WTF Bites
-
Countdown timer on my phone ringed 2 minutes late.
HOW DO YOU EVEN FUCK THIS UP!?
-
@levicki said in WTF Bites:
@Vixen Let's see:
void MyUberSecurity(MyStupidUser u, My3DObject o) { Watermark wm = DetectWatermark(o); if (!wm.Present() || (wm.Present() && wm.Owner == u)) { LetUserDoWhateverTheFuckTheyWantWith(o); } else { YellAtUser(u, "BITCH! SPANK SPANK SPANK"); } }Did I get that right?
FTFE
-
@Gąska
Off byonetwo thread is
-
@Luhmann off by 1:53 to be precise. Yes, it showed me exactly how much it was late.
-
@Luhmann off by 1:53 to be precise. Yes, it showed me exactly how much it was late.
At least it's honest.
-
From the WTF-I-don't-even shelf of youtube:
NANOWAR OF STEEL - Valhalleluja (ft. Angus McFife from Gloryhammer) | Napalm Records – 06:42
— Napalm RecordsHorse Meatballs indeed.
-
@cvi I was going it's pretty cool and certainly an interesting idea - then I've got to 2:45.
-
@Gąska Yeah.
-
@levicki said in WTF Bites:
HOW DO YOU EVEN FUCK THIS UP!?
By having Android phone? CPU was too busy running crypto-mining to do the actual task.

Given your attitude to built-in security features, I can see how you can run in this scenario on regular basis.
-
@levicki said in WTF Bites:
HOW DO YOU EVEN FUCK THIS UP!?
By having Android phone? CPU was too busy running crypto-mining to do the actual task.

Given your attitude to built-in security features, I can see how you can run in this scenario on regular basis.
But you don't understand. Android is the haxxored!!(one)ELEVEN
-
@levicki said in WTF Bites:
@sloosecannon Find me an application in Apple Application store which can install itself so that there is no icon to prevent removal, which can display full screen ads over other applications, and even obscure system settings pages by painting over them.
Never seen it on Android either. Only heard it in scary stories from people too smartass for their own good.
-
@levicki did you even read the article?
Google Play Protect detects and blocks malicious apps, including ones using this technique.
-
@levicki the necessary precondition for

 to escape the barn is to install random apps that weren't verified by Play Protect. If you need an NK-style walled garden to avoid shooting yourself in the foot, that says more about you than about Android.
to escape the barn is to install random apps that weren't verified by Play Protect. If you need an NK-style walled garden to avoid shooting yourself in the foot, that says more about you than about Android.
-
@levicki or does it? Because it clearly says that in order to have this problem, you have to install the malicious app in the first place.
-
Chromium updated today to 79.0.3945.79 (using the "official" Ubuntu build) on my work machine. Now it freezes in OWA and Jira.

