The REAL Real WTF is that they're probably not using salted password hashing. I say probably because while they could re-hash the new password using each existing hash, anyone who would go to that much trouble would no doubt remember why they used salts in the first place...
Posts made by ailivac
-
RE: The password entered is already in useposted in Side Bar WTF
-
RE: I expect random junk in comments in the HTML source of pages from time to time.posted in Side Bar WTF
The real WTF is a block of lisp code that uses not one but TWO while loops
-
RE: The Godfather of Webdesignposted in Side Bar WTF
Wait, so the WTF isn't that the entire site is nothing but a flash movie?
Just because everyone does it doesn't mean it can't be a bad idea; after all, 90% of computers ship with Windows...
-
RE: Unexpected Google Products resultposted in Side Bar WTF
@PJH said:
You could always re-enable SafeSearch if it offends you - it won't show up then.
But then my image searches won't be nearly as amusing!
-
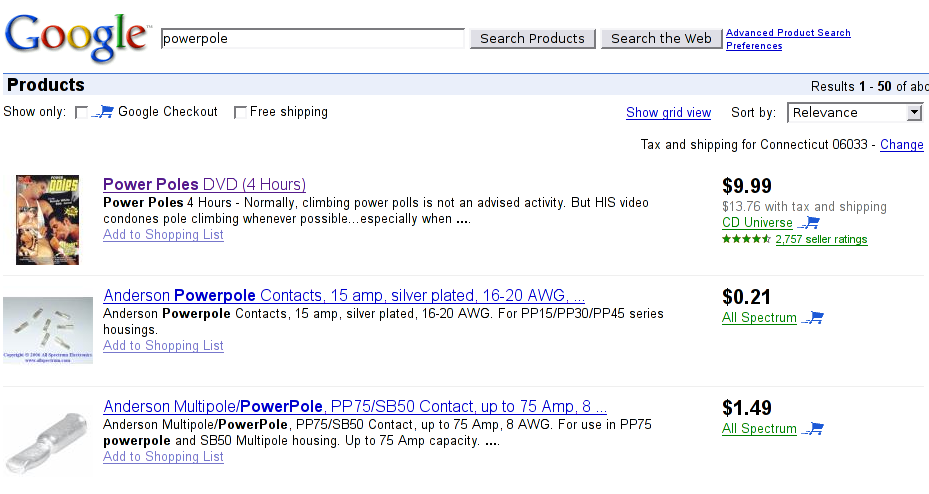
Unexpected Google Products resultposted in Side Bar WTF
Several months ago Google introduced a feature that automatically searches for words that are similar to but not spelled identical to the words in your query. While it saves a lot of time with words that have multiple spellings, different conjugations/tenses and compound words that can be spelled with or without a space or hyphen, it has an annoying tendency to decompose unquoted product names into smaller common nouns and add lots of bogus results.
Finding gay porn instead of electrical connectors is a new low however:
-
RE: Click and tellposted in Side Bar WTF
Gotta give them credit for originality. At least it's not yet another "PHP warning: Mysql connect failed"
-
RE: Yet another clbuttic mistake prevents verizon subscriptionposted in Side Bar WTF
Verizon wireless doesn't let you use any feature on your phone until they can find a way to make money in the process, Verizon branded routers only allow a few internal IP addresse even when the underlying hardware and software support more, and Verizon DSL tries to tell you that your name is a swear. Everything Ihear about that company seems to imply it's run by a bunch of greedy assholes.
-
RE: Email-based securityposted in Side Bar WTF
@morbiuswilters said:
Intellectual property is property. I cannot understand why people think tacking "intellectual" on the front changes the meaning or makes it less credible. And when it comes to intellectual property, duplication without the consent of the creator is the same thing as theft. You're not even debating piracy, you're just trying to obscure your theft with synonyms.
Fine. Duplicating the property of others. But there's still a big difference betwene copying and stealing. If I build a car identical to yours, I haven't stole anything. You still have a fucking car.
