At least they used bcrypt?
Best posts made by rad131304
-
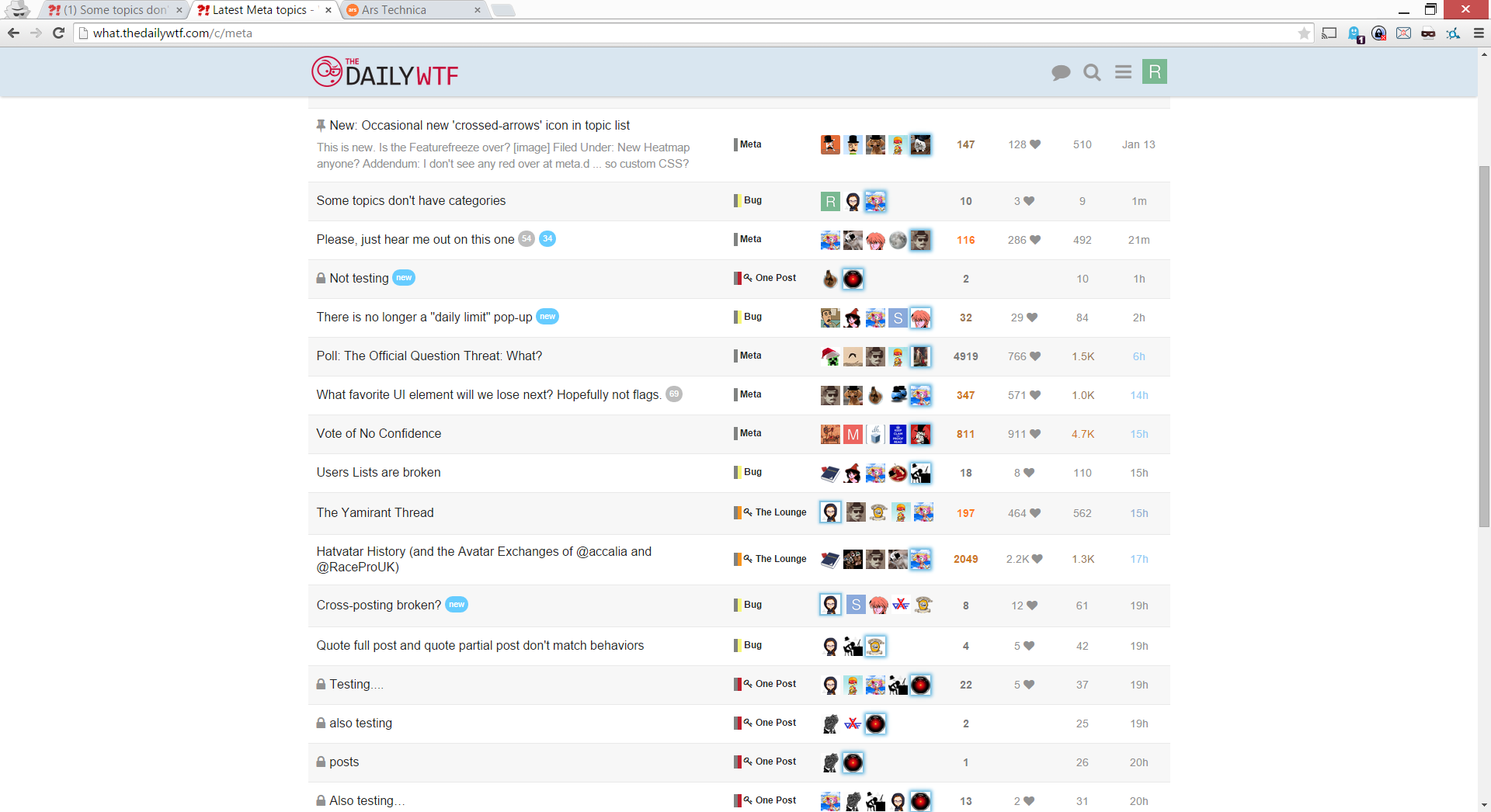
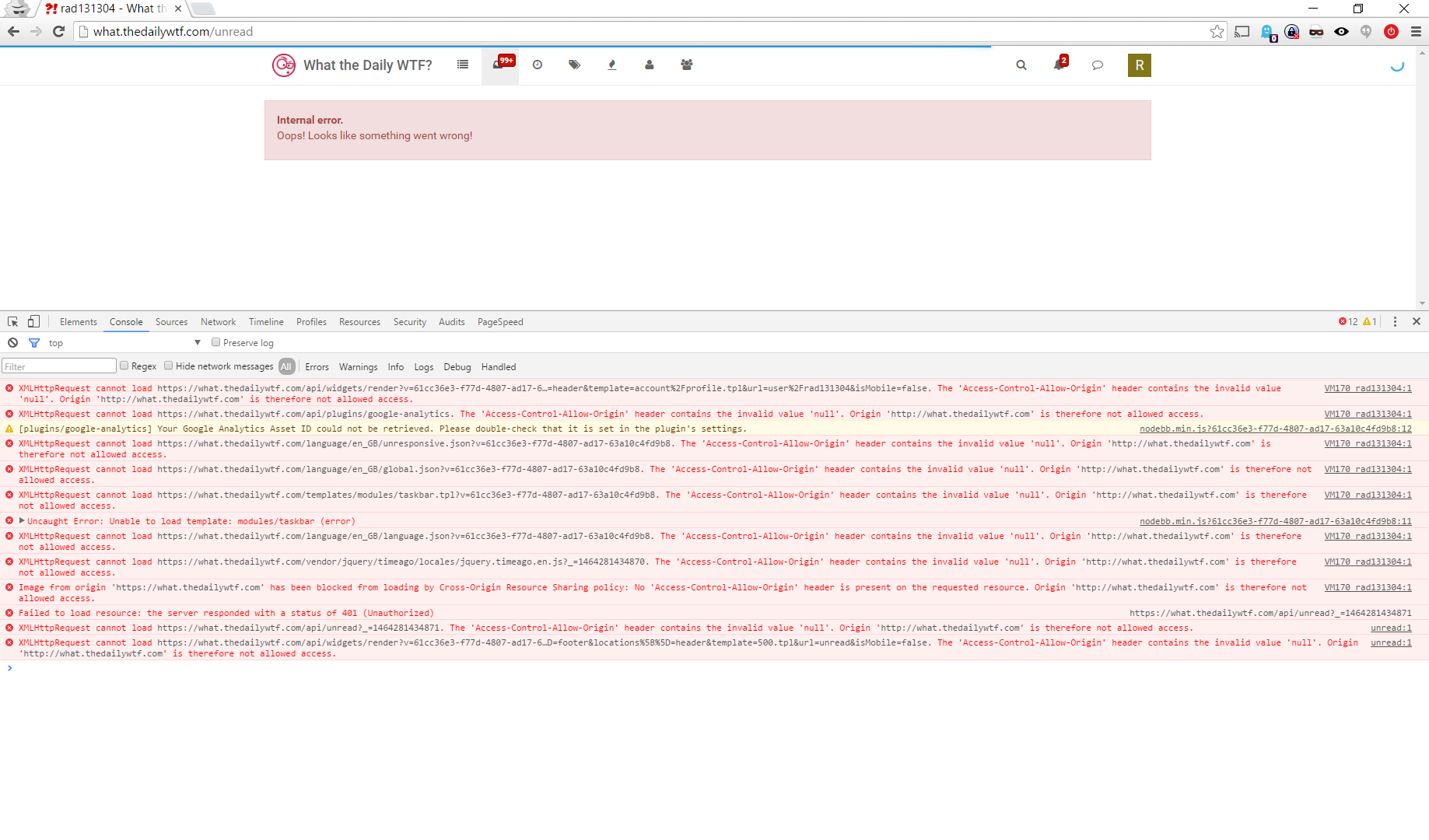
Access-Control-Origin Header Bugposted in Bugs
Expected:
Things Work
Actual:
When navigating way from profile page, Errors abound!
Steps to Reproduce:
OS: Windows 10 Home
Browser: Chrome latest
Possibly Important Plugins: Ghostery:latest; Google Optouts:latest; HTTPS Everywhere:latest
Other: Porn Mode (a.k.a. Incognito)- Open Chrome.
