Okay, not quite... but if the developer registers a domain name and prints it on the sign/placard (QR code or human-readable), they really need to keep it active for the lifetime of the park. Or at least a little longer than the typical 5-minute attention span of Internet-goers (or marketers for that matter).
Best posts made by quijibo
-
This children's park is brought to you by: our porn siteposted in Side Bar WTF
-
RE: We need *all the shiny*posted in Side Bar WTF
Did anyone else find the hidden hamburger-style menu on the right?
At first I thought it was a display glitch that was following the page as I scrolled. When you scroll it highlights different pieces based on where you are. If you mouse over it tries to do the same highlights as it tracks your cursor around the hexagon (poorly in Firefox).
... 'cause you know, you might need to jump down on the page quickly and going to the bottom-left coordinate of the
hamburgerhaxagon is exactly how I would do that! -
Microsoft is limited to receiving 100 emails per day?posted in Side Bar WTF
I had the follow conversation with someone at our ISP a while back.
From: abuse@isp.com
To: admin@customer.com
Subject: Internet Abuse Complaint -- IP address 1.2.3.4
Attention Customer,
There has been a complaint received by our security team indicating that an IP address traced back to your cloud instances. Blah blah blah, make sure your machines are not compromised... refer to the report below.
The Report:
ISP has received reports of unusual mail activity coming from your connection. Over 90% of mail to certain domains are being flagged as Spam. This is likely due to malicious software running on a pc behind your router.
IP Address: 1.2.3.4
For period: 1/8/2018 1:00 AM to 1/9/2018 12:00 AM
Potential Spam Attempts: 106
Message Recipients: 106Me: Oh crud... I keep on top of security updates and have monitoring on that server. This can't be right.
From: quijibo@customer.com
To: abuse@isp.com
That IP address is our main external mail server that handles all contact with our customers. If ISP is doing any monitoring of network traffic that would be expected as we are in the middle of a seasonal increase in sales.
That said, I do understand that abuse of servers to send spam is serious so I will investigate immediately.
Do you have access to any emails (with headers) that were reported as spam to the abuse team?Their reply:
From: abuse@isp.com
To: quijibo@customer.com
The report you received is forwarded to ISP from Microsoft’s Smart Network Data Services (SNDS). The SNDS is a service provided by Microsoft which is responsible for analyzing and reporting on spam sent to mail hosted by Microsoft, such as Hotmail, MSN and Live accounts.
Please note: SNDS reports are created and compiled by Microsoft. ISP does not create these reports nor determine what content is considered spam. Because of this, ISP is unable to request removal from SNDS or provide samples of the alleged spam.So I dig into that server and look for anything usual and I found nothing obviously wrong. I counted up the number of going emails to @hotmail.com addresses. We sent receipts to 114 customers who provided an @hotmail.com address. That doesn't count all of the other domains that Microsoft owns.
I sent that information back to our ISP, letting them know that we can easily send 100+ emails a day to customers who sign up for services on our site. They didn't reply to my follow-up. So that's the end of that, right? Hah!
A week later...
From: abuse@isp.com
To: admin@customer.com
Subject: Internet Abuse Complaint -- IP address 1.2.3.4
Attention Customer,
There has been a complaint received by our security team indicating that an IP address traced back to your cloud instance has been abused in some way affecting other servers or users. You will find more information in the attached document.
(Attached Word file:)
ISP has received reports of unusual mail activity coming from your connection. Over 90% of mail to certain domains are being flagged as Spam. This is likely due to malicious software running on a pc behind your router.
IP Address: 1.2.3.4
For period: 1/15/2018 6:00 AM to 1/16/2018 1:00 AM
Potential Spam Attempts: 105
Message Recipients: 105Okay, I'm beginning to see the pattern here.
From: quijibo@customer.com
To: abuse@isp.com
To whom it may concern,
The report indicates that we sent 105 emails to Microsoft servers on January 15. As I explained before, we have 10,000 active users on our site, so sending 105 emails to Microsoft servers in a day is not unusual or malicious, and certainly not enough traffic to "affect other servers or users".
Please provide direct contact information from the originator of these reports so that we can verify what specific activity is triggering the report, or whitelist our IP addresses with ISP's security team so that we do not continue to receive these erroneous claims.The response:
From: abuse@isp.com
To: quijibo@customer.com
The report you received is forwarded to ISP from Microsoft’s Smart Network Data Services (SNDS). The SNDS is a service provided by Microsoft... blah blahWord-for-word identical to last time. My solution? Prevent users from using a Hotmail email address when they purchase services on our site. Problem solved.
But seriously, 100 emails sent to Hotmail in one day triggers an alert from Microsoft? And no one at our ISP can comprehend how ridiculously low that number is, and therefore take that alert as a sign of a compromised server.
