Cloudflare? moar liek cloud BARE amirite
-
We keep finding more sensitive data that we need to cleanup. I didn't realize how much of the internet was sitting behind a Cloudflare CDN until this incident.
The examples we're finding are so bad, I cancelled some weekend plans to go into the office on Sunday to help build some tools to cleanup. I've informed cloudflare what I'm working on. I'm finding private messages from major dating sites, full messages from a well-known chat service, online password manager data, frames from adult video sites, hotel bookings. We're talking full https requests, client IP addresses, full responses, cookies, passwords, keys, data, everything.
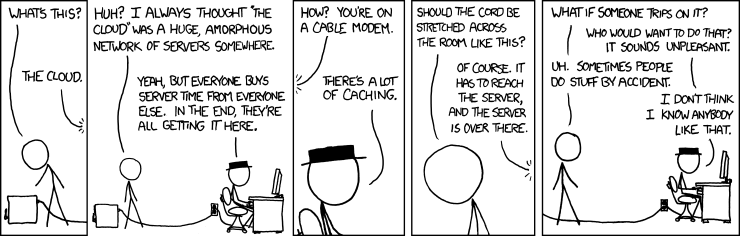
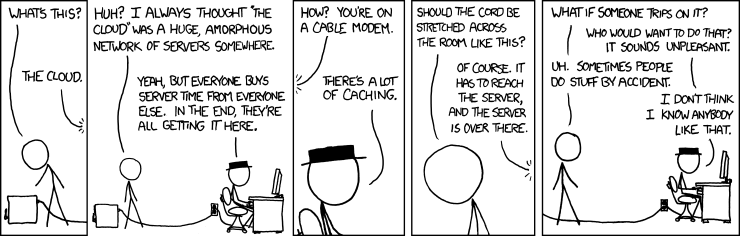
As MeFite zachlipton wonders: "Why exactly did we think it was a good idea to have a single company MITM a giant chunk of the internet?"
-
-
Yeah. All the idiots on Discord are @all mentioning in their server slices blowing up everything about changing your password and crap.
#RaisingAwareness #TURNON2FA
-
even plaintext API requests from a popular password manager that were sent over https (!!).
Uh. :-/
-
@flabdablet said in Cloudflare? moar liek cloud BARE amirite:
full messages from a well-known chat service
Not sure if that's what he's talking about, but this just popped in my IRC client:
[24/02/2017 09:43:50] [Notice] -christel- [Global Notice] Hi all, Cloudflare has announced that a bug may have caused disclosure of data, sent via CF, to third parties, further info can be found at https://blog.cloudflare.com/ | freenode uses CF for CDN, while we have not received any reports indicating that we are affected, we urge webchat users in particular to consider changing their passwords! Thank you.
Yeah, that was Freenode, where
#thedailywtfchannel lives. Yay.I mean, I didn't discuss anything sensitive anywhere on freenode, personally, but I think password change might be in order, just in case...
-
@flabdablet said in Cloudflare? moar liek cloud BARE amirite:
online password manager data
I'm glad I use the offline version of KeePass
-
@Tsaukpaetra said in Cloudflare? moar liek cloud BARE amirite:
Yeah. All the idiots on Discord are @all mentioning in their server slices blowing up everything about changing your password and crap.
As if this fixes underlying issue.
-
/me is happy she uses a different password for each site/service/other she uses
/me is even happier about all the 2FA she's activated, including Discord :D
-
This is a CRAZY day from a netsec perspective with the Cloudflare memory leak announcement on top of the SHA-1 collision announcement. I can already tell I'm going to be in meetings all day.
-
@Jaloopa said in Cloudflare? moar liek cloud BARE amirite:
@flabdablet said in Cloudflare? moar liek cloud BARE amirite:
online password manager data
I'm glad I use the offline version of KeePass
Is there another version?
-
@Gąska said in Cloudflare? moar liek cloud BARE amirite:
@Tsaukpaetra said in Cloudflare? moar liek cloud BARE amirite:
Yeah. All the idiots on Discord are @all mentioning in their server slices blowing up everything about changing your password and crap.
As if this fixes underlying issue.
Also discord sounds suspiciously close to discourse....
