And THIS kind of BS is EXACTLY why I have NoScript ON by default, EVERYWHERE
-
An oldie, but...
-
Not exactly a lethal weapon, is it?
They'd make mildly decent blunt instruments. And then when they broke, they'd have jagged edges. Soooooooo... Yeah, totally could be.
-
As terrible as Java was, at least it didn't have any problems with third-party code injection. At least, none that I've heard of. Then again, this isn't really JavaScript's fault. It's HTML's fault. As far as I know, there are no injection vulnerabilities in JavaScript programs that aren't also HTML programs.
-
@Lorne_Kates said:
Actually, they're designed to float, but not completely. If they were design to not float, they'd sink.
Maybe they are designed to not float, but the designers are incompetent. EVER THINK OF THAT!?
-
You mean there are no scripts out there that might pass unsanitised strings to
eval()?And yes,
eval()is a level of stupid beyond all others; why that was ever part of the language, I'll never understand.
-
I don't think people could be stupid like that. Please don't appropriate my world view.
-
Fair enough. Counter-point, explain why the VAST majority of infection points in the last 5 years have been either: Flash, Java Applets, or JavaScript based? Why is the TOOL itself, not a PROBLEM? I don't CARE who is responsible for it. If the browsers are implementing it wrong, it is still a problem, isn't it? Can't we as a professional group of people do better than this steaming pile of crap? Do we need laws to force companies and people to stop this nonsense and FORCE security at the design stage? How pathetic is that?
If you demand a tool that programmers can use that will not allow them to shoot themselves in the foot, do stupid things, and cause security holes...you're going to have a bad time. Such a thing cannot reasonably exist and still be usable for a wide variety of applications. And, if you did get it, you would be constantly pissed at its shortcomings that you would have to work around.
-
Does it throw a projectile? If not, it's not really a gun, but just called that due to the overall shape.
-
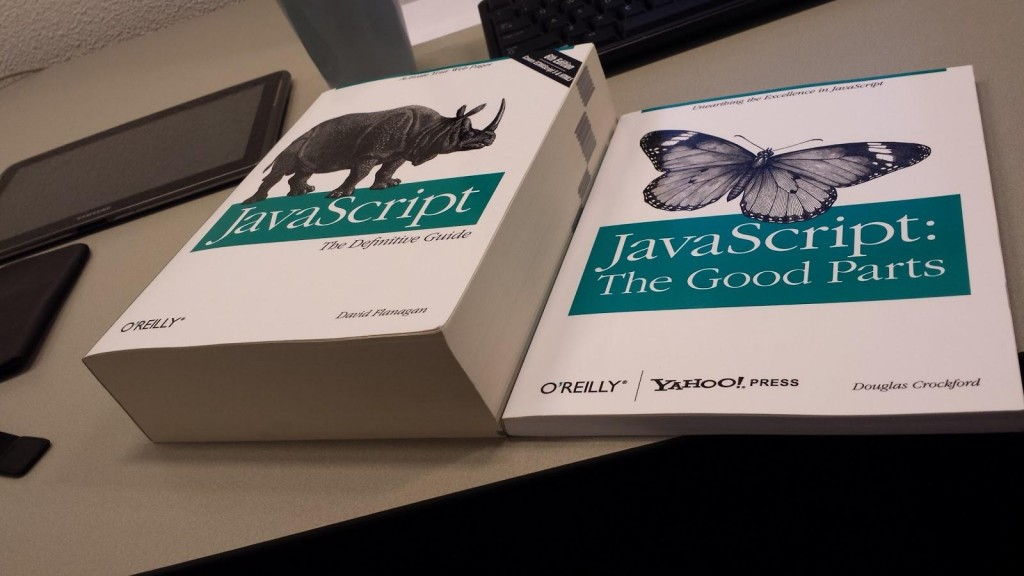
An oldie, but...
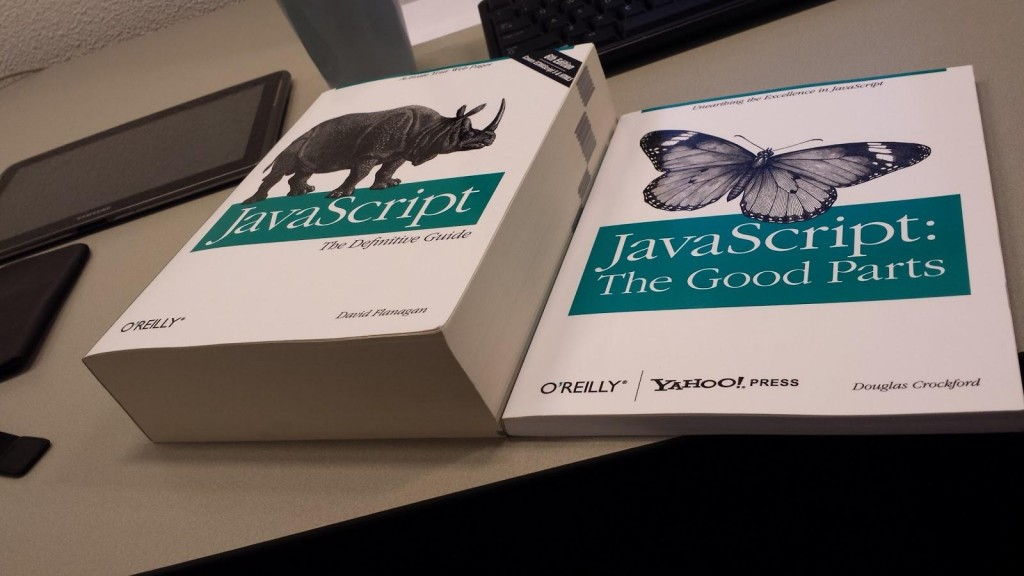