-
RE: Wordpress, you make it so hard to defend you -- or do automatic updates anymoreposted in Side Bar WTF
Ah, Wordpress... possibly the biggest POS ever made, and the only thing that marketing people "know how to use" (except they don't and I get stuck troubleshooting). Our last marketing "expert" convinced the bigwigs to move our site to Wordpress, and then promptly quit shortly thereafter, leaving us with this POS to maintain. Before that we had static HTML files that developers could edit as needed (and our site is static content anyway).
Fortunately, I was able to stand my ground and not make Wordpress publicly accessible. It is in a subdirectory with apache only allowing access through whitelisted IPs. We then use a plugin called Simply Static that crawls Wordpress and saves everything as static files, to the directory that apache then serves as our site.
Our logs are full of bots attempting to exploit what looks like Wordpress, but is not. Plus we don't have to be on the upgrade treadmill, so I can update Wordpress when I have time to go through and check that everything still works. Or never.
-
RE: Mozilla Rebranding Or: How to Waste Several Hundred Thousand Dollars on Awful Graphic Designsposted in Side Bar WTF
This whole debacle reminds me of what happened when, out of the blue, one government tried to ask citizens to vote for a new license plate design. They thought that they were being all trendy by having an online poll so that everyone could get involved in choosing their favorite design.
And then that plan blew up in their face... first by those asking why we needed a new design (and all options removing a cherished local symbol), and then by asking why the only designs were those created by 3M, when instead the project could have been put out to tender for local design companies.
In the end they promptly dropped the whole idea and just added a digit to the current plates, the sensible choice.
-
RE: Lime scootersposted in Side Bar WTF
I read the story below the other day. Before this I had never heard of the scooter craze. It caught my attention because of the (to me) obvious hoarding that will happen from the "extra incentive" to find lost scooters and eventual fighting to pick them up before someone else does.
Also, I can't imagine anyone could make money charging these things in the vastly suburban area where I live. I suppose if the density of scooters is high enough it makes sense to drive around and pick them up, but my first assumption was that after gas for a truck or van and the wear-and-tear from the extra mileage that $5 per scooter must be close to break-even for the contractors.
-
RE: 🐧 Lunixposted in Side Bar WTF
Meh. Just another n00b completely misunderstanding "the" (or "a") UNIX philosophy.
Having one program per task that does its task well does not mean that programming magically becomes easy. Other important benefits include modularity of code (in days when everything was C or assembly and not object oriented), and the ability to understand each piece very well. (Think from a sys-admin perspective who can understand that grep, sort, and uniq all do exactly what they are told and nothing more.)
And in the case of shell scripts, you don't need -print0 or -0 to handle spaces in file names. That is more for unicode characters and other odd cases. In Bash setting IFS=$'\n' works just fine to split the output of a program by newlines only and not spaces.
Like any language, you can mess yourself up in shell scripts if you don't think and understand the limitations of piping one program to another. You need split file names by newlines or null characters, quote file names that are passed as arguments to programs that you call, etc. No different than knowing that you need to use parametrized statements in SQL.
-
RE: Meanwhile, in B*****M: Luc Rectumposted in Side Bar WTF
This reminds me of a similar incident over a custom license plate:
-
RE: For security purposes, customer service needs to see your passwordposted in Side Bar WTF
For a while Sirius Radio did that (and maybe still do, I don't know). About 10 years ago I called their tech support because my username and password for the Internet radio access wasn't working. The person on the phone helpfully read out my username and password to check if that was what I was using to log in. Yikes. And that's why I always try to use my least secure password first when signing up on unimportant websites.
-
RE: EU wants to filter codeposted in Side Bar WTF
@timebandit said in EU wants to filter code:
Like most politicians, the sum of their knowledge about software is E_DIVISION_BY_ZERO
So very large when approached from the right?
See: Asymptote
-
RE: Using your mobile to pay for public transportposted in Side Bar WTF
@gurth said in Using your mobile to pay for public transport:
But they’re making it out to be like it needs to support different phone models individually when all you really need is one version for Android and one for iOS and you’ve got the vast majority of users covered, I’d think.
Ha ha ha ha ha ha ha, ha ha ha, ha ha!
That's what you might guess, but you would be totally wrong. Android on each model of phone is different from the next, whether that is because manufacturers and telecoms don't release updates for "old" models, or because they customize the OS.
I love my Android phone, but damn is it hard to keep track of things like where to find a setting when someone asks for help. And as a programmer who rarely writes Android apps, it seems to take a lot of extra care to write an app that runs on older and newer OSes. I spend most of my time reading the documentation and figuring out what works on older and newer OS versions, compared to the small amount of time needed to actually write the code.
