Posts made by trainbrain27
-
RE: Mutant validationposted in Side Bar WTF
It's nice to see some crossover between my startup tabs. Greetings from the nicest imageboard, family friendly http://www.1chan.net/rail/!
-
RE: Apple Mail failposted in Side Bar WTF
@too_many_usernames said:
*Because I know I always put things in the recycling bin when I think I might want to dig them out a couple weeks later.**
Adding no value to the conversation, my recycle bin is not automatically emptied and fills so slowly that I empty it quarterly.
Since I started this job, I have recovered documents from it twice to save the effort of reprinting them, and it is the source of all my scratch paper.
So I do use it like my digital recycle bin, which tends to gather copies and minor revisions and is only emptied when my pretty blue drive bar turns red.
-
RE: .jpg.jpegposted in Side Bar WTF
Case sensitivity training
To add to the hidden extension issue, one of the systems I interface with treats extensions (only) as case sensitive.
The scripts that feed it do not, so if schedule.CSV exists, they will happily update it.
I spent the morning tracking why only old data was being parsed.
The external system apparently held and used schedule.csv even after we sent schedule.CSV.
I know extensions can be unhidden, but without access to the external system I didn't have a hint to look there.
-
Network bootedposted in Side Bar WTF
We're imaging 1000 computers this month. Thanks to fog, it's pretty easy. I WoL the whole lab into Linux and they image automagically.
Until students step in.
Last year the summer cleaners hooked a patch cable into two drops to keep it out of the way. The switch wasn't very smart, and the whole network went down. I spent an hour finding the loop and we updated the permanent switches after that.
This summer, the tech help wired the wireless clients to temp switches, but they wouldn't network book. The spinning bar (/-\|) didn't even spin.
They blamed the server, and I started checking for loops in the cables. 1st switch, no cable leaving and returning, 2nd switch, same, ect.. They had made a mesh topology. I need smarter switches or smarter help.
One particular Heaping Pile desktop refuses to network boot. The first workaround was gPXE by CD, but then the kids rip out the drive belts.I don't feel like replacing the drives, and I get tired of using two tweezers and a rubber band to fix it for a week until they pull it off.
I tried USB gPXE, which was booting to linux to boot from the ethernet to boot linux to install Windows, but that wasn't complicated enough, so now I use RMprepusb to load linux from the USB to choose an ISO to boot linux to boot from the ethernet to boot linux to install Windows.
-
Where did Java go?posted in Side Bar WTF
My server just 'lost' Java. Like many programmers, my programs don't start in the morning without java.
The last update changed the path to Java, but not the PATH that Windows uses. 10 second fix, but annoying.
-
Power Strippedposted in Side Bar WTF
Quote from the government hosting service that handles websites and e-mail for half the state:
WHAT HAPPENED? Monday morning during scheduled maintenance to replace a faulty power strip, we experienced a catastrophic data loss when the faulty part tripped a breaker, sending everything into a hard fault.
The faulty power strip was a heavy duty device that monitors the amperage draw of anything plugged into it. Replacement of the strip involved shutting down anything plugged into the strip, unplugging and replacing, then powering up the equipment. Somewhere during the power down, power up process, a breaker in the circuit panel blew, taking the HP SAN down hard. When we finally got the SAN controller back on line, we could not see any of the configured array of storage drives. Immediately, we opened a case with HP Support who confirmed our worst fears, the metadata file on the SAN was corrupted and the only recourse was to reformat and recover from backups. We chose against the recover from backup path because our backup software could not completely recover VMWare servers, only the data on the servers. Our only recourse for quick service restoration was to have our data professionally recovered. We drove the drives up to Ontrack in Minnesota Tuesday night and waited all day Wednesday for them to analyze the data and report back. As of now (Friday) the data recovery is underway. -
RE: Best place to store business critical documents? Try Outlook deleted items!posted in Side Bar WTF
@joe.edwards said:
@superjer said:
What I really want is for GUI file managers to recycle overwritten files, not just deleted ones. I rarely delete by mistake, but I overwrite by mistake all the time.
Norton GoBack saved me from this a couple times, before my love-hate relationship with Norton tilted violently toward hate.