Obviously "The Good Parts" book has a fair amount of fluff in it. It really should be a pamphlet that you open and it says, "You can use it basically anywhere there is a CPU".
The end.
-
You can use it basically anywhere there is a CPU
Isn't that true for pretty much any language that can be compiled or interpreted?
-
Shut up Ben.
-
And yes, eval() is a level of stupid beyond all others; why that was ever part of the language, I'll never understand.
Maybe it should have been a total (non-turning-complete) language as well, if it was just for page interactivity. Would be easier to assess the safety of code.
-
I bet, if that had happened, someone would have extended it to be Turing-complete anyway; hell, XSLT is Turing-complete!
-
I'm actually amazed it's possible to write such a thick book ("definitive" or not) about JavaScript. It's a pretty small language.
-
It wouldn't surprise me if the thicker book is 90%+ about DOM and/or jQuery instead of JS
-
-
Dude, it even includes an overview of CSS! and yes, a whole bunch on jQuery and HTML5.
-
OK, so the balance is more like 30:70 JA:other stuff; there's still a helluva lot of DOM and jQuery in there
-
And thus a new generation of annoying fuckers who say "JavaScript" when they mean "DOM".
-
Even if it was Javascript's fault (looks like it's not) what is the point in turning it off by default? The only sites that would be a security risk to you will be ones you are actually doing business with, which would be, I suspect, the same ones you would whitelist.
You can't win, basically. Just give up.
-
It's not just security issues; it's also about stopping intrusive ads and data harvesting
-
Yes, thank you for that, we totally needed to know you like to use children's toys as murder implements. We didn't already hate you. Great job.
-
Yes, thank you for that, we totally needed to know you like to use children's toys as murder implements. We didn't already hate you. Great job.
How many trans teens must perish to satisfy Fox's nerfrotic asphyxiation fetish?
-
It's not just security issues; it's also about stopping intrusive ads and data harvesting
I mean, I'm not a huge fan of intrusive ads nor data harvesting but neither one of those compares to getting malware infected or passwords stolen.
-
-
Emmm.... you never heard VBScript?