- Browse to WTDWTF
- Log In
- Click on Mailbox link
-
RE: Discourse sucksposted in General
Continuing the discussion from Please stop poking holes in our cardboard security!:
as i recall.... yes.
:large_purple_dildo: was rejected.
or am i misremembering that it was ever brought up as an option?
Discourse chased away all the people who made the purple dildo jokes, so there's no point having an emote for it.
Discourse sucks.
AFAIK neither @dhromed nor @morbiuswilters rage-quit like you. They're probably just busy doing things other than compiling code.
Edit: INB4 a potential blakeyrant because the above is ambiguous - I meant it as a comparison; i wasn't trying to provoke an argument
Filed Under: 303
-
RE: [BYDESIGN] Sign Up Button Disappears After Scrolling In Threadposted in Bugs
Heaven forbid people read some of a thread before deciding they want to sign up and participate?
-
RE: The bad jokes topic 🐴🍹👨posted in General
@rad131304 said:
Ok - I was just confused by the response -
that keeps happening around me.... I'm not sure if that's because i'm going it epically wrong or epically right....
all of the above?
-
RE: Dev tools worth buying for myself?posted in General
@xaade If you're a USian, you can claim the purchase on your taxes as an unreimbursed expense ... assuming you itemize.
-
RE: So, Windows has more linux in it these daysposted in General
We talked about this during the W10 beta:
https://what.thedailywtf.com/t/windows-10-gets-package-manager/4426
-
RE: WTF is happening with Windows 10? And nothing elseposted in Megatopics
My argument has been made. I'm not the one who thinks that any SoC can easily be updated with a new kernel, and that the failure to do so means you have a different fork of the code.
- Both Windows RT and Windows 10 Mobile can target the ARMv7 architecture.
- As I understand, Windows 8 Phone and Windows RT contained the same kernel, but the drivers/UI/etc. on top were different.
- As I understand, the resource requirements for Windows 10 Mobile do not preclude, per-se, all Windows RT devices from being able to receive Windows 10 Mobile
- No device currently using Windows RT is getting Windows 10 Mobile.
You said:
Windows RT is just getting a new name.
If that were true, a full wipe and update would be possible on Windows RT devices. Clearly something prevents the device from being upgraded. I don't know what that is. Unless you've got a connection at Microsoft you haven't yet quoted directly, you don't know what that is either. But, given the available evidence, Windows 10 Mobile is more likely to be an update to Windows 8 Phone. Both Windows 8 Phone and Windows RT probably shared a lot of code since it looks like they shared a kernel, but Windows 10 Mobile is not an upgrade to Windows RT. If it were, Windows RT devices would be able to upgrade if their specs were good enough to run the OS.
Windows RT HAS NO UPGRADE PATH TO WINDOWS 10 MOBILE. Microsoft said this. It will get some features, but it will never be on Windows 10 Mobile. They did not say it was because the devices were incapable of supporting it due to SOC incompatibility. The CPU architecture targeted is the same (ARMv7) so it's not an SOC incompatibility unless the drivers for Kernel 6.2 are incompatible with Kernel 6.3 - which would be strange given how MS numbers their Kernel versions (since sub-numberings usually indicate general compatibility unless a bug is fixed which breaks a driver).
I still don't understand how the end of a build path because the build is not possible with the current source is not an orphaning of the build path.
Unless all Windows RT ARMv7 chipsets aren't actually ARMv7 compatible, your SOC argument sounds really uninformed.
-
RE: WTF is happening with Windows 10? And nothing elseposted in Megatopics
This is what I've been saying. All I get in response is "BUT SURFACE RT CANT UPDATE TO 10 SO WINDOWS RT IS ORPHANED!!!"... no, it's just renamed. It's part of Windows 10. Devices being orphaned != an OS being orphaned.
No, what you're getting is no Windows RT is getting updated so that fork of the OS is being orphaned. It doesn't matter how much of the code gets reused if the OS path is a dead end. Stop being so obtuse.
-
RE: WTF is happening with Windows 10? And nothing elseposted in Megatopics
@aliceif said:
Either way, MicroSoft fuck over existing Windows RT users, don't they?
