How not to do UUIDs
-
-
Related: https://what.thedailywtf.com/post/1370374
Swann Security has blamed a factory error for the data breach - which was brought to its attention by the BBC - and said it was a "one-off" incident.
It was an incident with their "one-offs", rather.
-
@zecc How about this?
Swann's spokeswoman said that this matter was still under investigation, but that it suspected both parties had registered their products with the same username and password.
It could happen!
-
What? How many users is this thing going to have? You want to waste a full 128 bits on that? 16 bits should be enough(tm).
-
I wish they released details on how they generated their IDs. Depending on how much exactly they fucked it up, it might've become a perfect counterargument to all the people saying "very long random numbers are just as unique as actual unique numbers".
-
@cvi said in How not to do UUIDs:
What? How many users is this thing going to have? You want to waste a full 128 bits on that? 16 bits should be enough(tm).
Heh, I designed a portable product that used a custom RF modulation scheme. Nothing else would ever be able to talk to my stuff so I used a single byte (they're expensive for battery powered stuff!) for the ID and we just rolled the unit IDs assigned during production.
Of course we had a collision about as soon as it was possible to have one. And then really never after that. Sod's law strikes again...
-
@gąska said in How not to do UUIDs:
I wish they released details on how they generated their IDs
Likely, someone had a password generator on their workstation and forgot to click "generate!" after they cookies copied it, and simply pasted it twice on two units.
-
[A Swann spokeswoman] said that "human error" had caused two cameras to be manufactured that shared the same "bank-grade security key - which secures all communications with its owner".
If you're not already sniggering up your sleeve at this, I'll give you some time to let it sink in.
The least it needs to be is military-grade...
-
Knowing what I do about bank IT and security practices, describing something as bank grade security somehow fails to reassure.
-
@pjh said in How not to do UUIDs:
[A Swann spokeswoman] said that "human error" had caused two cameras to be manufactured that shared the same "bank-grade security key - which secures all communications with its owner".
If you're not already sniggering up your sleeve at this, I'll give you some time to let it sink in.
The least it needs to be is military-grade...
Civilians don't need military grade assault UUID generation.
-
@pie_flavor said in How not to do UUIDs:
Civilians don't need military grade assault UUID generation.
That'll be the 256-bit MUUIDs, yes?
-
@pjh if you're planning on mixing my data with data from this universe go ahead and delete my account.
-
@pjh said in How not to do UUIDs:
That'll be the 256-bit MUUIDs, yes?
Sounds great! I'll just set all those extra bits to a constant value for my convenience though; that'll work out just as well, yes?
-
@benjamin-hall said in How not to do UUIDs:
Knowing what I do about bank IT and security practices, describing something as bank grade security somehow fails to reassure.
Hmm, have I posted about my bank yet? [googles] Nope, okay, time to go start a thread.
Here's a preview:
-
English letters
ſtreƿþ!
-
@greybeard said in How not to do UUIDs:
ſtreƿþ
congrats on this word having 4 Google results and all of them being this page.
-
-
@zemm said in How not to do UUIDs:
@lorne-kates Letters? Luxury...
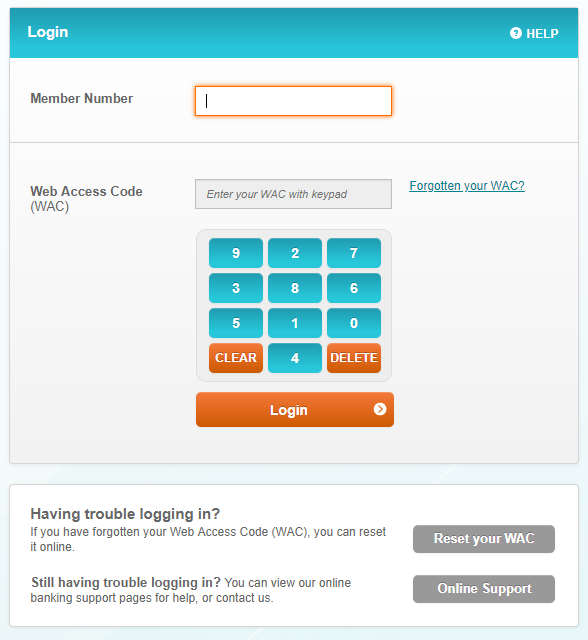
(No, there's no other password or anything)
enter your wisconsin athletic center with keypad
this is more secure than a physical keyboard because
uhhhhhhhhhhhh
-
-
That's the theory, yes. Of course, it only works against hardware keyloggers, which are an unlikely threat for people like you and me. It won't prevent a software keylogger from screenshoting the area you're clicking on, defeating the purpose.