-
The i-beam: sequel to the wooden tableposted in Side Bar WTF
Take a look at "Figure 1" on this page. Another example of someone who doesn't understand the relationship between Microsoft Word and web pages.
-
RE: Someone didn't know about case statments..posted in Side Bar WTF
@AbbydonKrafts said:
@Daniel15 said:
Even using elseifs would make it look much better
As an immediate fix, I agree that ElseIf would've cleaned this up. I'm sure there's something else that can be done, though, but I can't think of it at the moment.
If the language has a map data structure and first-class functions (or at least function pointers or Java's anonymous classes), you can use a dispatch table.
-
Death by lack of input validationposted in Side Bar WTF
I may not be an expert on the game of hangman, but I don't think the player is supposed to be punished for guessing characters outside the alphabet being used.
See the very bottom of http://www.elementsdatabase.com/
And forum software should be responsible for converting URLs into real links
-
Why bother fixing website bugs...posted in Side Bar WTF
... when you can just tell visitors how to use the workaround!

Indeed, pressing enter (as opposed to taking your hands away from the keyboard to click the button) on True Value's store locator will just refresh the current page, instead of submitting the form.
-
RE: You wanted WHAT PAGE???posted in Side Bar WTF
Also forgot:
-1: By using Internet Explorer, you lose your right to complain about web sites not displaying properly.
-
RE: Wikipedia, anyone can edit itposted in Side Bar WTF
@shadowman said:
What!?!? A low-quality article on Wikipedia!?!? Stop the presses!
I'd ask for my money back if I were you. Seriously, though, Wikipedia can be an OK source of informal information, but did you really expect every article to be well-written and completely accurate?
In other news, my new favorite form of punctuation is the double-excla-question-mark. '!?!?'
I don't even understand why he thinks this one is so bad. "Commonly called" is very subjective; I'm sure there are people somewhere who call them "script languages." "Interpreted" distinguishes them from compiled languages since scripts are not stand-alone executables.
-
RE: Firefox Add-on Ironyposted in Side Bar WTF
Wow, are firefox users that lazy?
I use Seamonkey, and some days I'm disappointed that 99% of the new firefox extensions that everyone is yelling about will never get ported to my browser (because programmers are lazy). Other days I don't feel like I'm missing anything important.
-
RE: Direct URL Disk Access: Not just for PHP!posted in Side Bar WTF
@fluffy777 said:
How about going after C:\pagefile.sys ? ...
I got an HTML page with "Persits.Upload.1 (0x800A001A) The process cannot access the file because it is being used by another process."
I always thought that windows's inability to share files between processes was just a bug that unix had figured out decades ago but microsoft couldn't fix. Maybe it's intentional, to make web applications more secure.
-
Available... where exactly?posted in Side Bar WTF
I'm not sure what this seemingly contradictory set of availability indications is trying to tell me...
The other WTF is that the infamously low-priced Walmart charges more for the same product than Newegg, even when you take standard shipping into account.
-
RE: How not to use a variableposted in Side Bar WTF
I love bashing PHP for being a completely insane language, and people like this make it so easy :)
I don't actually know what built-in function he's reinventing/ignoring, since i haven't read and memorized the PHP library documentation, as I'm not into masochism...
-
RE: Colors may vary?posted in Side Bar WTF
@PJH said:
@kimos said:
Well, from a little reseach, you are paying for only 55 pieces* of paper - it's hardly as if you're buying it by the ream - it makes all the difference.I did like the three cent savings on that paper though... bargain
* And not all of them are full size - only 8 of them are.
[edit] and the site that I found the details on is $1 cheaper than Amazon anyway.
Actually this is a 50 pack of 5-7/8" paper, not the 55-sheet assorted sizes/colors you see in most bookstores.