Yes, all 8 of them.
Microsoft would build an upgrade path
What I'm saying is that they probably didn't build it in right. They didn't build in an upgrade path for windows phone 7, but windows 8 is pretty much just a new version. Once you've made that mistake, what are you going to do? Recall everyone's phones? Give them free hardware?
Except it wasn't - 7 was based on CE and 8 was based on NT.
-
Feature Request: button in top links to display keyboard shortcutsposted in Meta
I know that typing ? in the forum displays keyboard shortcuts - but that's, IMO, not very discoverable. This could easily be made discoverable by putting a ? or a [keyboard][1]* icon in with the menu search and comments bubbles. You could even just put a link in the menu if you are dead set on a minimalist UI.
* I have no idea how to insert unicode text - it's \f11c
[1]: http://fontawesome.io/icon/keyboard-o/ -
RE: The bad jokes topic 🐴🍹👨posted in General
At least end it with Pope raping the little girl, for Christ's sake.
That's the inappropriate jokes thread which is

-
RE: Yet another bug in pollsposted in Bugs
KNOWN_PROBABLYWONTFIX_WHOWOULDDOTHATINREALLIFE
dioraoslrls er vitiyaibeveitpt tc;B e ltyemniddo
A statistician? How else do you make sure that the result comes out the way you want it?
-
RE: Jeff on mayonnaiseposted in General
But, if they use a password that the hash collides with the real password hash, then it doesn't matter. They've already logged in.
Now, they have to do that PER user.
But if they only need one login to do what they need to do, then game over.
But most are looking for the algorithm so they can log into everyone's account.
So anything past 130 no longer protects your own account, but simply protects everyone else's account.
The maximum security of individual accounts on your service is the amount of entropy available in the hash algorithm (assuming you use hash sized per user salts), period. That has nothing to do with the amount of security provided in your database for the set of passwords after it's been stolen because, inevitably, you did something wrong (because the meat sacks always do). They are two separate concerns. The second problem the larger password length could (but probably won't) help you avoid is leaking PII - namely a user/password pair. Most people will probably use a password shorter than your hash algorithm, but why penalize those who want to use longer ones. The goal isn't entropy; it's forcing the thief to waste resources solving the problem. It's the same with key-stretching.
As an aside, if you let someone brute-force throw passwords at your system until they accidentally collide with the "real" password which is longer than your hash, you've got other problems to deal with.
Note: I'm not saying I think you, personally, would mess up your security, I'm saying most security failures are user errors.
-
RE: Windows 10 OOBE Stuck in a Boot Loopposted in General Help
@Tsaukpaetra This is actually just Webroot, and not a Trojan ... unless Dell is selling infected computers. It's a brand new PC.
Whenever old people ask me about computers, I:
- resign myself to the fact I'll never escape their questions, and
- have them buy a non-shitty computer through me.
Since they know me as the "computer young person", I'd at least like to know where the computer started (and capture an image of it).
-
RE: Jeff on mayonnaiseposted in General
If you discover a shorter password that happens to hash the same - it will work. So, you can't really have much more entropy in the password that the hash can retain. You could use that for a maximum password. If you are storing 256 bit hashes, any more than 130 characters in the password will simply result in lost entropy. So, there's your max password length.
Password collisions isn't the issue you're trying to avoid with hashing - the discovery of the actual password BECAUSE of the collision is. If, even with a rainbow table, they can't be sure that the password they recovered is the byte code of the password, the hash collision becomes less useful.
EDIT:
The problem space I'm looking at is: hax0r has all the usernames and p@$$w0rds! because we failed security. Will they recover just the dumb user passwords and use them in other locations, or all user passwords? The shorter password might create a collision here, but it won't if my hash algorithm isn't the one someone else uses. They wouldn't be trolling to use the password against the new target site if they could get in any other way.
I agree that no more entropy is added, but if they have to extend the attack 10x just to get 10 possible passwords, that's a security win, too.
-
RE: Jeff on mayonnaiseposted in General
I'm not so prideful as to never admit my lack of knowledge.
But what I'm saying is that if you use passwords longer than the entropy, you make it that much harder to determine the methodology of the hash.