GoBack caused/contributed to the demise of one of my hard drives. Conservatively, the wackadoo partition confused my recovery software, even if it was not at fault. I lost everything since my last weekly backup.
Now I use Shadow Copy when I'm on Windows.
-
RE: Asset management failposted in Side Bar WTF
@da Doctah said:
I dare you to bury the item offog somewhere into the middle of the list of hardware without explanation.
Good story, bad link (but still recognizable).
I was going to suggest fog in the future. It's not the only solution, but it makes my life much easier. When we deployed, the inventory feature was just a nice bonus.
-
RE: The case of the magic routerposted in Side Bar WTF
Users can't configger them fancy WPAs, and they certainly can't remember a password.
Plug and play prevents thousands of returns.
-
RE: The Laserjet routerposted in Side Bar WTF
I've seen both at work (a secondary school) The cleaning staff saw a dangling cable and plugged the other end into the wall, too*. Our entire network went down while I tried to find a serial cable and console in. The primary ProCurve didn't have spanning tree enabled. It does now.
*This was my first or second guess, but I had to find the darn thing.
We share a network with a Career Center. Their IT training lab is the Wild West, and we'd prefer to physically and mentally wall them off, but they need access to our servers. One of their 'servers' decided to pass out IP addresses to anyone who asked. LaserJet phones were the least of it.
This is the same teacher that was doing 15Mb/s on our 20MB/s line from one torrent. He has been throttled, but not the way I wanted to.
I made a visit to the wood shop, and now have a clue-by-four behind my desk.
-
RE: A special kind of heat?posted in Side Bar WTF
He must have a severe case of British.
Sadly, there is no cure.
-
RE: I got a {1}!posted in Side Bar WTF
Farmville is sometimes a decent-quality product. At other times, it freezes, restarts, spikes your CPU, loses gifts, and gives you unlimited junk* (that's not so bad, but I did fill my farm that way).
Zynga is bad, but some of the others are worse. Elf Wars and dozens of others share the same codebase, just changing the names and graphics.
* The URL was www.farmville.com/give_you_some_crap_15.htm, but you could get it again with www.farmville.com/give_you_some_crap_015.htm, etc. It didn't take much to get 500.
-
RE: Feel the Sicnessposted in Side Bar WTF
The Coriponder link is busted, but http://www.coriponder.net is reachable. Bonus points for the scrolling title.
Should someone be alerted that we've found the main site of CP network?
<font face="georgia,palatino" size="7">HE IS A DIFFERENCE</font>
<font color="#ff0000" size="2">WELCOME TO CORIPONDER.NET</font>
<font color="#ff0000" size="2">THE MAIN SITE OF CP NETWORK, TO ENTER CORIPONDER.NET PLEASE JUST CLICK ENTER BELOW, </font>
-
RE: "password" "protected"posted in Side Bar WTF
I half hoped someone would crack it, but the password to the first one is "password" and it sends you to [site]/password.htm.
One guess if you even need to enter the password.
The second part is never (to my knowledge) called. The page that contains it doesn't take text input.
Here is the bit that gets the password (with the old way commented out):
<td width="100%" bgcolor="#333333">
<!--
<form name="password1"><div align="center"><center>
<p><input
type="text" name="password2" size="20">
<span class="style8">x</span>
<input type="submit" value="go" onClick="submitentry()"></p>
</center></div>
<INPUT type="text" style="DISPLAY:none">
</form>
-->
<form action="password.php" method="post" name="password1"><div align="center"><center>
<p><input
type="text" name="password2" size="20">
<input type="submit" value="go"></p>
</center></div>
<INPUT type="text" style="DISPLAY:none">
</form>It shows up later in the page.
The Base64 encoding is a picture of J. R. "Bob" Dobbs, from the Church of the SubGenius.
</div> </div> -
"password" "protected"posted in Side Bar WTF
Here's a sample of unaltered code from a website that will, if properly prodded, provide "protected" personal phone numbers.