They also have a solid violet package with a yellow picture... now I'm wondering of the patterned paper I ordered yesterday will actually look like the picture
-
RE: An _old_ PHP documentation representative lineposted in Side Bar WTF
@MaHuJa said:
In decreasing order of probability, your system had one of these properties:
-Storing plaintext passwords on the server
-Constant (per-user) salt, meaning no protection against replay attacks.
-HUGE DATABASE of password hashes valid for a particular user.If I remember right (I think I have a backup somewhere from before the first hard drive on my old laptop failed, but I don't feel like digging it up now) it stored a single password hash on the server end. It was actually more of a nonce than a salt. Each time you requested the login page it generated a random string, stored this in a server-side session container (with a standard session ID cookie) and sent this along with a small script and a link to a javascript hash library. The script would pull the plaintext password out of the form, hash it, append the nonce to the hash, then hash that thing, and submit that in lieu of the original password. The CGI script already had the hashed password and the nonce (in session storage; the client doesn't send it back) so it runs the same process, without the initial password hashing step, and compares the submitted hash-of-hash-plus-nonce. Then it removed that session information so replaying with the same nonce wouldn't do anything.
First of all, most browsers, by default, warn you of this. If you turn it off, that should be because you're not interested in knowing, right? (Well, most don't care and only see it as a bother/hindrance to what they're trying to do, but that's not the browser's fault.)I think you're talking about the "You are about to leave a secure page" warning when the form action is an insecure URL, which isn't what's going on here. The login is sent from a secure page to another secure page, which then issues a redirect (after the form submission is done) to an insecure page.
On the other hand, look at what you do protect.
The ability to
-access the data in the future (when the user has moved on to another place)
-alter or remove the data
-send mail (verifiably) from that user
-probably more that I missed.Valid point; I know that having someone be able to read a few of your messages one time isn't a huge loss in the long run, but do you at least admit that it's fairly stupid of Google, who has the capability to encrypt everything, and will happily do it if someone specifically asks them to, to not encrypt more than the login by default?
-
RE: An _old_ PHP documentation representative lineposted in Side Bar WTF
I can't understand why so many people who supposedly design web applications for a living are so clueless about security. Everyone (ESPECIALLY programmers) should know by now that clients can NEVER be trusted with sensitive information. PHP in my opinion shouldn't even be used anymore; its designers over the years have introduced so many incredible security holes like register globals, magic quotes (not exactly a security hole, but part of an attempt to solve another unforgivable omission from the database libraries) and god knows what else I might know about had I actually spent any time working with PHP once I learned how useless it was, that are still enabled just so that some people can run legacy code written 6 years ago by people who can probably barely understand BASIC, that they should be banned from any software-related company or organization for the rest of their lives.
Also, why are we still sending so many passwords in cleartext? A couple years ago I hacked together a little salted-hash-based password form with maybe a hundred lines of Perl and Javascript... please tell me I'm not the only person who's ever tried this?? Of course hacks like that wouldn't even be necessary if SSL were easier to implement. But we have this "certificate authority oligopoly" where everyone is forced to pay through the nose for security that's just as fraud-susceptible as it would be if it were free. And maybe if there were more SSL sites floating around by now, web server/browser writers would have come up with a TLS implementation that works with virtual hosts and doesn't need to use a different port to explicitly enable encryption. Then there's the "encrypt some stuff so you look secure" approach that Gmail and others take: they go to the trouble of getting a certificate and configuring an SSL server, but only use it for the login, so once you're logged in, unless you typed httpS://mail.google.com in the first place, it drops you back to a cleartext channel so all that precious information that you're using a password to secure in the first place is right there for anyone sitting near the same wireless hotspot as you to easily and *undetectably* grab out of the ether. Does running an entire site through SSL really make it that much slower, especially when you're processing everything through non-byte-compiled Ruby scripts? I swear I've seen hardware crypto accelerators for sale for a few years....