-
@RaceProUK said:
It's not just security issues; it's also about stopping intrusive ads and data harvesting
I mean, I'm not a huge fan of intrusive ads nor data harvesting but neither one of those compares to getting malware infected or passwords stolen.
You do know some malware is distributed via ad networks?

-
I realize you are joking, but you know damn well that the TOY you cited does not meet the primary dictionary definition of a gun. Quit trying to deflect.
Actually, while toy guns may not meet your definition for gun, they can meet definition of gun in law if properly modified.In Hong Kong, you're required to have gun license in order to use pepper spray designed for ladies to protect themselves, or any "toy gun" that can shoot projectile with power higher than 2 joule.
The line is finer than what you may think.
-
I mean, I guess my sarcasm tag closes sometimes.
-
What ads? You mean the static images that look like this?
-
What ads? You mean the static images that look like this?
If it's a static image, why did you Discupload it instead of linking to it?
-
I didn't bother to look at the proportions - I just saw jQuery and posted the link.
-
Due to the way it's served, the link would break next time the site reboots.
-
Due to the way it's served, the link would break next time the site reboots.
Then it isn't really static, is it?
-
Well, the image doesn't change, but the URL used to access it is a randomly generated UUID.
-
C was designed to be a systems language, then later, people started writing games in it. Since C wasn't designed for games, does that make it a bad idea to write games in C?
Yes it does, because most game libraries are in C++. Using a language where you have to roll your own vtables, where you don't have constructors, destructors, namespaces, inheritance, templates, etc., and where there aren't as many compatible libraries means unnecessary suffering!
If everyone in this thread is going to be a pedantic dickweed motherfucker, I'm going to be one, too!
-
Sure, they're in C++ now, but what about before it existed?

Also, IIRC, Sonic Spinball (from 1993) was coded in C at a time when console games were still mainly done in assembly.
-
Because, uh... it's effectively the only language nowadays that runs client-side?
My SONAR install and all the virtual instruments I use with it, all the 3D modeling and character generation software that comprise my asset pipeline, and my entire Steam library beg to differ.
-
So what, are the image bits stored as a BLOB in a table somewhere, or is there actually a gif/png on disk somewhere?
-
Sure, they're in C++ now, but what about before it existed?

Yes, that was a problem for people in the late 80's and early 90's who were targeting modest console hardware running a 6502 or Z80. However, their projects were also much simpler and probably didn't require complex polymorphic objects.
Also, IIRC, Sonic Spinball (from 1993) was coded in C at a time when console games were still mainly done in assembly.
I have a couple of André LaMothe game programming books of that vintage, and he spends a couple sentences in each talking about how great C++ is with its constructors and destructors, but all the examples are plain C as a courtesy to the lowest common denominator. I can imagine there was some eagerness to make the jump to a higher level language as soon as hardware allowed developers to develop in something other than hand-coded assembly.
-
There's a PNG outside of the webroot.
-
So how is libelously accusing people of being murderers okay?
-
So how is libelously accusing people of being murderers okay?
#THE CORRECT TERM IS "SO HOW IS LIBELOUSLY CALLING PEOPLE MURDERERS OK?"

#FUCKING HELL YOU LITERALLY CAN'T GET ANYTHING RIGHT!
Filed under: SHILCPMO
-
-
That was before the official ratification of SHILCPMO. You're judging a final product on it's pre-release alpha.
Also, the only way you could have found that is by using DiscoSearch, so really-- I think I've caused you more than enough pain for today.
-
As terrible as Java was, at least it didn't have any problems with third-party code injection.
Actually ...
The most underrated, underhyped vulnerability of 2015 has recently come to my attention, and I’m about to bring it to yours. No one gave it a fancy name, there were no press releases, nobody called Mandiant to come put out the fires. In fact, even though proof of concept code was released OVER 9 MONTHS AGO, none of the products mentioned in the title of this post have been patched, along with many more. In fact no patch is available for the Java library containing the vulnerability. In addition to any commercial products that are vulnerable, this also affects many custom applications.
In this post I’ll be dropping pre-authentication, remote code execution exploits that leverage this vulnerability for WebLogic, WebSphere, JBoss, Jenkins, and OpenNMS. All on the newest versions.
-
@Lorne_Kates said:
You're judging a final product on it's pre-release alpha.

@Lorne_Kates said:Also, the only way you could have found that is by using DiscoSearch, so really-- I think I've caused you more than enough pain for today.
http://i.imgur.com/oGmpcEX.jpg
-
@Lorne_Kates said:
All joking aside, though-- fuck JavaScript.
I just picked up a JavaScript book today morning with my hard earned moneyz. Now I am confused.

-
Now I feel like I've completely got a shitty book. I thought the Doug crockford book was what everyone read to write JavaScript without going insane ?
-
write JavaScript without going insane

That's like trying to write readable Perl code. Or non-shitty PHP code.


