This is an old Windows compatibility feature where any executable that contains "install" or "setup" in the exe name will be run as Administrator because no old installer had a manifest and installing would fail badly otherwise.
hifi
@hifi
Best posts made by hifi
-
RE: Install under any other name…posted in Side Bar WTF
-
Ingenious FizzBuzz solutionposted in CodeSOD
We were talking on TDWTF IRC channel about the FizzBuzz test and out of curiosity I gave the test to my wife who is not a professional programmer. She didn't know the modulus syntax of PHP (her choice) so she came up with this gem:
<?php $i = 1; while ($i <= 100) { if ((strlen($i/3) < 3) && (strlen($i/5) < 3)) { echo "FizzBuzz\n"; } else if (strlen($i/3) < 3) { echo "Fizz\n"; } else if (strlen($i/5) < 3) { echo "Buzz\n"; } else echo $i."\n"; $i++; } ?>For the disbelievers it does work: http://codepad.org/9KcyveJF
I'm so proud!

-
Microsoft Teams browser desktop notifications failposted in Side Bar WTF
So we're moving to Microsoft Teams at work and on Linux I use it in-browser. Unfortunately desktop notifications didn't work so when someone said something somewhere I never got any notification and would essentially ignore the person because of that.
Anyway, I wanted to fix this by adding desktop notifications and dug up the AngularJS mess of what Teams is and found the plugin/module/whatever that does that. Then hooked things for a while and finally captured the in-tab notifications that were created. Hooray!
When I started using the
NotificationAPI to actually show those notifications outside the browser I suddenly noticed I got the real notifications from Teams in addition to what I hacked together.Took me a while to realize this but it would have worked from the start if Microsoft had this anywhere in the bootstrap code as the plugin they use does indeed send the notifications:
Notification.requestPermission();
So if you want desktop notifications from the Microsoft Teams browser version, paste that into the browser JS console and accept the request once to permanently get notifications from everything like you should.
-
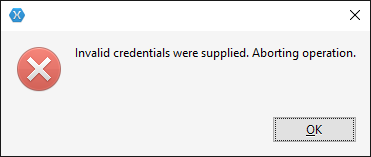
How hard is Git integration? Can Spambots do it?posted in Error'd
I gave Xamarin Studio a go to see if it can do a basic clone of a Git repository over SSH. The reason I wanted to try it was that VS does not yet have it and it's such a bloat to install and I'm already using MonoDevelop on Linux so it should be straightforward.
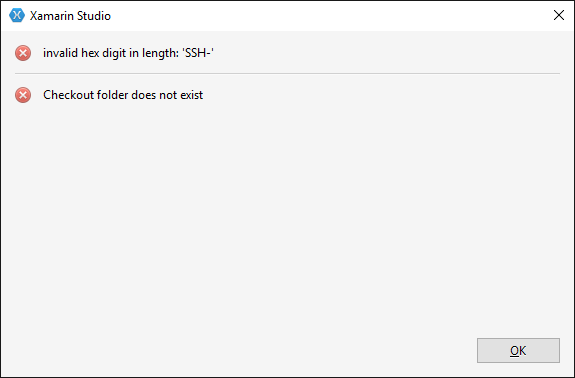
Ok, maybe I did something wrong but this error dialog is a
 in itself. There's no context of what it tried and what went wrong. I'm assuming 'SSH-' is the partial plain text header SSH protocol has so it wasn't expecting SSH even thought I thought I asked for SSH.
in itself. There's no context of what it tried and what went wrong. I'm assuming 'SSH-' is the partial plain text header SSH protocol has so it wasn't expecting SSH even thought I thought I asked for SSH.Bonus
 from Windows 10 when trying to remove some leftover directories when trying this again:
from Windows 10 when trying to remove some leftover directories when trying this again: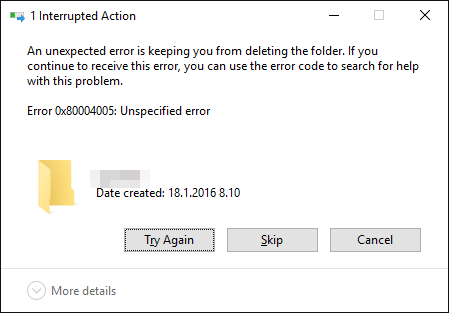
First I thought my Shift-Delete didn't go through because I hit the return key from muscle memory and the directory was still there and for some reason Windows 10 didn't refresh the view so that error came from trying to remove a directory that didn't exist.