And are self-signed certs really that bad? Unless someone happens to be dns-spoofing the site you're connecting to the first time you accept the certificate, and that same person does it with the same fake certificate every other time, what's the difference?
(That whole password/SSL part wasn't connected to the thread at all; I just wanted to do an off-topic security rant. I'm sure I could think of more things to complain about, but it's approaching 4 am :] )
-
RE: Eject your hard disks.posted in Side Bar WTF
@Renan_S2 said:
I used to have a similar behaviour with the Ubuntu live-CD. If I unmounted any partition, it would tell me to "not eject the drive until the operation is done" or words to that effect. But the "drive" was an internal IDE drive.
I wonder how can I "eject" a hard drive. Will it break through my case?Ubuntu seems to dumb down their disk management way too much. The last time I used an ubuntu livecd, I connected my usb flash drive to it, which is configured in a somewhat interesting way (3 partitions, one vfat, one ext2, and one with LUKS encryption). But it wouldn't let me mount or unmount those partitions manually: it mounted everything immediately, and when I told it to unmount one of them, it unmounted everything and refused to acknowledge they exist anymore, let alone mount them, until i unplug and reconnect the drive.
For the ejectable hard drive part, the system probably knows it's not removable, but someone probably forgot to check the removable flag in the HAL properties, or, more likely, didn't even know HAL storage devices had a removable property.
-
RE: Header beautificationposted in Side Bar WTF
@Thief^ said:
(Making a webserver in my free time, currently serves one fixed page and can return 6 different errors)
Just what the world needs, another IIS clone :)
-
Another strange "Tip of the Day"posted in Side Bar WTF
I saw this in pgAdmin's tip of the day window today:

Not as bad as the "Tips file does not exist" screenshot that appeared in Error'd a couple weeks ago, but still funny.
-
RE: School Projectsposted in Side Bar WTF
The thing I've come to hate about school projects is that everyone knows that we have a limited amount of time to finish the project, and everyone wants to do the minimum amount of work possible (which isn't necessarily so bad) so instead of spending the little time we have actually working, we have hour-long meetings discussing how many corners we're going to cut.
Somewhat ironically, I think most of the projects I've done are things that I could have done faster and better *without* the "help" of 3 or 4 other people.
Right now I'm working with people who seem to honestly believe that email is an acceptable version control system...
-
RE: Not what you want to see on your internet banking site...posted in Side Bar WTF
@Kyanar said:
Maybe they remapped the ASP extension on the webserver to the aspnet_isapi.dll module? That could explain it - keep links intact after an upgrade and all that.
Why didn't they design the application right in the first place, so that the URLs are human-readable or at least logical based on the context of the application, not arbitrarily tied to whatever programming system they used and how they have the filesystem organized? (another thing PHP has lousy support for despite it supposedly being so great for web development)
-
RE: I think I may need to optimize this queryposted in Side Bar WTF
@tchize said:
Better question, are there still any language around that doesn't allow parametrized query? (And yes, java has, for a long time)
Does PHP have them yet? The many shortcomings of its database libraries are one of the reasons I refuse to use or recommend PHP to anyone. I think the rest of the language is hopeless as well... if it's taking them this long to support namespaces, there must be something fundamentally wrong with how they designed/implemented the symbol table in the first place.
-
RE: Please use caps onlyposted in Side Bar WTF
@SuperousOxide said:
They're too lazy to do even minimal text-massaging behind the scenes.
Makes you wonder... If they don't know how to compare strings case-insensitively, what are the chances they know what SQL injection means, let alone how to prevent it?
-
RE: PHP Tutorial: Well, that's one way to do it...posted in Side Bar WTF
[quote user="iwpg"]I don't do much PHP (thank god) but I don't know of a better way to pull a value out of a hash table case-insensitively - actually, I can't think of one in any language, not just PHP.[/quote]
You should learn perl
sub getValueByFieldName { return @request{grep { lc $_ eq lc $fieldname} keys %request}; }