I don't envy anyone who writes Android apps for a living.
-
RE: Good job, that Bing!posted in Side Bar WTF
1) Bing's advertising gets sanitized after going up (which would be TRWTF)
2) Wherever the "This is a malicious site" stuff in Edge goes, it gets acted upon across the Microsoft estate, and quickly- That reporting link sets a cookie that hides the ad in your browser only, making it look like Microsoft has the fastest response time ever. They might actually look at your comment half way into next year.
(No, I wouldn't put it past an advertising company to do such a thing...)
-
Let's count now: 10, 11, ... 19, 22, 6, 7posted in Side Bar WTF
http://www.homedepot.ca/catalog/electric/173425+4294379628/24/0/P_OfferPrice|0
We've all seen it before... numbers that are stored as strings instead of numerically. But you would think that a major retailer would be able to sort prices properly on their web site... sheesh.
I just picked one category above that would show the sorting all on one page. I was looking through the ranges section last night and I couldn't believe there were none listed under $1000 (CAD). After lots of filtering down and jumping between pages I realized why...
-
RE: CloudFlare down. Again.posted in Side Bar WTF
@Gąska said in CloudFlare down. Again.:
@dfdub said in CloudFlare down. Again.:
AFAIK, every jurisdiction on this planet has accepted the fact that there's no such thing as bug-free software.
And to be honest, I hate it. When a civil engineer fucks up building construction, he's liable for everything that goes wrong due to it. Software developers should be too, to some extent.
Actually... they don't seem to.
Honestly, I've been hearing that statement for my whole career, except I also have an interest in the construction industry and see so much crap all the time (that doesn't kill anyone, so sure, but unsafe buildings). Since that story came out I've been bringing it up as a good counter-example of how our perception of engineering is changing too.
Of course, maybe I will be proven wrong if some combination of the engineering company that made the design, the other engineering company that was supposed to verify the math, the contractor that saw the cracks, or even the DOT inspector that saw the cracks that morning and ignored them, are prosecuted. And then maybe my faith in humanity will be partially restored...
-
RE: AV Warning: This string triggers Avast & AVGposted in Side Bar WTF
Aside from AV programs being stupid as usual, TRWTFs are in the http://8ch.net/av.html link:
No one can learn about malware or security if they are not allowed to study the source code of malware. Unfortunately, even reading the source code of malware is a security threat according to Avast.
No, really? You expect a program that scans files for virus-like patterns to allow you to save a virus file on your computer without warning?
Okay, okay... some of us have been around long enough to know that AV scanners use pattern matching inside files (among other techniques) and not just a checksum of a entire bad EXE (or JavaScript file or whatever). Maybe the n00bs don't know that, as the AV scanner sees it, saving a file with known bad pattern is equivalent to saving a bad EXE.
Antivirus software works by spying on all your internet traffic and disk reads/writes. Users of these software pay for the privilege of having someone spy on them, quite simply.
OMG! An AV scanner requires actually reading the files/data that it is about to scan! All of the programs on my computer are spying on me!
-
RE: Web USBposted in Side Bar WTF
I guess what we need now is a firewall for USB, video, and audio devices; a shim that will sit just above the kernel drivers and check if Chrome is trying to interact with these devices. If so, then the firewall can return "no devices found"1
1. Or a fake USB descriptor with the string "get off my lawn" for us graybeards
-
RE: Android phones might crash when calling 911posted in Side Bar WTF
A similar bug was created in Android 1.5, affecting the HTC Dream and HTC Magic (first two phones produced). When dialling 911, the OS is supposed to turn on GPS to send your current coordinates as part of e911, but that code had a NullPointerException which rebooted the phone.
In Canada, we had a debacle similar to the recent Samsung exploding battery recall. After much confusion and misinformation, Rogers (the only carrier with android phones at the time) decided to cut off both of these phones from their network until owners installed an update. The problem (at least for me) was that the update wiped all of the phone data for some unexplainable reason, and closed all known holes to root the device.
I had a bit of fun figuring out how to extract the baseband firmware from the system update and only flash that portion to get my cell service back. :)
That's the sad nature of software. These life critical bugs will keep happening and may even appear back in the Android code base some day. Which company takes responsibility when the bug is released?
-
RE: Automation!posted in Side Bar WTF
@kazitor I think you missed the part where the "developer" dictated the contents of that page on microcassette and the secretary misunderstood "32" as "3-Q".
-
Strange exclusionsposted in Side Bar WTF
When I bought my current place, I bought a new stove from Sears and had it delivered on the closing date. Sears is not necessarily the best place for appliances, but it was close and they deliver and take away the old one, so it was just the path of least resistance.