Anyone else seeing this? Lately I've been noticing Chrome having trouble keeping up in gmail and facebook's tab is often blank when I come back to it. I usually have a gmail and fb and tdwtf tab sitting open all the time. I figure the fb thing is the tab freezing stuff that takes a while to recover for a big site like that. No clue what's going on with chromium or gmail. It's not like RAM is in short supply (16G VM on a 32G host at work and 24G at home, nowhere near fully utilized) and when chromium freezes there's no noticeable CPU utilization from it.
-
@levicki said in WTF Bites:
@levicki or does it? Because it clearly says that in order to have this problem, you have to install the malicious app in the first place.
You say that like that's something hard to do on Google Play store.
If you only install Play Protect-verified apps, then yes, it is indeed hard to do. If you just can't help yourself and absolutely must install every Temple Run clone you can get your hands on, that's not a software problem.
Also, see the edit above.
What edit? You haven't said what you added and your edit history is hidden.
-
@levicki said in WTF Bites:
Never seen it on Android either. Only heard it in scary stories from people too smartass for their own good.
The vulnerability allows malicious apps to masquerade as legitimate apps that targets have already installed and come to trust, researchers from security firm Promon reported in a post. Running under the guise of trusted apps already installed, the malicious apps can then request permissions to carry out sensitive tasks, such as recording audio or video, taking photos, reading text messages or phishing login credentials. Targets who click yes to the request are then compromised.
That's just the latest one.
There is no application mentioned in the Google Play store that matches the description you asked for there. As a reminder, you said:
@levicki said in WTF Bites:
Find me an application in Apple Application store
And then proceeded to post an article about apps that were blocked, from the play store, by play protect.
This does not mean there was no vulnerability, however it does mean they were exploitable if that app was installed outside of the Play Store.
-
@sloosecannon said in WTF Bites:
@levicki said in WTF Bites:
Find me an application in Apple Application store
And then proceeded to post an article about apps that were blocked, from the play store, by play protect.
Um, not quite. AFAIK not all apps stored in Play Store are protected by Play Protect.
(I might be wrong but I really really wanted to write that sentence.)
-
@sloosecannon said in WTF Bites:
@levicki said in WTF Bites:
Find me an application in Apple Application store
And then proceeded to post an article about apps that were blocked, from the play store, by play protect.
Um, not quite. AFAIK not all apps stored in Play Store are protected by Play Protect.
(I might be wrong but I really really wanted to write that sentence.)
Pretty sure they are, now. In fact I'm pretty sure that all Play Store apps are Play Protected when you upload them, because that's how the Play Store team keeps their Play Store Protected.
-
-
@levicki said in WTF Bites:
@error said in WTF Bites:
Fucking Citrix environment wipes out my IE settings
Are you sure it's not a bad GPO?
AFAICT the VMs they let me remote into are re-imaged nightly.
Filed under: But please, continue to jump to conclusions with little to no information.
-
@levicki said in WTF Bites:
majority of people using Android do so because they can't afford flagship phones from big brands.
Man, those Android phones are so cheap.
Only poor people use Android! They should save up and buy an Apple.
-
-
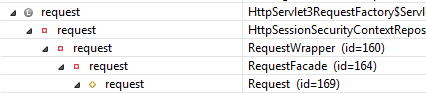
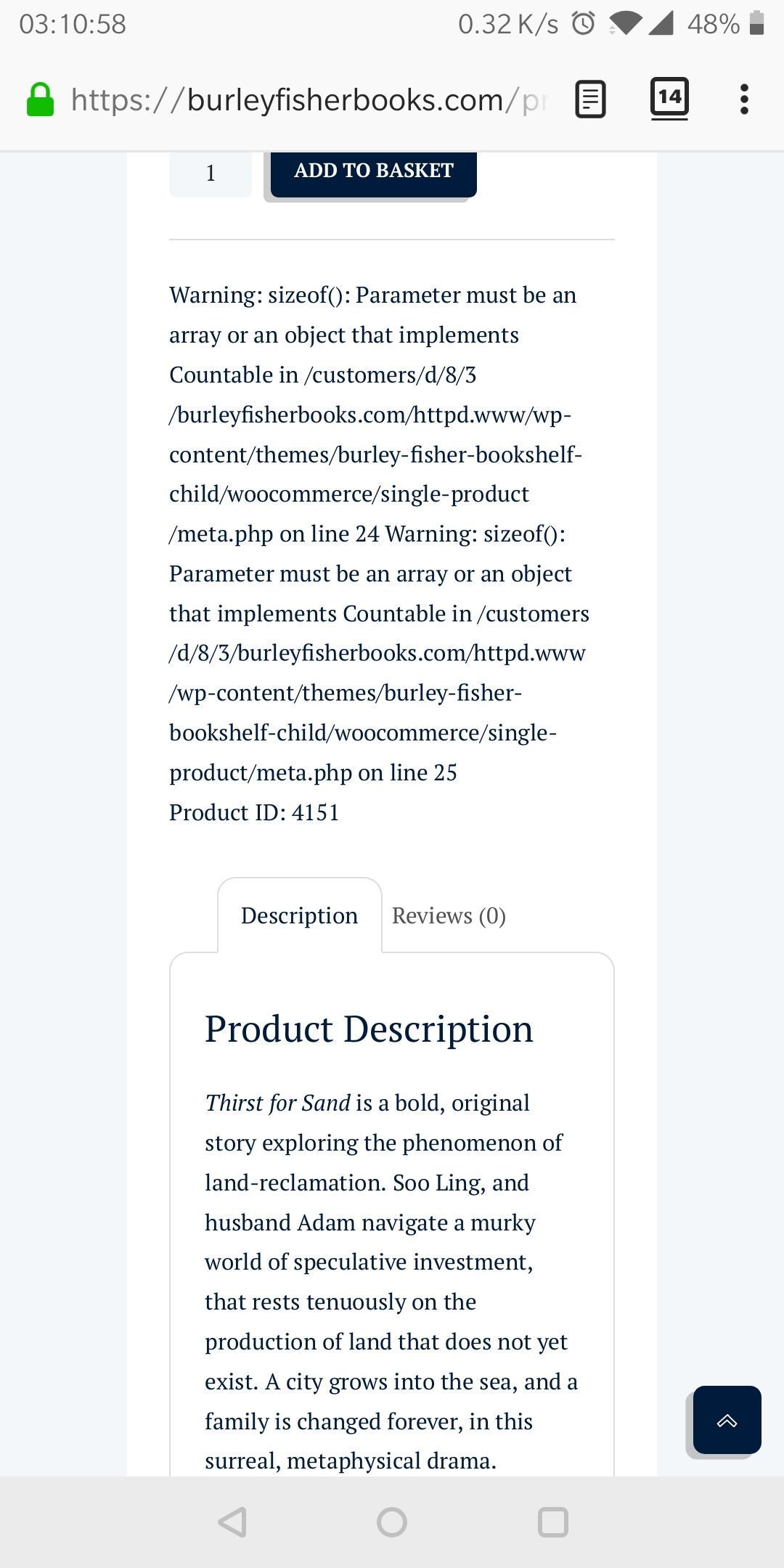
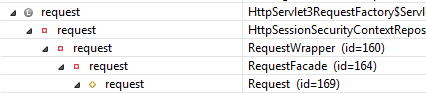
The decorator pattern strikes again. It's extremely pervasive in JavaScript land.
-
@error This is Java, Spring framework specifically, which has lots of wrappers and delegates for reasons that I'm sure are compelling. But it makes it annoying to debug when the thing you're looking for is a riddle, wrapped in a mystery, inside an enigma
-
This is Java,
I gathered from the word "Servlet", which is Javanese. Just sayin', I work with JS all the time, and so I see that shit constantly.
But it makes it annoying to debug when the thing you're looking for is a riddle, wrapped in a mystery, inside an enigma
You have no idea...
-
The only reason I haven't dropped $2.5K on a Galaxy Fold is I've heard multiple reviewers say they are fragile, and report damage to the device within the first 30 days.
Filed under: Cue Levicki somehow twisting this into an Android problem., Conveniently forgetting BendGate.
-
@error This is Java
What do you think "Java" in "JavaScript" stands for?
-
@error This is Java
What do you think "Java" in "JavaScript" stands for?
European Computer Manufacturers Association
-
@error touchę.
-
-
Giphy said in https://giphy.com/gifs/sparta-Ny4Ian52lZDz2 :