And therefore you protect everyone.
But if someone manages to brute force your account, having a password longer than the entropy only overlaps onto existing hashes.
You're absolutely correct. The number of possible passwords that produce the hash that will unlock the account goes from 1 to whatever number of hash overflows you allow in the byte space.
The response to this concern is that X/(2Y) is close to 1/(2Y) which is close to 0 as long as Y >> X. In other words chance of a collision on any given hash goes up an incredibly small amount, but the number of potential passwords the attacker is required to check goes up exponentially as long as the number of bytes in your hash is significantly larger than the number of hash overflows. And the result is that, they will have a 1 in X chance of guessing the password because there are X possible solutions. The hash has becomes non-deterministic of the original content used to produce it.
Or there's really not much of a difference between 2 out of one billion odds and 1 out of a billion odds.
-
RE: Visual Studio...posted in General
Put the cursor in the object class name that defines the variable and press Control + .. If the class is defined in the resources, press enter to do the using insert. Works fine for me in VS2013.
e.g.: for
Class instance = new Class();put the cursor in the first
Classtoken. -
RE: Two things I hate when it comes to UXposted in General
The entirety of that information is "look at the screen and do what it says." It's like a free space on a bingo card.
Except at every grocery store I've ever been to, when it's like that xkcd
-
RE: Attack of the Cootiesposted in Meta
How is that relevant? @Blakeyrat got the database for CS afair. I am not saying he has the passwords. I just wanted to make a snarky remark. Maybe he can tell us whether or not he can now post as morbs?

Not my password he doesn't
Swordfish?Filed Under: Either that or it's the date of your birthday!
all I see there is ■■■■■■■■■.
Filed Under: hunter2
-
RE: Vote of No Confidenceposted in Meta
Filed under: Did you mean recursion?
Nope, I was talking about recursion
-
RE: Hydrogen Vehicles - Truly Beneficial?posted in General
Hydrogen is the fuel of the future, and it always will be
- Unknown
The main problem is that our current best source of hydrogen is natural gas. Hydrogen fuel has a lower energy density (0.01005 MJ/L) than natural gas (0.0364 MJ/L), it takes energy to separate the hydrogen from the natural gas, we already have an infrastructure to distribute natural gas to homes, and we have fuel cells that work with natural gas.
Why would I want to use hydrogen?
-
RE: Vote of No Confidenceposted in Meta
The correct response is: "Raisins".
EDIT: How is Raisins not in the Discopædia?
-
RE: You merely adopted the 500. I was born in it, molded by it. I didn't see a fully rendered Discourse page until I was already a manposted in Meta
Look, the real problem here is that all of those crappy old forums that Discourse devs make fun of have NO PROBLEM changing avatars.
This is just yet another embarrassing bug. Community Server even did this right, and it didn't do anything right.
Extremely embarrassing.
BUT WE MUST REBAKE ALL THE THINGS!
-
RE: You merely adopted the 500. I was born in it, molded by it. I didn't see a fully rendered Discourse page until I was already a manposted in Meta
But then it would take N days till you see brand new avatars we can not set expiry to 0
Have you not heard of ETag?
-
RE: This is why we can't have nice wireless things in the USA ....posted in Side Bar WTF
Pretty much.
If you want the FCC to address it, talk to the FCC. Don't blame Verizon or T-Mobile for making use of their legal rights.
This is like the people in the open source world who gives away their products for free, then bitch that companies don't "give back". Well, why should they? If you wanted that, you should have put that in your license, idiot.
You assume I don't file complaints or petitions with the FCC, how cute.
