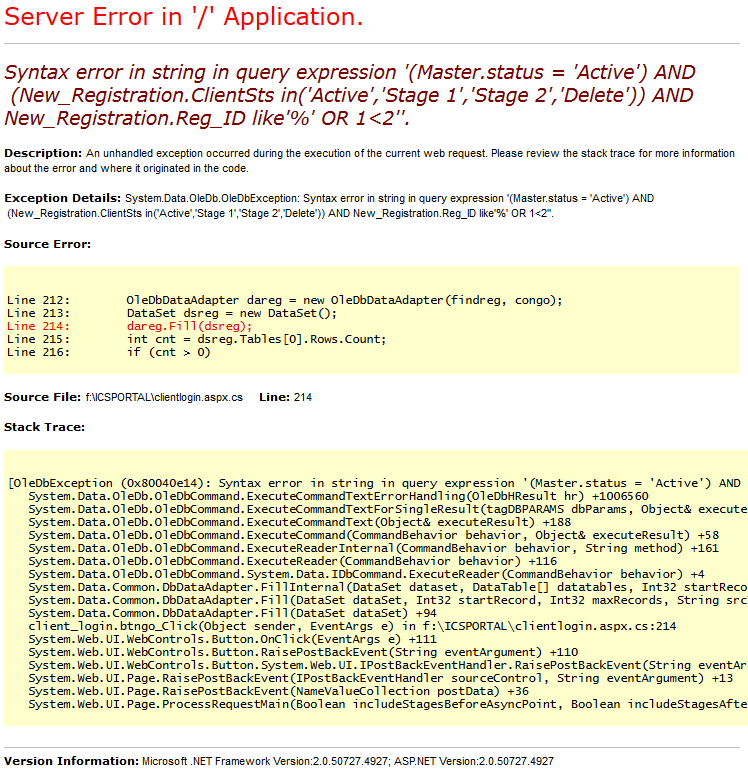
Sweet... So we can see they tried to prevent SQL injection by looking for
1=1but not actually using parameters etc. That's a pretty neat fail, but OK, I honestly don't have time to mess around with this any further. The important thing is that I can see there is aLIKE '%'in there, so I try a substring of my given certificate ID and presto! It works, and shows me what I want to see.So, finally, I see they claim they are a Microsoft Certified Partner. So cue half an hour of searching for a way to check this. Nope. Neither Microsoft nor Google know nothing about it (lost count of the number of useless outdated Microsoft sub-sites I've seen over the years that are still up). But the final blow to my sanity is the 'certificates' they give to the companies. They are actually glass/plastic/metal plaques that look pretty nice, and are stamped with whatever specializations your company has. They vary from year to year, but they look similar to that below...

However, do you spot a potential problem? Go on; take another look. I'll wait.
...
...Yeah... I have no way to verify this plaque actually belongs to said company, because there is no fucking company name or registration number anywhere on it.
So, I'm shocked to say, in this particular case, Microsoft is more of a WTF than SQL injection.
-
they are claiming compliance with ISO XYZ, certified by company A
they claim compliance with ISO ABC certified by company B
I just checked and neither of these are real ISO codes, so I think they may be lying to you. Also, the company names are very suspicious.
-
I assure you that those companies are legit. Mr. Bobby Tables himself sits on the board of directors for both of them.
-
Sweet... So we can see they tried to prevent SQL injection by looking for 1=1 but not actually using parameters etc.
WTF? You either don't know about SQL injection and just use the naive string substitution, or you know and use parameters. Who would think the correct method is to check the input for all possible forms of attacks?
RE certificates. Are these things even worth checking? Feels like some kind of bureaucratic racketeering against the little guys.
-
Who would think the correct method is to check the input for all possible forms of attacks?
Looks around
Looks at the post editorHello!
-
RE certificates. Are these things even worth checking? Feels like some kind of bureaucratic racketeering against the little guys.
Good question. There is actually no red tape in place that forces me to do this, but since I'll be dealing with their devs directly, I want to scrutinize them as far as reasonably possible. They made claims about conformance, so I was sure to check it. If they couldn't back it up, it would be a red flag and a good reason to drop them.
-
Good question. There is actually no red tape in place that forces me to do this, but since I'll be dealing with their devs directly, I want to scrutinize them as far as reasonably possible. They made claims about conformance, so I was sure to check it. If they couldn't back it up, it would be a red flag and a good reason to drop them.
Fair enough, I was just asking in general.
-
If the MS Partner award/certification "trophy" is similar to the MVP Award, it is not going to have that information. However, the information should be on the actual certificate. For example MVP Awardee's have their full name on all award certificates, so that can be used to verify that a person did indeed receive it, but there is nothing that would "map" the trophy/award thing that they receive to them, I'd suspect they use a similar method for the Partners- a "Trophy" like the one pictured, but an actual certificate as well.
If you want to verify that a company is a Microsoft Certified Partner you should be able to search the MS Partner site for the company:
-
What do you expect? They're fictitious* business names.
* which evidently has an interesting connotation to it
-
https://mspartner.microsoft.com
Yeah, I went there. I went back again, but still can't find what I'm looking for... something that actually lists their licensed companies or allows me to search by company name.
-
WTF? You either don't know about SQL injection and just use the naive string substitution, or you know and use parameters. Who would think the correct method is to check the input for all possible forms of attacks?
Either they didn't understand, but had gotten reports, or they just didn't want to go through the full effort of a real fix and figured covering the most common case was good enough, or at least better than what they had. I know I've made those sorts of trade offs before (though not with respect to SQL injection).
-
Either they didn't understand, but had gotten reports, or they just didn't want to go through the full effort of a real fix and figured covering the most common case was good enough, or at least better than what they had.
PEN tester: Ummm... you know guys, if I pass in this string I can screw up your database.
Devs: It's ok. We'll just ban it.
-
PEN tester: Ummm... you know guys, if I pass in this string I can screw up your database.
Devs: It's ok. We'll just ban it.That's basically how it works, yes, because that's cheaper than Doing It Right™
It certainly seems to be kind of how the Discourse way is too...
-
Only we're the main pen testers.
Blakey was right, we should've sent in an invoice.
-
-
-
Do you fart in their general direction?
-
Mixing shows here but sure, I can do that too.
-
Blakey was right, we should've sent in an invoice.
(by the way, Ruby is equally retarded in that its redirect handling logic boils to
while (url not in visited_urls) follow_redirect();, and it doesn't even time out gracefully)
-
I did not, I retain my right to invoice.