Sears offers their own warranty on appliances, but their sales gimmick is that if you don't make a claim against the warranty after it expires, you get the value paid for the warranty back in the form of an in-store coupon. Normally I never buy the extra warranties on electronics and whatnot... we all know that they are a scam that is basically pure profit for the store. That said, I have bad luck with things that break and I thought that some time down the road I would probably need a new fridge so I could always use the credit to buy something else. (It turns out that the fridge went about a year too early... so that almost worked out but not quite.)
The warranty on the stove is now up and I called to get my coupon. I expected many restrictions on how it could be used, but one of them made me go


Prices ending in .97? What's that about?
-
RE: More Excelence in spreadsheet-landposted in Side Bar WTF
Excel runs scripts after users clicks "Allow". News at 11!
More seriously, we make use of this stupidity in Excel when users want to export from our system so that they can see the underlying formulas and edit them after the export. I'm sure lots of other tricks could be done to access data from the target computer using formulas (like injecting VB script?).
The whole idea that Excel tries to guess what to do with the data (and is annoyingly wrong sometimes) is typical Microsoft crap.
-
RE: --no-preserve-common-senseposted in Side Bar WTF
Ummm... sudo doesn't pull GUI libraries along. gksu does, which was in the screenshot, yes, but I used that to demonstrate that there is a mechanism by which this is handled by default - in GUI, not necessarily in CLI.
Yes, I was picking on gksu and GUI programs in general, but the same principle applies with sudo. Either rm would have to pull in a sudo library, or parse the sudoers file (or heaven forbid, sudoers in LDAP). That is still more things to go wrong in a simple, core OS program. A higher-level wrapper or replacement for rm that can do such fancy things on a desktop or less-critical server is a much better approach.
Also sudo is a setuid program, which it needs in order to elevate to root after it checks your password. And actually sudo runs as root before even asking for your password. Having many more programs run as setuid just so they could edit/remove system files after verifying a password increases the likelihood of there being a root exploit.
More features can be nice, but they are also just more things to go wrong...
-
RE: Microsoft is limited to receiving 100 emails per day?posted in Side Bar WTF
@spencer said in Microsoft is limited to receiving 100 emails per day?:
I don't think preventing Hotmail addresses would be enough, as there are other domains that go to the Hotmail servers, eg. @live.com, @outlook.com, including domains with the country-level code (@live.co.uk).
We actually disallow @hotmail. , @live. , @outlook. , @skype. which covers most of the variants for Hotmail addresses. So far that has been enough to keep our ISP from complaining again.
A quick search turned up some similar results about Outlook and Gmail send limits,but also this from https://postmaster.live.com/snds/FAQ.aspx
IP Address ...
The IP address that the ISP sent to us is the public IP of our external mail server. It is behind a 1:1 NAT so no other systems will start outgoing connections from that public IP.
From https://postmaster.live.com/pm/services.aspx#Section1, to me it sounds like warnings are only generated when a significant number of emails you've sent are being marked as junk
Smart Network Data Services ...
We only send receipts to our customers when they pay for a service. That email contains their username and where log in to get started (but presumably they know to go back to our site to log in). Some users may tag that email as junk but I doubt that most have.
What is most likely happening is that Microsoft's spam filter is automatically tagging our receipts as junk because they all look similar to each other, and even worse SNDS then uses the feedback from their spam filter false positives to trigger on.
You can't use one bad filter's output to train another filter on what is spam or not. That's why I asked for specific emails that users have submitted and not what some filter thinks is spam (before getting the reply about SNDS).
Seeing as it's free, you could possibly sign up on SNDS and get access to better reports/data on why you're getting the warnings. While not the best solution, I get the feeling that having additional SMTP servers at other (different public) IP addresses would skirt around the issue.
Why should that be my problem to figure out why SNDS is alerting our ISP? If I am confident that our server is not sending spam (and I realize that there are lot of servers that do get compromised) then I don't really care if my ISP wants to subscribe to SNDS. Just stop forwarding them on to me and everyone is happy.
-
RE: Edge zero day^Wsecurityposted in Side Bar WTF
When I read about this I felt vindicated in my habit of always opening a new tab before visiting a "more secure" site, like reading Slashdot and then logging into my bank. I've been doing that forever to be sure that nothing on the last page that I was viewing could leak into the bank's login page. It turns out that I was right!
-
RE: XML file confusion (wooden table, advanced edition)posted in Side Bar WTF
@greybeard said in XML file confusion (wooden table, advanced edition):
@gąska said in XML file confusion (wooden table, advanced edition):
Well, I don't know any other country in the world where checks are used.
Canada
What are checks? We use cheques in Canada (very rarely), which are similar to checks, but different.