-
RE: Break out *all* the popcorn!posted in Side Bar WTF
Tl;dr version: Three lawyers and a "computer scientist" buy up rights to porn films, then file suit against hundreds of thousands of people who allegedly torrented the movies, thousands per suit, in different courts. The suits are designed to get names and addresses and blackmail them for about three grand a pop. They fuck up a number of different ways, including:
- Not even trying to verify there's a jurisdictional nexus
- Dodging court fees by suing thousands at a time (improper joinder)
- Suing in places they're not admitted to practice, hiring local attorneys as mouthpieces, and not letting them do their jobs
- Not showing up for court appearances
- Not actually getting the copyright for the movies they're suing over
- Not verifying that the person they're suing actually downloaded anything, or even anyone in the same building
- Making one lawyer's housekeeper the CEO and only employee of the alleged company behind these lawsuits, without knowledge, consent, or compensation
- Failing to disclose that they themselves received the bulk of the proceeds from these suits/settlements
- Not showing up for court dates to be grilled about these improprieties
- Not paying a few hundred thousand in sanctions
- Arguing to a judge with a straight face on appeal that they want to be tried for their criminal contempt, rather than just take the fucking fine, even though they could rack up multiple life sentences instead
- "Suing over porn is too hard, let's just sue over ADA violations instead!"
TechDirt also has some pretty good coverage, as well as embeds of most of the interesting legal documents.
IIRC, for at least one porn, they seeded the torrent sites themselves, too.
Edit:
-
RE: 💣 Discourse 1.2 incoming! 軣posted in Meta
Any time you want to annoy someone, you can go for the "ship them random shit from the internet":
You could also mail them glitter:
-
RE: T-Mobile WTFposted in Side Bar WTF
At least they aren't AT&T, who believes that SIM cards can't be moved. One time I gave my old phone to my mother - who is on my plan. The threw both the SIM from her old phone and the SIM from my phone away and put a new SIM in my old phone so they could assign it to her.
A sane provider would have just dropped her SIM in my old phone - or even better, allow me to do it without going to an AT&T store.
Verizon is the same; I tried handing my old SIM to the clerk when I got my new phone and she stared at me like I had suddenly grown a second head.
-
RE: That's below the belt, Appleposted in Error'd
@loose said:
Oh, so that's why I'm being asked to upgrade to version 38.something something
Haha actually I should qualify that: I think they stopped doing it after 4.
Still, the IE team always sent the Mozilla/Netscape developers a cake after a major release, and vice versa. It was really classy.
I'm guessing the guys at Apple who were working on Safari back in those days just burned Mozilla and Microsoft in effigy while smearing their naked torsos with goat blood. Or whatever Apple asshole developers do.
So, you're telling me the cake is a lie?
-
RE: I'm a :wtf: but I think Microsoft is, tooposted in Side Bar WTF
I think that if you cycle through a throwaway password you can get an old one back, but it's been probably ten years since I tried (why, yes, I do have a Hotmail account that goes back to about 1996, why do you ask?)
I've not tried to do a third password reset, but their error message seemed to indicate that the ban on reuse was forever. Maybe I'll try it later tonight - the problem is that the reset voids all "app" passwords, so my Xbox gets kicked offline when I do the reset, which is annoying.
IIRC, there's a 30 day lockout period before a password can be reused, but it could be higher.
That's just ... even worse and more annoying because the error message is lying and I highly doubt most people would run into that problem.
-
RE: АLL F-!!1 TOPIC TITLEposted in Meta
Looks that way. Although Stalin made an appearance in post 216:
I'm naming this the Boomzilla corollary, since I can't seem to find any better name out on the internets.
-
RE: In Soviet Reddit, you ban Russiaposted in Side Bar WTF
I can't wait until we have QUIC and HTTP/2+TLS/1.2 support everywhere so people stop treating middle-man editing of HTTP streams as something that makes sense for non-malicious use.
In order for that reality, you'd have to divorce the stream encryption from the proof-of-identity contained in the cert chain. I don't see that separation ever happening, unfortunately ....
Edit:
And even then, you're probably looking at DNSSEC to pin your proof of identity which only magnifies the devastation involved in DNS reflection attacks, unless there's something in DNSSEC that can help mitigate them (which I honestly don't know if there is or not).
-
RE: Just use sublime text (anti-vim rant)posted in Side Bar WTF
If you're trying to bring networking back up, file transfers aren't very useful, yet being able to get access to a console (there are some very useful pieces of hardware for this sort of thing) would be enough for running vi.
Even sneakernet?
Note: I'm still being serious here - why wouldn't sneakernet + better editor be less of a hassle than learning vi. I remember almost throwing computers in college because I hated using it so much.