-
@dangeRuss Discord is basically synchronous Discourse with more "telemetry."
-
@dangeRuss said in Cloudflare? moar liek cloud BARE amirite:
Is there another version?
When it comes to Android apps, there's Keepass2Droid which lets you use an online database, or Keepass2Droid Offline, which doesn't have the internet permission and only works on local databases
-
What's this? A company that basically holds the entire Internet for ransom, exposing private data at scale through an obvious bug? I'm shocked, shocked I tell you!
-
@bugmenot said in Cloudflare? moar liek cloud BARE amirite:
A company that basically holds the entire Internet for ransom
wat.
an obvious bug
wat.
-
@heterodox With the massive volume of DDoS attacks available from botnets for anyone willing to lay out the bitcoin, you're effectively forced to use CloudFlare to act as a bandwidth sponge for your website if you don't want it to get knocked over by any script kiddie who wants to have a go. The cost of that is you become susceptible to bugs like this one, as well as the usual impacts of a man-in-the-middle attack. The bug itself is by all accounts the classic C mistake of not checking your bounds logic to see if your I/O write will actually point to where you expect.
-
@heterodox OH FUCK. I knew I was right to use SHA-512 for all my secure hashing.
-
@bugmenot said in Cloudflare? moar liek cloud BARE amirite:
@heterodox With the massive volume of DDoS attacks available from botnets for anyone willing to lay out the bitcoin, you're effectively forced to use CloudFlare to act as a bandwidth sponge for your website if you don't want it to get knocked over by any script kiddie who wants to have a go. The cost of that is you become susceptible to bugs like this one, as well as the usual impacts of a man-in-the-middle attack. The bug itself is by all accounts the classic C mistake of not checking your bounds logic to see if your I/O write will actually point to where you expect.
None of what you said is equivalent to CloudFlare holding the Internet for ransom; it's equivalent to CloudFlare providing an essential service. If CloudFlare were the one launching the DDoS attacks they'd be holding the Internet for ransom.
As far as the bug, you only read the Google thread, I can see. Yes, the bug is obvious in:
script_consume_attr := ((unquoted_attr_char)* :>> (space|'/'|'>')) >{ ddctx("script consume_attr"); } @{ fhold; fgoto script_tag_parse; } $lerr{ dd("script consume_attr failed"); fgoto script_consume_attr; };</s>
I'm all too happy to board the managed languages train, but I can see how certain properties of managed languages could be undesirable in a highly performance-dependent environment and how these mistakes can happen. This is why defense in depth of the type practiced by 1Password etc. is important.
-
@flabdablet said in Cloudflare? moar liek cloud BARE amirite:
As MeFite zachlipton wonders: "Why exactly did we think it was a good idea to have a single company MITM a giant chunk of the internet?"
Boy, if you think trusting Cloudflare is bad, wait until you learn how much power we have all given to the actually big companies.
-
@anonymous234 said in Cloudflare? moar liek cloud BARE amirite:
much power we have all given to the actually big companies.
hmm..... just about all of it.
the thing is i'm not sure who will notice that fact first..... if they do it could be really really really bad, if the populous does..... it will be really really really bad......
-
@Jaloopa said in Cloudflare? moar liek cloud BARE amirite:
@dangeRuss said in Cloudflare? moar liek cloud BARE amirite:
Is there another version?
When it comes to Android apps, there's Keepass2Droid which lets you use an online database, or Keepass2Droid Offline, which doesn't have the internet permission and only works on local databases
yea, but neither is a problem here. I don't care if someone gets a copy of my db as much, because they would need my password to use it.
-
@flabdablet said in Cloudflare? moar liek cloud BARE amirite:
Why exactly did we think it was a good idea to have a single company MITM a giant chunk of the internet?
The Illuminati made us think that so they have a handy single monitoring infrastructure.
-
4,287,625 possibly affected domains.
What should I do?
Check your password managers and change all your passwords
-
Just because a domain is on the list does not mean the site is compromised, and sites may be compromised that do not appear on this list.
Makes you wonder why bother compiling it.
-
@accalia said in Cloudflare? moar liek cloud BARE amirite:
i'm not sure who will notice that fact first
It's OK, it was rms and the standard "smelly hippie" propaganda manouevre was enough to deal with that threat.