I kept trying to clone the repository again multiple times after I finally got all the bits right that usually just work when you give a
ssh://URL to any other Git thingy. Then the next thing happened: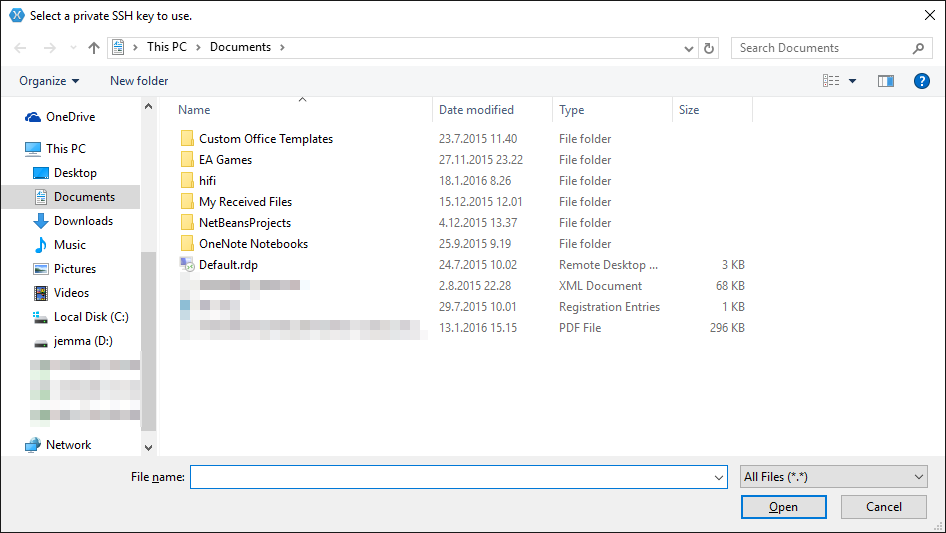
If you shat bricks in under 2 seconds, congratulations, you're a professional Windows user. I got no question, warning, explanation, nothing. Just suddenly popped up a file selection dialog which I wasn't expecting.
After a while I read the title which confused me as I already have my key loaded to Pageant which every fucking Git software on Windows seems to work OK with except Xamarin Studio.
Whatever, here's my (passphrased) key in PuTTy format as the dialog didn't even specify what format it wants (I tried the OpenSSH version as well, no dice):
I give up.
P.S Title

-
RE: Windows 10 automatically installing :shit:posted in General
XP at least asked you if you want it to do that. Usually it failed to find any drivers anyway.
-
RE: Guy brings down thousands of npm buildsposted in Side Bar WTF
For once, PHP is not TRWTF. It also actually has string padding functions.
-
RE: WTDWTF Chat! [now working]posted in Meta
I'd rather have the channel on a public and stable network. There are plenty to choose from. Freenode would be at the top of my list as there are a lot of programming related channels.
EDIT: Why don't we just do it? #thedailywtf @ irc.freenode.net. If no one comes, it was a dead idea to begin with.
-
RE: Linus is on a tear againposted in General
Meanwhile, Linus seems perfectly fine with the
gotostatement... :person_frowning.mif:In C,
gotois a way to handle error conditions in nested code and is very readable when the programmer isn't shit. -
RE: MS apps and the genius question.posted in Side Bar WTF
It lacks a
E_GENIUS_NOT_FOUNDoptionFound them! Maybe they can help.
[img]http://www.macobserver.com/imgs/teaser_images/20120822_appleretailemployees.jpg[/img]
Latest posts made by hifi
-
RE: Ingenious FizzBuzz solutionposted in CodeSOD
@ben_lubar said in Ingenious FizzBuzz solution:
@hifi said in Ingenious FizzBuzz solution:
She didn't know the modulus syntax of PHP
I don't think I've ever seen a language where it wasn't
%, other than assembly languages and languages where there is no modulus operator.It's the only language she knows and she has never needed the modulus operator for anything she does with PHP.
-
Ingenious FizzBuzz solutionposted in CodeSOD
We were talking on TDWTF IRC channel about the FizzBuzz test and out of curiosity I gave the test to my wife who is not a professional programmer. She didn't know the modulus syntax of PHP (her choice) so she came up with this gem:
<?php $i = 1; while ($i <= 100) { if ((strlen($i/3) < 3) && (strlen($i/5) < 3)) { echo "FizzBuzz\n"; } else if (strlen($i/3) < 3) { echo "Fizz\n"; } else if (strlen($i/5) < 3) { echo "Buzz\n"; } else echo $i."\n"; $i++; } ?>For the disbelievers it does work: http://codepad.org/9KcyveJF
I'm so proud!

-
RE: Compromising MD5/SHA1 hashed passwordsposted in General
@dkf said in Compromising MD5/SHA1 hashed passwords:
@Groaner said in Compromising MD5/SHA1 hashed passwords:
that still doesn't answer my question as to why application user account credentials are so valuable when the attacker already has the entire database
Because many people use the same username and password for many services. The breach in one place may allow an attack in another more valuable location, despite that other service following many more proper security practices.
This thread has wandered a bit off from the topic. The question is how you can get the original non-salted password brute forced so you can reuse it in another service, like @dkf said here.
The original database that would have been already breached is irrelevant as that's already a lost cause but the damage can be extended by actually reusing a weak password that is weakly hashed on some other service, say, GMail or Hotmail which gives you a lot more valuable data.