-
Pins don't stay pinned in the "All Categories" viewposted in Bugs
Bug: pinned topics don't stay at the top of the "All Categories" view
Expected: pinned topics would stay, well, pinned
Actual: pinned topics work when in a specific filtered category view, but fall to their normal unpinned position when in the All Categories viewEdit: apparently I need more coffee to type a bug report correctly ......
-
RE: Windows 10 can-of-worms, Episode II: @Mike_Hunt strikes backposted in Side Bar WTF
@fwd said:
The biggest roadblock I've hit with the ribbon is if I'm looking for a feature and don't already know where to go for it, I don't have any idea how to find it. 95% of the time it's faster to ask google where to go before I even touch the ribbon.
This.
- Go to the dropdown arrow next to the Quick Access Toolbar
- Select "More Commands"
- Move your mouse to the "Choose Commands From" Dropdown
- Select All Commands
All commands are now listed in alphabetical order.
Bonus: If you select a command and then type a letter, you jump to that position in the list (e.g. Q takes you to all the commands that start with Q).
-
RE: Wimbledon uses laptops to run the control room's displays.posted in Side Bar WTF
I would say that maybe it's done for portability...
But (seeing as how I know nothing of Tennis) isn't the Wimbledon held in the same spot every time?
It is - at the All England Club in Wimbeldon
Edit: plus wouldn't a half server rack on wheels be more portable?
-
RE: Poll: Remove bugs from front pageposted in Meta
So, I get the idea (bugs/meta are interfering with normal TDWTF ass-hattery), but hiding bugs sounds like you're realizing the beta test is going worse than you wanted and you want to hide this failure from new users which seems disingenuous.
I'm not sure if hiding is the solution, but it feels ... weird to me.
-
Spendyourleapsecondhere.composted in Funny stuff
Comical, if useless:
I got to watch Nicholas Cage in a bear suit punch a woman in the face.
-
RE: Remy's back! A script for those who don't want to read the sourceposted in Side Bar WTF
updated bookmarklet for the new look:
javascript: void (function () { document.querySelector('.articleWrapper').innerHTML = document.querySelector('.articleWrapper').innerHTML.replace(/<!--/g, "<span style='color: red'> (").replace(/-->/g, ") </span>"); document.querySelector('.articleWrapper span[onclick]').style.color = 'magenta'; }()) -
RE: Remy's back! A script for those who don't want to read the sourceposted in Side Bar WTF
a bookmarklet version:
javascript:void(function(){document.querySelector('.ArticleBody').innerHTML=document.querySelector('.ArticleBody').innerHTML.replace(/<!--/g,"<span style='color: red'> (").replace(/-->/g,") </span>");document.querySelector('.ArticleBody span[onclick]').style.color = 'magenta';}()) ``` -
RE: Should big digressions be split to a new topic?posted in Meta
They do stuff like kill the program in Washington, DC that gave money to poor kids to get out of the abysmal public school system. I guess the good private schools (where their kids all go) were getting too crowded.
Well, except, (IIRC) the studies done showed there was no difference in outcomes for the poor kids who got those vouchers - they dropped out and failed at pretty much the same rate. So the only thing going on was the transfer of money from one corrupt organization that paid teachers well to a corrupt organization that paid teachers poorly and skimmed it off the top for the rich people who owned the private school which, ironically, reduces the chances that the public school will perform because all of the parents who care take their kids and money and leave, further screwing the public school over.
-
RE: In Which @Captain asks C# Beginner Questionsposted in Coding Help
@Captain said in In Which @Captain asks C# Beginner Questions:
@accalia don't you ever forget to type a comma and then have to go item by item in a long list until you find which item was missing it? Maybe C# has better error reporting that other languages where I've done that, but I've been burned by that kind of thing too many times.
Visual Studio will definitely tell you about it, and what line it's on:

There are red squiggles after three and four.
Error reporting will even show you the lines and that it expects a comma:

 Lessons learned from cracking 4,000 Ashley Madison passwords
Lessons learned from cracking 4,000 Ashley Madison passwords



 'd
'd HTTP ETag - Wikipedia
HTTP ETag - Wikipedia