-
@zerosquare Well, you can bypass those by using a password manager. (Assuming that site is as sloppily coded as treasurydirect.gov's login page).
-
From memory the site "encrypts" your WAC before sending it off (Ceasar cypher over HTTPS), which would defeat any password manager.
This is my secondary account: my main bank used to have a keyboard that moved on every click but at least it was alphanumeric. It's a normal (looking) password field now.
-
@zerosquare said in How not to do UUIDs:
That's the theory, yes. Of course, it only works against hardware keyloggers, which are an unlikely threat for people like you and me. It won't prevent a software keylogger from screenshoting the area you're clicking on, defeating the purpose.
RuneScape tried to get around that by hiding the number you hovered over on the bank PIN screen.
Of course, the other 9 numbers were still visible, so the "security" feature only made it harder to use for people and did nothing to add security.
Also, the concept of a bank PIN in a video game that isn't part of the storyline is hilarious to me because it means the company assumes its users will have bad enough security practices that their accounts will be regularly broken into.
(Also, at one point, they made it so if you type a message that contains your exact password into chat, it refuses to let you send it. So they might have been right about their users being idiots.)
-
@zemm said in How not to do UUIDs:
which would defeat any password manager
Nice, an anti-security measure. Nice to have those on important websites.
-
@Zemm I think the WAC is your password.
-
@ben_lubar said in How not to do UUIDs:
(Also, at one point, they made it so if you type a message that contains your exact password into chat, it refuses to let you send it. So they might have been right about their users being idiots.)
<Cthon98> hey, if you type in your pw, it will show as stars <Cthon98> ********* see! <AzureDiamond> hunter2 <AzureDiamond> doesnt look like stars to me <Cthon98> <AzureDiamond> ******* <Cthon98> thats what I see <AzureDiamond> oh, really? <Cthon98> Absolutely <AzureDiamond> you can go hunter2 my hunter2-ing hunter2 <AzureDiamond> haha, does that look funny to you? <Cthon98> lol, yes. See, when YOU type hunter2, it shows to us as ******* <AzureDiamond> thats neat, I didnt know IRC did that <Cthon98> yep, no matter how many times you type hunter2, it will show to us as ******* <AzureDiamond> awesome! <AzureDiamond> wait, how do you know my pw? <Cthon98> er, I just copy pasted YOUR ******'s and it appears to YOU as hunter2 cause its your pw <AzureDiamond> oh, ok.
-
@ben_lubar said in How not to do UUIDs:
congrats on this word having 4 Google results and all of them being this page.
Apple does a little better:
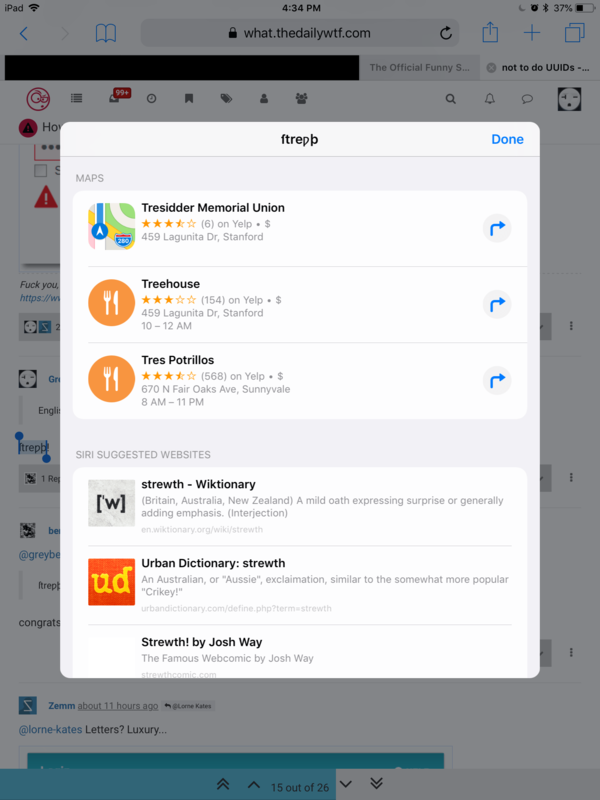
Except for Maps. But, you know, Apple Maps.
-
@zemm said in How not to do UUIDs:
Ceasar cypher over HTTPS
That's great, because if an attacker manages to break whatever encryption SSL is using, there's still the Caeser Cypher to stop them.