-
@PleegWat Majestic 12 actually, they split from the Illuminati some time before that.
-
erlfdoulC
-
@flabdablet said in Cloudflare? moar liek cloud BARE amirite:
It's OK, it was rms and the standard "smelly hippie" propaganda manouevre was enough to deal with that threat.
Toby Faire, RMS really seems to play up that aspect of himself.
-
@anonymous234 said in Cloudflare? moar liek cloud BARE amirite:
how much power we have all given to the actually big companies.
TREMENDOUS power?
-
You know, it's interesting how we consider page rewriting bad when a consumer ISP does it, but we think it's somehow perfectly OK when CloudFlare does it...
This vulnerability just reminds us why it's a bad thing.
-
@powerlord said in Cloudflare? moar liek cloud BARE amirite:
You know, it's interesting how we consider page rewriting bad when a consumer ISP does it, but we think it's somehow perfectly OK when CloudFlare does it...
The latter is authorized by the owner of the page; it's something they chose to enable, just like anything else on the page itself. The former is a third party sticking their nose in where it's not wanted.
-
@RaceProUK said in Cloudflare? moar liek cloud BARE amirite:
Makes you wonder why bother compiling it.
Every single place I saw the announcement I also saw the dude posting about his GitHub. It was just for attention. And it was obnoxious because Cloudflare DNS (which I believe is free, or low-cost) != Cloudflare proxy services and the latter were the only ones vulnerable to having their traffic leaked. The difference in scope is massive. And you just knew the news were going to pick up sites in that list (because they don't know any better when it comes to technology) and then those site owners were going to be busy rebutting news of a leak that in no way affected them.
-
@heterodox Any reputable site is going to alert its users separately anyway. For instance, Change.org uses CloudFlare, and they emailed all their users to say they likely weren't affected, but it doesn't hurt to play it safe, so change your password anyway. I mean, let's face it, you're meant to change passwords regularly, but who does?

-
@RaceProUK Yeah, I've been sighing at people spreading the CHANGE YOUR PASSWORDS NOW posts, but haven't said anything cause the end result isn't bad.
-
-
@RaceProUK said in Cloudflare? moar liek cloud BARE amirite:
Change.org uses CloudFlare, and they emailed all their users to say they likely weren't affected, but it doesn't hurt to play it safe, so change your password anyway
They must not want my change, I have not recieved such an email.
-
@heterodox said in Cloudflare? moar liek cloud BARE amirite:
As far as the bug, you only read the Google thread, I can see. Yes, the bug is obvious in:
Yeah. It's not directly obvious because they used a macrolanguage that obfuscates the actual bug.
TLDR, fucking security audit your fucking generated code you fucking morons.
-
@Weng said in Cloudflare? moar liek cloud BARE amirite:
@heterodox said in Cloudflare? moar liek cloud BARE amirite:
As far as the bug, you only read the Google thread, I can see. Yes, the bug is obvious in:
Yeah. It's not directly obvious because they used a macrolanguage that obfuscates the actual bug.
TLDR, fucking security audit your fucking generated code you fucking morons.
Actually.
Let me be more specific.
Security audit your source.
Security audit any transpiled source.
Security audit and test every component individually.
Security audit and test the entire system as a whole.You know. Not just any one step. Fucking morons.