People are now crazy about using SHA-82938 or something else but the question is do MD5 and SHA-1 actually pose the kind of security issue for sane salted passwords that they would be as insecure as being in plain text. Can we actually attack them in that way and if Moore's Law applies, how long would it take to get there?
Regarding the topic, because we assume salt we can rule out collisions as it would be very unlikely to hit a collision of
saltFoowhen the actual salted plain text password wassaltBarso we do know when we find the real password by comparing the salt to the brute forced string and that's the real value of the attack. -
RE: Compromising MD5/SHA1 hashed passwordsposted in General
@dkf said in Compromising MD5/SHA1 hashed passwords:
Instead, switch to something like bcrypt, which is quite a strong algorithm and comes with built-in per-password salting. (I'm assuming you're using session tokens as well; bcrypt is actually too computationally expensive for use on a per-request basis in any site or API that requires many calls to be made in quick session.)
I've heard good things about bcrypt from multiple sources so it seems to be the obvious choice.
@Weng said in Compromising MD5/SHA1 hashed passwords:
@hifi If you know the salt and how the salt is applied (or can make a reasonable guess at how it's applied) it's as simple as building a custom rainbow table.
Isn't building a custom rainbow table essentially the same as brute forcing?
@Weng said in Compromising MD5/SHA1 hashed passwords:
This is why, when a salted password database using high end hash algorithms is compromised, you still change your passwords. Too much work to compromise ALL the accounts, but relatively trivial to take on a few targeted ones.
What's relatively trivial? If the length of the password is anything reasonable, is it actually trivial to brute 12+ character MD5 or SHA-1 password? @PleegWat threw some numbers on the table which seem to speak on the behalf of "not practical" as of today.
-
Compromising MD5/SHA1 hashed passwordsposted in General
I had a small argument about this and I'm interested in how practical it would be to crack a single password of a high value target given the following conditions:
- its sum is either MD5 or SHA-1 (both declared shit by now)
- it has some salt so it can't be directly pulled from a rainbow table but you have access to it and know how it's applied
- the length of the password is, say, 12 characters, in this case we would know the exact length for some reason
- you know the service password charset limitations, say, printable ascii characters (alnum + special but no space)
- a) you have access to the regular consumer crap (high end GPUs and such)
b) you run a criminal organization and have enough money to buy shittons of consumer crap
How practical would it be to get the original string out? How about the vulnerabilities in MD5 and SHA-1, can brute forcing be accelerated enough for practical attacks? Getting a collision is not that useful if your intention is to reuse the password to gain access to something else than the service it was leaked from.
My argument is that given these conditions it's probably impractical even with a lot of money to crack a password even when hashed with these algorithms if you have length and salt.
Now tell me I'm wrong about the world not ending.
-
RE: Microsoft Teams browser desktop notifications failposted in Side Bar WTF
@Zecc said in Microsoft Teams browser desktop notifications fail:
I don't know if this is what you meant, but it's Permissions tab on the Page Info dialog, which you can reach either through the Tools menu or the page's context menu.
I had to look that up because I couldn't remember where it was.
Yes, there, the list that comes down from the button only had the ones with non-default values.
-
RE: Microsoft Teams browser desktop notifications failposted in Side Bar WTF
@LB_ Actually you're right, it's buried a bit deeper. Easier fix than doing the JS thingy although it doesn't remove the WTF of not calling it in the first place as the user doesn't know he/she could receive notifications.
-
RE: Microsoft Teams browser desktop notifications failposted in Side Bar WTF
@LB_ That's probably a Chrome only feature to have a list of all permissions. Firefox does not list them unless a site has requested something once.
-
Microsoft Teams browser desktop notifications failposted in Side Bar WTF
So we're moving to Microsoft Teams at work and on Linux I use it in-browser. Unfortunately desktop notifications didn't work so when someone said something somewhere I never got any notification and would essentially ignore the person because of that.
Anyway, I wanted to fix this by adding desktop notifications and dug up the AngularJS mess of what Teams is and found the plugin/module/whatever that does that. Then hooked things for a while and finally captured the in-tab notifications that were created. Hooray!
When I started using the
NotificationAPI to actually show those notifications outside the browser I suddenly noticed I got the real notifications from Teams in addition to what I hacked together.Took me a while to realize this but it would have worked from the start if Microsoft had this anywhere in the bootstrap code as the plugin they use does indeed send the notifications:
Notification.requestPermission();
So if you want desktop notifications from the Microsoft Teams browser version, paste that into the browser JS console and accept the request once to permanently get notifications from everything like you should.
-
RE: Windows 10 license, or hold your boards!posted in Side Bar WTF
@LB_ said in Windows 10 license, or hold your boards!:
In addition, we're introducing the ability to link your Microsoft account (MSA) to the activation digital license with this Insider Preview build. If you already used an MSA to log in to your activated Windows 10 Home or Pro device, your MSA will be automatically linked. You can use this MSA linked digital license to re-activate your Genuine Windows 10 device by running the Activation troubleshooter, if you run into Activation issues caused by hardware changes.
So wait, now I have only one license and PC for the rest of my life?