-
@zecc said in How not to do UUIDs:
@zemm said in How not to do UUIDs:
Ceasar cypher over HTTPS
That's great, because if an attacker manages to break whatever encryption SSL is using, there's still the Caeser Cypher to stop them.
Status: Extremely tempted to implement this in a library
-
@djls45 said in How not to do UUIDs:
@Zemm I think the WAC is your password.
Yes it is. That is a screen shot from one of my two banks I actually use. My password or WAC is an 8 digit number.
-
@pjh said in How not to do UUIDs:
[A Swann spokeswoman] said that "human error" had caused two cameras to be manufactured that shared the same "bank-grade security key - which secures all communications with its owner".
If you're not already sniggering up your sleeve at this, I'll give you some time to let it sink in.
The least it needs to be is military-grade...
Given that banks give me a 20-character maximum on passwords...
-
@zemm said in How not to do UUIDs:
@lorne-kates Letters? Luxury...
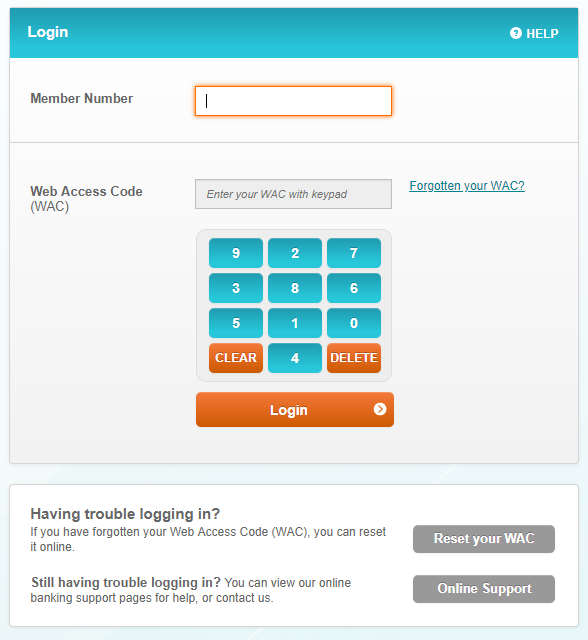
(No, there's no other password or anything)
That's whack.
-
@benjamin-hall said in How not to do UUIDs:
Knowing what I do about bank IT and security practices, describing something as bank grade security somehow fails to reassure.
The banks network security here are as tight as it's possible with current tech, afaik
-
@ben_lubar said in How not to do UUIDs:
Also, the concept of a bank PIN in a video game that isn't part of the storyline is hilarious to me because it means the company assumes its users will have bad enough security practices that their accounts will be regularly broken into.
It's been 10+ years since I've played RuneScape, but it was common back then. There were Chinese hacker farms that brute-forced passwords until they got into player accounts, then they'd empty their in-game banks and trade the items to their own accounts and later sell the stolen in-game items for real-world money.
-
@mott555 said in How not to do UUIDs:
@ben_lubar said in How not to do UUIDs:
Also, the concept of a bank PIN in a video game that isn't part of the storyline is hilarious to me because it means the company assumes its users will have bad enough security practices that their accounts will be regularly broken into.
It's been 10+ years since I've played RuneScape, but it was common back then. There were Chinese hacker farms that brute-forced passwords until they got into player accounts, then they'd empty their in-game banks and trade the items to their own accounts and later sell the stolen in-game items for real-world money.
Speaking of password security:
-
@ben_lubar said in How not to do UUIDs:
@zerosquare said in How not to do UUIDs:
That's the theory, yes. Of course, it only works against hardware keyloggers, which are an unlikely threat for people like you and me. It won't prevent a software keylogger from screenshoting the area you're clicking on, defeating the purpose.
RuneScape tried to get around that by hiding the number you hovered over on the bank PIN screen.
Of course, the other 9 numbers were still visible, so the "security" feature only made it harder to use for people and did nothing to add security.
Also, the concept of a bank PIN in a video game that isn't part of the storyline is hilarious to me because it means the company assumes its users will have bad enough security practices that their accounts will be regularly broken into.
(Also, at one point, they made it so if you type a message that contains your exact password into chat, it refuses to let you send it. So they might have been right about their users being idiots.)
It all made perfect sense to 9 year old me.
-
@ben_lubar said in How not to do UUIDs:
@greybeard said in How not to do UUIDs:
ſtreƿþ
congrats on this word having 4 Google results and all of them being this page.
We have five now!