-
RE: Good article on the root of Windows quality problemsposted in Side Bar WTF
@Zmaster said in Good article on the root of Windows quality problems:
Frankly, the article assumes too much stuff IMHO and seems to just say “they’re not unit-testing their code”.
Some things are easy to unit test, but race conditions, drivers, integration between different systems are a different story. I’m not saying unit testing is a bad idea, it just won’t get you 100% covered.Bang on. Also, what happens when Team A creates all of those great unit tests and later Team B commits something that breaks the tests, but no one on Team B has enough in-depth knowledge to update Team A's code (say with new APIs or necessary API changes due to a flawed design earlier)? I've seen that happen before.
Instead of being worried about "speed" and "number of unit tests", the real problem here is that management either doesn't care to stop deployment of highly broken code or those who know about it don't have the authority to say it isn't ready yet. Marketing promised the release of the great new shiny and no matter what the shiny will ship on time.
-
RE: Strange exclusionsposted in Side Bar WTF
Yup. I worked at a store that used .44 and .88 to indicate a special price that was not eligible for other discounts.
Interesting.
I wonder how many POS systems have .97 or other similar prices hard-coded into them as business rules for discounts or not eligible for discounts!
-
RE: --no-preserve-common-senseposted in Side Bar WTF
Core stuff like rm don't do that. Why? I'm assuming compatibility.
The reason is not just compatibility. It is because us server admins don't want rm and every other basic command to install a bucket load of GUI shared libraries just so that someone can have their pretty pop-up window.
Plus, if you have ever had to repair a system that barely boots and you don't have the right kind of boot disk/CD handy or can't reboot, you are very thankful when the very simple programs like ls, cat, and rm at least work (and even ls is optional).
Greybeard rant: If some users need crutches like pop-up windows to remind them what to do, then they can use GUI programs instead of the core CLI utilities. ;)
PS: And it would be much better if more helper programs existed for novice users, rather than giving them magical incantations on forums to solve basic config problems.
-
RE: Linus RAID failure: suspense / horror thriller for IT professionals (video)posted in Side Bar WTF
If you have a mission-critical, single-point-of-enterprise-failure, not-properly-backed-up server (which, granted, you never should have, but we've all seen it happen) and it starts falling over, the first thing you do is not keep it running while putting extra load on it with a backup job. You don't know what's wrong with it yet; until you do, you have no idea what it's about to do to your data.
Yes! You explained this better than the rant that I was going to write.
There are so many wtfs in that video, as was pointed out with their initial setup and recovery procedure.
Another wtf that I will point out is using a second power supply to power some of the drives, but connecting the data cables to a different system. Unless you know for sure that the power supplies are the same and are both working correctly (like in a system designed for redundant power supplies), this is a bad idea.
I'm not an EE and don't know all of the intimate details, but "ground" and "n volts" lines coming out of any power supply may not be as expected. The ground line may be any voltage (like +2V) but the other power lines coming from the same supply are offset consistently and so the supply works.
By using two power supplies, one drive/mobo could be sending signals at, say, 7V relative to the ground of the other supply (for a really bad power supply), and receiving end of the signal is designed to receive 3.3V, which will fry the receiving end... leading to more data loss. Bonus points are awarded if he used the power supply out of the dying system, but that was not stated in the video.
Just like with their initial setup with the RAID cards, using cheap/incorrect parts to monkey something together is just asking for more trouble...
-
RE: Symantec email exploit bites Symantecposted in Side Bar WTF
I'm not sure what all the excitement is about running as an administrator.
Viruses don't need to do that to cause lots of damage.
- Your computer can be used as a spam bot or the like with your everyday account, and
- If any of your files are accessible (which they probably are if you do anything useful with your computer) then malware can delete, upload copies, or encrypt all of your files.
No admin privileges needed to do a lot of damage.
So a good AV scanner is needed, but not the crap that auto-executes the viruses for you...
-
RE: Horrible bank security practices (not really news)posted in Side Bar WTF
I was a happy little Australian with my chip-and-PIN card... and then all the banks started issuing all this NFC bullshit, where just putting the card near the reader for two seconds is enough to authorize any transaction of up to $100. Didn't ask for that. Didn't want that. No way to turn it off either, without risking destruction to the chip.
This is the worst thing with the new cards. (In Canada it is $50 max, but still...). First they start by increasing security using Chip-and-PIN for bank and credit cards, and then then they take it all away for "convenience" of paying quickly, because typing in your PIN takes an extra 5 seconds at the checkout.
A while ago I was at a currency exchange place, which accepts only cash or debit (bank card) as payment for buying another currency. I took my C-n-P bank card out of my wallet and set the wallet down near the reader. Put the card in the slot and immediately the reader showed some failure message and quit. The teller insisted that I was trying to use a VISA card and that they won't do credit card cash advance. After a few minutes of pleading to just try it again, the second time it went through okay. It wasn't until after I left that I realized that my C-n-P, NFC VISA was in my wallet and was probably picked up by the reader. (Which I suppose it could have also randomly picked the other NFC credit card that I had in the same wallet.)
