Online in the train? Now we know exactly where you are.
-
Sorry, couldn't find an english version. So, TG;CR:
The German rail company is switching their onboard wifi to a new shiny "multi provider" technology.
Problem is: The captive portal is on a separate domain from the gateway that unlocks the user and (idiotically) also provides nice statistics about the train and the user's device and stuff.
Because AJAX requests don't work across domains, they use JSONP (because that doesn't give a shit about stupid security barriers) without extra validation tokens (because neither do the devs) to tell the gateway when the user has accepted the terms of use on the captive portal.Because of this stupid solution, EVERY website the user visits can now tell the browser to send requests to the gateway and return information like
- Train position and speed (https://www.ombord.info/api/jsonp/position/)
- User IP, MAC, transfer stats (https://www.ombord.info/api/jsonp/user/)
or just disconnect the user altogether:
<iframe src="https://www.ombord.info/hotspot/hotspot.cgi?method=logout&url=&onerror="></iframe>
NICE IPAD YOU HAVE THERE. WOULD BE A SHAME IF SOMEONE JOINED YOU ON $NEXT_STATION AND TOOK IT, EH? GIVE ME MONEY. I'LL KILL YOUR CONNECTION NOW TO SHOW YOU I'M SERIOUS.
-
@ChrisH said in Online in the train? Now we know exactly where you are.:
NICE IPAD YOU HAVE THERE. WOULD BE A SHAME IF SOMEONE JOINED YOU ON $NEXT_STATION AND TOOK IT, EH? GIVE ME MONEY. I'LL KILL YOUR CONNECTION NOW TO SHOW YOU I'M SERIOUS.
Mugging someone for their stuff:

Mugging someone for their iDiot device:



-
@masonwheeler Getting a iDiot device owner to send you money via ucash: PROFIT
-
@ChrisH It took them years to make their own website usable, so I'm not surprised.
-
@ChrisH said in Online in the train? Now we know exactly where you are.:
JSONP
BTW, this is the first time I hear about JSONP, and if had not already quit web development, I would now. If you think this is a good idea in the first place, you should be legally required to stay away from computers for the rest of your life.
-
@asdf Probably because it was a short-lived hack that was, unfortunately, the best way to solve a specific problem until CORS headers became the standard.
Now that we've got CORS headers to do cross-origin resource sharing the right way, there's really no need for JSONP anymore. (Which doesn't mean a few
 developers aren't still using it, of course.)
developers aren't still using it, of course.)
-
@masonwheeler said in Online in the train? Now we know exactly where you are.:
Probably because it was a short-lived hack that was, unfortunately, the best way to solve a specific problem until CORS headers became the standard.
How about contacting the other server via your own backend? Yes, that requires a bit more time, but doesn't open a huge attack vector.
-
@asdf said in Online in the train? Now we know exactly where you are.:
How about contacting the other server via your own backend?
Configuring nginx to do the proxying is easy enough. I imagine it's easy with other webservers too. The point is you can get your frontend server to do the proxying for you; you don't need to involve the backend at all.
-
@dkf I wasn't suggesting using your own web server as a proxy, but actually validating the returned data on your own server before forwarding it to the user. I dislike the idea of including scripts from other domains in general.
-
@asdf said in Online in the train? Now we know exactly where you are.:
actually validating the returned data

I dislike the idea of including scripts from other domains in general.
There is much about the way the modern web works to loathe.
-
@dkf said in Online in the train? Now we know exactly where you are.:
There is much about the way the modern web works to loathe.
Me too.
But this habit of including scripts from other domains without thinking of the security implications is one of the worst, because it makes absolutely no sense. Just copy the damn thing to your own web server, goddammit!
-
@asdf but CDN, performanzzzzzz and hipster point zzz?
-
Isn't using public Wi-Fi a stupid idea in general?
-
Well, without any hacking you can also know where a train is (because they run according to a published schedule) and without any hacking you can also be pretty sure that any long-distance train will have quite a lot of people on board who carry expensive laptops/tablets/smartphones with them.
-
@aliceif said in Online in the train? Now we know exactly where you are.:
Isn't using public Wi-Fi a stupid idea in general?
Technically, anything less than using a wired connection drawn in pressurized-argon-filled titanium tubes to your next internet exchange is. You could just use a VPN though.
-
@Grunnen said in Online in the train? Now we know exactly where you are.:
without any hacking you can also be pretty sure that
any long-distance train will have quite a lot ofpeopleon board whocarry expensive laptops/tablets/smartphones with them.It's common enough that there's no point trying to figure out if they're there. They (almost certainly) are because going with out Facebook is too much.
-
@aliceif Public wifi is extremely insecure, anyone can not just view but (I think) modify your traffic.
This is a bad thing for you as an individual user, but a good thing for users as a whole, since it has forced developers to take end-to-end encryption seriously and made the Internet more secure rather than less.
Game theory, motherfuckers.
-
@thegoryone
-
@LaoC said in Online in the train? Now we know exactly where you are.:
You could just use a VPN though.
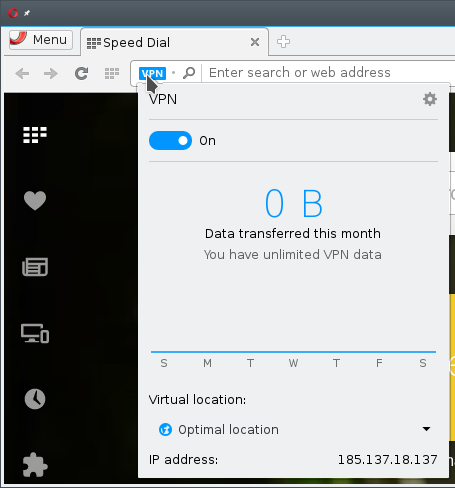

Filed under: Enjoy that IP, I have no idea what's there :P
-
@anonymous234 said in Online in the train? Now we know exactly where you are.:
@aliceif Public wifi is extremely insecure, anyone can not just view but (I think) modify your traffic.
This is a bad thing for you as an individual user, but a good thing for users as a whole, since it has forced developers to take end-to-end encryption seriously and made the Internet more secure rather than less.
Game theory, motherfuckers.
Of course, then you have situations like that recent one which just condition the users to click through any HTTPS errors no matter how big, red and scary the browsers make them...
-
@Maciejasjmj And very soon, browsers are going to be issuing warnings that HTTP sites with forms are also insecure... so more warnings we can condition users to click through on autopilot.
 Pineapple Surprise! Mixing trusting devices with sneaky Wi-Fi at #wdc13
Pineapple Surprise! Mixing trusting devices with sneaky Wi-Fi at #wdc13