-
Speaking of Javascript, sometimes when I put a breakpoint in Firefox's JS debugger, it completely stops working. It shows "paused on breakpoint" but hitting either the step over or continue buttons does nothing.
-
@hungrier Also, sometimes
$('selector').load(url,data)will work fine, but the next time I try it I get TypeError: e is undefined from some function deep in the bowels of jquery.min.js
-
@hungrier Lets play: Try to figure out WTF
Non-working code, obviously and clearly wrong:
let idCheckboxes = $('.whatever'); let ids = idCheckboxes.filter(function (i, cb) { return cb.checked; }).map(function (i, cb) { return Number(cb.dataset.relevantId); }); let data = ({ 'ids': ids, // rest of the data }); $('#selector').load(url, data);Fixed code:
let idCheckboxes = $('.whatever'); // this is the only different part let ids = []; for (let i = 0; i < idCheckboxes.length; i++) { let cb = idCheckboxes[i]; if (cb.checked) { ids.push(Number(cb.dataset.relevantId)); } } let data = ({ 'ids': ids, // rest of the data }); $('#selector').load(url, data);
-
@levicki and yet, the only times I hear about Android malware is in angry rants coming from power users.
Also:
-
The docs for map say:
As the return value is a jQuery object, which contains an array, it's very common to call .get() on the result to work with a basic array.
Have you tried that?
-
This where clause fragment (in oracle)
CASE WHEN REGEXP_LIKE(NAME,'...') THEN (SELECT MAX(1) FROM ... WHERE ...=NAME) ELSE 1 END = 1
-
@PleegWat can you compare empty sets with integers in Oracle SQL? Also, I seriously hope NAME is a unique key...
-
@Gąska NAME was from the outer query, but would never match more than one row.
The subquery aggregates so it always returns one row; if the condition is false for all rows the value is NULL.
The new DB version didn't like it. I rewrote it to the slightly less
(NOT REGEXP_LIKE(NAME,'...') OR NAME IN (SELECT ... FROM ...))
-
@Zecc So
 is Jquery's "something like an array except it breaks Jquery functionality" object
is Jquery's "something like an array except it breaks Jquery functionality" objecte: It was so simple, I'm wondering why Jquery's AJAX function wouldn't just do that when it detected their own friggin object instead of an array, rather than barfing with an unhelpful error.
-
@levicki said in WTF Bites:
Each vulnerability you find on iOS I can match on Android:
Then that only leaves one sane choice. Tizen.

-
@levicki said in WTF Bites:
Also:
Each vulnerability you find on iOS I can match on Android
To my knowledge, the reverse doesn't hold true, but by all means you guys keep trying to prove me wrong -- I am enjoying it.
I'm pretty sure enjoying mobile OS flamewars has its own ICD-10 code.
Just think about it -- taking pictures, sound and video without having camera permission. Can it get any worse?
Depends. Have you been removing any "optional" components from the system?
-
@levicki said in WTF Bites:
Just think about it -- taking pictures, sound and video without having camera permission. Can it get any worse?
The only thing worse than that might be if there was a way to make a user accept a video call without their consent or requiring any malware at all.
-
Let's also not forget that the very first iPhone jailbreak was a buffer overflow exploit in an image file in the web browser that executed arbitrary code with root privileges without requiring user interaction (just viewing the image file).
Very safety. Such secure.
-
Oh, and there was that time when rendering a certain string of text in any app (including SMS) would crash the phone.
Again, no malware required!
-
@error But iOS is malware.

-
-
is a riddle, wrapped in a mystery, inside an enigma
Parabola of confusion?
-
I'm pretty sure enjoying mobile OS flamewars has its own ICD-10 code.
It's more like an ID-10-T one.
 Vulnerability in fully patched Android phones under active attack by bank thieves
Vulnerability in fully patched Android phones under active attack by bank thieves