And no one around here (banks or customers) seem to care that everyone is a walking ATM for the bad guys. Sigh.
-
RE: Microsoft is limited to receiving 100 emails per day?posted in Side Bar WTF
@spencer said in Microsoft is limited to receiving 100 emails per day?:
Implying Microsoft's spam filter has never seen a receipt before. Or a newsletter. Or any other legit templated email.
Not so. If our receipts look spammy because of some words used, formatting, or whatever triggers their spam filter, then that is what it is. Other receipts, newsletters, or whatever else may not look like spam. But you have to know "for sure" that you are looking at spam or ham (based on whatever your definition of spam is) before training your SNDS alert to fire off a report saying "I think I have seen 100+ spam messages from you and therefore your server is compromised".
Why should that be my problem to figure out why SNDS is alerting our ISP? If I am confident that our server is not sending spam (and I realize that there are lot of servers that do get compromised) then I don't really care if my ISP wants to subscribe to SNDS. Just stop forwarding them on to me and everyone is happy.
These two statements seem incongruous with each other. Either you want to know why your emails are being considered spam, or you don't. I daresay a number of your potential customers may not have an alternative, non-Hotmail address and may be frustrated enough at not being allowed to use (and having to set up another somewhere else) it that they'd take their sale elsewhere. It literally costs you nothing but a little time to sign up, you'd get to learn why they're being filtered and improve your service for everyone. Not to mention bragging rights within your company for being the one that worked it out.
I think you are assuming that I care why SNDS is alerting my ISP and therefore should sign up for SNDS. I don't care why it is sending out reports. False positives are a fact of life, they aren't a big enough problem to impede our ability to sell services, and there is an acceptable work-around, which is for the customer to look in their junk folder.
Of course the big-wigs have discussed this topic already and have decided that it is not worth the time to investigate further after that first report. There is always a cost of time input to solving the problem. Furthermore, even if we did sign up for SNDS, there is no guarantee that we can solve whatever is causing them.
TLDR: I don't want the SNDS reports and for now don't care why Microsoft is complaining. We took the first complaint from our ISP seriously and now that I am sure we are not spamming (aside from false positives), I don't want our ISP to keep forwarding false alarms to me.
-
RE: More Excelence in spreadsheet-landposted in Side Bar WTF
@bb36e said in More Excelence in spreadsheet-land:
@quijibo said in More Excelence in spreadsheet-land:
Excel runs scripts after users clicks "Allow". News at 11!
Excel also performs HTTP requests without any confirmation:
...
No, it does not. Excel 2010 does not support IMPORTXML and the article only talks about Google Sheets. If Excel does support some method for doing HTTP requests, my guess is that it would either prompt to run scripts when you open the file, or prompt about a cross-site request (local file loading from the web) before it makes the request.
From the article:
Well recall that while we cannot run macros in Google Sheets, we can absolutely run formulas. And formulas don’t have to be limited to simple arithmetic. In fact, are there any Google Sheets commands available in formulas that can send data elsewhere? Why yes, there seem to be quite a few. But lets take a look at IMPORTXML in particular.
I already feel dirty for defending Microsoft, but let's not spread misinformation.
-
RE: Android phones might crash when calling 911posted in Side Bar WTF
@jaloopa said in Android phones might crash when calling 911:
I had a Hero, which was basically a Magic (known as the G1 in the UK) without the hardware keyboard or factory underclocking.
Actually the Magic did not have a hardware keyboard. The Dream (G1 in US) did. Incidentally, all of the Android phones that I've owned had a hardware keyboard until I bought a new phone just recently.
-
C#: Using a Uri to percent encode dataposted in Side Bar WTF
So I've spent most of this week working with a partner organization who is having troubles sending data to our API. The API requires that the data be percent encoded according to RFC 3986 (in short, the usual % encoding of non-alphanumeric, - . _ ~, and UTF-8 encoding of non-ASCII characters).
When they sent us a person's name that had all three of é, a space, and an apostrophe, it would be encoded wrong and cause our API to reject the request. I sent them an email to check their non alpha-numeric characters and make sure that the encoding was right. First they tested unicode characters and got back to me... nope those work. Then I explained that in Java, the URLEncoder makes spaces a + instead of %20, so check that too... nope, that works.