-
So I wonder if this is related. Slightly obfuscated headers:
Delivered-To: gearbest@dangeruss.com Received: by 10.237.35.134 with SMTP id j6csp298537qtc; Fri, 10 Mar 2017 19:15:49 -0800 (PST) X-Received: by 10.36.116.71 with SMTP id o68mr2186451itc.60.1489202149379; Fri, 10 Mar 2017 19:15:49 -0800 (PST) Return-Path: <bounces+30983-2423-gearbest=dangeruss.com@email.fitbit.com> Received: from o3.email.fitbit.com (o3.email.fitbit.com. [167.89.18.128]) by mx.google.com with ESMTPS id n17si4881489ioo.93.2017.03.10.19.15.49 for <gearbest@dangeruss.com> (version=TLS1_2 cipher=ECDHE-RSA-AES128-GCM-SHA256 bits=128/128); Fri, 10 Mar 2017 19:15:49 -0800 (PST) Received-SPF: pass (google.com: domain of bounces+12345-5678-gearbest=dangeruss.com@email.fitbit.com designates 167.89.18.128 as permitted sender) client-ip=167.89.18.128; Authentication-Results: mx.google.com; dkim=pass header.i=@email.fitbit.com; spf=pass (google.com: domain of bounces+12345-5678-gearbest=dangeruss.com@email.fitbit.com designates 167.89.18.128 as permitted sender) smtp.mailfrom=bounces+30983-2423-gearbest=dangeruss.com@email.fitbit.com; dmarc=pass (p=REJECT sp=REJECT dis=NONE) header.from=fitbit.com DKIM-Signature: v=1; a=rsa-sha1; c=relaxed/relaxed; d=email.fitbit.com; h=content-type:from:mime-version:subject:to; s=smtpapi; bh=JZGDDEO/Undb5/+1j5ZTxZXsZkg=; b=Z6k7W8mQTezxozuHMn 8XIfOMFaAX8HPSgeCBXKU4WSKMBot18KtEUQ600luP+9l9z7HpzjjhNXnfFqK8E4 zJl7kQONpR60iyWDb93EB22ScW6Hod6+cHLktLPmu22SUknz6siTSNJZ/g39yjJ0 koW8jflRl2l6qhkiSZbDPCV+U= Received: by filter0095p1las1.sendgrid.net with SMTP id filter0095p1las1-28240-58C36BE4-2B 2017-03-11 03:15:48.697038119 +0000 UTC Received: from MzA5ODM (a9.fe.a86c.ip4.static.sl-reverse.com [108.168.254.169]) by ismtpd0003p1sjc2.sendgrid.net (SG) with HTTP id kvQoaZxqSwa3J4Nfkszj1A for <gearbest@dangeruss.com>; Sat, 11 Mar 2017 03:15:48.614 +0000 (UTC) Content-Type: multipart/alternative; boundary=df361e6fe995c360110e912270822f72ec03d6ad5daef043ada01bc7a5dc Date: Sat, 11 Mar 2017 03:15:48 +0000 From: "http://rayban.ddnsking.com/" <messages-noreply@fitbit.com> Mime-Version: 1.0 Subject: [Fitbit] http://rayban.ddnsking.com/ vous a invité(e) à rejoindre le groupe · sur Fitbit To: gearbest@dangeruss.com Message-ID: <kvQoaZxqSwa3J4Nfkszj1A@ismtpd0003p1sjc2.sendgrid.net> X-SG-EID: KZiMIh2ZtZI8pNnCAUheF4ufE1zf707K3b/RphfOAOnAwYs3W/gTu+RQPROGneL50+BhMEopS2REbm 2/bF+Nf9PvQMoiu9MbboqrGqK6/AosANoXFlYWdftB9GEEYaeP/a2W7KyP614A7SYK1S/XekecRE+g 84tZ7bq0K0RyPEY9qMoPHt3WbgBectVPPnfs8JE4FOkxaCCzMDyeDZVf5zdpBbqCg0oNMqRbHO+xoB BkE5TOXAjMUW/I7B0EZpDR X-SG-ID: OGhsOBKlDLVmM893F6FJZpN7/hqgTn+Oil7lrVrv6l0=Looks like their api key to sendgrid got leaked maybe?
This is not just regular spam. All the security checks passed and it went straight into my gmail inbox.
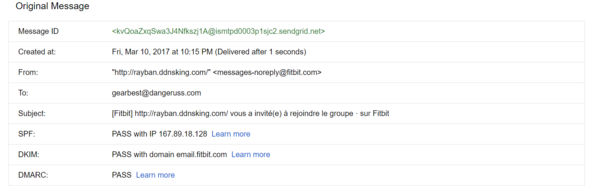
Also I guess they got my gearbest email somewhere.... Maybe gearbest was breached too?
 1139 -
project-zero -
Project Zero -
Monorail
1139 -
project-zero -
Project Zero -
Monorail
 Pragmatic thoughts on #CloudBleed
Pragmatic thoughts on #CloudBleed