<script>
var pass=new Array()
var t3=""
var lim=8
pass[0]="U6VInhJlsnP6tBJ"
pass[1]="OqDAJvc7xhswD6T"
pass[2]="S4ZjU8P8vYVvpMe"
pass[3]="yNDDrzwS8PDwdkS"
pass[4]="878LlKGT1KRz9GOA"
pass[5]="5978LlKGT1KRz9GO"
//configure extension to reflect the extension type of the target web page (ie: .htm or .html)
var extension=".htm"
var enablelocking=0
var numletter="0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ"
var temp3=''
var cur=0
function max(which){
return (pass[Math.ceil(which)+(3&15)].substring(0,1))
}
function testit(input){
temp=numletter.indexOf(input)
var temp2=temp^parseInt(pass[phase1-1+(1|3)].substring(0,2))
temp2=numletter.substring(temp2,temp2+1)
return (temp2)
}
function submitentry(){
t3=''
verification=document.password1.password2.value
phase1=Math.ceil(Math.random())-6+(2<<2)
var indicate=true
for (i=(1&2);i<window.max(Math.LOG10E);i++)
t3+=testit(verification.charAt(i))
for (i=(1&2);i<lim;i++){
if (t3.charAt(i)!=pass[phase1+Math.round(Math.sin(Math.PI/2)-1)].charAt(i))
indicate=false
}
if (verification.length!=window.max(Math.LOG10E))
indicate=false
if (indicate) {
document.write(verification+extension);
window.location=verification+extension;
}
else
alert("Invalid password. Please try again")
}
</script>The rest of the site is constructed off templates full of template code. Image names have been changed around the way the code is written instead of the other way around.
Once you have guessed the password, the "protected" page contains, but does not run, this code. The page doesn't offer and input at all.
<!-- Original: Lefteris Haritou -->
<!-- Web Site: lef@writeme.com> www.geocities.com/~lef -->
<!-- This script and many more are available free online at -->
<!-- The JavaScript Source!! http://javascript.internet.com -->
<!-- Begin
var base= new Array("0", "1", "2", "3", "4", "5", "6", "7", "8", "9","A", "B", "C", "D", "E", "F", "G", "H", "I", "J", "K", "L", "M", "N", "O", "P", "Q", "R", "S", "T", "U", "V", "W", "X", "Y", "Z","a", "b", "c", "d", "e", "f", "g", "h", "i", "j", "k", "l", "m", "n", "o", "p", "q", "r", "s", "t", "u", "v", "w", "x", "y", "z")
var pass=""
var z=23;
var y=28;
var f= new Array();
var K= new Array();
for (x=0; x<10; x++){
f[x]=x<<9
f[x]+=23
}
for (x=10; x<36; x++){
y=y<<1
v= Math.sqrt(y)
v = parseInt(v,16)
v+=5
f[x]=v
y++
}
for (x=36; x<62; x++){
z=z<<1
v= Math.sqrt(z)
v = parseInt(v,16)
v+=74
f[x]=v
z++
}
var iCounter = 3 //How many retries
function inc(){
iCounter--
if (iCounter > 0)
{
if (confirm("\nPassword is incorrect.\n\n\n\nRetry?"))
Check()
else
alert('Password incorrect.');
history.go(-1);
// You may use this element istead if you want.
// location.href='denied.html' //Cancel html file
}
else
alert('Your three tries are up. Access Denied.');
history.go(-1);
// You may use this element istead if you want.
// location.href='denied.html' // 3 times incorrect html file
}
function Check(){
pass = prompt("Enter your password.","")
if(pass==null || pass==""){
history.go(-1)}
else{
var lpass=(pass.length)+1
for (l=1; l<lpass; l++){
K[l]=pass.charAt(l)
}
var code=0;
for (y=1; y<lpass; y++){
for(x=0; x<62; x++){
if (K[y]==base[x]){
code+=f[x]
code*=y
}
}
}
<!-- STEP TWO: Put access code here! -->
if (code==174153441) // code==[your access code]
go()
else
inc()
}
}
function go(){
location.href=pass+".html";
}
// End -->
</SCRIPT> -
RE: Fifa 07 - file not foundposted in Side Bar WTF
TRWTF is you have a time machine and just use it to brag about how long you've played a game released two years ago.
-
RE: Does this count as a WTF?posted in Side Bar WTF
@mahoromhr said:
@tgape said:
(1). All programming languages suck.
