Http://a/%%30%30 crashes Chrome
-
But at least with the crash in Go, it gives you an error message with a specific line to check, whereas Chrome just says "oops" and then crashes more.
Apples and oranges.
You're comparing Go (the programming language/compiler) to Chrome (the web browser)?
I think the "oops" page was placed there intentionally to hide the debug details from the user.
At the very least, check Chrome's [debug] log.Disclaimer: I stopped liking Chrome some time ago and I do like Go, but this is a case of pedantic dickweedery!

-
Too bad Google's search isn't more robust. Because then I could search for pages containing this URL, and see how many instances there are of people dropping "fuck you Chrome" stinkbombs all across the Internet.
-
Explanation:
Looking into the DCHECK failure, this arises because of the following sequence:
- An input string "http://a.com/%00" is unescaped to "http://a.com/" and considered a valid GURL.
- This GURL is eventually sent to GURLToDatabaseURL(), which calls ReplaceComponents() on it to strip the username and password.
- ReplaceComponents() re-canonicalizes the URL.
- Canonicalization of the path hits the "%00" sequence, unescapes, sees this is a 0 char which is invalid in URLs, leaves it escaped, but marks the resulting URL as invalid.
- Once we return back to GURLToDatabaseURL(), it calls .spec() on the new URL, expecting it to be valid, since the input URL was guaranteed to be valid and we merely removed the username and password. This DCHECKs.
It's not clear to me where in this sequence the bug lies. The key seems to be that we unescape the input URL to a form that looks as if it's still escaped, and the canonicalization code aggressively tries to unescape again. One possible fix would be that unescaping could always try to recurse until no further unescaping was possible, but I'm not convinced this is correct.
Another possibility would be to bandaid this so GURLToDatabaseURL() calls possibly_invalid_spec() instead. This would fix this DCHECK, but it leaves the underlying issue that we have a valid unescaped URL that looks like an invalid escaped URL.
I'm sure the other crashes are caused by this same problem -- something auto-canonicalizes this URL and marks it invalid, leading to bugs -- but I'm having a hard time debugging because Visual Studio is crashing literally every time I try to debug for more than a minute.
Game:
-
So it's yet another double-interpretation bug. Bobby Tables works for Google's Chrome team now…
-
marks the resulting URL as invalid
the input URL was guaranteed to be valid
I found the bug.
-
<img class=fa-spin src=https://what.thedailywtf.com//uploads/default/8214/16c00f5bd6b57125.png/>
<img class=fa-spin src=https://what.thedailywtf.com//uploads/default/8214/16c00f5bd6b57125.png/>
Filed under: [Discourse!](#tag)
-
I think we've found a new tag cloud to attack.
Filed Under: We need a new tag cloud to attack
-
Belgium.
Discourse eats the link in an a...
-
Oh belgian belgium.
Filed Under: Doing It Wrong, Links Must Match Specs, CLOSED_WONTFIX_NOTABUG
-
Well aren't you clever.
-
Did I miss something? Since when do we have working XSS again? Not that I'm complaining.
-
Since September 8. I believe it is the first fix that we do not get.
Here's an impractical application: https://what.thedailywtf.com/t/in-which-ben-lubar-possibly-asks-for-and-is-awarded-an-xss-badger/51031/101
Here's a practical application: https://what.thedailywtf.com/t/in-which-ben-lubar-possibly-asks-for-and-is-awarded-an-xss-badger/51031/116
-
$.ajax({url:'http://a/%00'}); best method of crashing current tab. only effects chrome, so firefox users won't even know what was attempted.
-
Hey now, the evil ideas thread is NOT THE FUCK HERE
-
ftp://a/%%300 works and is the shortest method for links (except on this site.......................)
-
This post is deleted!
-
avoid crash game
You mean this one?:
Game:
-
Or This one
-
oh..
-
I watched as you tried to fix that up

-
Fuck markdown
-
Filed Under: Do the
[s go first, or is it the(s... and is it the URL or the text first? Fukkit I'll just go with a<a>
-
So it's yet another double-interpretation bug.
Everyone who writes code that leads to that kind of bug needs to read this article:
-
Boo. Chrome doesn't support Gopher.. So gopher://a/%%30%30 is safe.
Filed under: I wonder if Archie works...
-
I can't view the post this is in reply to without my browser crashing.
-
So here's discoursistency, clicking the link on android is safe, click and holding to bring up the nav menu to open in a new tab will crash the browser.
-
I'll just note that, while hovering over the link in the OP did indeed crash my Chrome tab, I had to view this thread in Chrome because IE seems unable to render it at all (five attempts over the course of several minutes have all resulted in a completely blank page).
Usually the only reason I have to view a WTDWTF thread in Chrome is because someone has used a somewhat exotic Unicode character and IE refuses to acknowledge that it exists (scroll down, long pause when it is about to come into view, then suddenly jump far enough down that the offending character is now off the top of the screen. Similar behaviour in reverse when scrolling up.)
-
five attempts over the course of several minutes have all resulted in a completely blank page
?
-
Still happens if I try to view the top of the thread, but I can jump in lower down OK. Must be something in the first $n posts that IE doesn't like.
Edit: I can view from post 7, but not from earlier. If I start from post 7 and scroll up, I can see everything except the OP, which infinispins.
-
At first I was like "ha ha, gopher in Chrome", but most of those comments seem serious o_O
-
refuses to acknowledge that it exists
I don't mind at all if something doesn't know everything (nobody and nothing within this world does), but I hate if something believes it did know everything, and be it in one field that is not finite and finalized by definition and globally accepted standards.
(Example: when I tested Star Office's HTML editor in 1999, it silently deleted all HTML tags it didn't recognize, no matter how W3C acknowledged they were.)
-
Whelp, looks like it's patched already?
Darn, it was kinda exciting...
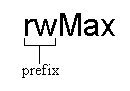
 Making Wrong Code Look Wrong
Making Wrong Code Look Wrong