Finally they get back to me and say it was the apostrophe. That seemed odd, as in my experience URL encoding libraries usually encode apostrophes too (Java, JS, Python off the top of my head). It turns out that their "fix" is to use this code in C#:
foo = new Uri("Person's name"); postData += foo.Query.Replace("'", "%27");When I see this, I figure that there must be a better way than passing data into a Uri class to be percent encoded, but I don't use C# regularly. I did some Googling and apparently this is what people do in C#? 1, 2, (or write their own encoder).
I mean, why would it be a normal procedure to pass free-form data into a "URI" (which may be a theoretically valid URI) just so you can percent encode it? wtf
-
RE: My web app died from performance bankruptcyposted in Side Bar WTF
@pie_flavor That's why Sun invented Java Web Start :)
-
RE: SHOCKING NEWS: Big Banks Not Ready For Mobileposted in Side Bar WTF
Hey, I thought that was my bank! But now I can do you one better:
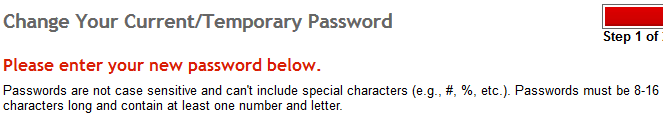
^^^ "Passwords are not case sensitive..."
At least they're 8-16 characters. That makes up for reducing the alphabet down by nearly half, right?
-
RE: AV Warning: This string triggers Avast & AVGposted in Side Bar WTF
This reminds me of the time I was investigating some PHP files infected with PHP malware and Windows Defender was helpfully deleting them without telling me. Even though I was saving them from Notepad++.
The only thing worse than that was for some scanners to automatically quarantine files. Not only would the user be confused as their files disappeared, but then they were placed in that special folder so that the virus could accidentally be rerun at a later date! (For example, if someone uninstalled the scanner and then went snooping around their hard drive.)
One of the first thing I always did after installing our corporate-approved scanner was to turn off the quarantine entirely (either delete, clean, or whatever was possible), and especially for myself to have it ask first before taking any action.
-
RE: FTP is just as goodposted in CodeSOD
Fair enough. An argument made on actual measured results is good enough in my books!
-
RE: Runtastic cannot into privacyposted in Side Bar WTF
Sadly, in the US just by changing the id in the url you are already guilty of "hacking" the site. Personally, I wouldn't post such information unless being very sure of your anonymity.
For some examples of past cases, see:
-
RE: Texmaker doesn't like filenames with spacesposted in Side Bar WTF
Sort of. The Teχ tools assume they're running as some sort of pipeline, ...
What?!? No!
latex filename latex filename latex filename dvips filename.dvi ps2pdf filename.psThe output contains info about what it is doing and any error messages.
One reason that dragging a file into a shortcut may not work, is that latex expects the CWD to be the directory where your latex file/project is, when you include other files into your top-level tex file (and also graphics).
-
RE: The Story So Far, or what the hell has mikeTheLiar Been Up to for the Past Two Yearsposted in Side Bar WTF
@asdf said in The Story So Far, or what the hell has mikeTheLiar Been Up to for the Past Two Years:
@Jaloopa said in The Story So Far, or what the hell has mikeTheLiar Been Up to for the Past Two Years:
it's possible to do it in Java with enough abuse of reflection.
I recently had to replace a
private static finalfield via reflection for a unit test. I still feel dirty.That variable must have been pointing to an object. That wouldn't do anything useful for primitives (including strings). The compiler will inline the primitive value anywhere it is used.
That was a common issue for our new hires when one of our classes stored what was really a configuration setting in a
public static final String. Rebuild that class only (as in command-line javac) and no other classes see the new value.Now we use IDEs that rebuild dependencies and config files (well, in more places... it could be better).
-
RE: Google Authenticator API - like dragons, for cansposted in Side Bar WTF
@Parody said in Google Authenticator API - like dragons, for cans:
There are a couple of plugins for KeePass for Windows that give OTP functionality, in both the "you must provide an OTP from somewhere else to open the database" ...
What exactly does that protect the database from?
I did some searching to see if my new security key could be used to add 2FA to my KeePass database and by end of that I was convinced that having OTP in KeePass (or for any static file) makes no sense. For example, if OTP changes after each use, then the static file must be re-encrypted with the next OTP to be able to open it next time. However, if a bad guy has an older copy of the file then the previous OTP that was used to open the file would be forever usable, which defeats the purpose of a one time password.
The closest (and possibly best) idea that I can think of is to use the GPG key on my security device (along with a password) to encrypt the database. That creates a 2-factor system because the security device never discloses its GPG key and needs to be present to open the file, but this is not an OTP.
-
RE: Microsoft is limited to receiving 100 emails per day?posted in Side Bar WTF
@wft said in Microsoft is limited to receiving 100 emails per day?:
Do your emails have the usual stuff like DKIM and SPF?