Yeah, real programmers write their programs with a hex editor directly on the executable file.
Mahoro
You've got hex? I have to toggle them in with a single switch.
-
RE: You hit the Ed! --more--posted in Funny stuff
I still have it (and the sequel) on my flash drive. I think it's portable without modification, so you do the install once, then copy the results to the drive and carry it with you.
I beat it and started collecting treasure. Turns out there's a memory overflow if you have too much stashed in the town. The workaround is to use containers, but you still wind up selling alot of it.
My other addiction keeping me from getting the new Lenovos ghosted is Exile (now Avernum). http://www.spiderwebsoftware.com/
-
RE: Exceptional exceptionposted in Side Bar WTF
I'd like some background, and until I get it, I'm going to humor myself that you have a blog exception.
Yes, I know it's just a bool to decide what flavor your exception is.
-
RE: Nice Truck! or the Where's Waldo of WTFsposted in Side Bar WTF
Do you know how many people are killed or injured by pointy knives over here?

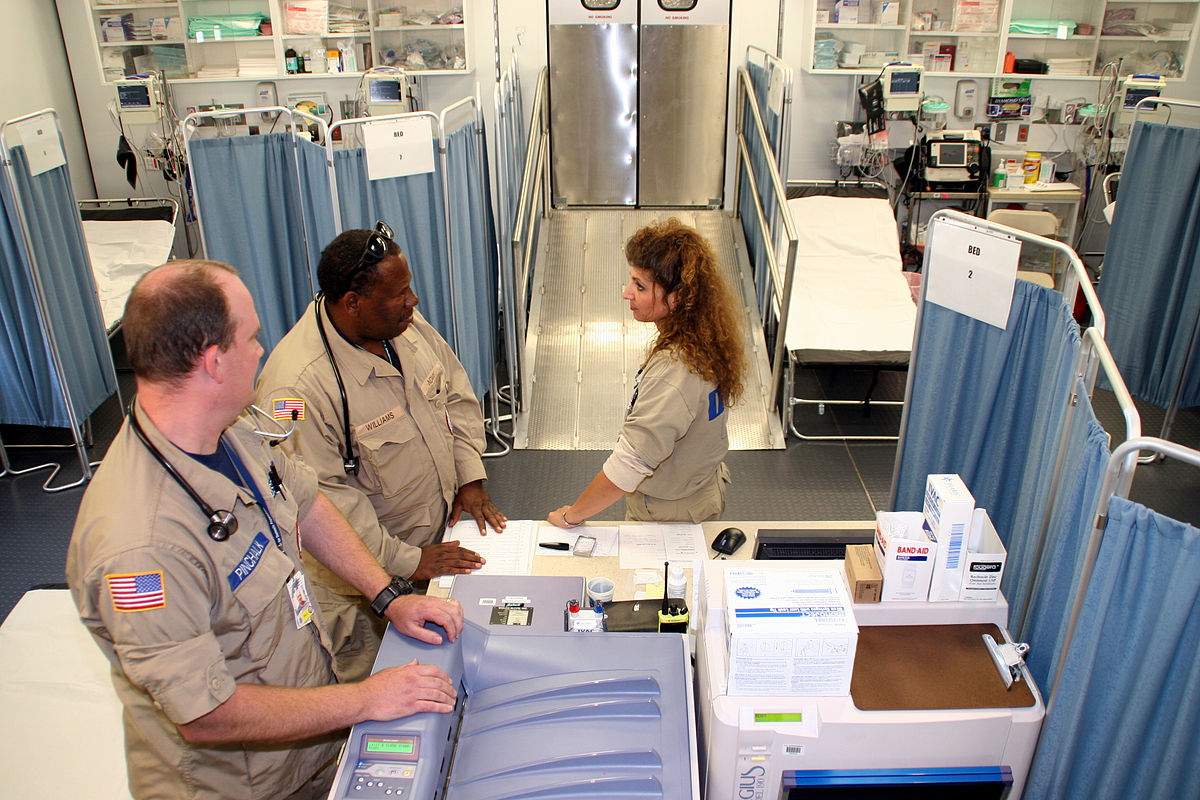
 Emergency department - Wikipedia
Emergency department - Wikipedia