We have SPF but not DKIM. As @japonicus also said, it doesn't seem to matter in my experience. I know for many years now a few of our emails get lost in Hotmail accounts (like when replying to someone who has emailed our support address). But that situation is rare and for the most part if people use Hotmail and need to interact with us everything seems fine.
-
RE: "Le mobile multifonction"posted in Side Bar WTF
Meanwhile in Canada, some purists complain about how Quebecois should pronounce PK Subban's name. (Hint: He pronounces his own name as you would in English.)
-
RE: target=_blank exploitposted in Side Bar WTF
@cartman82 said in target=_blank exploit:
Apparently, if you open a site with target="_blank", they can reach back and mess with your original window, including transfer you to a phishing website.
Hey, now! Don't go messing with features that some of us really, really need. Like the ability to change the DOM in the parent window's page from the child window. Yes, we actually do this on our site.
But IIRC, that it only works if the two windows are on the same host and protocol (HTTP/S). Cross-domain scripting restrictions should prevent that. And then if you want to cross domains you need to use window.postMessage(), which allows the recipient to check the sender's domain before processing message.
-
RE: Pretty Aggressive Codeposted in Side Bar WTF
Also, and this is the part that hurts me professionally, the way that Guid columns have to be cast to string, to accommodate the extra column's info. So not only do we lose type safety, there is an additional burden on the process to break it up into 2 different pieces of data.
I think that you've made a wrong assumption that they even care about the contents of the ClientId column at all. Since they are too lazy/incompetent/whatever to change their code for the new column, it is very likely that they simply take the string contents of ClientId and use that as-is to store into their local database. As far as they are concerned, they need no changes because the data will just go into a text field and use string compare in their code (probably with case sensitivity too!).
In other words, if the client type changes in that compound string, I'm willing to bet that the client will be treated as a brand new client on their end.
I have seen something similar happen before, and now when I see an idea like the one proposed here the alarm bells go off. That, after having had to clean up the mess when another group didn't understand that an internal user ID needs to be unique and immutable for as long as the user exists (at least in our system).
-
RE: The discovery of Apache ZooKeeper’s poison packetposted in Side Bar WTF
...it gets an out of memory exception...which was not handled. Let me say that again: Not caught...
You cannot catch OOM exceptions in multi-threaded Java application and expect to go on doing useful work, because you do not know what other threads may have died due to the same OOM condition. That is, right before the OOM was thrown to the leader, all other threads may have tried to allocate a reasonable sized object from the heap and also got OOM exceptions. There can also be issues with lower-level resources not allocated or cleaned up properly in other threads due to the OOM.
There may be some small cases where OOM can be handled gracefully, but in the general case the only thing to do is to exit the program as gracefully as possible at that point.
So if anything, this is more of a Java
 than ZooKeeper.
than ZooKeeper. -
RE: Cloning drivesposted in Side Bar WTF
I can't believe all of those crappy 90's cloning programs still exist. Who buys (or even tries) that crap?
The proper procedure:
- Download CloneZilla and burn to CD
- In CloneZilla, run
ntfsresize --size ###G /dev/sdaX - Resize the partition using fdisk (make it slightly larger than the number above just in case of rounding issues)
- Run CloneZilla (
ocs-live) to clone the disk - If the boot sector isn't restored, use a Windows CD to repair the boot sector.
I've done this twice on my main Windows 7 desktop to move to SSD and then a larger SSD later, and numerous disk upgrades for other people. Works every time. CloneZilla even has an option to delete pagefile.sys and hiberfil.sys before cloning.
The only thing that would be better is that CloneZilla could do the ntfsresize steps as part of the nice menus that it has.
-
RE: Hooray for encrypted home directoriesposted in Side Bar WTF
Seems to me the biggest wtf is that your encrypted files are freely accessible just because you're logged in on a different terminal. Could Linux not manage it so that only the session that's actually authenticated has access to the decrypted data?
No. If you are an administrator (root) on a system... even a Windows system... you have access to everything. That follows from the simple fact that the administrator can load modules/drivers into the kernel and therefore access all memory or impersonate anyone on the system.
Your basic filesystem permissions protect one user from another though, regardless of encryption. So unlocking your home directory when you log in isn't introducing a big risk that other users will now have access to your files, unless you mess up the filesystem permissions too.
-
RE: AV Warning: This string triggers Avast & AVGposted in Side Bar WTF
... well yeah. What would be the point if it told you you had a virus after it let you run the file?
I think he means from the old days when an AV scanner would suck all of the CPU time trying to scan into a large zip file or whatever. You couldn't do anything until it finished. And then of course that was "fixed" by setting a maximum scan time (at least in McAfee), so then who knows if zip would get scanned properly not... among many other
 s related to scanning zip files.
s related to scanning zip files.



